上午有两场summits,议题分别是:
sum-w01: G2B: Cyber-Business in Myanmar, Indonesia and Thailand
sum-w02: Achieving e-Commerce Success through Effective Internet Security: A Primer for SMEs
Myanmar是东南亚第二大国家,按照speaker的说法,人口多,发展快,市场很有潜力。不过business不是我们关心的,听了10分钟换场。
sum-w02主要讲中小企业如何从头构建有效的互联网安全体系。
Asia Pacific is the largest e-commerce region in the world. With 60% of the world's population, exploding smartphone usage and a growing consumer base that is twice as likely to buy online than any other group in the world, Asia is setting the agenda for global online retail. Such growth demands many things, chief among them building trust with consumers, who need to know their online payment transactions are secure. In a 2014 study by Mastercard, 31% of respondents cited security of transactions as a barrier to e-commerce uptake. If you consider that $567 billion was transacted online in the region in 2014, that translates to almost $176 billion in online sales impacted by security concerns. How can SMEs best address security concerns? Where should focus be placed to have maximum impact, both in security measures implemented and in success achieved? How do you even get started? This summit will explore security ramifications and provide critical guidance to SMEs looking to engage in e-commerce securely.
AGENDA ITEMS
- 08.00 – 08.45 hrs | Registration, breakfast, arrivals
- 08.45 – 08.50 hrs | Welcome and Introduction | Hugh Thompson
- 08.50 – 09.35 hrs | Overview of the Security Landscape | Bryce Boland
- 09.35 – 10.20 hrs | Building a Business Case for Security | Leon Miri Ronnie Islam
- 10.20 – 10.40 hrs | BREAK
- 10.40 – 11.25 hrs | Getting Started in Security: Balancing Budgets and Bodies | Philip Lee
- 11.25 – 12.00 hrs | Case Study: Security as a Differentiator | Freddy Tan
- 12.00 – 13.00 hrs | LUNCH
- 13.00 – 13.45 hrs | Scaling for Growth: Building Out a Process that Works Today and Tomorrow | Sunil Varkey
- 13.45 – 14.30 hrs | Panel Discussion | Hugh Thompson Bryce Boland Sunil Varkey Leon Miri Ronnie Islam Philip Lee Freddy Tan
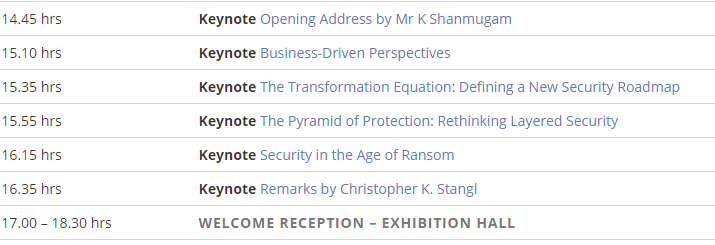
下午有6场keynotes,分别是:
详细信息如下:
key-w04 Keynote Speaker, Minister for Home Affairs & Minister for Law, Singapore (内务)外交部长
Mr K Shanmugam.
缺少description信息。cyber-crime 造成的损失, cyber-space
train our people work better in the syber space
2045, reach out
second, agency, meet & deal challege. command cyber criminals, shape prevention, CRDs. legislation
patner work with industry malware. late this year.
commit to fight cyber . China gov what?
key-w05 Business-Driven Perspectives . Amit Yoran, President, RSA
Today's security challenges can seem too large, too broad and too numerous for even the most talented teams to tackle. But what is lacking is a sharper perspective, viewing the problems from a diverse point of view and with technologies that can deliver at scale. This talk will challenge your perspective and discuss how advanced organizations are tackling cyber.
当前的安全挑战太大,范围太广,数量无穷,即使是最厉害的团队都很难处理。我们缺少的是什么呢?一种更犀利的视角,通过发散思维、利用可以大规模部署的技术手段 来看待问题。本次演讲将挑战你的视角并讨论如何提高组织的电子化处理水平。
over 5000 attenders
talk about perspective
perspective design action
Dick Fosbury, high jumper. example, 1936. Why not change the way you jump. A new way to jump. shock people's eye.
World wide cybersecurity spend 7.5Billion
Perspective is everything.
what you do matters. preciate the difference.
key-w06 The Transformation Equation: Defining a New Security Roadmap. Matthew Alderman, VP, Global strategy, Tenable Network security.
The security industry is robust and growing rapidly, with hundreds of technologies to address new challenges and attack vectors. But even companies heavily invested in leading solutions are still being breached. No matter what security solutions you deploy, if they don't work together, your organization is at risk. How do you change your approach? It's time to define a new security roadmap.
就算是重金投入了顶级解决方案的企业,也依然被攻陷。不管你部署了怎样的安全方案,如果它们不能协同工作,你的组织就还是处在风险之中。如何改变方法呢?是时候来重新定义新的security roadmap了。 (安全路线图)
waves of change
IT infrastructure migrateds to the Cloud
52% GE move to amazon
Applications are the Future, Security are behind
Traditional Endpoints are Dead
layered security creates Gaps: time for a new approach
Transforming SecurityBridging the Gaps
key-w07: The Pyramid of Protection: Rethinking Layered Security. Ben Johnson, Co-Founder & Chief Security Strategist, Carbon Black.
With the current cybersecurity climate, organizations are rebuilding or upgrading their security programs. But what should they be doing, and what have the successful teams done? This session will discuss architecting your cyberstrategy around a pyramid of capabilities versus categories of technologies. The discussion will focus on uniting man and machine, and on doing more with less.
防护金字塔:重新思考分层安全
企业应该做什么?成功的团队已经做了什么?本session将谈谈如何构建你的网络策略,能力金字塔VS技术分类。讨论内容将关注与如何将人与机器组合起来,以及事半功倍。
NSA 前雇员
Capability no category
时间都去哪儿了?(一张文字云图)
team of man-machine:
you cannot know everything ahead of time
Orchestration ?(P) 和谐的结合
collaborate, share, learn, evolve.
let engineer be more creative
how are we/ our team spending time.
What's essential?
key-w08: Security in the Age of Ransom, Chris Carlson, VP of Product Management, Qualys
This is the Age of Ransom! An age where global enterprises are brought to their knees by sophisticated, unrelenting attacks by criminal elements. Chris Carlson will expose the fatal flaws in today's antiquated systems, while investigating how risk and security professionals can take action. He'll make the urgent case for rapid migration to a new paradigm of continuous monitoring, visibility and response.
勒索时代的安全。复杂的、精细的、无情的犯罪分子袭击。 CC将曝光当前过时系统的致命弱点。
BBC:university pays $20,000 to ransomware hackers
Wired: Why Hospitals are the perfect Targets for ransomware.
DNA(Digital News Asis) Ransomware Back with a vengeance, Singapore is a target
Solution: Preven t / Restore / Protect
Stripe:条纹,种类。
Gartner TOP 10 Strategic technology trends 2016
Continuous Security Solutions: Visibility/ Monitoring / Response
key-w09: Remarks by Christopher K. Stangl, Christopher K. Stangl, Section Chief, Federal Bureau of Investigation, Cyber Division, Cyber Operations Section V. 联邦调查局(FBI)网络部门,网络运维5部,主管。
remark:评论,摘要,附注。
confronting
跟国内的某大会常见网警类似,干货没有,聊聊法规和段子而已。
插曲:这哥们的议题是临时安排的,会议材料有张A4纸单独进行了update说明。看来都喜欢找FBI糊人。
来自为知笔记(Wiz)