本文主要是介绍我实践:wireguard多场景安装配置指导.md,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
我实践:wireguard多场景安装配置指导.md
文章目录
- 我实践:wireguard多场景安装配置指导.md
- 介绍
- 安装
- 配置
- server
- client
- 使用场景
- 场景1:PC-to-LAN
- 场景2:LAN-to-LAN
- 手机端
- 防火墙策略
- 日常使用
- 客户端使用wg-quick的反应
- 配置文件解析
- 另:ip rule,ip route,iptables 三者之间的关系
- wg-quick
- wg
介绍
wireguard与openVPN、strongswanVPN、ipsecVPN的优劣请自行百度,总的一句wireguard很好用,配置简单,短小精悍,Linus很喜欢,多平台支持,你值得拥有。唯一不好的是可能容易被墙。
本文主要介绍在几种场景下的配置方法。
安装
参考:
https://www.wireguard.com/install/
https://www.wireguard.com/quickstart/
以下为在centos下的安装方法:
yum update -y
yum install epel-release https://www.elrepo.org/elrepo-release-7.el7.elrepo.noarch.rpm
yum install yum-plugin-elrepo
yum install kmod-wireguard wireguard-tools
reboot
配置
服务器信息:
公网信息:5.5.5.5:51820 (dnat)
vpn peer ip: 172.30.0.1
服务器内部网段:10.1.0.0/16
公钥: dLssYxxxxxxxxxxxxxxxxxZq98NQKOivi3MN/VM=
客户端信息:
客户端在adsl内网,不能公网访问
vpn peer ip: 172.30.0.2
客户端内部网段:192.168.0.0/16
公钥: PTr03Yp2MxxxxxxxxxxxxxxxxxFwVRUl2ZNXfLTA=
server
# 1、设置网卡
ip link add wg0 type wireguard # 自动处理内核模块加载
ip address add 172.30.0.1/24 dev wg0# 2、生成秘钥
wg genkey > private.key
wg pubkey < private.key # 查看公钥># 用法:Usage: wg set <interface> [listen-port <port>] [fwmark <mark>] [private-key <file path>] [peer <base64 public key> [remove] [preshared-key <file path>] [endpoint <ip>:<port>] [persistent-keepalive <interval seconds>] [allowed-ips <ip1>/<cidr1>[,<ip2>/<cidr2>]...] ]...# 3、设置本地wg0网卡侦听端口与私钥
wg set wg0 listen-port 51820 private-key ./private.key# 4、设置客户端公钥及允许客户端访问服务器的ip范围,多个时以逗号分隔(客户端需要生成相关信息才可执行下面的命令,方法同上);设置保持连接(peer在nat防火墙后面的或者是动态地址的需要加上,服务器端一般有固定地址,所以不需要)
wg set wg0 peer PTr03Yp2Mhd2GEUN2KjrRJMVAn0JbFwVRUl2ZNXfLTA= allowed-ips 172.30.0.2/32# 5、激活网卡
ip link set wg0 up
wg
client
# 1、设置网卡
ip link add wg0 type wireguard # 自动处理内核模块加载
ip address add 172.30.0.2/24 dev wg0# 2、生成秘钥
wg genkey > private.key
wg pubkey < private.key # 查看公钥># 3、设置本地wg0网卡侦听端口与私钥,侦听端口不用设置,因为客户端不需要被别人主动连接,会自动使用一个随机端口
wg set wg0 private-key ./private.key
# 以上部分和服务器端设置是一样的# 4、设置服务器端公钥;设置允许服务器访问客户端的ip范围(服务器端需要生成相关信息才可执行下面的命令);设置保持连接(nat防火墙后面需要加上);设置服务器地址与端口
wg set wg0 peer dLssY8xxxxxxxxxxxxxxxxx8NQKOivi3MN/VM= persistent-keepalive 25 allowed-ips 172.30.0.1/32 endpoint 5.5.5.5:51820# 5、激活网卡
ip link set wg0 up
wg
使用场景
前面只是点到点的基本场景,是最简单的使用场景,下面我们再探讨下其他使用场景
场景1:PC-to-LAN
# 允许客户端访问服务器端所有局域网(即PC-to-LAN,一般采用这种模式)
# 基于基本场景还需执行以下设置:## on server:
# 添加vpn网段路由到服务器端企业路由器
# 172.30.0.0/24 via [本机的局域网ip]## on client:
# 添加server端网段到本机路由表
ip route add 10.1.0.0/16 via 172.30.0.1
...
