本文主要是介绍取出/var/log/secure中一小时内登录失败超过三次的IP,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
取出/var/log/secure中一小时内登录失败超过三次的IP
前两个字段是日期,第三个字段是小时,第四个字段是IP
cat /var/log/secure | sort -i | awk -F '[ :]' '/Failed/{a[$1" "$2" "$3" "$4" "$(NF-3)]++}END{for(i in a)if(a[i]>3)print i}'
s="Jul 7 13:49:08"
sed -n "/$s/,$ p" /var/log/secure | awk '/Failed/{a[$(NF-3)]++}END{for(b in a){if(a[b]>2){print b}}}'
统计/var/log/secure日志中出现“Failed”关键词的IP地址及次数。
···
awk 是三剑客中一把利刃。
cat /var/log/secure
Jul 18 10:28:59 sshd[1377656]: Accepted password for root from 172.16.100.66 port 59750 ssh2
Jul 18 10:28:59 sshd[1377656]: pam_unix(sshd:session): session opened for user root by (uid=0)
Jul 18 10:38:20 sshd[1416681]: Accepted password for root from 172.16.100.21 port 62366 ssh2
Jul 18 10:38:20 sshd[1416681]: pam_unix(sshd:session): session opened for user root by (uid=0)
Jul 18 10:58:57 sshd[1502199]: Accepted password for root from 172.16.100.66 port 61038 ssh2
# 可以看到正常的一个访问日志记录,新建一个连接 故意输错密码,让日志记录一下
Jul 18 10:59:13 sshd[1503821]: Failed password for root from 172.16.100.21 port 63802 ssh2
#可以看到错误登陆时的日志记录是这样的。
那么就可以开始使用awk来实现二级标题中的需要了。
先给出命令再来解析
awk '/Failed/ {++ip[$(NF-3)]} END {for (i in ip) print i"="ip[i]}'
一、登录ssh失败次数统计
1)错误的打开方式
awk '/Failed password/ {print $(NF-3)}' secure |sort -n |uniq -c|sort -n |tail /var/log/secure
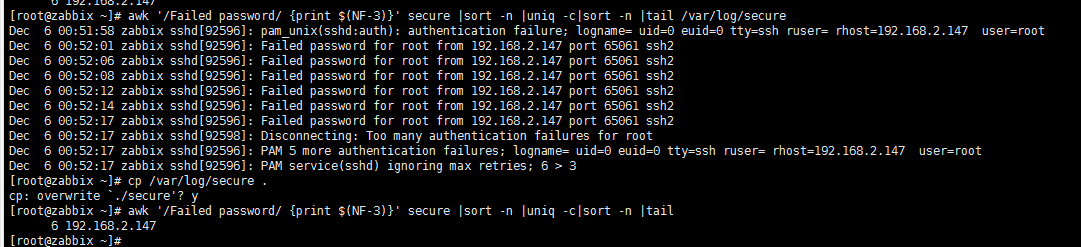
2)拷贝文件,再查看失败
cp /var/log/secure .
awk '/Failed password/ {print $(NF-3)}' secure |sort -n |uniq -c|sort -n |tail
3)直接查看失败
![]()
$ awk '/Failed password/ {print $(NF-3)}' /var/log/secure |sort -n |uniq -c|sort -n
4)查看最近失败的时间
less /var/log/secure
按G
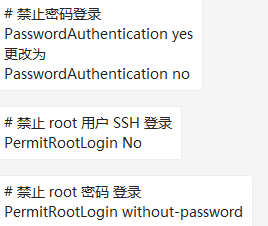
二、对于防破解问题的处理
1)禁止密码登录方式
vi /etc/ssh/sshd_config
2)禁止失败的IP登录的方式
![]()
![]()
# # hosts.deny This file contains access rules which are used to # deny connections to network services that either use # the tcp_wrappers library or that have been # started through a tcp_wrappers-enabled xinetd. # # The rules in this file can also be set up in # /etc/hosts.allow with a 'deny' option instead. # # See 'man 5 hosts_options' and 'man 5 hosts_access' # for information on rule syntax. # See 'man tcpd' for information on tcp_wrappers # sshd:192.168.2.41:deny
/etc/hosts.deny
在/etc/hosts.deny文件下面
添加 sshd:192.168.2.41:deny
重启sshd
Linux 系统SSH 登录失败的内容会记录到/var/log/secure文件,通过查找关键字 Failed,可以定位到这些异常的IP地址,比如:
[root@www.cndba.cn ~]# cat /var/log/secure|grep 36.250.229.118
Jan 10 16:54:25 iZbp15upsrdbnwnq3zksepZ sshd[10813]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:25 iZbp15upsrdbnwnq3zksepZ sshd[10813]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:27 iZbp15upsrdbnwnq3zksepZ sshd[10813]: Failed password for root from 103.152.101.235 port 59352 ssh2
Jan 10 16:54:27 iZbp15upsrdbnwnq3zksepZ sshd[10813]: Connection closed by 103.152.101.235 port 59352 [preauth]
Jan 10 16:54:29 iZbp15upsrdbnwnq3zksepZ sshd[10820]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:29 iZbp15upsrdbnwnq3zksepZ sshd[10820]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:31 iZbp15upsrdbnwnq3zksepZ sshd[10820]: Failed password for root from 103.152.101.235 port 60970 ssh2
Jan 10 16:54:31 iZbp15upsrdbnwnq3zksepZ sshd[10820]: Connection closed by 103.152.101.235 port 60970 [preauth]
