本文主要是介绍ENSP校园网设计实验,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
前言
哈喽,我是ICT大龙。本次更新了使用ENSP仿真软件设计校园网实验。时间比较着急,可能会有错误,欢迎大家指出。
获取本次工程文件方式在文章结束部分。
拓扑设计
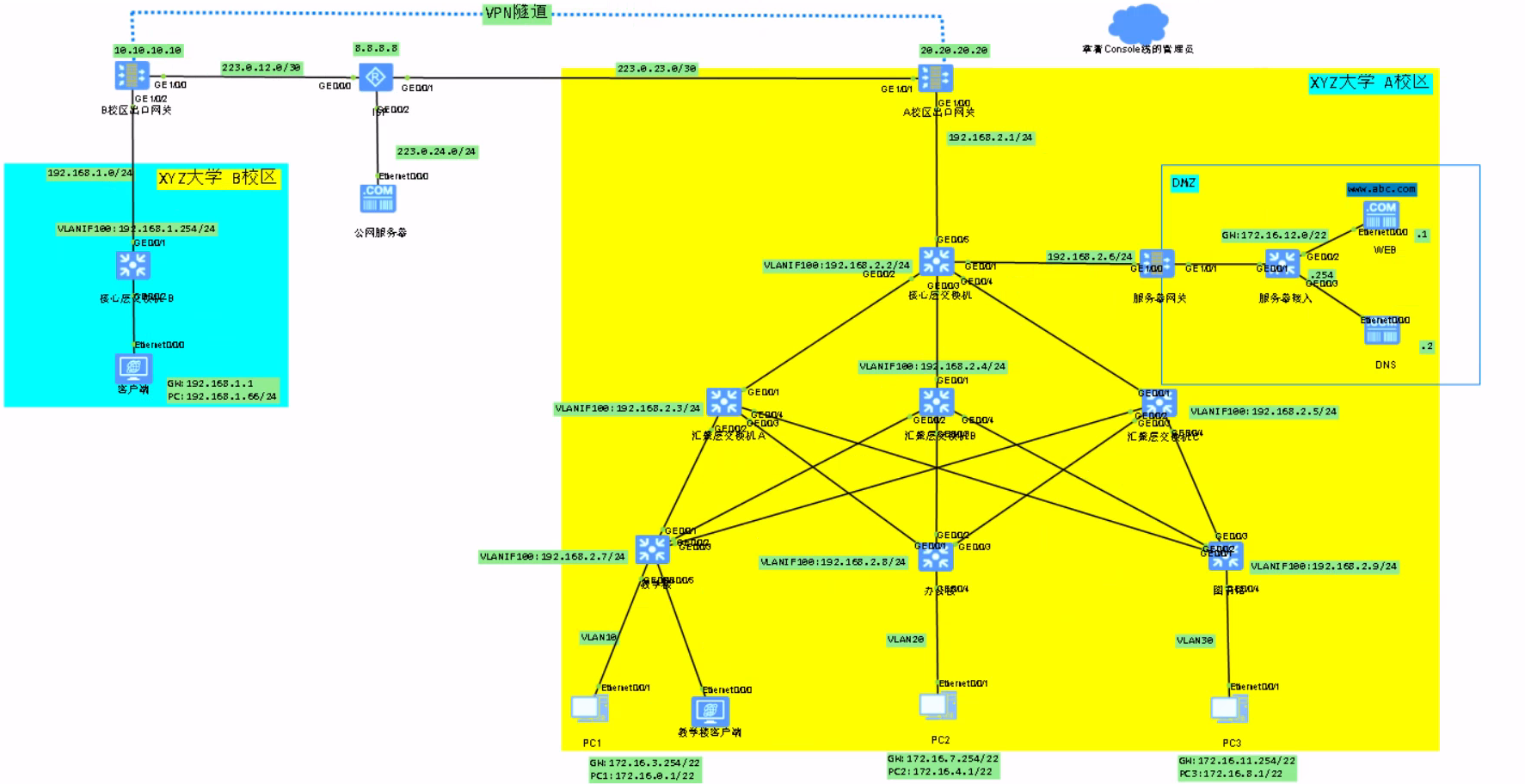
拓扑介绍---A校区
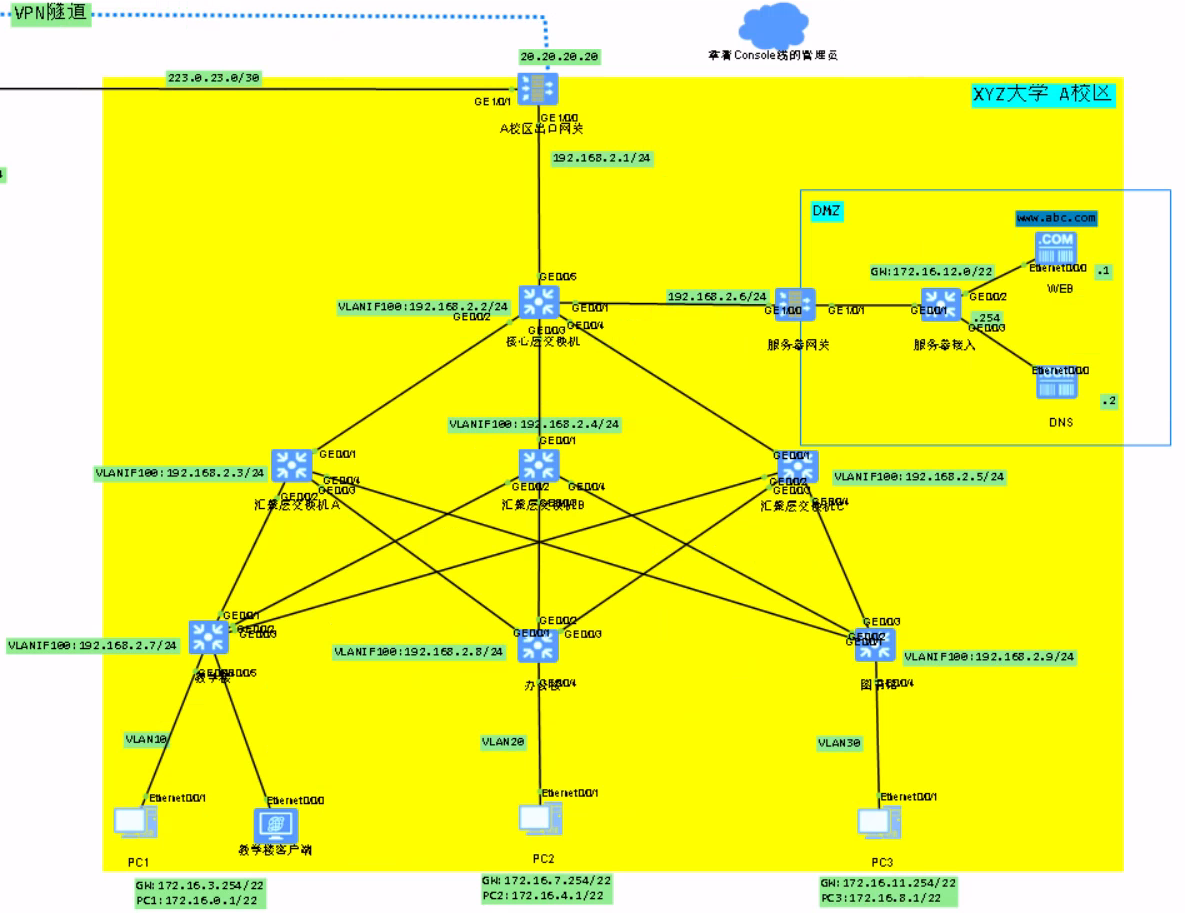
如图,XYZ大学校园网设计分为3部分,分别是A校区、B校区与互联网区域
A校区分为3个部门(教学楼、办公楼、图书馆)与一个服务器机房
A校区的网络架构为接入层、汇聚层与核心层。终端设备上的网关设在接入层上面
为了有效的隔离广播风暴,按照每个部门属于一个VLAN的方式进行划分
学校共有两台服务器,分别提供WEB和DNS服务,通过一台接入交换机进行接入并连接到服务器机房的网关上面。为了保证服务器不被非法用户进行恶意攻击,服务器机房采用一台防火墙设备充当网关
核心层、汇聚层与接入层使用OSPF协议计算路由与开销,使得A校区网络内部可以实现通信。
A校区使用一台防火墙来充当网关设备,这样不仅可以进行路由,还能有效的保证内网的安全。
拓扑介绍---B校区

上图中可以看到B校区的出口网关也是一台防火墙设备。下面连接了一台核心层交换机,再往下就是客户端了。
B校区的拓扑并没有设计的很复杂,直接使用了VLANIF接口进行模拟。
拓扑介绍---互联网区域
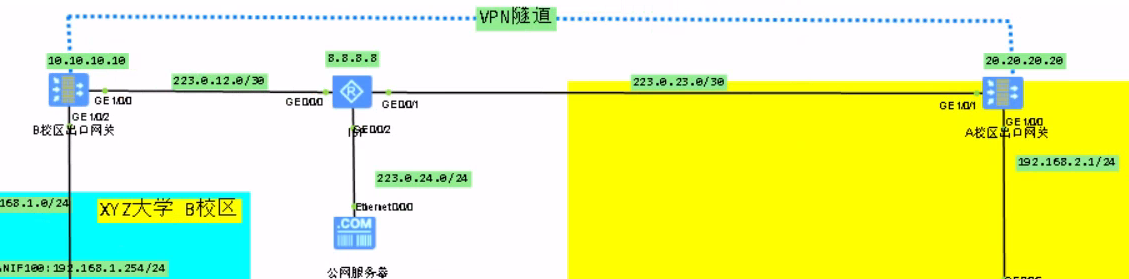
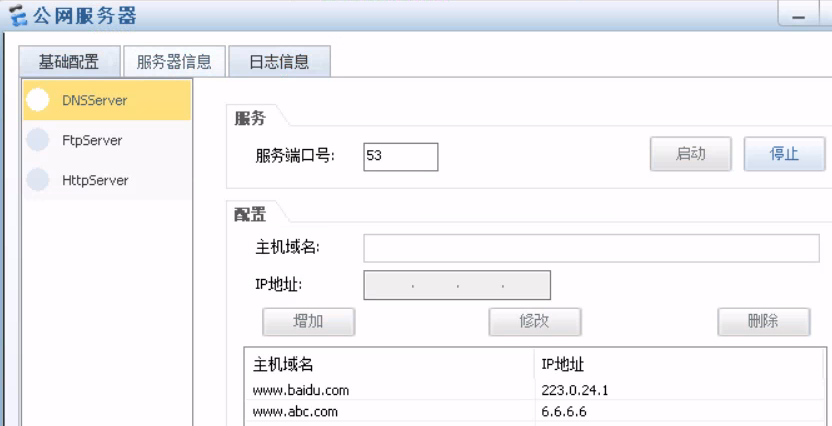
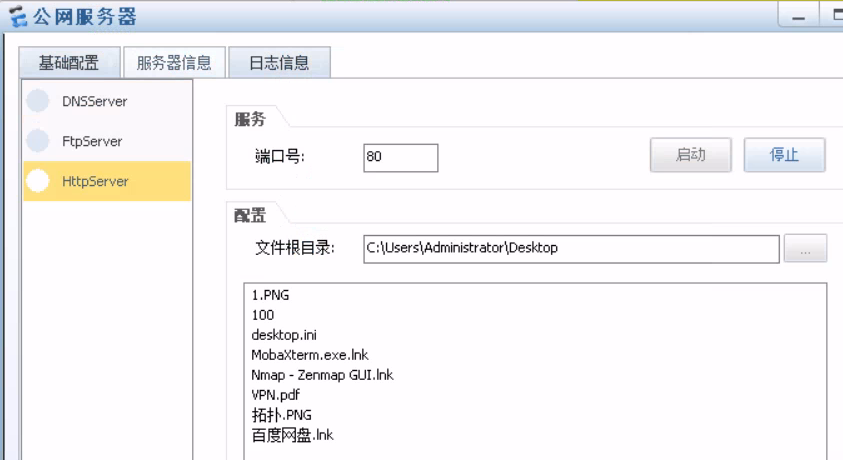
互联网区域使用一台路由器来充当ISP设备。可以看到连接了一台公网服务器用来充当百度服务器,后期需要终端用户对该域名进行访问。
A校区网关、B校区网关与ISP设备之间运行了ISIS路由协议实现互通。A校区与B校区之间通过互联网建立了虚拟的专用网络,即VPN隧道。
需求规划
1.两个校区的所有终端设备可以访问公网的百度服务器与A校区中学校官网服务器的WEB服务。
2.终端用户访问互联网时需要进行NAT地址转换,转换为出口网关的出口地址。
3.因为B校区中没有学生居住,只有行政岗位的老师在此办公,所以A校区中只有办公楼可以与B校区通信。
4.A校区与B校区需要经过VPN隧道进行通信。
5.在学校中,学生接入局域网后。经常使用对校内服务器进行ping测试的方式来验证是否成功接入局域网,这样对校内服务器造成了压力。为了杜绝以上行为,决定在相关设备上进行策略配置。
6.公网中的用户配置DNS地址为公网DNS服务器。校内用户配置DNS地址为校内DNS服务器。
A校区配置
1.配置终端用户的IP地址、网关等信息
教学楼客户端1
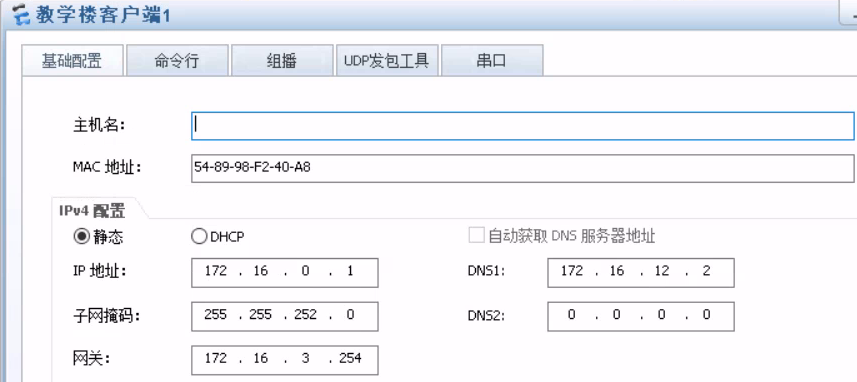
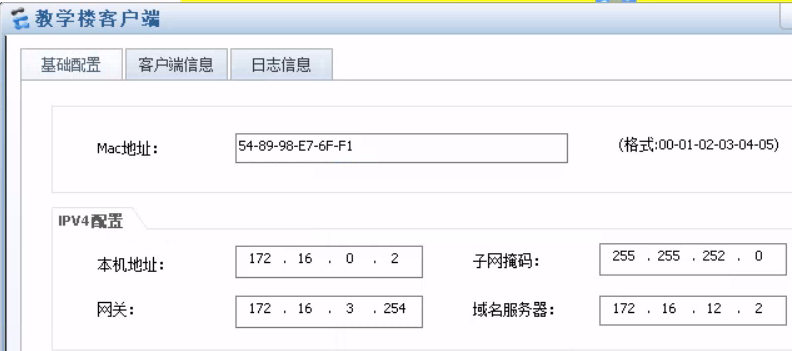
教学楼客户端
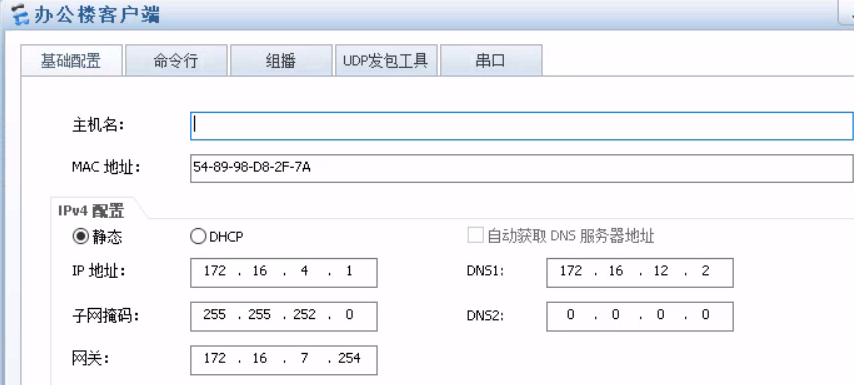
办公楼客户端
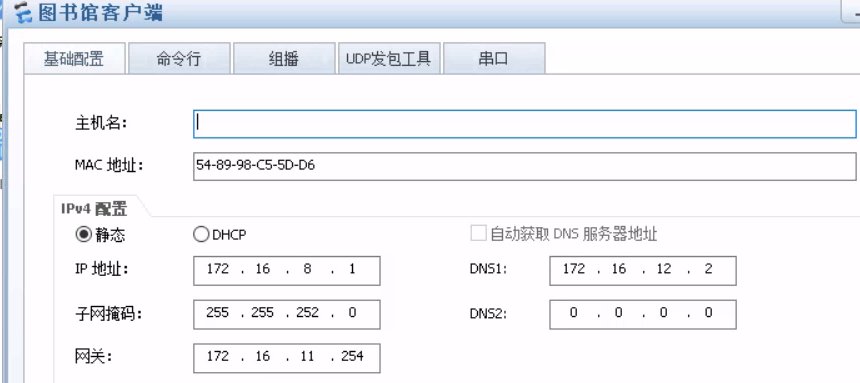
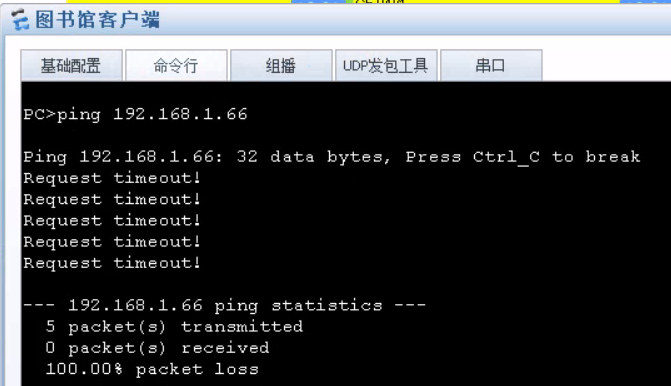
图书馆客户端
2.接入层设备划分VLAN,配置VLANIF接口。
[JR-A]vlan 10
[JR-A-vlan10]int g0/0/4
[JR-A-GigabitEthernet0/0/4]port link acc
[JR-A-GigabitEthernet0/0/4]port de vlan 10
[JR-A-GigabitEthernet0/0/4]int g0/0/5
[JR-A-GigabitEthernet0/0/5]port link ac
