本文主要是介绍Python解包及反编译: PyInstaller Extractor+uncompyle6,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
Python解包及反编译: PyInstaller Extractor+uncompyle6
文章目录
- Python解包及反编译: PyInstaller Extractor+uncompyle6
- 一、前言
- 二、PyInstaller Extractor解包
- 1、安装pyinstxtractor
- 2、解包
- 三、反编译uncompyle6工具使用
- 1、pip安装uncompyle6
- 2、找到主文件并编译
- 3、解压完成查看源码
- 四、一键解包并编译
一、前言
有时候会遇到一些人制作一键安装包的时候会把一些程序封装进exe里面,但我们又想拿到里面源码的情况。在这里就涉及到了解包与反编译的。
二、PyInstaller Extractor解包
目前的python主流的打包方式是使用pyinstaller,针对这种情况可以使用pyinstaller Extractor进行解包。
- 前提
- 使用pyinstaller进行打包
- 未加密
1、安装pyinstxtractor
新建一个py文件pyinstxtractor.py,然后将下面的内容拷贝进去
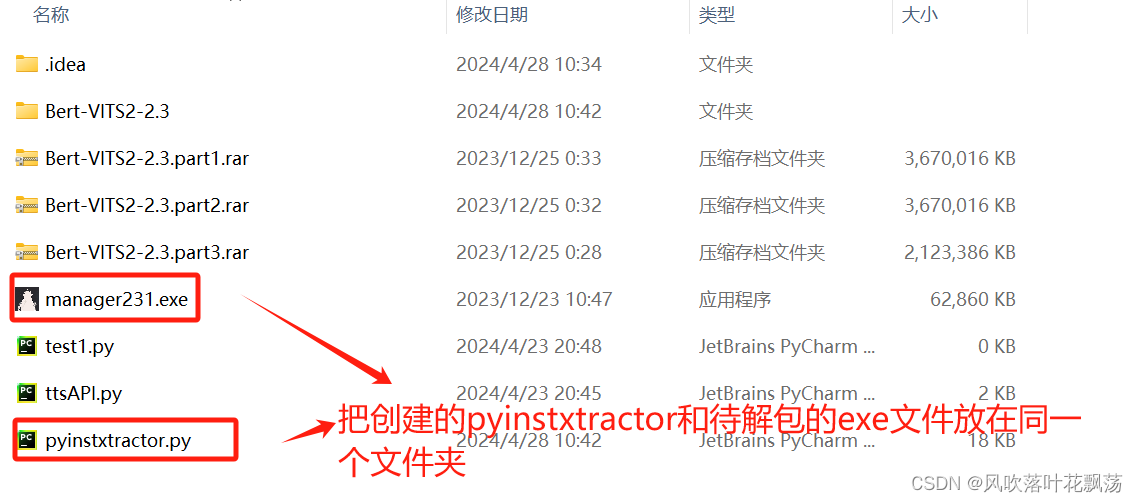
然后就安装好了,要使用的时候与待解包的exe文件放在同一文件夹即可
"""
PyInstaller Extractor v2.0 (Supports pyinstaller 6.6.0, 6.5.0, 6.4.0, 6.3.0, 6.2.0, 6.1.0, 6.0.0, 5.13.2, 5.13.1, 5.13.0, 5.12.0, 5.11.0, 5.10.1, 5.10.0, 5.9.0, 5.8.0, 5.7.0, 5.6.2, 5.6.1, 5.6, 5.5, 5.4.1, 5.4, 5.3, 5.2, 5.1, 5.0.1, 5.0, 4.10, 4.9, 4.8, 4.7, 4.6, 4.5.1, 4.5, 4.4, 4.3, 4.2, 4.1, 4.0, 3.6, 3.5, 3.4, 3.3, 3.2, 3.1, 3.0, 2.1, 2.0)
Author : Extreme Coders
E-mail : extremecoders(at)hotmail(dot)com
Web : https://0xec.blogspot.com
Date : 26-March-2020
Url : https://github.com/extremecoders-re/pyinstxtractorFor any suggestions, leave a comment on
https://forum.tuts4you.com/topic/34455-pyinstaller-extractor/This script extracts a pyinstaller generated executable file.
Pyinstaller installation is not needed. The script has it all.For best results, it is recommended to run this script in the
same version of python as was used to create the executable.
This is just to prevent unmarshalling errors(if any) while
extracting the PYZ archive.Usage : Just copy this script to the directory where your exe residesand run the script with the exe file name as a parameterC:\\path\\to\\exe\\>python pyinstxtractor.py <filename>
$ /path/to/exe/python pyinstxtractor.py <filename>Licensed under GNU General Public License (GPL) v3.
You are free to modify this source.CHANGELOG
================================================Version 1.1 (Jan 28, 2014)
-------------------------------------------------
- First Release
- Supports only pyinstaller 2.0Version 1.2 (Sept 12, 2015)
-------------------------------------------------
- Added support for pyinstaller 2.1 and 3.0 dev
- Cleaned up code
- Script is now more verbose
- Executable extracted within a dedicated sub-directory(Support for pyinstaller 3.0 dev is experimental)Version 1.3 (Dec 12, 2015)
-------------------------------------------------
- Added support for pyinstaller 3.0 final
- Script is compatible with both python 2.x & 3.x (Thanks to Moritz Kroll @ Avira Operations GmbH & Co. KG)Version 1.4 (Jan 19, 2016)
-------------------------------------------------
- Fixed a bug when writing pyc files >= version 3.3 (Thanks to Daniello Alto: https://github.com/Djamana)Version 1.5 (March 1, 2016)
-------------------------------------------------
- Added support for pyinstaller 3.1 (Thanks to Berwyn Hoyt for reporting)Version 1.6 (Sept 5, 2016)
-------------------------------------------------
- Added support for pyinstaller 3.2
- Extractor will use a random name while extracting unnamed files.