Jan 10 16:54:33 iZbp15upsrdbnwnq3zksepZ sshd[10825]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:33 iZbp15upsrdbnwnq3zksepZ sshd[10825]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:35 iZbp15upsrdbnwnq3zksepZ sshd[10825]: Failed password for root from 103.152.101.235 port 34445 ssh2
Jan 10 16:54:35 iZbp15upsrdbnwnq3zksepZ sshd[10825]: Connection closed by 103.152.101.235 port 34445 [preauth]
Jan 10 16:54:37 iZbp15upsrdbnwnq3zksepZ sshd[10831]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:37 iZbp15upsrdbnwnq3zksepZ sshd[10831]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:39 iZbp15upsrdbnwnq3zksepZ sshd[10831]: Failed password for root from 103.152.101.235 port 36166 ssh2
Jan 10 16:54:39 iZbp15upsrdbnwnq3zksepZ sshd[10831]: Connection closed by 103.152.101.235 port 36166 [preauth]
Jan 10 16:54:41 iZbp15upsrdbnwnq3zksepZ sshd[10836]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:41 iZbp15upsrdbnwnq3zksepZ sshd[10836]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:43 iZbp15upsrdbnwnq3zksepZ sshd[10836]: Failed password for root from 103.152.101.235 port 37866 ssh2
Jan 10 16:54:43 iZbp15upsrdbnwnq3zksepZ sshd[10836]: Connection closed by 103.152.101.235 port 37866 [preauth]
Jan 10 16:54:45 iZbp15upsrdbnwnq3zksepZ sshd[10841]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:45 iZbp15upsrdbnwnq3zksepZ sshd[10841]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:47 iZbp15upsrdbnwnq3zksepZ sshd[10841]: Failed password for root from 103.152.101.235 port 39832 ssh2
Jan 10 16:54:47 iZbp15upsrdbnwnq3zksepZ sshd[10841]: Connection closed by 103.152.101.235 port 39832 [preauth]
Jan 10 16:54:49 iZbp15upsrdbnwnq3zksepZ sshd[10847]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=103.152.101.235 user=root
Jan 10 16:54:49 iZbp15upsrdbnwnq3zksepZ sshd[10847]: pam_succeed_if(sshd:auth): requirement "uid >= 1000" not met by user "root"
Jan 10 16:54:51 iZbp15upsrdbnwnq3zksepZ sshd[10847]: Failed password for root from 103.152.101.235 port 41558 ssh2
Jan 10 16:54:52 iZbp15upsrdbnwnq3zksepZ sshd[10847]: Connection closed by 103.152.101.235 port 41558 [preauth]
比如这里,明显这个IP地址在进行SSH 扫描,不断的更换端口和用户进行暴力测试。
在Linux里面有两个相关的文件:
/etc/hosts.allow: 允许哪些IP访问主机
cat /etc/hosts.allow
sshd:19.16.18.1:allow
sshd:19.16.18.2:allow
/etc/hosts.deny 禁止哪些IP访问主机:
cat /etc/hosts.deny
sshd:13.7.3.6:deny
sshd:92.4.0.4:deny
sshd:94.10.4.2:deny
sshd:94.4.1.6:deny
sshd:11.64.11.5:deny
因此,我们只需要从/var/log/secure文件中提取IP地址,如果次数达到10次则将该IP写到 /etc/hosts.deny中,禁止这些IP访问主机。
脚本如下secure_ssh.sh:
#! /bin/bash
cat /var/log/secure|awk '/Failed/{print $(NF-3)}'|sort|uniq -c|awk '{print $2"="$1;}' > /boss/config/black.list
for i in `cat /boss/config/black.list`
do
IP=`echo $i |awk -F= '{print $1}'`
NUM=`echo $i|awk -F= '{print $2}'`
echo $IP=$NUM
if [ $NUM -gt 10 ]; then
grep $IP /etc/hosts.deny > /dev/null
if [ $? -gt 0 ];then
echo "sshd:$IP:deny" >> /etc/hosts.deny
fi
fi
done
将secure_ssh.sh脚本放入cron计划任务,每1小时执行一次。
# crontab -e
0 */1 * * * sh /usr/local/bin/secure_ssh.sh
1 CentOS7通过定时脚本阻断异常IP连接SSH(实测)_secure_ssh.sh-CSDN博客
这篇关于取出/var/log/secure中一小时内登录失败超过三次的IP的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!