[JR-A-GigabitEthernet0/0/5]port de vlan 10
[JR-A]vlan 100
[JR-A-vlan100]int g0/0/1
[JR-A-GigabitEthernet0/0/1]port link tr
[JR-A-GigabitEthernet0/0/1]port tr allow vlan 100
[JR-A-GigabitEthernet0/0/1]int g0/0/2
[JR-A-GigabitEthernet0/0/2]port link tr
[JR-A-GigabitEthernet0/0/2]port tr allow vlan 100
[JR-A-GigabitEthernet0/0/2]int g0/0/3
[JR-A-GigabitEthernet0/0/3]port link tr
[JR-A-GigabitEthernet0/0/3]port tr allow vlan 100
[JR-A]int vlan 100
[JR-A-Vlanif100]ip add 192.168.2.7 24
[JR-A-Vlanif100]int vlan 10
[JR-A-Vlanif10]ip add 172.16.3.254 22
[JR-B]vlan 100
[JR-B-vlan100]vlan 20
[JR-B-vlan20]int g0/0/4
[JR-B-GigabitEthernet0/0/4]port link ac
[JR-B-GigabitEthernet0/0/4]port de vlan 20
[JR-B-GigabitEthernet0/0/4]int g0/0/1
[JR-B-GigabitEthernet0/0/1]port link trunk
[JR-B-GigabitEthernet0/0/1]port trunk allow vlan 100
[JR-B-GigabitEthernet0/0/1]int g0/0/2
[JR-B-GigabitEthernet0/0/2]port link trunk
[JR-B-GigabitEthernet0/0/2]port trunk allow vlan 100
[JR-B-GigabitEthernet0/0/2]int g0/0/3
[JR-B-GigabitEthernet0/0/3]port link trunk
[JR-B-GigabitEthernet0/0/3]port trunk allow vlan 100
[JR-B-GigabitEthernet0/0/3]int vlan 100
[JR-B-Vlanif100]ip add 192.168.2.8 24
[JR-B-Vlanif100]int vlan 20
[JR-B-Vlanif20]ip add 172.16.7.254 22
[JR-C]vlan batch 30 100
[JR-C]int g0/0/1
[JR-C-GigabitEthernet0/0/1]port link trunk
[JR-C-GigabitEthernet0/0/1]port trunk allow vlan 100
[JR-C-GigabitEthernet0/0/1]int g0/0/2
[JR-C-GigabitEthernet0/0/2]port link trunk
[JR-C-GigabitEthernet0/0/2]port trunk allow vlan 100
[JR-C-GigabitEthernet0/0/2]int g0/0/3
[JR-C-GigabitEthernet0/0/3]port link trunk
[JR-C-GigabitEthernet0/0/3]port trunk allow vlan 100
[JR-C-GigabitEthernet0/0/3]int g0/0/4
[JR-C-GigabitEthernet0/0/4]port link ac
[JR-C-GigabitEthernet0/0/4]port de vlan 100