- For encrypted pyz archives it will dump the contents as is. Previously, the tool would fail.Version 1.7 (March 13, 2017)
-------------------------------------------------
- Made the script compatible with python 2.6 (Thanks to Ross for reporting)Version 1.8 (April 28, 2017)
-------------------------------------------------
- Support for sub-directories in .pyz files (Thanks to Moritz Kroll @ Avira Operations GmbH & Co. KG)Version 1.9 (November 29, 2017)
-------------------------------------------------
- Added support for pyinstaller 3.3
- Display the scripts which are run at entry (Thanks to Michael Gillespie @ malwarehunterteam for the feature request)Version 2.0 (March 26, 2020)
-------------------------------------------------
- Project migrated to github
- Supports pyinstaller 3.6
- Added support for Python 3.7, 3.8
- The header of all extracted pyc's are now automatically fixed
"""from __future__ import print_function
import os
import struct
import marshal
import zlib
import sys
from uuid import uuid4 as uniquenameclass CTOCEntry:def __init__(self, position, cmprsdDataSize, uncmprsdDataSize, cmprsFlag, typeCmprsData, name):self.position = positionself.cmprsdDataSize = cmprsdDataSizeself.uncmprsdDataSize = uncmprsdDataSizeself.cmprsFlag = cmprsFlagself.typeCmprsData = typeCmprsDataself.name = nameclass PyInstArchive:PYINST20_COOKIE_SIZE = 24 # For pyinstaller 2.0PYINST21_COOKIE_SIZE = 24 + 64 # For pyinstaller 2.1+MAGIC = b'MEI\014\013\012\013\016' # Magic number which identifies pyinstallerdef __init__(self, path):self.filePath = pathself.pycMagic = b'\0' * 4self.barePycList = [] # List of pyc's whose headers have to be fixeddef open(self):try:self.fPtr = open(self.filePath, 'rb')self.fileSize = os.stat(self.filePath).st_sizeexcept:print('[!] Error: Could not open {0}'.format(self.filePath))return Falsereturn Truedef close(self):try:self.fPtr.close()except:passdef checkFile(self):print('[+] Processing {0}'.format(self.filePath))searchChunkSize = 8192endPos = self.fileSizeself.cookiePos = -1if endPos < len(self.MAGIC):print('[!] Error : File is too short or truncated')return Falsewhile True:startPos = endPos - searchChunkSize if endPos >= searchChunkSize else 0chunkSize = endPos - startPosif chunkSize < len(self.MAGIC):breakself.fPtr.seek(startPos, os.SEEK_SET)data = self.fPtr.read(chunkSize)offs = data.rfind(self.MAGIC)if offs != -1:self.cookiePos = startPos + offsbreakendPos = startPos + len(self.MAGIC) - 1if startPos == 0:breakif self.cookiePos == -1:print('[!] Error : Missing cookie, unsupported pyinstaller version or not a pyinstaller archive')return Falseself.fPtr.seek(self.cookiePos + self.PYINST20_COOKIE_SIZE, os.SEEK_SET)if b'python' in self.fPtr.read(64).lower():print('[+] Pyinstaller version: 2.1+')self.pyinstVer = 21 # pyinstaller 2.1+else:self.pyinstVer = 20 # pyinstaller 2.0print('[+] Pyinstaller version: 2.0')return Truedef getCArchiveInfo(self):try:if self.pyinstVer == 20:self.fPtr.seek(self.cookiePos, os.SEEK_SET)# Read CArchive cookie(magic, lengthofPackage, toc, tocLen, pyver) = \struct.unpack('!8siiii', self.fPtr.read(self.PYINST20_COOKIE_SIZE))elif self.pyinstVer == 21:self.fPtr.seek(self.cookiePos, os.SEEK_SET)# Read CArchive cookie(magic, lengthofPackage, toc, tocLen, pyver, pylibname) = \struct.unpack('!8sIIii64s', self.fPtr.read(self.PYINST21_COOKIE_SIZE))except:print('[!] Error : The file is not a pyinstaller archive')return Falseself.pymaj, self.pymin = (pyver//100, pyver%100) if pyver >= 100 else (pyver//10, pyver%10)print('[+] Python version: {0}.{1}'.format(self.pymaj, self.pymin))# Additional data after the cookietailBytes = self.fileSize - self.cookiePos - (self.PYINST20_COOKIE_SIZE if self.pyinstVer == 20 else self.PYINST21_COOKIE_SIZE)# Overlay is the data appended at the end of the PEself.overlaySize = lengthofPackage + tailBytesself.overlayPos = self.fileSize - self.overlaySizeself.tableOfContentsPos = self.overlayPos + tocself.tableOfContentsSize = tocLenprint('[+] Length of package: {0} bytes'.format(lengthofPackage))return Truedef parseTOC(self):# Go to the table of contentsself.fPtr.seek(self.tableOfContentsPos, os.SEEK_SET)self.tocList = []parsedLen = 0# Parse table of contentswhile parsedLen < self.tableOfContentsSize:(entrySize, ) = struct.unpack('!i', self.fPtr.read(4))nameLen = struct.calcsize('!iIIIBc')(entryPos, cmprsdDataSize, uncmprsdDataSize, cmprsFlag, typeCmprsData, name) = \struct.unpack( \'!IIIBc{0}s'.format(entrySize - nameLen), \self.fPtr.read(entrySize - 4))try:name = name.decode("utf-8").rstrip("\0")except UnicodeDecodeError:newName = str(uniquename())print('[!] Warning: File name {0} contains invalid bytes. Using random name {1}'.format(name, newName))name = newName# Prevent writing outside the extraction directoryif name.startswith("/"):name = name.lstrip("/")if len(name) == 0:name = str(uniquename())print('[!] Warning: Found an unamed file in CArchive. Using random name {0}'.format(name))self.tocList.append( \CTOCEntry( \self.overlayPos + entryPos, \cmprsdDataSize, \uncmprsdDataSize, \cmprsFlag, \typeCmprsData, \name \))parsedLen += entrySizeprint('[+] Found {0} files in CArchive'.format(len(self.tocList)))def _writeRawData(self, filepath, data):nm = filepath.replace('\\', os.path.sep).replace('/', os.path.sep).replace('..', '__')nmDir = os.path.dirname(nm)if nmDir != '' and not os.path.exists(nmDir): # Check if path