# 允许server端网络访问client端(无需ip link down + up;这里0.0.0.0/0代表所有网络)
wg set wg0 peer dLssxxxxxxxxxxxxxxxxxq98NQKOivi3MN/VM= persistent-keepalive 25 allowed-ips 172.30.0.1/32,0.0.0.0/0 endpoint 192.168.11.29:51820
场景2:LAN-to-LAN
# 将两边的局域网连成一个整体的局域网(即LAN-to-LAN)
# 基于基本场景还需执行以下设置:## on server:
# 添加vpn网段路由到服务器端企业路由器
# 172.30.0.0/24 via [本机的局域网ip]
# 添加client端网段路由到服务器端企业路由器
# 192.168.2.0/24 via [本机的局域网ip]
# ...
# 添加client端网段路由到本机路由表
ip route add 192.168.0.0/16 via 172.30.0.2
...
# 允许client端访问server端网络(无需ip link down + up)
wg set wg0 peer VbR3Kxgxxxxxxxxxxxxxxxxxzq3H4ebdgTng= allowed-ips 172.30.0.2/32,192.168.0.0/24## on client:
# 添加vpn网段路由到客户端企业路由器
# 172.30.0.0/24 via [本机的局域网ip]
# 添加server端网段路由到客户端企业路由器
# 10.1.0.0/16 via [本机的局域网ip]
# ...
# 添加server端网段路由到本机路由表
ip route add 10.1.0.0/16 via 172.30.0.1
...
# 允许server端访问client端网络(无需ip link down + up;0.0.0.0/0代表所有网络)
wg set wg0 peer dLssxxxxxxxxxxxxxxxxx98NQKOivi3MN/VM= persistent-keepalive 25 allowed-ips 172.30.0.1/32,0.0.0.0/0 endpoint 5.5.5.5:51820
手机端
- 路由的ip地址(段):就是allowed-ips,不仅仅是字面意义的路由表
- persistent-keepalive连接保活间隔建议开启:25,否则从服务器端ping手机端地址ping不通:
# ping 172.30.0.12
PING 172.30.0.12 (172.30.0.12) 56(84) bytes of data.
From 172.30.0.1 icmp_seq=1 Destination Host Unreachable
ping: sendmsg: Destination address required
- 其他:略
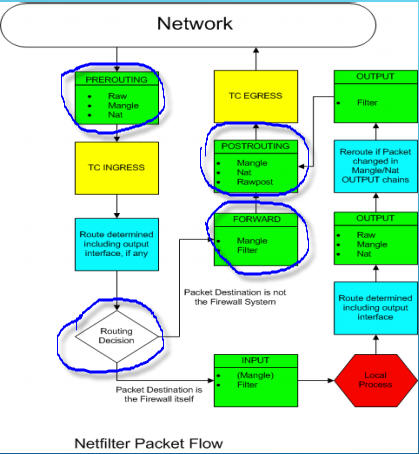
防火墙策略
# 如果server端启用了系统防火墙,比如:firewalld.service,你可能需要开启一些端口,比如:# 将网卡加入到public区域,默认策略允许ping:
firewall-cmd --zone=public --add-interface=wg0
# 开放wireguard侦听端口51820/udp
firewall-cmd --zone=public --add-port=51820/udp# 允许客户端172.30.0.2访问服务器端局域网的10.1.3.77:80
firewall-cmd --direct --add-rule ipv4 filter FORWARD 1 -p tcp -d 10.1.3.77 --dport 80 -s 172.30.0.2 -j ACCEPT
# 允许客户端172.30.0.2访问服务器端局域网的所有服务器的80端口
firewall-cmd --direct --add-rule ipv4 filter FORWARD 1 -p tcp --dport 80 -s 172.30.0.2 -j ACCEPT
# 允许客户端172.30.0.2访问服务器端局域网的所有服务器的所有端口
firewall-cmd --direct --add-rule ipv4 filter FORWARD 1 -p tcp -s 172.30.0.2 -j ACCEPT# 允许客户端172.30.0.2访问服务器端的81端口
firewall-cmd --add-rich-rule='rule family=ipv4 source address=172.30.0.2 port port=81 protocol=tcp accept'# 允许所有人访问服务器端的82端口
firewall-cmd --add-port=82/tcp
日常使用
用法:Usage: wg-quick [ up | down | save | strip ] [ CONFIG_FILE | INTERFACE ]
# 保存配置,这种指令行方式更加可控,最好不要直接编辑/etc/wireguard/wg0.conf中的配置文件
touch /etc/wireguard/wg0.conf
wg-quick save wg0#或: wg showconf wg0 > /etc/wireguard/wg0.conf #如果peer在nat后面的可能需要删除相关Endpoint信息,因为那是不能被主动访问的# 启动/停止
wg-quick up wg0 #自动选择配置文件'/etc/wireguard/wg0.conf'
wg-quick up /path/to/wg0.conf #指定路径
wg-quick down wg0# 删除peer
wg set wg0 peer $(cat cpublickey1) remove
客户端使用wg-quick的反应
他拥有wg没有的功能,wg-quick是一个sh脚本
以下是使用wg-quick前后的变化
# cat /etc/wireguard/wg5.conf
[Interface]
Address = 172.30.5.11/24
ListenPort = 52235
PrivateKey = kET16oZ4DOmsvflMxxxxxxxxxxxxxxxxxYZK0RdF0s=
DNS = 8.8.8.8
[Peer]
PublicKey = dLssY8S+xxxxxxxxxxxxxxxxxq98NQKOivi3MN/VM=
AllowedIPs = 0.0.0.0/0
Endpoint = 11.21.31.94:51820
PersistentKeepalive = 25
#
# wg-quick up wg5
[#] ip link add wg5 type wireguard
[#] wg setconf wg5 /dev/fd/63
[#] ip -4 address add 172.30.5.11/24 dev wg5
[#] ip link set mtu 1420 up dev wg5
[#] resolvconf -a tun.wg5 -m 0 -x
[#] wg set wg5 fwmark 51820