3.汇聚层与核心层分别放通相应VLAN并配置VLANIF地址
[HJ-A]vlan 100
[HJ-A-vlan100]int vlan 100
[HJ-A-Vlanif100]ip add 192.168.2.3 24
[HJ-A-Vlanif100]int g0/0/1
[HJ-A-GigabitEthernet0/0/1]port link trunk
[HJ-A-GigabitEthernet0/0/1]port tr allow vlan 100
[HJ-A-GigabitEthernet0/0/1]int g0/0/2
[HJ-A-GigabitEthernet0/0/2]port link trunk
[HJ-A-GigabitEthernet0/0/2]port tr allow vlan 100
[HJ-A-GigabitEthernet0/0/2]int g0/0/3
[HJ-A-GigabitEthernet0/0/3]port tr allow vlan 100
[HJ-A-GigabitEthernet0/0/3]port link trunk
[HJ-A-GigabitEthernet0/0/3]int g0/0/4
[HJ-A-GigabitEthernet0/0/4]port link trunk
[HJ-A-GigabitEthernet0/0/4]port tr allow vlan 100
[HJ-B]vlan 100
[HJ-B-vlan100]int vlan 100
[HJ-B-Vlanif100]ip add 192.168.2.4 24
[HJ-B-Vlanif100]int g0/0/1
[HJ-B-GigabitEthernet0/0/1]port link trunk
[HJ-B-GigabitEthernet0/0/1]port tr allow vlan 100
[HJ-B-GigabitEthernet0/0/1]int g0/0/2
[HJ-B-GigabitEthernet0/0/2]port link trunk
[HJ-B-GigabitEthernet0/0/2]port tr allow vlan 100
[HJ-B-GigabitEthernet0/0/2]int g0/0/3
[HJ-B-GigabitEthernet0/0/3]port tr allow vlan 100
[HJ-B-GigabitEthernet0/0/3]port link trunk
[HJ-B-GigabitEthernet0/0/3]int g0/0/4
[HJ-B-GigabitEthernet0/0/4]port link trunk
[HJ-B-GigabitEthernet0/0/4]port tr allow vlan 100
[HJ-Cvlan 100
[HJ-C-vlan100]int vlan 100
[HJ-C-Vlanif100]ip add 192.168.2.5 24
[HJ-C-Vlanif100]int g0/0/1
[HJ-C-GigabitEthernet0/0/1]port link trunk
[HJ-C-GigabitEthernet0/0/1]port tr allow vlan 100
[HJ-B-GigabitEthernet0/0/1]int g0/0/2
[HJ-C-GigabitEthernet0/0/2]port link trunk
[HJ-C-GigabitEthernet0/0/2]port tr allow vlan 100
[HJ-C-GigabitEthernet0/0/2]int g0/0/3
[HJ-C-GigabitEthernet0/0/3]port tr allow vlan 100
[HJ-C-GigabitEthernet0/0/3]port link trunk
[HJ-C-GigabitEthernet0/0/3]int g0/0/4