exists, create if notos.makedirs(nmDir)with open(nm, 'wb') as f:f.write(data)def extractFiles(self):print('[+] Beginning extraction...please standby')extractionDir = os.path.join(os.getcwd(), os.path.basename(self.filePath) + '_extracted')if not os.path.exists(extractionDir):os.mkdir(extractionDir)os.chdir(extractionDir)for entry in self.tocList:self.fPtr.seek(entry.position, os.SEEK_SET)data = self.fPtr.read(entry.cmprsdDataSize)if entry.cmprsFlag == 1:try:data = zlib.decompress(data)except zlib.error:print('[!] Error : Failed to decompress {0}'.format(entry.name))continue# Malware may tamper with the uncompressed size# Comment out the assertion in such a caseassert len(data) == entry.uncmprsdDataSize # Sanity Checkif entry.typeCmprsData == b'd' or entry.typeCmprsData == b'o':# d -> ARCHIVE_ITEM_DEPENDENCY# o -> ARCHIVE_ITEM_RUNTIME_OPTION# These are runtime options, not filescontinuebasePath = os.path.dirname(entry.name)if basePath != '':# Check if path exists, create if notif not os.path.exists(basePath):os.makedirs(basePath)if entry.typeCmprsData == b's':# s -> ARCHIVE_ITEM_PYSOURCE# Entry point are expected to be python scriptsprint('[+] Possible entry point: {0}.pyc'.format(entry.name))if self.pycMagic == b'\0' * 4:# if we don't have the pyc header yet, fix them in a later passself.barePycList.append(entry.name + '.pyc')self._writePyc(entry.name + '.pyc', data)elif entry.typeCmprsData == b'M' or entry.typeCmprsData == b'm':# M -> ARCHIVE_ITEM_PYPACKAGE# m -> ARCHIVE_ITEM_PYMODULE# packages and modules are pyc files with their header intact# From PyInstaller 5.3 and above pyc headers are no longer stored# https://github.com/pyinstaller/pyinstaller/commit/a97fdfif data[2:4] == b'\r\n':# < pyinstaller 5.3if self.pycMagic == b'\0' * 4: self.pycMagic = data[0:4]self._writeRawData(entry.name + '.pyc', data)else:# >= pyinstaller 5.3if self.pycMagic == b'\0' * 4:# if we don't have the pyc header yet, fix them in a later passself.barePycList.append(entry.name + '.pyc')self._writePyc(entry.name + '.pyc', data)else:self._writeRawData(entry.name, data)if entry.typeCmprsData == b'z' or entry.typeCmprsData == b'Z':self._extractPyz(entry.name)# Fix bare pyc's if anyself._fixBarePycs()def _fixBarePycs(self):for pycFile in self.barePycList:with open(pycFile, 'r+b') as pycFile:# Overwrite the first four bytespycFile.write(self.pycMagic)def _writePyc(self, filename, data):with open(filename, 'wb') as pycFile:pycFile.write(self.pycMagic) # pyc magicif self.pymaj >= 3 and self.pymin >= 7: # PEP 552 -- Deterministic pycspycFile.write(b'\0' * 4) # BitfieldpycFile.write(b'\0' * 8) # (Timestamp + size) || hash else:pycFile.write(b'\0' * 4) # Timestampif self.pymaj >= 3 and self.pymin >= 3:pycFile.write(b'\0' * 4) # Size parameter added in Python 3.3pycFile.write(data)def _extractPyz(self, name):dirName = name + '_extracted'# Create a directory for the contents of the pyzif not os.path.exists(dirName):os.mkdir(dirName)with open(name, 'rb') as f:pyzMagic = f.read(4)assert pyzMagic == b'PYZ\0' # Sanity CheckpyzPycMagic = f.read(4) # Python magic valueif self.pycMagic == b'\0' * 4:self.pycMagic = pyzPycMagicelif self.pycMagic != pyzPycMagic:self.pycMagic = pyzPycMagicprint('[!] Warning: pyc magic of files inside PYZ archive are different from those in CArchive')# Skip PYZ extraction if not running under the same python versionif self.pymaj != sys.version_info.major or self.pymin != sys.version_info.minor:print('[!] Warning: This script is running in a different Python version than the one used to build the executable.')print('[!] Please run this script in Python {0}.{1} to prevent extraction errors during unmarshalling'.format(self.pymaj, self.pymin))print('[!] Skipping pyz extraction')return(tocPosition, ) = struct.unpack('!i', f.read(4))f.seek(tocPosition, os.SEEK_SET)try:toc = marshal.load(f)except:print('[!] Unmarshalling FAILED. Cannot extract {0}. Extracting remaining files.'.format(name))returnprint('[+] Found {0} files in PYZ archive'.format(len(toc)))# From pyinstaller 3.1+ toc is a list of tuplesif type(toc) == list:toc = dict(toc)for key in toc.keys():(ispkg, pos, length) = toc[key]f.seek(pos, os.SEEK_SET)fileName = keytry:# for Python > 3.3 some keys are bytes object some are str objectfileName = fileName.decode('utf-8')except:pass# Prevent writing outside dirNamefileName = fileName.replace('..', '__').replace('.', os.path.sep)if ispkg == 1:filePath = os.path.join(dirName, fileName, '__init__.pyc')else:filePath = os.path.join(dirName, fileName + '.pyc')fileDir = os.path.dirname(filePath)if not os.path.exists(fileDir):os.makedirs(fileDir)try:data = f.read(length)data = zlib.decompress(data)except:print('[!] Error: Failed to decompress {0}, probably encrypted. Extracting as is.'.format(filePath))open(filePath + '.encrypted', 'wb').write(data)else:self._writePyc(filePath, data)def main():if len(sys.argv) < 2:print('[+] Usage: pyinstxtractor.py <filename>')else:arch = PyInstArchive(sys.argv[1])if arch.open():if arch.checkFile():if arch.getCArchiveInfo():arch.parseTOC()arch.extractFiles()arch.close()print('[+] Successfully extracted pyinstaller archive: {0}'.format(sys.argv[1]))print('')print('You can now use a python decompiler on the pyc files within the extracted directory')returnarch.close()if __name__ == '__main__':main()
2、解包
在使用前:
将需解包的exe与下载的pyinstxtractor.py存入同级文件夹
使用命令行输入如下指令, 得到exe的解包文件夹.
