本文主要是介绍ECDSA 签名的内在延展性(“重放“攻击)学习,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
相关推特:https://twitter.com/danielvf/status/1563169773684305921
原理文章:https://www.derpturkey.com/inherent-malleability-of-ecdsa-signatures/
签名的内在延展性,意味着可以为相同的数据创建第二有效的签名,导致如果在签名中没有加入nonce ,deadline等限制条件,攻击者可以再次提交对应交易(使用第二份签名)造成意外损失。
python验证代码:
import imp
from ellipticcurve.ecdsa import Ecdsa
from ellipticcurve.privateKey import PrivateKey
from web3 import Web3;
from ellipticcurve.signature import Signature
from ellipticcurve.curve import secp256k1, getCurveByOid
# Generate new Keys
privateKey = PrivateKey()
publicKey = privateKey.publicKey()message = "My test message"# Generate Signature
signature = Ecdsa.sign(message, privateKey)# To verify if the signature is valid
print(Ecdsa.verify(message, signature, publicKey))privateKey = PrivateKey(secret=1)
publicKey = privateKey.publicKey()
print(publicKey.toString());
message = "give to"# Generate Signature
signature = Ecdsa.sign(message, privateKey)
print('aa:',Web3.toHex(signature.r),': ',Web3.toHex(signature.s))
# To verify if the signature is valid
print(Ecdsa.verify(message, signature, publicKey))
print(signature._toString())
sig2=Signature(r=signature.r,s=secp256k1.N-signature.s,recoveryId=signature.recoveryId);
print('aa:',Web3.toHex(sig2.r),': ',Web3.toHex(sig2.s))
print(Ecdsa.verify(message, sig2, publicKey))
print(Web3.toHex(secp256k1.N));
再evm合约中测试:
function tryRecover(bytes32 hash,uint8 v,bytes32 r,bytes32 s) public pure returns (address) {//删掉无关代码:address signer = ecrecover(hash, v, r, s);return (signer);}
将sig1.r 3dd21cd54e1b1178bba113b5c06b4a58c3b101eb007597fe4a0fca796daa67e7
// sig1.s 4e1bf4b3211203e356603c1a900846e8a40b0b0372aeffb6319de96ec8c25a1d
及
// sig2.r 3dd21cd54e1b1178bba113b5c06b4a58c3b101eb007597fe4a0fca796daa67e7
// sig2.s b1e40b4cdeedfc1ca99fc3e56ff7b91616a3d1e33c99a0858e34751e0773e724
分别填入对应参数:
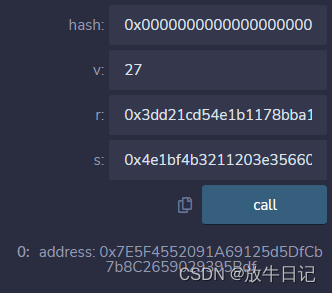
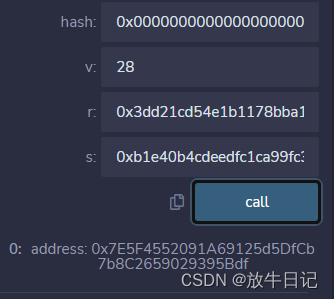
即可返回相同address.
s的计算方式为:Secp256k1.N -sig1.s;
这篇关于ECDSA 签名的内在延展性(“重放“攻击)学习的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!







