本文主要是介绍Ed25519算法,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
Curve25519/Ed25519/X25519 是著名密码学家 Daniel J. Bernstein 在 2006 年独立设计的椭圆曲线加密 /签名 /密钥交换算法,和现有的任何椭圆曲线算法都完全独立,其中Ed25519用于签名,可在区块链中进行签名,Stellar就是使用了Ed25519作为签名算法的
1. Curve25519
http://cr.yp.to/ecdh.htmlCurve25519 是目前最高水平的 Diffie-Hellman函数,适用于广泛的场景,由Daniel J. Bernstein教授设计。由于NIST P-256的设计过程不透明,有来历不明的参数,被广泛怀疑有后门,所以设计了Curve25519,Curve25519的设计过程完全公开,没有任何来历不明的参数。 部署情况:http://ianix.com/pub/curve25519-deployment.html
2.Ed25519
http://ed25519.cr.yp.to/Ed25519是一个数字签名算法,签名和验证的性能都极高, 一个4核2.4GHz 的 Westmere cpu,每秒可以验证 71000 个签名,安全性极高,等价于RSA约3000-bit。签名过程不依赖随机数生成器,不依赖hash函数的防碰撞性,没有时间通道攻击的问题,并且签名很小,只有64字节,公钥也很小,只有32字节。 部署情 况:http://ianix.com/pub/ed25519-deployment.html
3. 前向安全性
前向安全性( Perfect Forward Secrecy )http://vincent.bernat.im/en/blog/2011-ssl-perfect-forward-secrecy.html前向安全性指的是,如果攻击者抓取并保存流量,那么将来私钥泄露后,攻击者也无法利用泄露的私钥解密这些流量。
25519 系列曲线自 2006 年发表以来,除了学术界无人问津, 2013 年爱德华·斯诺登曝光棱镜计划后,该算法突然大火,大量软件,如 OpenSSH 都迅速增加了对 25519 系列的支持,如今 25519 已经是大势所趋,可疑的 NIST 曲线迟早要退出椭圆曲线的历史舞台,目前, RFC 增加了 SSL/TLS 对 X25519 密钥交换协议的支持,而新版 OpenSSL 1.1 也加入支持,是摆脱老大哥的第一步,下一步是将 Ed25519 做为可选的 TLS 证书签名算法,彻底摆脱 NIST 。
根据其网站介绍,Ed25519算法具有以下优势:
玩全开放设计,算法各参数的选择直截了当,非常明确,没有任何可疑之处,相比之下目前广泛使用的椭圆曲线是 NIST 系列标准,方程的系数是使用来历不明的随机种子 c49d3608 86e70493 6a6678e1 139d26b7 819f7e90 生成的,至于这个种子的来历没有资料介绍;
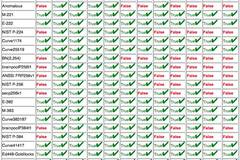
安全性高,一个椭圆曲线加密算法就算在数学上是安全的,在实用上也并不一定安全,有很大的概率通过缓存、时间、恶意输入摧毁安全性,而 25519 系列椭圆曲线经过特别设计,尽可能的将出错的概率降到了最低,可以说是实践上最安全的加密算法。例如,任何一个 32 位随机数都是一个合法的 X25519 公钥,因此通过恶意数值攻击是不可能的,算法在设计的时候刻意避免的某些分支操作,这样在编程的时候可以不使用 if ,减少了不同 if 分支代码执行时间不同的时序攻击概率,相反, NIST 系列椭圆曲线算法在实际应用中出错的可能性非常大,而且对于某些理论攻击的免疫能力不高, Bernstein 对市面上所有的加密算法使用 12 个标准进行了考察, 25519 是几乎唯一满足这些标准的,以下是评价的截图,具体可以看网站 https://safecurves.cr.yp.to/index.html
速度快, 25519 系列曲线是目前最快的椭圆曲线加密算法,性能远远超过 NIST 系列,而且具有比 P-256 更高的安全性;
以下是其网站的介绍,都是比较简单的英语描述,最近事情太多,实在来不及翻译了,偷下懒
Fast single-signature verification.The softwaretakes only 273364 cycles to verify a signature on Intel's widely deployed Nehalem/Westmere lines of CPUs. (This performance measurement is for short messages; for very long messages, verification time is dominated by hashing time.) Nehalem and Westmere include all Core i7, i5, and i3 CPUs released between 2008 and 2010, and most Xeon CPUs released in the same period.
Even faster batch verification.The software performs a batch of 64 separate signature verifications (verifying 64 signatures of 64 messages under 64 public keys) in only 8.55 million cycles, i.e., under 134000 cycles per signature. The software fits easily into L1 cache, so contention between cores is negligible: a quad-core 2.4GHz Westmere verifies 71000 signatures per second, while keeping the maximum verification latency below 4 milliseconds.
Very fast signing.The software takes only 87548 cycles to sign a message. A quad-core 2.4GHz Westmere signs 109000 messages per second.
Fast key generation.Key generation is almost as fast as signing. There is a slight penalty for key generation to obtain a secure random number from the operating system;/dev/urandomunder Linux costs about 6000 cycles.
High security level.This system has a 2^128 security target; breaking it has similar difficulty to breaking NIST P-256, RSA with ~3000-bit keys, strong 128-bit block ciphers, etc. The best attacks known actually cost more than 2^140 bit operations on average, and degrade quadratically in success probability as the number of bit operations drops.
Foolproof session keys.Signatures are generated deterministically; key generation consumes new randomness but new signatures do not. This is not only a speed feature but also a security feature, directly relevant to the recent collapse of the Sony PlayStation 3 security system.
Collision resilience.Hash-function collisions do not break this system. This adds a layer of defense against the possibility of weakness in the selected hash function.
No secret array indices.The software never reads or writes data from secret addresses in RAM; the pattern of addresses is completely predictable. The software is therefore immune to cache-timing attacks, hyperthreading attacks, and other side-channel attacks that rely on leakage of addresses through the CPU cache.
No secret branch conditions.The software never performs conditional branches based on secret data; the pattern of jumps is completely predictable. The software is therefore immune to side-channel attacks that rely on leakage of information through the branch-prediction unit.
Small signatures.Signatures fit into 64 bytes. These signatures are actually compressed versions of longer signatures; the times for compression and decompression are included in the cycle counts reported above.
Small keys.Public keys consume only 32 bytes. The times for compression and decompression are again included.
博主QQ: 122209017
这篇关于Ed25519算法的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!