[HJ-C-GigabitEthernet0/0/4]port link trunk
[HJ-C-GigabitEthernet0/0/4]port tr allow vlan 100
[LSW-HX]vlan 100
[LSW-HX-vlan100]int vlan 100
[LSW-HX-Vlanif100]ip add 192.168.2.2 24
[LSW-HX-Vlanif100]int g0/0/2
[LSW-HX-GigabitEthernet0/0/2]port link tr
[LSW-HX-GigabitEthernet0/0/2]port tr allow vlan 100
[LSW-HX-GigabitEthernet0/0/2]int g0/0/3
[LSW-HX-GigabitEthernet0/0/3]port link tr
[LSW-HX-GigabitEthernet0/0/3]port tr allow vlan 100
[LSW-HX-GigabitEthernet0/0/3]int g0/0/4
[LSW-HX-GigabitEthernet0/0/4]port link tr
[LSW-HX-GigabitEthernet0/0/4]port tr allow vlan 100
[LSW-HX-GigabitEthernet0/0/4]int g0/0/1
[LSW-HX-GigabitEthernet0/0/1]port link access
[LSW-HX-GigabitEthernet0/0/1]port de vlan 100
4.配置STP优先级
[LSW-HX]stp priority 0
[HJ-A]stp priority 4096
[HJ-B]stp priority 4096
[HJ-C]stp priority 4096
[JR-A]stp priority 8192
[JR-B]stp priority 8192
[JR-C]stp priority 8192
5.配置出口网关地址并在A校区设备上面启用OSPF协议
[GW-A]int g1/0/0
[GW-A-GigabitEthernet1/0/0]ip add 192.168.2.1 24
[GW-A]ospf 1
[GW-A-ospf-1]default-route-advertise always //后期会配置下发默认路由
[GW-A-ospf-1]area 0
[GW-A-ospf-1]int g1/0/0
[GW-A-GigabitEthernet1/0/0]ospf enable 1 area 0
[LSW-HX]ospf 1
[LSW-HX]int vlan 100
[LSW-HX-Vlanif100]ospf enable 1 area 0
[HJ-A]ospf 1
[HJ-A-ospf-1]int vlan 100
[HJ-A-Vlanif100]ospf enable 1 area 0
[HJ-B]ospf 1
[HJ-B-ospf-1]int vlan 100
[HJ-B-Vlanif100]ospf enable 1 area 0
[HJ-C]ospf 1
[HJ-C-ospf-1]int vlan 100
[HJ-C-Vlanif100]ospf enable 1 area 0
[JR-A]ospf 1
[JR-A-ospf-1]int vlan 100
[JR-A-Vlanif100]ospf enable 1 area 0
[JR-A-Vlanif100]int vlan 10
[JR-A-Vlanif10]ospf enable 1 area 0
[JR-B]ospf 1
[JR-B-ospf-1]int vlan 100
[JR-B-Vlanif100]ospf enable 1 area 0
[JR-B-Vlanif100]int vlan 20
[JR-B-Vlanif10]ospf enable 1 area 0
[JR-C]ospf 1