python pyinstxtractor.py {exe路径}
示例: python pyinstxtractor.py CreatFoder.exe
运行结果:
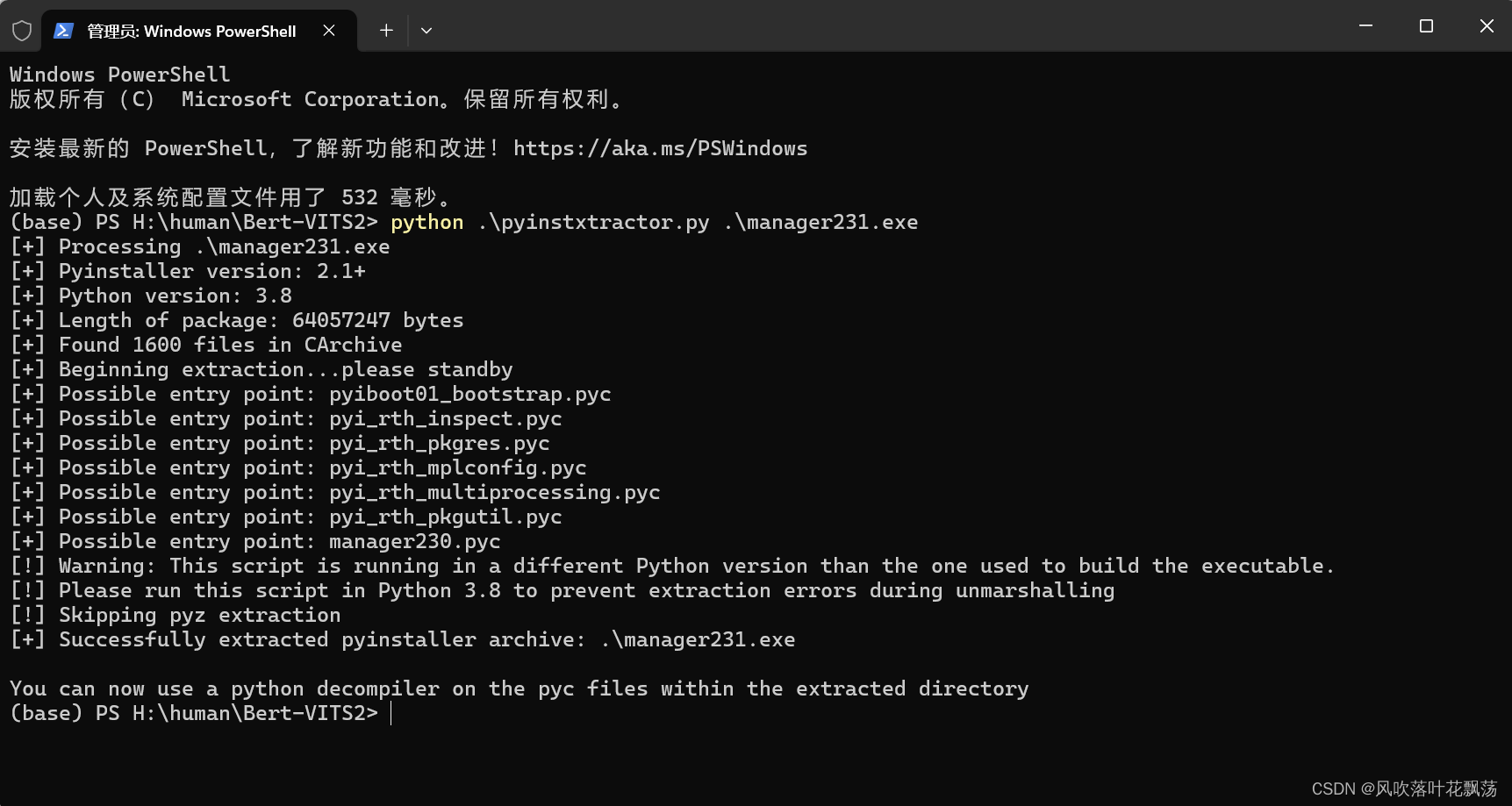
解包后文件放在以exe名字+_extracted的文件夹中
三、反编译uncompyle6工具使用
目前代码还不能用,打开会看到基本全是乱码。
在这里需要对在线pyc,pyo,pyd文件等进行反编译成py文件
1、pip安装uncompyle6
pip install uncompyle6
2、找到主文件并编译
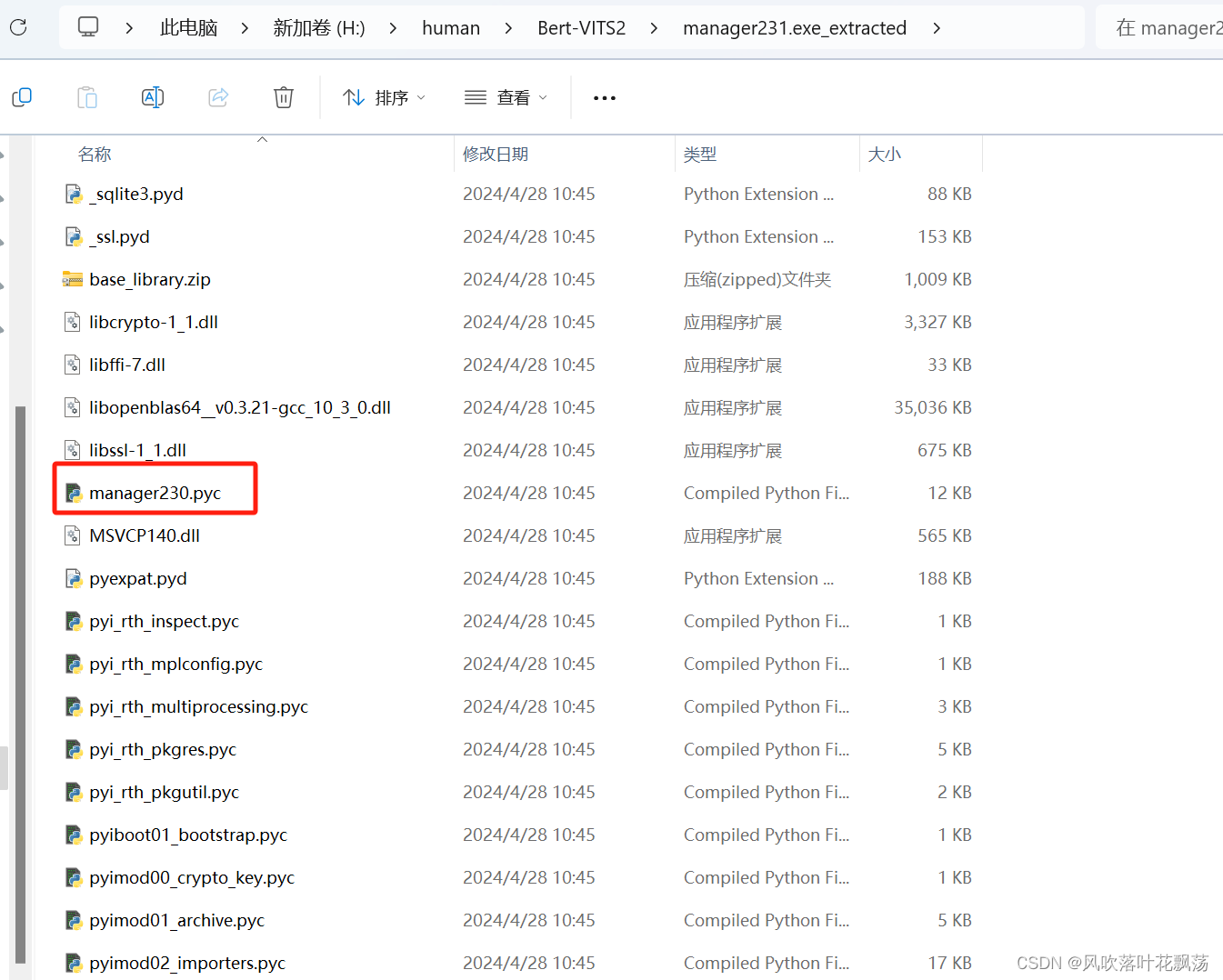
主文件的命名一般与其他库不同,有比较明显的开发者个人特征,且后缀通常是pyc。
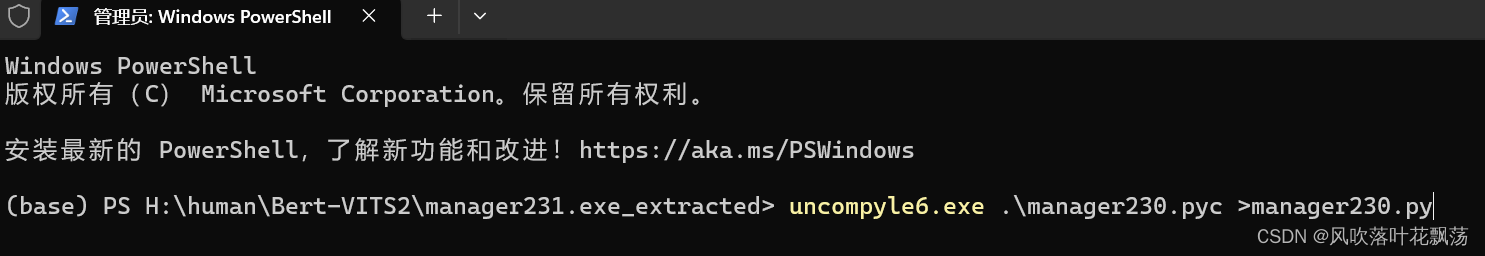
找到之后再同级目录下输入命令行执行
uncompyle6.exe {pyc文件} >{py文件输出路径}
示例
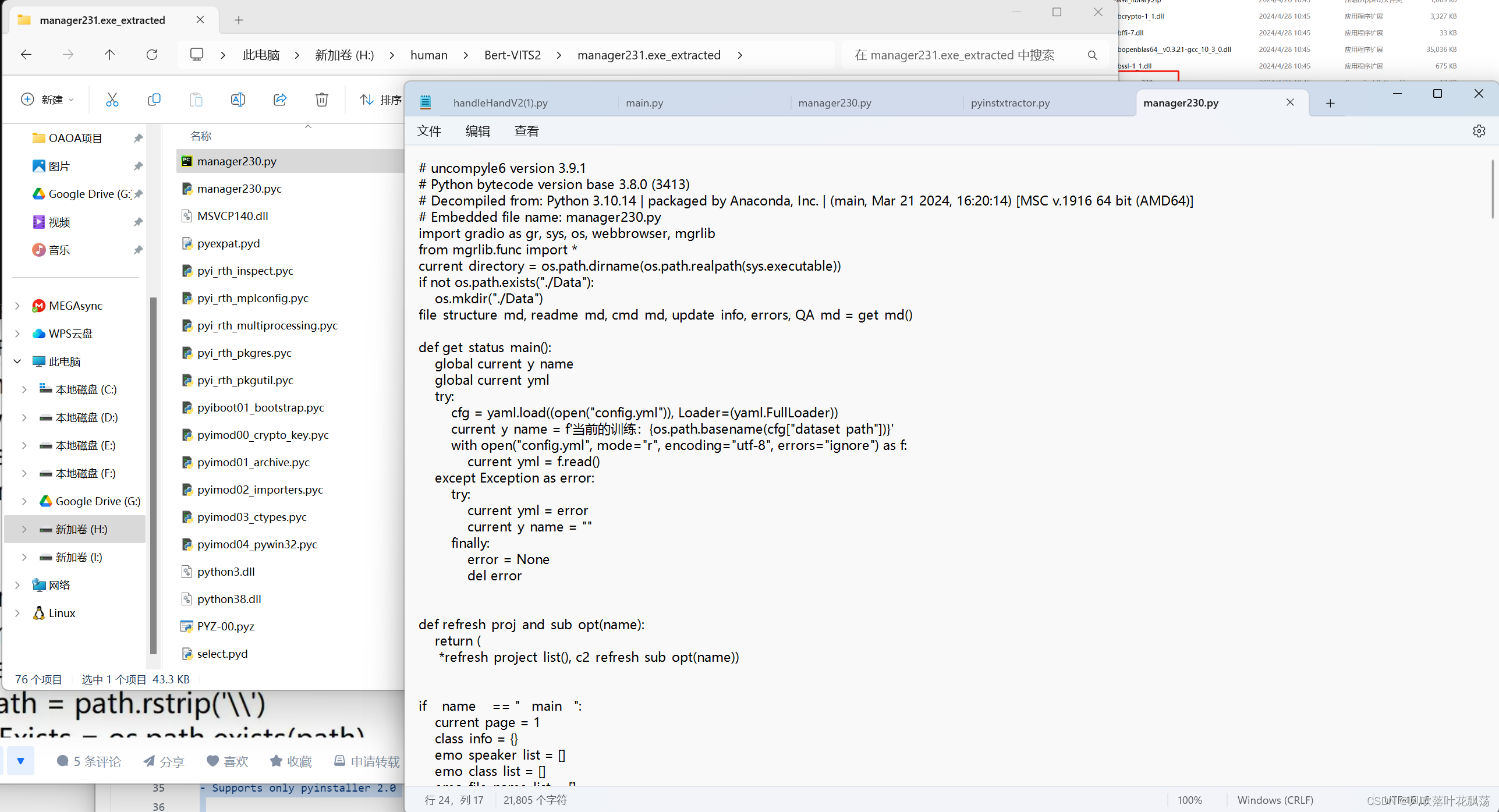
3、解压完成查看源码
无乱码,一切正常
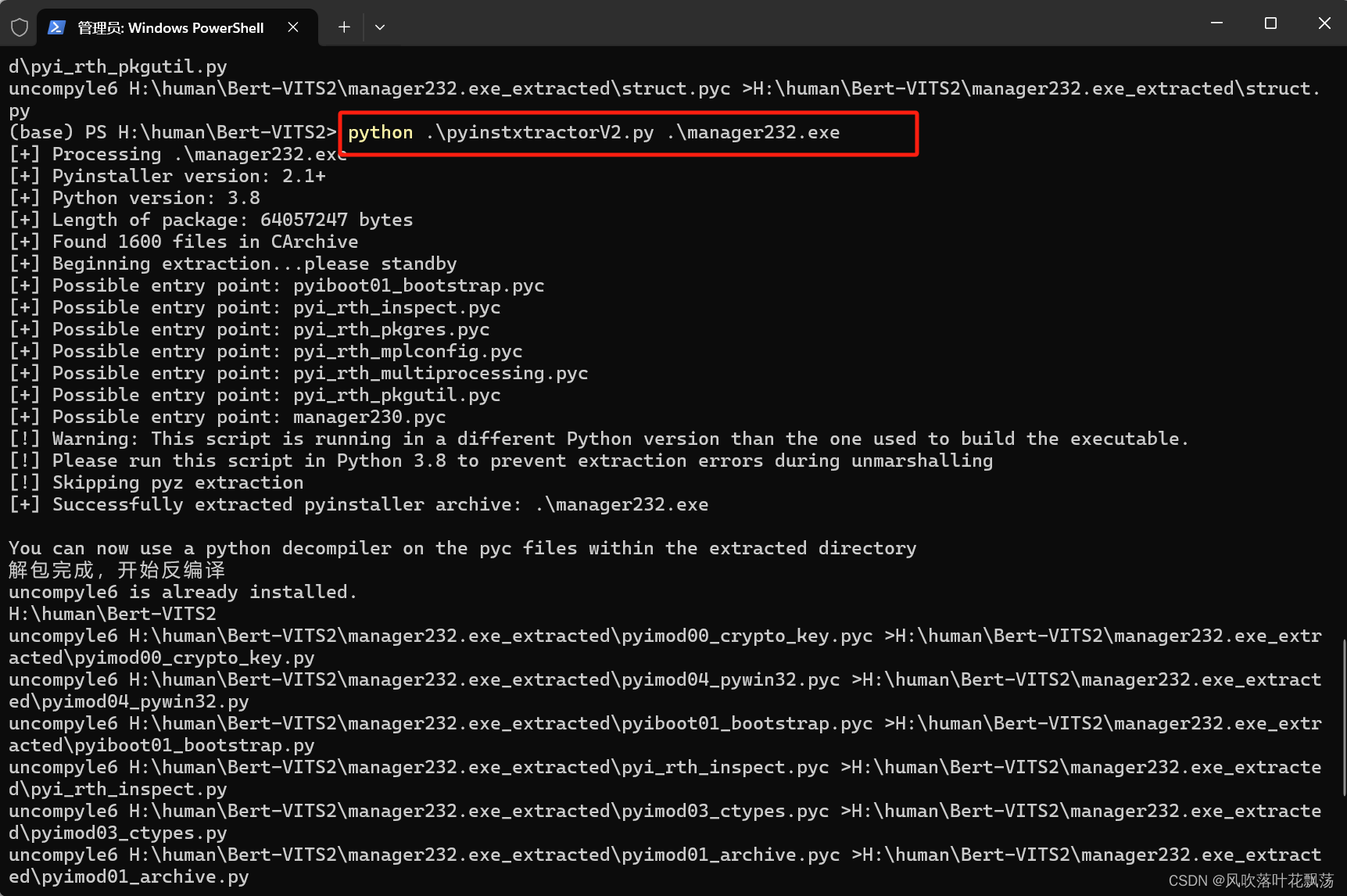
四、一键解包并编译
很多时候我们对于解包和编译是同一流程的。为了加快获取目标源码这一步骤,我将解包和编译的流程集中了起来,源码如下:
新建一个py文件:pyinstxtractorV2.py
"""
PyInstaller Extractor v2.0 (Supports pyinstaller 6.6.0, 6.5.0, 6.4.0, 6.3.0, 6.2.0, 6.1.0, 6.0.0, 5.13.2, 5.13.1, 5.13.0, 5.12.0, 5.11.0, 5.10.1, 5.10.0, 5.9.0, 5.8.0, 5.7.0, 5.6.2, 5.6.1, 5.6, 5.5, 5.4.1, 5.4, 5.3, 5.2, 5.1, 5.0.1, 5.0, 4.10, 4.9, 4.8, 4.7, 4.6, 4.5.1, 4.5, 4.4, 4.3, 4.2, 4.1, 4.0, 3.6, 3.5, 3.4, 3.3, 3.2, 3.1, 3.0, 2.1, 2.0)
Author : Extreme Coders