[#] ip -4 route add 0.0.0.0/0 dev wg5 table 51820
[#] ip -4 rule add not fwmark 51820 table 51820
[#] ip -4 rule add table main suppress_prefixlength 0
[#] sysctl -q net.ipv4.conf.all.src_valid_mark=1
[#] iptables-restore -n
#
# cat /etc/resolv.conf
# Dynamic resolv.conf(5) file for glibc resolver(3) generated by resolvconf(8)
# DO NOT EDIT THIS FILE BY HAND -- YOUR CHANGES WILL BE OVERWRITTEN
nameserver 8.8.8.8 #---新加的
nameserver 127.0.1.1
#
# ip rule list
0: from all lookup local
218: from all lookup main suppress_prefixlength 0 #---新加的
219: not from all fwmark 0xca6c lookup 51820 #---新加的,0xca6c即51820
32766: from all lookup main
32767: from all lookup default
#
# ip route list table 51820
default dev wg5 scope link #---新加的
#
# ip route list #---即:ip route list table main
default via 192.168.43.1 dev wlp2s0 proto static metric 600
172.17.0.0/16 dev docker0 proto kernel scope link src 172.17.0.1 linkdown
172.18.0.0/16 dev br-542d8a49cc45 proto kernel scope link src 172.18.0.1 linkdown
172.30.5.0/24 dev wg5 proto kernel scope link src 172.30.5.11 #---新加的
192.168.43.0/24 dev wlp2s0 proto kernel scope link src 192.168.43.19 metric 600
192.168.122.0/24 dev virbr0 proto kernel scope link src 192.168.122.1 linkdown
#
# iptables -t mangle -L
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
CONNMARK udp -- anywhere anywhere /* wg-quick(8) rule for wg5 */ CONNMARK restore #---新加的Chain INPUT (policy ACCEPT)
target prot opt source destination Chain FORWARD (policy ACCEPT)
target prot opt source destination Chain OUTPUT (policy ACCEPT)
target prot opt source destination Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
CONNMARK udp -- anywhere anywhere mark match 0xca6c /* wg-quick(8) rule for wg5 */ CONNMARK save #---新加的
CHECKSUM udp -- anywhere anywhere udp dpt:bootpc CHECKSUM fill
#
# wg-quick down wg5
[#] ip -4 rule delete table 51820
[#] ip -4 rule delete table main suppress_prefixlength 0
[#] ip link delete dev wg5
[#] resolvconf -d tun.wg5 -f
[#] iptables-restore -n
配置文件解析
参考:https://manpages.debian.org/unstable/wireguard-tools/wg-quick.8.en.html
文件默认路径为/etc/wireguard/,文件名为接口名.conf,比如wg0.conf
如下:
[Interface]
Address = 10.200.100.1/24 #接口IP(v4或v6),可以多次指定,逗号分隔
ListenPort = 51820 #侦听端口
PrivateKey = oK56DE9Uexxxxxxxxxxxxxxxxx6lm7cXXsQKrQM= #私钥
DNS = 8.8.8.8 #多个则以逗号分隔,增加dns服务器在/etc/resolv.conf中,通过resolvconf命令进行配置,需要安装此包
MTU = 1420 #设置mtu,默认为自动设置
#
# PreUp, PostUp, PreDown, PostDown : 里面的内容会在bash中执行,'%i'代表接口,这些都是wg-quick的功能
# 以加密形式存储私钥,例如通过使用pass(1):
PostUp = wg set %i private-key <(pass WireGuard/private-keys/%i)
#
# 当[peer]里设置了'AllowedIPs = 0.0.0.0/0'时,可能会被'kill-switch'攻击,为了防止非加密数据包通过non-WireGuard接口,添加以下两行:
PostUp = iptables -I OUTPUT ! -o %i -m mark ! --mark $(wg show %i fwmark) -m addrtype ! --dst-type LOCAL -j REJECT
PreDown = iptables -D OUTPUT ! -o %i -m mark ! --mark $(wg show %i fwmark) -m addrtype ! --dst-type LOCAL -j REJECT
#
# Table : 保存到哪个路由表。off|auto,“off”禁用路由的创建,“auto”(默认)将路由添加到默认表中,这是wg-quick的功能。
# Table,PostUp和PreDown字段的组合也可以用于策略路由
# 参考:https://www.cnblogs.com/EasonJim/p/8424731.html(Linux下ip route、ip rule、iptables的关系)
Table = 1234
PostUp = ip rule add ipproto tcp dport 22 table 1234
PreDown = ip rule delete ipproto tcp dport 22 table 1234