[JR-C-ospf-1]int vlan 100
[JR-C-Vlanif100]ospf enable 1 area 0
[JR-C-Vlanif100]int vlan 30
[JR-C-Vlanif10]ospf enable 1 area 0
[Server-GW]ospf 1
[Server-GW-ospf-1]int g1/0/0
[Server-GW-GigabitEthernet1/0/0]ospf enable 1 area 0
[Server-GW-GigabitEthernet1/0/0]int g1/0/1
[Server-GW-GigabitEthernet1/0/1]ospf enable 1 area 0
6.配置服务器网关策略
[Server-GW-policy-security]rule name b
[Server-GW-policy-security-rule-b] source-zone untrust
[Server-GW-policy-security-rule-b] destination-zone dmz
[Server-GW-policy-security-rule-b] service icmp
[Server-GW-policy-security-rule-b] service icmpv6
[Server-GW-policy-security-rule-b] action deny
[Server-GW-policy-security-rule-b] rule name a
[Server-GW-policy-security-rule-a] action permit
[Server-GW]firewall zone untrust
[Server-GW-zone-untrust]add int g1/0/0
[Server-GW]firewall zone dmz
[Server-GW-zone-untrust]add int g1/0/1
7.出口网关配置IP地址、默认路由、NAT配置以及策略
[GW-A]int g0/0/0
[GW-A-GigabitEthernet0/0/0]ip add 192.168.66.2 24
[GW-A-GigabitEthernet0/0/0]int g1/0/0
[GW-A-GigabitEthernet1/0/0]ip add 192.168.2.1 24
[GW-A-GigabitEthernet1/0/0]int g1/0/1
[GW-A-GigabitEthernet1/0/1]ip add 223.0.23.2 30
[GW-A-GigabitEthernet1/0/1]int l0
[GW-A-LoopBack0]ip add 2.2.2.2 32
[GW-A-LoopBack0]int l10
[GW-A-LoopBack10]ip add 6.6.6.6 32
[GW-A]firewall zone trust
[GW-A-zone-trust]add inter g1/0/0
[GW-A-zone-untrust]dis this
[GW-A-zone-trust]add inter g1/0/1
[GW-A]firewall zone dmz
[GW-A-zone-dmz]add interface Tunnel 1
[GW-A]ip address-set b type object ip address-set b type object
[GW-A-object-address-set-b] address 0 172.16.4.0 mask 22
[GW-A]ip address-set c type object
[GW-A-object-address-set-c] address 0 192.168.1.0 mask 24
[GW-A]ip address-set d type object
[GW-A-object-address-set-d] address 0 172.16.0.0 mask 22