E-mail : extremecoders(at)hotmail(dot)com
Web : https://0xec.blogspot.com
Date : 26-March-2020
Url : https://github.com/extremecoders-re/pyinstxtractorFor any suggestions, leave a comment on
https://forum.tuts4you.com/topic/34455-pyinstaller-extractor/This script extracts a pyinstaller generated executable file.
Pyinstaller installation is not needed. The script has it all.For best results, it is recommended to run this script in the
same version of python as was used to create the executable.
This is just to prevent unmarshalling errors(if any) while
extracting the PYZ archive.Usage : Just copy this script to the directory where your exe residesand run the script with the exe file name as a parameterC:\\path\\to\\exe\\>python pyinstxtractor.py <filename>
$ /path/to/exe/python pyinstxtractor.py <filename>Licensed under GNU General Public License (GPL) v3.
You are free to modify this source.CHANGELOG
================================================Version 1.1 (Jan 28, 2014)
-------------------------------------------------
- First Release
- Supports only pyinstaller 2.0Version 1.2 (Sept 12, 2015)
-------------------------------------------------
- Added support for pyinstaller 2.1 and 3.0 dev
- Cleaned up code
- Script is now more verbose
- Executable extracted within a dedicated sub-directory(Support for pyinstaller 3.0 dev is experimental)Version 1.3 (Dec 12, 2015)
-------------------------------------------------
- Added support for pyinstaller 3.0 final
- Script is compatible with both python 2.x & 3.x (Thanks to Moritz Kroll @ Avira Operations GmbH & Co. KG)Version 1.4 (Jan 19, 2016)
-------------------------------------------------
- Fixed a bug when writing pyc files >= version 3.3 (Thanks to Daniello Alto: https://github.com/Djamana)Version 1.5 (March 1, 2016)
-------------------------------------------------
- Added support for pyinstaller 3.1 (Thanks to Berwyn Hoyt for reporting)Version 1.6 (Sept 5, 2016)
-------------------------------------------------
- Added support for pyinstaller 3.2
- Extractor will use a random name while extracting unnamed files.