#
SaveConfig = false #如果设置为“true”,则在关闭时从接口的当前状态保存配置[Peer]
PublicKey = GtL7fZc/bLnqZldpxxxxxxxxxxxxxxxxxdLx+qtKU= #对端公钥
PresharedKey = /UwcSPgxxxxxxxxxxxxxxxxxuURMbS0sesJEP5ak= #设置两端[peer]预共享key,wg genpsk
AllowedIPs = 0.0.0.0/0 #对端可以访问的地址范围,如果多个则用逗号分隔。如果是0.0.0.0/0,则会自动添加ip rule,并配置为该rule的默认网关,这是wg-quick的功能
Endpoint = demo.wireguard.com:51820 #对端的地址信息,代表主动连接对端,客户端必须设置
PersistentKeepalive = 25 #保持连接
另:ip rule,ip route,iptables 三者之间的关系
参考:https://www.cnblogs.com/EasonJim/p/8424731.html
例:公司内网要求192.168.0.100 以内的使用 10.0.0.1 网关上网 (电信),其他IP使用 20.0.0.1 (网通)上网。
- 首先要在网关服务器上添加一个默认路由,当然这个指向是绝大多数的IP的出口网关:ip route add default gw 20.0.0.1
- 之后通过 ip route 添加一个路由表:ip route add table 3 via 10.0.0.1 dev ethX #—(ethx 是 10.0.0.1 所在的网卡, 3 是路由表的编号)
- 之后添加 ip rule 规则:ip rule add fwmark 3 table 3 #—(fwmark 3 是标记,table 3 是路由表3 上边。 意思就是凡事标记了 3 的数据使用 table3 路由表)
- 之后使用 iptables 给相应的数据打上标记:iptables -A PREROUTING -t mangle -i eth0 -s 192.168.0.1-192.168.0.100 -j MARK --set-mark 3
wg-quick
$ wg-quick --help
Usage: wg-quick [ up | down | save | strip ] [ CONFIG_FILE | INTERFACE ]CONFIG_FILE is a configuration file, whose filename is the interface namefollowed by '.conf'. Otherwise, INTERFACE is an interface name, withconfiguration found at /etc/wireguard/INTERFACE.conf. It is to be readableby wg(8)'s 'setconf' sub-command, with the exception of the following additionsto the [Interface] section, which are handled by wg-quick:- Address: may be specified one or more times and contains one or moreIP addresses (with an optional CIDR mask) to be set for the interface.- DNS: an optional DNS server to use while the device is up.- MTU: an optional MTU for the interface; if unspecified, auto-calculated.- Table: an optional routing table to which routes will be added; ifunspecified or 'auto', the default table is used. If 'off', no routesare added.- PreUp, PostUp, PreDown, PostDown: script snippets which will be executedby bash(1) at the corresponding phases of the link, most commonly usedto configure DNS. The string '%i' is expanded to INTERFACE.- SaveConfig: if set to 'true', the configuration is saved from the currentstate of the interface upon shutdown.
See wg-quick(8) for more info and examples.
wg
$ wg --help
Usage: wg <cmd> [<args>]Available subcommands:show: Shows the current configuration and device informationshowconf: Shows the current configuration of a given WireGuard interface, for use with 'setconf'set: Change the current configuration, add peers, remove peers, or change peerssetconf: Applies a configuration file to a WireGuard interfaceaddconf: Appends a configuration file to a WireGuard interfacesyncconf: Synchronizes a configuration file to a WireGuard interfacegenkey: Generates a new private key and writes it to stdoutgenpsk: Generates a new preshared key and writes it to stdoutpubkey: Reads a private key from stdin and writes a public key to stdout
You may pass '--help' to any of these subcommands to view usage.$ wg setconf --help
Usage: wg setconf <interface> <configuration filename>wg addconf wg0 <(wg-quick strip wg0) # ??
这篇关于我实践:wireguard多场景安装配置指导.md的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!