[GW-A-object-address-set-d] address 1 172.16.8.0 mask 22
[GW-A]security-policy
[GW-A-policy-security]rule name c
[GW-A-policy-security-rule-c] source-zone trust
[GW-A-policy-security-rule-c] destination-zone dmz
[GW-A-policy-security-rule-c] source-address address-set d
[GW-A-policy-security-rule-c] destination-address address-set c
[GW-A-policy-security-rule-c] action deny
[GW-A-policy-security-rule-c] rule name b
[GW-A-policy-security-rule-b] source-zone trust
[GW-A-policy-security-rule-b] destination-zone dmz
[GW-A-policy-security-rule-b] source-address address-set b
[GW-A-policy-security-rule-b] destination-address address-set c
[GW-A-policy-security-rule-b] action permit
[GW-A-policy-security-rule-b] rule name a
[GW-A-policy-security-rule-a] action permit
[GW-A]nat-policy
[GW-A-policy-nat] rule name a
[GW-A-policy-nat-rule-a] destination-zone untrust
[GW-A-policy-nat-rule-a] action source-nat easy-ip
[GW-A]ip route-static 0.0.0.0 0.0.0.0 223.0.23.1
B校区配置
1.终端用户IP地址信息
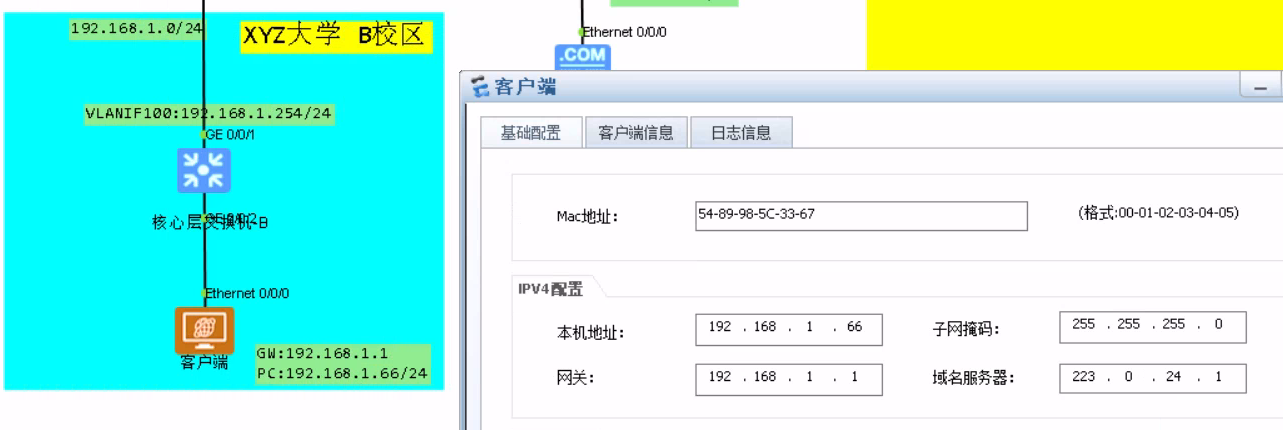
2.配置核心层交换机与出口网关的地址
[LSW-B]vlan 100
[LSW-B-GigabitEthernet0/0/1]port link-ty access
[LSW-B-GigabitEthernet0/0/1]port de vlan 100
[LSW-B]interface GigabitEthernet0/0/2
[LSW-B-GigabitEthernet0/0/2] port link-type access
[LSW-B-GigabitEthernet0/0/2] port default vlan 100
[LSW-Binterface Vlanif100
[LSW-B-Vlanif100] ip address 192.168.1.254 255.255.255.0[GW-B]int g0/0/0
[GW-B-GigabitEthernet0/0/0]ip add 192.168.66.2 24
[GW-B-GigabitEthernet0/0/0]int g1/0/0
[GW-B-GigabitEthernet1/0/0]ip add 223.0.12.1 30
[GW-B-GigabitEthernet1/0/0]int g1/0/2
[GW-B-GigabitEthernet1/0/2]ip add 192.168.1.1 24
[GW-B-GigabitEthernet1/0/2]int l9
[GW-B-LoopBack9]ip add 1.1.1.1 32
[GW-B]interface GigabitEthernet1/0/2