- For encrypted pyz archives it will dump the contents as is. Previously, the tool would fail.Version 1.7 (March 13, 2017)
-------------------------------------------------
- Made the script compatible with python 2.6 (Thanks to Ross for reporting)Version 1.8 (April 28, 2017)
-------------------------------------------------
- Support for sub-directories in .pyz files (Thanks to Moritz Kroll @ Avira Operations GmbH & Co. KG)Version 1.9 (November 29, 2017)
-------------------------------------------------
- Added support for pyinstaller 3.3
- Display the scripts which are run at entry (Thanks to Michael Gillespie @ malwarehunterteam for the feature request)Version 2.0 (March 26, 2020)
-------------------------------------------------
- Project migrated to github
- Supports pyinstaller 3.6
- Added support for Python 3.7, 3.8
- The header of all extracted pyc's are now automatically fixed
"""from __future__ import print_function
import os
import struct
import marshal
import zlib
import sys
from uuid import uuid4 as uniquenameclass CTOCEntry:def __init__(self, position, cmprsdDataSize, uncmprsdDataSize, cmprsFlag, typeCmprsData, name):self.position = positionself.cmprsdDataSize = cmprsdDataSizeself.uncmprsdDataSize = uncmprsdDataSizeself.cmprsFlag = cmprsFlagself.typeCmprsData = typeCmprsDataself.name = nameclass PyInstArchive:PYINST20_COOKIE_SIZE = 24 # For pyinstaller 2.0PYINST21_COOKIE_SIZE = 24 + 64 # For pyinstaller 2.1+MAGIC = b'MEI\014\013\012\013\016' # Magic number which identifies pyinstallerdef __init__(self, path):self.filePath = pathself.pycMagic = b'\0' * 4self.barePycList = [] # List of pyc's whose headers have to be fixeddef open(self):try:self.fPtr = open(self.filePath, 'rb')self.fileSize = os.stat(self.filePath).st_sizeexcept:print('[!] Error: Could not open {0}'.format(self.filePath))return Falsereturn Truedef close(self):try:self.fPtr.close()except:passdef checkFile(self):print('[+] Processing {0}'.format(self.filePath))searchChunkSize = 8192endPos = self.fileSizeself.cookiePos = -1if endPos < len(self.MAGIC):print('[!] Error : File is too short or truncated')return Falsewhile True:startPos = endPos - searchChunkSize if endPos >= searchChunkSize else 0chunkSize = endPos - startPosif chunkSize < len(self.MAGIC):breakself.fPtr.seek(startPos, os.SEEK_SET)data = self.fPtr.read(chunkSize)offs = data.rfind(self.MAGIC)if offs != -1:self.cookiePos = startPos + offsbreakendPos = startPos + len(self.MAGIC) - 1if startPos == 0:breakif self.cookiePos == -1:print('[!] Error : Missing cookie, unsupported pyinstaller version or not a pyinstaller archive')return Falseself.fPtr.seek(self.cookiePos + self.PYINST20_COOKIE_SIZE, os.SEEK_SET)if b'python' in self.fPtr.read(64).lower():print('[+] Pyinstaller version: 2.1+')self.pyinstVer = 21 # pyinstaller 2.1+else:self.pyinstVer = 20 # pyinstaller 2.0print('[+] Pyinstaller version: 2.0')return Truedef getCArchiveInfo(self):try:if self.pyinstVer == 20:self.fPtr.seek(self.cookiePos, os.SEEK_SET)# Read CArchive cookie(magic, lengthofPackage, toc, tocLen, pyver) = \struct.unpack('!8siiii', self.fPtr.read(self.PYINST20_COOKIE_SIZE))elif self.pyinstVer == 21:self.fPtr.seek(self.cookiePos, os.SEEK_SET)# Read CArchive cookie(magic, lengthofPackage, toc, tocLen, pyver, pylibname) = \struct.unpack('!8sIIii64s', self.fPtr.read(self.PYINST21_COOKIE_SIZE))except:print('[!] Error : The file is not a pyinstaller archive')return Falseself.pymaj, self.pymin = (pyver // 100, pyver % 100) if pyver >= 100 else (pyver // 10, pyver % 10)print('[+] Python version: {0}.{1}'.format(self.pymaj, self.pymin))# Additional data after the cookietailBytes = self.fileSize - self.cookiePos - (self.PYINST20_COOKIE_SIZE if self.pyinstVer == 20 else self.PYINST21_COOKIE_SIZE)# Overlay is the data appended at the end of the PEself.overlaySize = lengthofPackage + tailBytesself.overlayPos = self.fileSize - self.overlaySizeself.tableOfContentsPos = self.overlayPos + tocself.tableOfContentsSize = tocLenprint('[+] Length of package: {0} bytes'.format(lengthofPackage))return Truedef parseTOC(self):# Go to the table of contentsself.fPtr.seek(self.tableOfContentsPos, os.SEEK_SET)self.tocList = []parsedLen = 0# Parse table of contentswhile parsedLen < self.tableOfContentsSize:(entrySize,) = struct.unpack('!i', self.fPtr.read(4))nameLen = struct.calcsize('!iIIIBc')(entryPos, cmprsdDataSize, uncmprsdDataSize, cmprsFlag, typeCmprsData, name) = \struct.unpack( \'!IIIBc{0}s'.format(entrySize - nameLen), \self.fPtr.read(entrySize - 4))try:name = name.decode("utf-8").rstrip("\0")except UnicodeDecodeError:newName = str(uniquename())print('[!] Warning: File name {0} contains invalid bytes. Using random name {1}'.format(name, newName))name = newName# Prevent writing outside the extraction directoryif name.startswith("/"):name = name.lstrip("/")if len(name) == 0:name = str(uniquename())print('[!] Warning: Found an unamed file in CArchive. Using random name {0}'.format(name))self.tocList.append( \CTOCEntry( \self.overlayPos + entryPos, \cmprsdDataSize, \uncmprsdDataSize, \cmprsFlag, \typeCmprsData, \name \))parsedLen += entrySizeprint('[+] Found {0} files in CArchive'.format(len(self.tocList)))def _writeRawData(self, filepath, data):nm = filepath.replace('\\', os.path.sep).replace('/', os.path.sep).replace('..', '__')nmDir = os.path.dirname(nm)if nmDir != '' and not os.path.exists(nmDir): # Check if path exists, create if notos.makedirs(nmDir)with open(nm, 'wb') as f:f.write(data)def extractFiles(self):print('[+] Beginning extraction...please standby')extractionDir = os.path.join(os.getcwd(), os.path.basename(self.filePath) + '_extracted')if not os.path.exists(extractionDir):os.mkdir(extractionDir)os.chdir(extractionDir)for entry in self.tocList:self.fPtr.seek(entry.position, os.SEEK_SET)data = self.fPtr.read(entry.cmprsdDataSize)if entry.cmprsFlag == 1:try:data = zlib.decompress(data)except zlib.error:print('[!] Error : Failed to decompress {0}'.format(entry.name))continue# Malware may tamper with the uncompressed size# Comment