[GW-B-GigabitEthernet1/0/2] ip address 192.168.1.1 255.255.255.0
3.核心与网关分别配置相应路由
[LSW-B]ip route-static 0.0.0.0 0.0.0.0 192.168.1.1
[GW-B]ip route-static 0.0.0.0 0.0.0.0 223.0.12.2
4.网关配置NAT地址转换技术
[GW-B]nat-policy
[GW-B-policy-nat] rule name a
[GW-B-policy-nat-rule-a] destination-zone untrust
[GW-B-policy-nat-rule-a] action source-nat easy-ip
5.防火墙配置相应策略与区域
[GW-B]security-policy
[GW-B-policy-security] rule name a
[GW-B-policy-security-rule-a] action permit
[GW-B-zone-trust]
add interface GigabitEthernet1/0/2
[GW-B-zone-unust]
add interface GigabitEthernet1/0/0
[GW-B-zone-dmz
add interface tun 1
互联网区域配置
1.公网服务器IP地址与服务配置
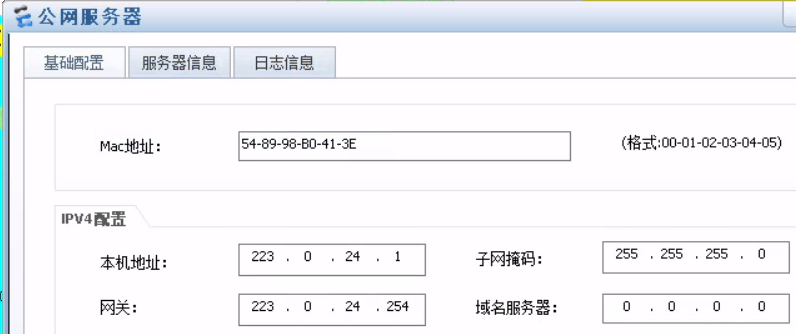
2.设备接口IP以及ISIS配置
[GW-A]isis 1
[GW-A-isis-1] is-level level-2
[GW-A-isis-1] network-entity 49.0001.0000.0030.0003.00
[GW-A]interface GigabitEthernet1/0/1
[GW-A-GigabitEthernet1/0/1] ip address 223.0.23.2 255.255.255.252
[GW-A-GigabitEthernet1/0/1] isis enable 1
[GW-A-GigabitEthernet1/0/1] service-manage ping permit
[GW-A-GigabitEthernet1/0/1] service-manage ping permit
[GW-A]interface LoopBack0
[GW-A-LoopBack0] ip address 2.2.2.2 255.255.255.255
[GW-A-LoopBack0] isis enable 1[ISP]isis 1
[ISP-isis-1] is-level level-2
[ISP-isis-1] network-entity 49.0001.0000.0020.0002.00
[ISP]int g0/0/0
[ISP-GigabitEthernet0/0/0]ip add 223.0.12.2 30
[ISP-GigabitEthernet0/0/0]isis enable 1
[ISP-GigabitEthernet0/0/0]int g0/0/1
[ISP-GigabitEthernet0/0/1]ip add 223.0.23.1 30
[ISP-GigabitEthernet0/0/1]isis enable 1
[ISP-GigabitEthernet0/0/1]int g0/0/2
[ISP-GigabitEthernet0/0/2]ip add 223.0.24.254 24
[ISP-GigabitEthernet0/0/2]isis enable 1
[ISP-GigabitEthernet0/0/2]int l0
[ISP-LoopBack0]ip add 8.8.8.8 32
[ISP-LoopBack0] isis enable 1[GW-B]isis 1
[GW-B-isis-1] is-level level-2