out the assertion in such a caseassert len(data) == entry.uncmprsdDataSize # Sanity Checkif entry.typeCmprsData == b'd' or entry.typeCmprsData == b'o':# d -> ARCHIVE_ITEM_DEPENDENCY# o -> ARCHIVE_ITEM_RUNTIME_OPTION# These are runtime options, not filescontinuebasePath = os.path.dirname(entry.name)if basePath != '':# Check if path exists, create if notif not os.path.exists(basePath):os.makedirs(basePath)if entry.typeCmprsData == b's':# s -> ARCHIVE_ITEM_PYSOURCE# Entry point are expected to be python scriptsprint('[+] Possible entry point: {0}.pyc'.format(entry.name))if self.pycMagic == b'\0' * 4:# if we don't have the pyc header yet, fix them in a later passself.barePycList.append(entry.name + '.pyc')self._writePyc(entry.name + '.pyc', data)elif entry.typeCmprsData == b'M' or entry.typeCmprsData == b'm':# M -> ARCHIVE_ITEM_PYPACKAGE# m -> ARCHIVE_ITEM_PYMODULE# packages and modules are pyc files with their header intact# From PyInstaller 5.3 and above pyc headers are no longer stored# https://github.com/pyinstaller/pyinstaller/commit/a97fdfif data[2:4] == b'\r\n':# < pyinstaller 5.3if self.pycMagic == b'\0' * 4:self.pycMagic = data[0:4]self._writeRawData(entry.name + '.pyc', data)else:# >= pyinstaller 5.3if self.pycMagic == b'\0' * 4:# if we don't have the pyc header yet, fix them in a later passself.barePycList.append(entry.name + '.pyc')self._writePyc(entry.name + '.pyc', data)else:self._writeRawData(entry.name, data)if entry.typeCmprsData == b'z' or entry.typeCmprsData == b'Z':self._extractPyz(entry.name)# Fix bare pyc's if anyself._fixBarePycs()def _fixBarePycs(self):for pycFile in self.barePycList:with open(pycFile, 'r+b') as pycFile:# Overwrite the first four bytespycFile.write(self.pycMagic)def _writePyc(self, filename, data):with open(filename, 'wb') as pycFile:pycFile.write(self.pycMagic) # pyc magicif self.pymaj >= 3 and self.pymin >= 7: # PEP 552 -- Deterministic pycspycFile.write(b'\0' * 4) # BitfieldpycFile.write(b'\0' * 8) # (Timestamp + size) || hashelse:pycFile.write(b'\0' * 4) # Timestampif self.pymaj >= 3 and self.pymin >= 3:pycFile.write(b'\0' * 4) # Size parameter added in Python 3.3pycFile.write(data)def _extractPyz(self, name):dirName = name + '_extracted'# Create a directory for the contents of the pyzif not os.path.exists(dirName):os.mkdir(dirName)with open(name, 'rb') as f:pyzMagic = f.read(4)assert pyzMagic == b'PYZ\0' # Sanity CheckpyzPycMagic = f.read(4) # Python magic valueif self.pycMagic == b'\0' * 4:self.pycMagic = pyzPycMagicelif self.pycMagic != pyzPycMagic:self.pycMagic = pyzPycMagicprint('[!] Warning: pyc magic of files inside PYZ archive are different from those in CArchive')# Skip PYZ extraction if not running under the same python versionif self.pymaj != sys.version_info.major or self.pymin != sys.version_info.minor:print('[!] Warning: This script is running in a different Python version than the one used to build the executable.')print('[!] Please run this script in Python {0}.{1} to prevent extraction errors during unmarshalling'.format(self.pymaj, self.pymin))print('[!] Skipping pyz extraction')return(tocPosition,) = struct.unpack('!i', f.read(4))f.seek(tocPosition, os.SEEK_SET)try:toc = marshal.load(f)except:print('[!] Unmarshalling FAILED. Cannot extract {0}. Extracting remaining files.'.format(name))returnprint('[+] Found {0} files in PYZ archive'.format(len(toc)))# From pyinstaller 3.1+ toc is a list of tuplesif type(toc) == list:toc = dict(toc)for key in toc.keys():(ispkg, pos, length) = toc[key]f.seek(pos, os.SEEK_SET)fileName = keytry:# for Python > 3.3 some keys are bytes object some are str objectfileName = fileName.decode('utf-8')except:pass# Prevent writing outside dirNamefileName = fileName.replace('..', '__').replace('.', os.path.sep)if ispkg == 1:filePath = os.path.join(dirName, fileName, '__init__.pyc')else:filePath = os.path.join(dirName, fileName + '.pyc')fileDir = os.path.dirname(filePath)if not os.path.exists(fileDir):os.makedirs(fileDir)try:data = f.read(length)data = zlib.decompress(data)except:print('[!] Error: Failed to decompress {0}, probably encrypted. Extracting as is.'.format(filePath))open(filePath + '.encrypted', 'wb').write(data)else:self._writePyc(filePath, data)def main():if len(sys.argv) < 2:print('[+] Usage: pyinstxtractor.py <filename>')else:arch = PyInstArchive(sys.argv[1])if arch.open():if arch.checkFile():if arch.getCArchiveInfo():arch.parseTOC()arch.extractFiles()arch.close()print('[+] Successfully extracted pyinstaller archive: {0}'.format(sys.argv[1]))print('')print('You can now use a python decompiler on the pyc files within the extracted directory')returnarch.close()import subprocess,os,concurrent.futures
def handle(filePath):try:# 定义要执行的命令command = "uncompyle6 {} >{}".format(filePath, filePath.replace('pyc', 'py'))# 使用subprocess模块执行命令process = subprocess.Popen(command, shell=True)process.wait() # 等待命令执行完成print(command)os.remove(filePath)return Trueexcept Exception as e:print(e)return False
def excutor():print('检查是否已安装uncompyle6')# 检查是否已安装uncompyle6try:subprocess.check_output(['uncompyle6', '--version'])print("uncompyle6 is already installed.")except (subprocess.CalledProcessError,FileNotFoundError):print("uncompyle6 is not installed. Installing...")subprocess.call(['pip', 'install', 'uncompyle6'])currentPath=os.path.dirname(os.path.abspath(__file__))targe=os.path.basename(sys.argv[1])print('解包完成,开始反编译')targeDir=os.path.join(currentPath,targe+'_extracted')with concurrent.futures.ThreadPoolExecutor(max_workers=8) as excutor:futures=[]for root,dirs,files in os.walk(targeDir):for file in files:filePath=os.path.join(root,file)if filePath.endswith('pyc'):task =excutor.submit(handle,filePath)futures.append(task)for future in concurrent.futures.as_completed(futures):ret=future.result()if __name__ == '__main__':main()excutor()
- 使用
将pyinstxtractorV2.py文件与待处理的exe文件放置在同一目录并执行:
示例:python .\pyinstxtractorV2.py .\manager232.exe
这篇关于Python解包及反编译: PyInstaller Extractor+uncompyle6的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!