[GW-B-isis-1] network-entity 49.0001.0000.0010.0001.00
[GW-B]interface GigabitEthernet1/0/0
[GW-B-GigabitEthernet1/0/0] ip address 223.0.12.1 255.255.255.252
[GW-B-GigabitEthernet1/0/0] isis enable 1
[GW-B-GigabitEthernet1/0/0] service-manage ping permit
[GW-B]interface LoopBack0
[GW-B-LoopBack0] ip address 1.1.1.1 255.255.255.255
[GW-B-LoopBack0] isis enable 1
3.A校区网关与B校区网关建立GRE VPN隧道
[GW-B]interface Tunnel1
[GW-B-Tunnel1] ip address 10.10.10.10 255.255.255.0
[GW-B-Tunnel1] tunnel-protocol gre
[GW-B-Tunnel1] source 1.1.1.1
[GW-B-Tunnel1] destination 2.2.2.2
[GW-B-Tunnel1] service-manage ping permit
[GW-B]ip route-static 172.16.0.0 255.255.252.0 Tunnel1
[GW-B]ip route-static 172.16.4.0 255.255.252.0 Tunnel1
[GW-B]ip route-static 172.16.8.0 255.255.252.0 Tunnel1[GW-A]interface Tunnel1
[GW-A-Tunnel1] ip address 20.20.20.20 255.255.255.0
[GW-A-Tunnel1] tunnel-protocol gre
[GW-A-Tunnel1] source 2.2.2.2
[GW-A-Tunnel1] destination 1.1.1.1
[GW-A-Tunnel1] service-manage ping permit
[GW-A]ip route-static 192.168.1.0 255.255.255.0 Tunnel1
需求验证
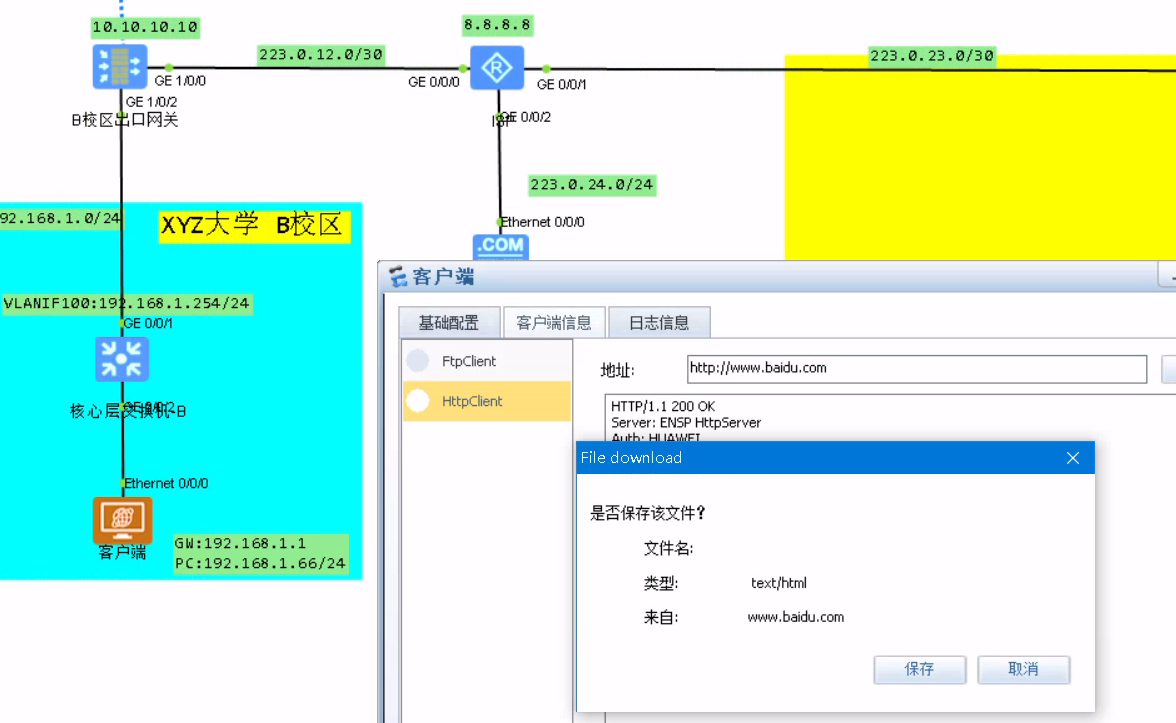
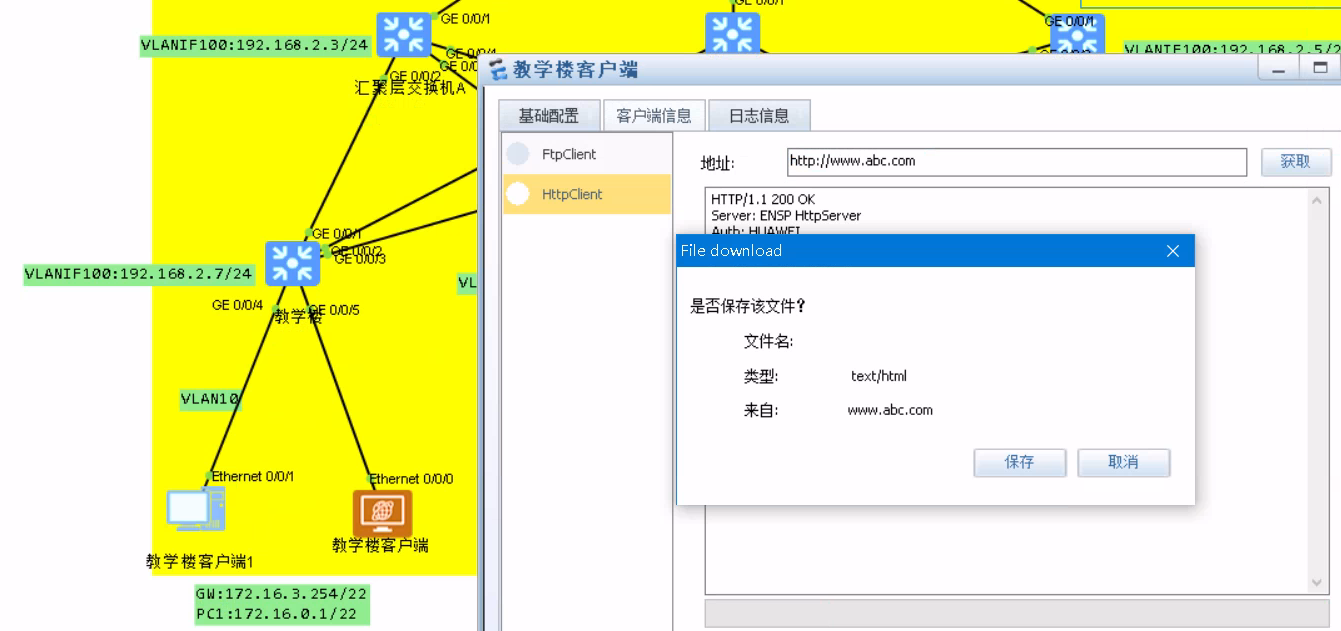
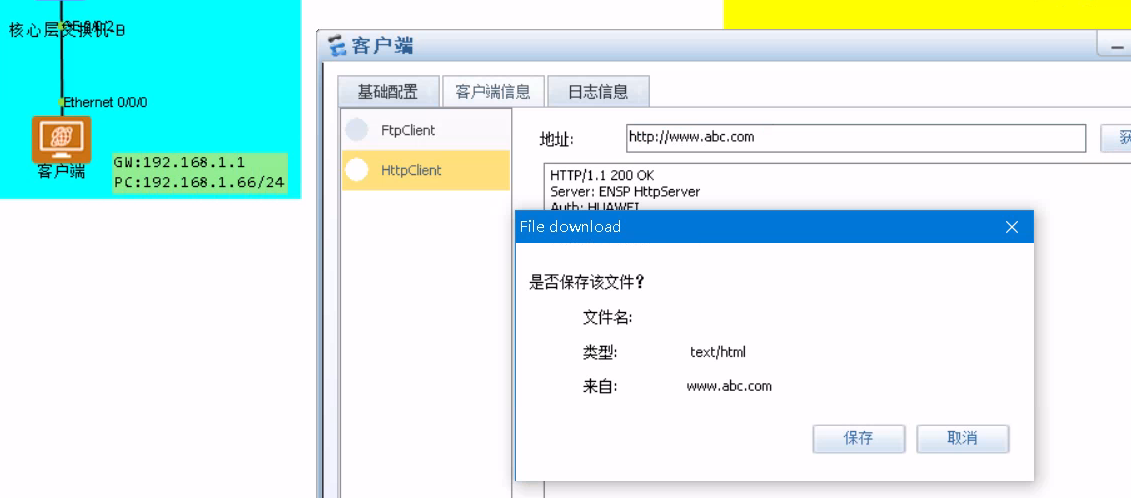
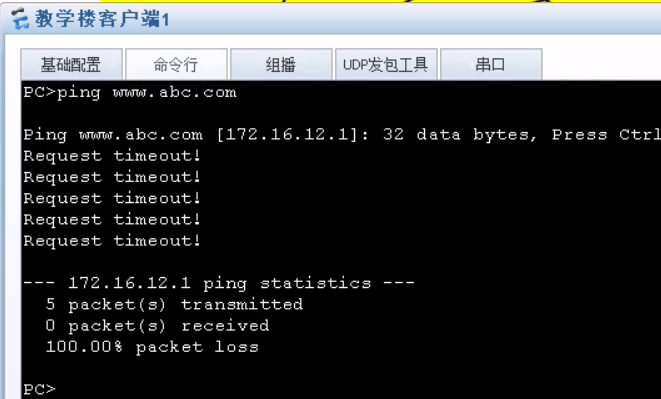
1.AB校区访问公网与校内官网服务器
访问百度服务器
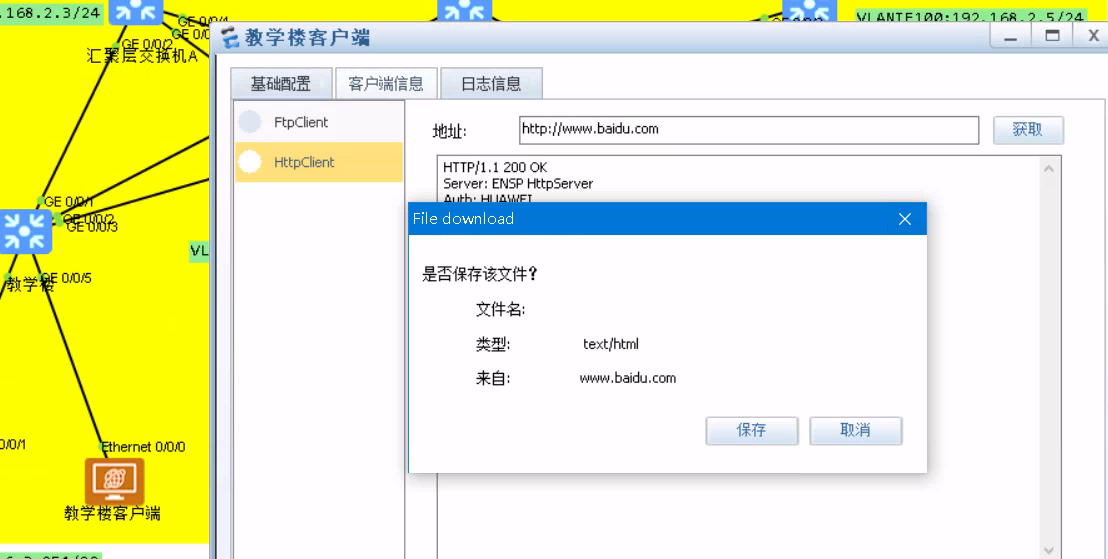
访问校内官网服务器
2.终端用户访问互联网需要进行NAT地址转换
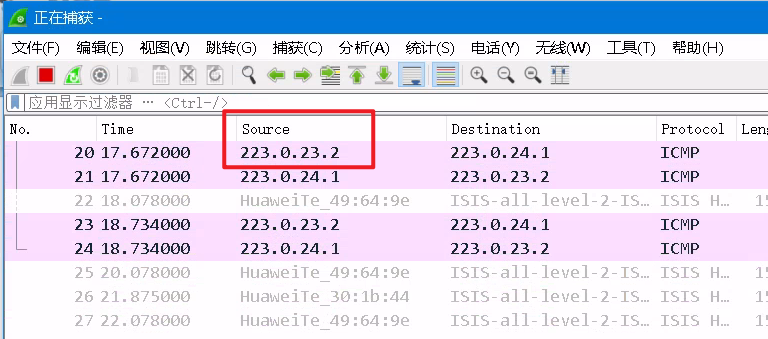
A校区ping公网服务器(抓包验证)
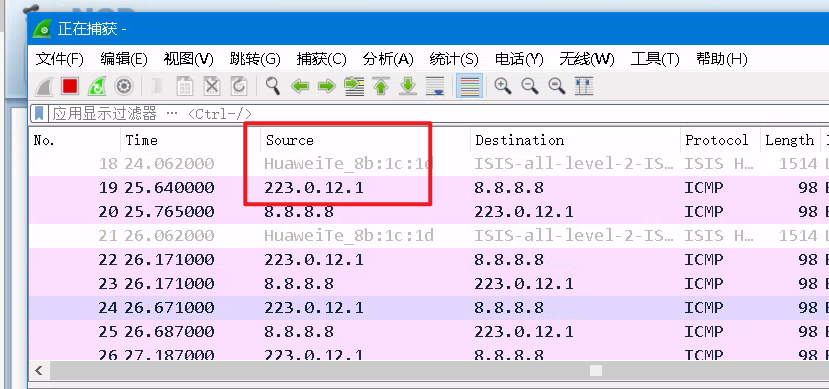
B校区ping公网服务器(抓包验证)
3.A校区办公楼与B校区互访,同时测试A校区其他部门无法与B校区互访
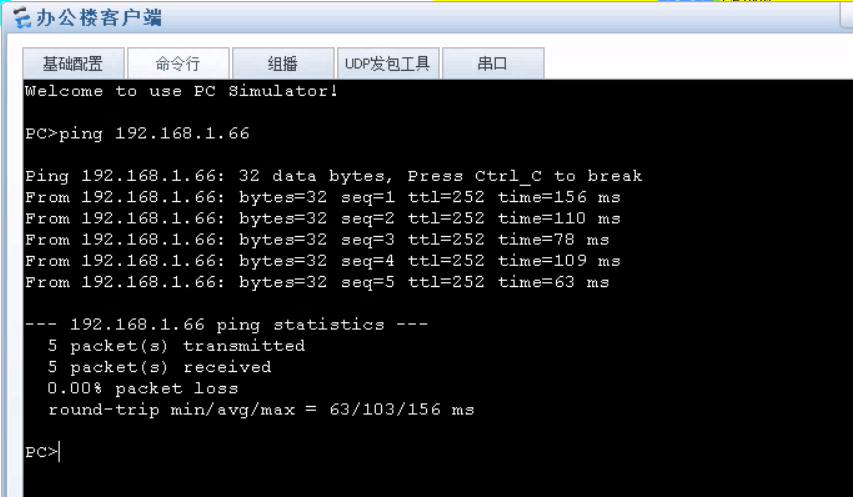
成功互访
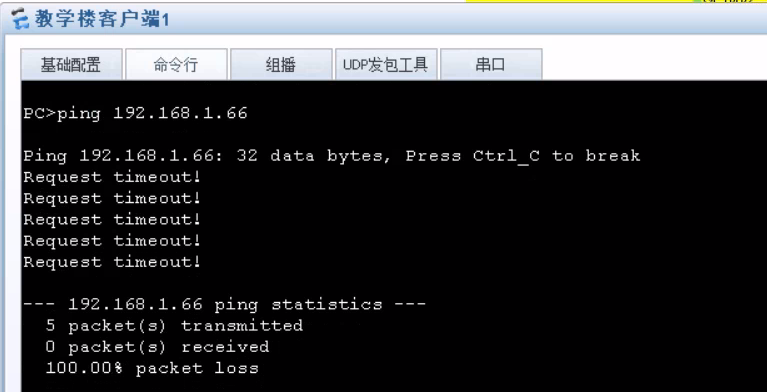
无法互访
4.验证是否经过VPN隧道转发(可以看到VPN封装的部分)

5.校内服务器不允许客户端进行ping测试
全部验证结束
结束
本次实验到此结束喽,如果你感觉本篇文章对你有很大的帮助,可以给我点一个关注。
这篇关于ENSP校园网设计实验的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!